AuthorTAFA Archives
April 2024
Categories
All
|
Back to Blog
Last week, cyberattacks from a range of industries (healthcare, government, education, gaming etc.) have led to serious consequences such as data leak of sensitive information and shut-down of services. Furthermore, new malwares, new vulnerabilities and patches have been found.
Read on to receive a quick summary of what happened this week in the space of cybersecurity. Australia & U.S cyber agencies warn of IDOR security flaws that got millions of people‘s data stolen. In a joint advisory, the U.S cybersecurity agency CISA and the Australian Cyber Security Centre warns of vulnerabilities, known as insecure direct object references (IDORs), that allows malicious attackers to access or modify sensitive data on an organization’s servers or even send malware to victims due to lack of proper security checks. They are urging vendors and developers to review their code and reduce the prevalence of IDOR vulnerabilities and flaws. Personal, financial, and health information of millions of people have been stolen by this vulnerability globally. Examples include but not limited to the exposure of thousands of medical documents caused by a data breach in LabCorp, the First American Financial security breach that resulted in 800 million personal financial files exposed, and the leak of hundreds of thousands of people’s private data stolen by a global stalkerware network. Medical files of more than 8 million people compromised via the MOVEit mass-hacks. Maximus, a U.S. government services contracting giant, has confirmed that the protected health information of “at least” 8 to 11 million individuals have been accessed via the MOVEit mass-hacks. Maximus has not yet confirmed which specific types of health data were accessed, but they had begun notifying the impacted customers, federal and state regulators of this data breach. Maximus is expecting this data breach to cost approximately $15 million to investigate and remediate. With current additions to the victims’ list of the MOVEit mass-hack, there are currently at least 514 organizations and more than 36 million individuals impacted. CardioComm, provider of heart monitoring technologies, confirms cyberattack downed its services. CardioComm Solutions, a Canadian provider of consumer and professional-grade heart monitoring technologies, has taken their systems offline due to a cyberattack. They stated last Tuesday that due to a cyberattack, their business operations will be “impacted for several days and potentially longer”. A number of CardioComm’s products and services were affected by the outrage, which includes the HeartCheck CardiBeat, the Global Cardio 3 software, and the Home Flex software. The full extent of the outrage and the number of impacted consumers are not yet known. The details of the nature of the cyberattack were also not shared, but CardioComm did state they are working to restore their data, and to reestablish their production server environments. Also CardioComm stated that as of yet, there is no evidence that their customers’ health information were compromised by the attack. 12 Norwegian Ministries impacted by Ivanti’s EPMM zero-day vulnerability. The Norwegian Security and Service Organization (DSS) have disclosed that 12 Norwegian government agencies have been compromised by a “data attack” last Monday. This attack was via the exploitation of a zero-day vulnerability found in Ivanti’s mobile endpoint management software by hackers. The vulnerability (tracked as CVE-2023-35078) is an authentication bypass flaw that affects all supported versions of Ivanti’s EPMM (Endpoint Manager Mobile) software, which allows unauthenticated users to remotely access the software to access users’ personal information such as names, phone numbers, and other mobile device details. The U.S. cybersecurity agency, CISA, warned last Monday that the hackers could create an EPMM administrative account, which would allow them to make further changes to a vulnerable system. Ivanti chief security officer, Daniel Spicer, stated that after the company became aware of the vulnerability, they have released a patch and are engaging with customers to assist them in fixing the flaw. Hawai’i Community College paid the ransom to prevent data leak. The Hawai’i Community College (UH) admitted that they had paid a ransom to the relatively new NoEscape ransomware gang to prevent the data leak of approximately 28,000 people. As UH explained, after careful consideration of all options and consultation with an external team of cybersecurity experts, they decided to pay the ransom to protect the individuals whose sensitive information might have been compromised. After the ransom was paid, the ransomware gang removed UH from their data leak site. However, restoration of the damaged IT infrastructure is still ongoing, and is expected to be completed by 14 August. UH are also improving their security posture to prevent similar attacks from occuring in the future. However, it is important to note that paying a ransom does not mean that your data would not be leaked. There have been instances in the past whereby attackers have promised to destroy the stolen data but instead continued to extort the victims or released the data anyway. CISA: New Submarine malware used to hack Barracuda ESG appliances. CISA revealed that Submarine, another new malware, was used to backdoor Barracuda ESG (Email Security Gateway) appliances on federal agencies’ network via the exploitation of a now-patched zero-day bug. This new malware is a multi-component backdoor used for detection evasion, persistence and data harvesting. Barracuda has provided guidance to affected customers, advising them to thoroughly review their environments to ensure that other devices within their networks have not been compromised. All Swiss visa appointments canceled across the UK due to “IT incident’. All appointments for Swiss tourist and transit visas have been canceled across the UK due to an ‘IT incident’ that has occurred in TLScontact, the Swiss government's chosen IT provider that facilitates visa applicants, at its London, Manchester and Edinburgh centers. TLScontact has informed that the ‘IT incident’ was not a ransomware attack but rather “technical difficulties with the transfer of customers’ biometric data to the Swiss government servers”. Call of Duty players infected with self-spreading malware. Hackers are infecting players of Call of Duty: Modern Warfare 2, with a malware that spreads automatically in online lobbies. This was alerted after a user warned players of this game, and suggested running an antivirus. After 2 analyses of the malware by different people, it was confirmed that the malware appears to be a worm. The company had brought the game offline while they investigated the reports of the issue. WordPress plugin Ninja Forms vulnerabilities let attackers steal user data. Patchstack researchers found that WordPress form-building plugin, Ninja Forms, contains 3 vulnerabilities (CVE-2023-37979, CVE-2023-38393, CVE-2023-38386) that would allow hackers to achieve privilege escalation and steal user data. These vulnerabilities affected NinjaForms versions 3.6.25 and older. The issues are rated as high-severity, but the CVE-2023-38393 is especially dangerous as the Subscriber role user requirement is incredibly easy to meet. The developers have released version 3.6.26 to fix the vulnerabilities. However, only roughly half of all NinjaForms users have downloaded the latest version, this leaves about 400,000 sites vulnerable to attacks. It is highly recommended for all website administrators who use the Ninja Forms plugin to update to the latest version immediately. If this is not possible, it is highly recommended to disable the plugin from their websites till they can update. Apple released patches for exploited bugs in their Apple products. Apple has released fixes for several security flaws that affect their iPhones, iPad, macOS computers, Apple TV and watches. They warned that some of these bugs have already been exploited. Last Tuesday, CISA warned that threat actors can exploit these vulnerabilities and take control of affected devices. One of the vulnerabilities (CVE-2023-32409) seems to be used to deploy spyware onto victims’ devices. It is highly recommended for users and admins to apply the software updates, and check that automatic patching systems are working properly. Zimbra released a patch for the zero-day vulnerability exploited by attackers. 2 weeks after the initial disclosure, Zimbra has released patches for a zero-day vulnerability (known as CVE-2023-38750) exploited in attacks on Zimbra Collaboration Suite (ZCS) email servers. This vulnerability is a significant threat as it allows attackers to steal sensitive information or execute malicious code on vulnerable systems. CISA warned U.S. federal agencies last Thursday to secure their systems against this vulnerability, and have added this vulnerability to its Known Exploited Vulnerabilities catalog. It is also highly recommended for private companies to prioritize and implement patches for all vulnerabilities listed in this catalog. That is all for last week! Enjoy (to the best you can) the rest of the week and don't forget to update your devices and systems to the latest patches!
Back to Blog
In an era of digital transformation, businesses are increasingly relying on cloud services to store and manage their data. With cyber threats evolving at an unprecedented pace, understanding the state of cloud security is crucial for safeguarding sensitive data and preserving operational continuity. This is made worse with the growing adoption of cloud technologies, the risk of cyber attacks and data breaches targeting cloud assets has also surged. Security remains a paramount concern for businesses and organizations worldwide. Thales’ 2023 Cloud Security study highlights the growing threat landscape surrounding cloud assets, revealing that they have become prime targets for cyberattacks. This report is based on a survey from nearly 3,000 IT and security professionals across 18 countries in the Americas, Asia Pacific and EMEA (Europe, the Middle East and Africa), and this report focuses on the latest cloud security threats, trends and emerging risks. In this article, we delve into the key takeaways from the report, empowering businesses to fortify their cloud defenses and embrace the full potential of the cloud. Key Findings
Key Cloud Data Concerns: Few Data Is Encrypted & Lack Of Key Control Despite the dramatic increase in sensitive data stored in the cloud, and the increase in businesses that have experienced a data breach:
This is a true cause of concern as not only is there still a vast amount of cloud data that is not encrypted, there is also a lack of control over encryption keys by businesses. End-to-end encryption is especially important as it protects data throughout its entire lifecycle. Leveraging encryption effectively helps ensure that even if attackers manage to breach cloud defenses, they cannot access the encrypted data without the decryption keys. Complexity Added With Adoption Of Multi-Cloud The adoption of multi-cloud continues to increase, with 79% of organizations having more than 1 cloud provider. Not only the multi-cloud but also the use of SaaS apps have increased significantly. 22% of respondents reported their enterprises utilized 51-100 different SaaS applications. This is an increase from the 16% reported in 2021. The expansion of cloud usage has also resulted in a significant challenge. More than half (55%) expressed that managing data in the cloud is more complex than on-premises environments. This is a 9% increase compared to the previous year. Digital sovereignty, which is about how a state regulates and exercises control over the technology and services used, is also a priority for respondents, whereby 83% expressed concerns over data sovereignty. Furthermore, 55% of respondents agreed that data privacy and compliance in the cloud has become more difficult. Lack of Zero-Trust Controls Only 41% of organizations surveyed have implemented zero trust controls in their cloud infrastructure. The percentage decreases even further (to 38%) on those that employ zero trust controls within their cloud networks. This is another concern, as zero trust is based on the principle of "never trust, always verify." This is important as in today’s rapidly evolving cyber threats, traditional security models that rely on perimeter defenses and trust-based approaches are no longer sufficient to protect organizations against advanced cyber threats. Unlike traditional security models, the Zero Trust model challenges this assumption by treating every user, device, and application as potentially untrusted, regardless of their location. This ensures that only authorized entities can access sensitive resources. For more information about zero trust best practices do see this article: Zero Trust Best Practices: Securing Your Digital Ecosystem SaaS Creating Cybersecurity Challenges Not only do the majority of companies surveyed have multiple cloud key management systems but also with the increased use of SaaS apps, this expands the threat surface for data exfiltration.
This with the fact that SaaS was ranked as the leading target for hackers (38%), then followed by cloud storage at 36%, shows there is a true concern for the wide range of software applications used. The Human Factor: Addressing Human Errors The human factor remains a crucial consideration in cloud security. From accidental data exposure to insider threats, human errors can have severe consequences for cloud security.
To reduce human errors, comprehensive training programs and strict access controls are needed to mitigate insider-related risks. Takeaway The Thales 2023 Cloud Security Report provides invaluable insights into the ever-evolving cloud security landscape. By understanding the challenges and best practices highlighted in the report, organizations can bolster their cloud security defenses, protect sensitive data, and maintain operational continuity. In a digital age where the cloud serves as a catalyst for innovation and growth, it is essential for businesses to embrace cloud security as an integral part of their overall cybersecurity strategy. Let us empower ourselves with the knowledge from this report and navigate the cloud security landscape with confidence, ensuring that our cloud deployments are safe, resilient, and ready to unleash their full potential. Related Topics Zero Trust Best Practices: Securing Your Digital Ecosystem What is Zero Trust Model? Definition, Principles and It's Benefits 7 Types of Cyber Security Measures SMEs Need to Protect Their Business The Common Signs Of Being Cyberattacked
Back to Blog
In an increasingly interconnected and digital world, businesses are faced with a growing number of cyber threats that can compromise sensitive data, disrupt operations, and damage their reputation. This is especially important as according to IBM’s report, in 2022, 83% of organizations studied have had more than 1 data breach. To make it worse, the average total cost of a data breach in 2022 reached an all time high of USD$4.35 million globally. As cybercriminals become more sophisticated, traditional security measures alone are not enough to protect against potential attacks. This is where penetration testing, also known as ethical hacking, emerges as a crucial aspect of a comprehensive cybersecurity strategy. In this article, we will explore why businesses need penetration testing and the importance of conducting regular assessments to safeguard their digital assets. What is Penetration Testing? Penetration testing is a simulated cyber attack on an organization's systems, networks, or applications conducted by certified professionals known as ethical hackers. The objective of penetration testing is to identify vulnerabilities and weaknesses in an organization's security infrastructure before malicious hackers can exploit them. By simulating real-world attack scenarios, businesses can proactively assess their security posture and take appropriate measures to strengthen their defenses. Why Do Businesses Need Penetration Testing? 1. Identifying Vulnerabilities
One of the most important reasons businesses need penetration testing is to identify vulnerabilities within their IT infrastructure. It is especially the case when you think about how crucial your IT infrastructure is to your business? And how much would it cost you if the IT infrastructure is disrupted for a day? From outdated software and misconfigured security settings to undiscovered weaknesses, ethical hackers uncover potential entry points that cybercriminals could exploit. Due to the human element of penetration test, unlike vulnerability scans, a penetration test can reveal vulnerabilities that:
2. Protecting Customer Data Businesses often handle sensitive customer data, and any breach of this information can lead to significant legal and reputational consequences. Penetration testing ensures that customer data is adequately protected, reducing the risk of data breaches and safeguarding customer trust. It is also one way to show your customers that your business is secure. 3. Meeting Compliance And Regulations Many industries and regulatory frameworks require businesses to conduct regular security assessments, including penetration testing, to demonstrate adherence to cybersecurity standards. Complying with these regulations is essential for avoiding penalties and maintaining business continuity. 4. Strengthening Cybersecurity Strategies And Incident Response. Penetration testing can help you understand better the security holes your organization may have, and the possible damage they can cause to your system’s efficiency and effectiveness. With the recommendations provided to prompt remediation, this can assist in strengthening your security infrastructure. Furthermore, penetration testing can help you assess your incident response capabilities. By simulating cyberattacks, this can help you identify gaps in your response plans, and fine-tune your strategies for swift and effective mitigation in case of a real attack. 5. Reducing Financial Losses: A successful cyber attack can lead to significant financial losses, including data recovery expenses, legal fees, and business interruption costs. Based on IBM’s report, the typical time needed to detect and stop a data breach is 227 days in 2022. The longer your sensitive data and your system are exposed to harmful software, the more damage malicious cyberattackers can do, and the greater the repercussions - not just financially but also your reputation and customers’ loyalty and trust. According to IBM’s report, in 2022 the average cost of a data breach globally is $4.3 million, an increase of 12.7% as compared to 2020. These expenses include everything from ransom payments and lost revenues to remediation, business downtime, legal fees and audit fees. Penetration testing helps prevent such incidents, saving businesses from potential financial crises. More importantly, a penetration test cost a small fraction of what a successful cyberattack would! The Importance of Regular Penetration Testing While conducting a one-time penetration test can provide valuable insights into an organization's security posture, regular testing is crucial to maintain robust cybersecurity. Cyber threats are continually evolving, and new vulnerabilities emerge as technology advances. Regular penetration testing ensures that businesses stay ahead of potential attackers and maintain an up-to-date understanding of their security strengths and weaknesses. Takeaway In today's digitally-driven business landscape, the importance of penetration testing cannot be overstated. It is a proactive and invaluable investment in protecting valuable assets, customer data, and reputation from cyber threats. By identifying vulnerabilities, ensuring regulatory compliance, enhancing your cybersecurity strategies and incident response capabilities, and reducing financial losses, penetration testing equips businesses with the necessary tools to navigate the complex cyber landscape securely. Implementing regular penetration testing as part of a comprehensive cybersecurity strategy empowers businesses to detect weaknesses, address potential risks, and strengthen their defenses against ever-evolving cyber threats. Vulnerability Assessment and Penetration Testing with TAFA With the current cyber environment, organizations are facing increasingly sophisticated cyber threats. To protect against these threats, it is necessary to utilize cybersecurity solutions that can prevent zero-day and advanced cyber threats and help ensure regulatory compliance. With our vulnerability assessment and penetration testing services, we will help you to identify vulnerabilities and protect your organization from potential security threats. Our comprehensive VAPT service will also evaluate your organization’s security defenses against modern cyber threats, and provide you with actionable insights and recommendations to enhance your organization’s security posture. To learn more information about TAFA’s VAPT services and how we can help your company, do not hesitate to contact us for more information. Related Topics What is Vulnerability Assessment & Penetration Testing (VAPT)? Definition, Benefits & It's Importance The Common Signs Of Being Cyberattacked 7 Types of Cyber Security Measures SMEs Need to Protect Their Business
Back to Blog
Last week, there were data breaches and ransomware attacks from a range of industries and countries, which has resulted in data leaks from multiple organizations. With more victims of MOVEit theft-attack are being added to the list. New ransomware operations, new vulnerabilities have been found and important patches to update. Furthermore, governments from different countries have been taking actions to protect their citizens against cybersecurity risks.
Read on to receive a quick summary of what happened this week in the space of cybersecurity. VirusTotal data leak affects 5,600 customers. VirusTotal apologized on Friday for leaking information of over 5,600 customers after an employee mistakenly uploaded a 313KB CSV file containing customers’ information to the platform last month. The data leak only impacted Premium account customers, with the leaked file containing their names and corporate email addresses. Those impacted include but not limited to official U.S entities and government agencies in Germany, Netherlands,Taiwan and the United Kingdom. The file contained information on employees of national authorities and large corporations such as Allianz, BMW, Deutsche Telekom, Bundesbank etc. VirusTotal assured that this data leak was a result of human error, and not due to a cyberattack or vulnerabilities in VirusTotal. The leaked file was only accessible to VirusTotal partners and cybersecurity analysts with a Premium account on the platform. Hence, anonymous or free accounts were unable to access the leaked file. Roblox data leak: 4,000 developer profiles and personal information made public. Roblox, a massive gaming platform has suffered a major data breach which led to the leakage of personal information of those who attended the Roblox Developer Conference between 2017-2020. Personal information released included names, phone numbers, email addresses, birth dates, and the physical addresses of almost 4,000 developers. From the website, haveibeenpwned it seems that the original data breach occurred on 18 December 2020, with the information of this breach only coming to light on 18 July 2023, with a total of 3,943 accounts compromised. The sites notes that with the above information leaked, it also even included each individual’s t-shirt size. Roblox have stated they have begun investigations, and have engaged with independent experts to support the investigation. They have also stated they will be vigilant in monitoring and vetting the cybersecurity posture of Roblox and their third-party vendors. Estee Lauder breached: 2 ransomware groups claim responsibility. Estee Lauder has disclosed on 18 July, that they have suffered a cybersecurity incident whereby unauthorized groups have gained access to some of their systems and obtained data. Estee Lauder has started investigations with third party cybersecurity experts, and are currently still assessing the nature and scope of the data compromised. 2 ransomware groups have claimed responsibility for the attack. First is the Clop ransomware group that claims to have stolen 131GB of information and their archives via the MOVEit theft-attack, which has impacted more than 400 organizations worldwide. The second group is the BlackCat/Alphv ransomware gang, which on 18 July claimed that they still had access to the company’s systems, despite Microsoft and Mandiant being brought in for incident response. They have also threatened to reveal more information about the data stolen unless the cosmetic giant responds. Sophos impersonated by new SophosEncrypt ransomware. Sophos, a cybersecurity vendor, is being impersonated by SophosEncrypt, a new ransomware-as-a-service, with the threat actors using the company name for their operation. This was discovered by MalwareHunterTeam, it was initially thought that it was a part of a red team exercise by Sophos. However, the Sophos X-Ops team tweeted that they did not create this encryptor. Sophos have released a report on this ransomware, with their analysis that the ransomware seems to have the capability to do many things beyond encrypting files, which is unusual when compared to most contemporary ransomware. The ransomware also seems to emphasize methods for the target to communicate with the attacker that most ransomware groups no longer use. Also it seems that the IP address is associated with “Cobalt Strike command-and-control automated attacks that attempt to infect internet-facing computers with crypto mining software”. The JumpCloud breach linked back to North Korean state-backed hackers. According to multiple security researchers, US-based enterprise software company JumpCloud was breached by North Korean state-backed hackers who appear to be financially motivated to steal cryptocurrency. JumpCloud Chief Information Security Officer Bob Phan confirmed that “fewer than 5 JumpCloud customers….and fewer than 10 devices in total were impacted.” While JumpCloud did not name or attribute the hackers to a particular nation, researchers at CrowdStrike and SentinelOne have attributed the breach to North Korea-backed hackers, Lazarus. Mandiant has also attributed the hack to North Korea. Over 15,000 Citrix servers are likely vulnerable to CVE-2023-3519 attacks. Thousands of Citrix Netscaler ADC and Gateway servers have been exposed online. They are probably vulnerable against a critical remote code execution (RCE) bug which is exploited by unauthenticated threat actors as a zero-day. Shadowserver Foundation security researchers identified at least 15,000 appliances that were exposed to attacks that leveraged the flaw (CVE-2023-3519). On 18 July, Citrix released security updates to address this RCE vulnerability, and urged customers to install the patches as soon as possible. CISA also ordered U.S federal agencies last Wednesday to secure Citirix networks on their networks by 9 August. They have also warned that the bug was already used to breach the systems of a U.S. critical infrastructure organization. U.S government launched Cyber Trust Mark - loT security labeling program. The U.S government has launched Internet of Things (loT) cybersecurity labeling program called U.S. Cyber Trust Mark, that aims to protect Americans against the security risks associated with internet-connected devices. This program aims to help Americans to make informed decisions that they are buying internet-connected products that include strong cybersecurity protections against cyber threats and attacks. The U.S. Cyber Trust Mark will be a shield logo that would appear on products that meet the established cybersecurity criteria. Established by the National Institute of Standards and Technology (NIST), the criteria will include standards such as requiring devices to have unique and strong passwords, protect both stored and transmitted data, offer regular security updates and have incident detection capabilities. The full list of standards has not yet been finalized, and will be completed by the end of 2023. The U.S Cyber Trust Mark will also include a QR code that will link to a national registry of certified devices and provide up-to-date security information as they did not want to create a label that states this product “had been certified and then stayed secured forever”. GitHub warns developers of Lazarus hackers targeting them to infect their devices. GitHub cautions of a social engineering campaign that is targeting developers’ accounts in the cybersecurity, cryptocurrency, blockchain and online gambling sectors to infect their devices with malware. The campaign is linked to North Korean state-backed Lazarus hacking group. GitHub has identified that they are targeting personal accounts of employees of technology companies by either using compromised legitimate accounts or creating fake personas of developers and recruiters. These are used to contact and initiate conversations with developers and employees in the above said sectors. After establishing trust, the hackers will invite them to collaborate on a project. However, these projects utilize malicious NPM dependencies that download further malware to targets’ devices. The Norwegian Data Protection Authority (DPA) banned Facebook & Instagram behavioral advertising. The DPA, Norwegian’s data privacy watchdog, has temporarily banned behavioral advertising on Meta’s Facebook and Instagram as they consider that the practice of Meta is illegal. The ban prohibits the practice unless Meta gets explicit consent from Norwegian users to process their data. As stated by the DPA, Meta extensively monitors the users’ actions, and are tracking their activities across its platforms. Meta utilizes content preferences, location information and information users’ posts on Facebook and Instagram to build personalized profiles that makes targeted advertising much easier. The Norwegian DPA stated that if Meta fails to comply with the decision, there would be a daily penalty of roughly $100,000. This is a temporary ban of 3 months which starts on 4 August, however the DPA are considering contacting the European Data Protection Board to extend the decision beyond the 3-month ban. U.S government banned European spyware vendors - Intellexa and Cytrox. The U.S. government has banned the European commercial spyware manufacturers due to risks to the U.S. national security and foreign policy interests. The 4 commercial entities banned are: Intellexa S.A from Greece, Intellexa Limited from Ireland, Cytrox Holdings ZRT from Hungary, and Cytrox AD from North Macedonia. This was due to the 4 companies’ involvement in trafficking cyber exploits used to gain unauthorized access to the devices of high-risk individuals globally such as politicians, executives, journalists and activists. New NoEscape ransomware operation believed to be a rebrand of Avaddon. NoEscape launched in June this year when it started to target organizations in double-extortion attacks. These threat actors steal data and encrypt files on Windows, Linux, and VMware ESXi servers. They will threaten their victims to release the stolen data publicly if a ransom is not paid. The ransom tends to range between hundreds of thousands of dollars to over $10 million. It is believed that they are a rebrand of Avaddon ransomware gang who shut down operation in 2021 after the FBI and Australian law enforcement released Avaddon advisories. They also shared victims’ decryption keys with BleepingComputer in an anonymous tip.
Back to Blog
In today's dynamic and interconnected digital landscape, traditional security models that rely on perimeter defenses are no longer sufficient to protect against the sophisticated and evolving cyber threats. As the cyber landscape becomes increasingly complex, organizations are adopting a more proactive and comprehensive security approach: the Zero Trust model. Zero Trust best practices have emerged as a game-changing strategy to safeguard valuable assets and data from cyber threats. In this article, we will highlight essential best practices to implement this groundbreaking security framework effectively. Essential Zero Trust Best Practices: As highlighted in our previous article, Zero Trust is based on the principle of “never trust, always verify again and again”. Here are some best practices to help you implement this model effectively. 1. Identify and Classify Assets The first step in implementing Zero Trust is identifying and classifying all digital assets, including data, applications, and devices. Understanding the value and sensitivity of each asset helps you to prioritize your organization’s protection and allocate resources effectively. 2. Regular Security Audits and Penetration Testing Regular periodic security audits and penetration testing help identify vulnerabilities and weaknesses in the security infrastructure cyberattackers could utilize to enter and compromise your network. This is extremely important as one of the first steps to Zero Trust security is understanding the current state of your network security. Do you have cybersecurity defenses? If yes, how effective are they? Regular testing enables organizations to address potential issues promptly and improve their security posture. 3. Verify All Devices Verifying your users is one of the first steps of the principles of Zero Trust. This extends to endpoint devices, which includes but is not limited to mobile devices, desktop computers, embedded devices, servers and virtual machines. Verification includes ensuring that any device that is used to access your internal resources does meet the security requirements of your company. It is essential to look for a solution that allows you to easily track and enforce all device status with easy user onboarding and offboarding. Adopt a risk-based assessment that initiates the verification process when the system detects a possible intrusion to make it a good user experience. 4. Implement Strong Authentication Adopting multi-factor authentication (MFA) is fundamental to Zero Trust best practice. Requiring users to provide multiple verification factors, such as biometrics (i.e. fingerprint scan, retina scan, voice scan or face scan), tokens, or one-time passwords, adds an extra layer of security beyond traditional username and password combinations. 5. Least Privilege Access Applying the principle of least privilege ensures that users and applications only have access to the specific resources they need to perform their tasks. This principle is based on the ideology that a particular user should be granted just enough privileges to allow them to complete a particular task. This minimizes the potential impact of a security breach and reduces the attack surface. Least privilege access can also include “just in time” privileged access, whereby this will restrict privileges to only specific time when they are needed. This includes one-time-use credentials and privileges that expire. 6. Continuous Monitoring and Analytics Real-time monitoring and behavioral analytics are essential components of Zero Trust. Continuously monitoring user activities, network traffic, and application interactions enables the timely detection of suspicious behavior or anomalies. This is especially important for users who have administrative rights due to the large scope of access permissions and the highly sensitive nature of the data they can access. 7. Secure Access for Remote Users With the rise of remote work and mobile devices, secure access for remote users is critical. Zero Trust best practices include implementing secure remote access technologies such as virtual private networks (VPNs) and secure remote desktops. 8. Encrypt Data & Communications Encrypting sensitive data both at rest and in transit is a core Zero Trust practice. As your data could get into the hands of unauthorized users, it is an act of negligence if the data is unencrypted. Data and communication encryption means encoding it so that only verified users can read it. Hence, this ensures that even if data is intercepted, it remains unreadable and inaccessible to unauthorized individuals. 9. Incorporate Network Segmentation Network segmentation is a critical Zero Trust practice that involves dividing the network into smaller, isolated segments. This will help you restrict access to your components. Rather than unlimited access, users inside the network have limits to what they can access. This ensures that even if one segment is compromised, the attacker’s access is limited. Hence, the damage they can do will be limited as well. Takeaway As cyber threats continue to evolve, the Zero Trust model has emerged as a leading cybersecurity strategy to protect against advanced attacks. By adopting these best practices, organizations can build a robust security framework that continuously verifies users, devices, and applications, ensuring the protection of valuable assets and data. Implementing Zero Trust is a proactive step towards safeguarding the digital ecosystem, enabling organizations to navigate the ever-changing cyber landscape securely and confidently. Cyber Security For Organizations with TAFA With the current cyber environment, organizations are facing increasingly sophisticated cyber threats. To protect against these threats, it is necessary to utilize cybersecurity solutions that can prevent zero-day and advanced cyber threats and help ensure regulatory compliance. With our prevention first and zero-trust approach to security using machine learning (ML) and artificial intelligence (AI), TAFA Shield will strengthen your company's ability to prevent and block cyber attacks and threats. To learn more information about TAFA Shield and how we can help your company, do not hesitate to contact us for more information. Related Topics What is the Zero Trust Model? Definition, Principles and It’s Benefits Why do businesses need to be cyber secure? Is it as important as emphasized everywhere? 7 Types of Cybersecurity Measures SMEs Need to Protect Their Business
Back to Blog
The Philippine National Police stated that cybercrime incidents in Metro Manila have risen by 152% during the first half of 2023. This sheds light on the alarming increase in cybercrimes within the metropolitan area. As technology continues to advance, cybercriminals have become more sophisticated, exploiting vulnerabilities and posing significant risks to individuals and organizations alike.
In this article, we will delve into the key insights from the article and emphasize the urgent need for enhanced cybersecurity measures to combat the growing threat of cybercrimes in Metro Manila. The Escalating Cybercrime Landscape The latest statistics on cybercrime were released at the Joint Anti-Bank Robbery and Cybercrime Coordinating Committee meeting at the Cybercrime Investigation and Coordinating Center (CICC).
Despite the implementation of the SIM Registration Act, which requires Filipinos to register their SIM card with their respective telco providers to prevent individuals who commit scams via devices using SIM cards, this rise in incidents shows that there is still a strong need to strengthen our cybersecurity posture. From these latest statistics, it is obvious that cybercrime and cyber security related concerns are on the upward trend. But it is also important to note this rise in cybercrime is a worldwide trend. Hence, it seems that more is needed to prevent this from happening. The Need for Enhanced Cybersecurity Measures: To address the drastic increase in cybercrimes, the police have intensified their operations and investigation on these cases. Furthermore they have also intensified their information campaign to raise awareness and are providing support and training to their cyber cops. However, effort CANNOT be one-sided. Here are some useful practices you can use to enhance your security posture, and to ensure that you will not be tricked by these cyber scammers and attackers.
Takeaway The growing percentage of cybercrimes in Metro Manila serves as a wake-up call for individuals and organizations to prioritize cybersecurity. Enhanced cybersecurity measures, including heightened awareness, robust security infrastructure, incident response preparedness, and regulatory compliance, are essential to combat the evolving threat landscape. By proactively addressing cybersecurity risks, Metro Manila can build a secure and resilient digital environment that protects individuals, businesses, and critical infrastructure from the damaging consequences of cybercrimes. It is a collective responsibility to work together, raise awareness, and implement effective cybersecurity measures to safeguard the digital future of Metro Manila. Securing Your Business with TAFA Shield With the evolving threat landscape, securing your business against threat actors is now essential to your cybersecurity strategy. With our prevention first and zero-trust approach to security using machine learning (ML) and artificial intelligence (AI), TAFA Shield will strengthen your company's ability to prevent and block cyber attacks and threats. To learn more information about TAFA Shield and how we can help your company, do not hesitate to contact us for more information. Related Topics 7 Types of Cyber Security Measures SMEs Need to Protect Their Business The Common Signs Of Being Cyberattacked Philippines Ranked 4th Globally With Most Cyber Attacks Incidents - DICT. And Cybersecurity Tips To Help Protect Your Business
Back to Blog
Last week, there were data breaches and ransomware attacks from a range of industries and countries. With more organizations - banks, hotels, universities among the latest MOVEit mass-hack victims. Furthermore, new vulnerabilities have been found and important patches to update.
Read on to receive a quick summary of what happened this week in the space of cybersecurity. Deutsche Bank AG confirmed service provider breach exposed customer data. Deutsche Bank AG has confirmed that a data breach on one of their service providers has exposed their customers’ data in a likely MOVEit Transfer data-theft attack. The German bank has stated that the incident impacted customers in Germany who used their account switching service in 2016, 2017, 2018 and 2020. Although the number of impacted customers has not been determined, the bank has said only a limited amount of personal data was exposed during this breach. Deutsche Bank has also informed impacted clients on the breach, the direct impact of the breach and the precautionary measures clients should take. The bank also stated that cybercriminals cannot gain access to accounts using the exposed data, but they might try to initiate unauthorized direct debits. In response, the bank has extended the period of unauthorized direct debits returns to 13 months. HCA Healthcare data breach: 11 million patients affected. American healthcare operator, HCA Healthcare, has confirmed that they had been targeted by hackers in a cyberattack. HCA Healthcare is the largest for-profit health system in America. The data breach has resulted in at least 11 million patients’ personal data leaked online on hacker forums. The breach occurred on the 5th July, and the majority of the 11 million patients came from 20 states including California, Florida, Georgia, and Texas. The compromised data includes names, home addresses, phone numbers, data birth, email addresses, gender, appointment dates and location. Initially, the cybercriminals attempted to hold this data for ransom, but when HCA did not meet demands, they started to post now-for-sale data on hacker forums. Telekom Malaysia confirms data breach. Telekom Malaysia (TM) has confirmed a recent data breach that involves Unifi customers’ personal information. This includes names, national identification, passport numbers and contact details. The company also stated that no financial information was affected. TM stated that the breach has been contained and proactive steps have been taken to protect data across its platforms. Furthermore, they have notified customers of the data breach and warn them of phishing tactics that include online scams, suspicious links and unsolicited phone calls. The company also reported this breach to relevant authorities. 12,000 SBI employees’ data leaked on Telegram channels. In a massive data breach, more than 12,000 State Bank of India (SBI) employees’ data was leaked on Telegram channels. The leaked data include employees’ names, address, contact numbers, SBI Passbooks, PAN numbers, account numbers, photo IDs, Aadhar Card and Voter Card. The threat actor claimed to exploit an unprotected database which potentially gave unrestricted access to the financial details of millions of consumers such as bank balances and recent transactions. The same threat actor has also allegedly dumped the data on publicly accessible online forums whereby 4000 more employees’ data were leaked. Some of the threat actors have also put the leaked data up for sale in some dark web forums. Razer investigates the Razer Gold data breach. Razer is investigating an alleged data breach related to its Razer Gold, a virtual gaming credits platform. The firm stated that they are aware of the potential breach on Monday. This comes after a post surfaced on a hacker forum on Saturday whereby they claimed to have stolen data from Razer, which includes source codes, encryption keys, backend access log-ins and database for “Razer.com and its products”. The hackers included screenshots of the alleged breach as proof - listing folders that appear to contain API details, merchant vouchers and payment channels. The hackers have the entire set of data for sale for US$100,000 in Monero cryptocurrency, although they are willing to negotiate a sale for sale. Razer has stated that once investigations are concluded, they will report this matter to the relevant authorities. 1st Source data compromised by MOVEit data breach. Financing firm 1st Source Corp stated on Monday that a 3rd party gained access to data of their commercial and individual clients due to the MOVEit data-theft attack. The company did not disclose the scale of the data breach but they did state that they are in the process of identifying and notifying the impacted clients. Radisson Hotels Americas impacted by MOVEit data-theft attack. A spokesperson from Choice Hotels, which acquired Radisson Hotels Group in 2022, stated that a “limited number of guest records” were accessed by the hackers during the MOVEit data-theft attack. However, they did not state how many guests had been affected. They are currently still investigating this breach, and when affected guests are identified, they will send out data breach notification letters. Honeywell devices’ security flaws could be exploited to disrupt critical industries. Researchers at Armis discovered 9 vulnerabilities in Honeywell devices that are used in critical industries. If exploited, this would allow hackers to cause physical disruption and potentially impact the safety of human lives. The vulnerabilities are found in Honeywell’s Experion distributed control system (DCS) products. These are control systems that are utilized to control large industrial processes across critical industries, such as energy, oil, gas mining and pharmaceuticals, whereby high availability and continuous operations are critical. 7 of these vulnerabilities have been given a critical-severity rating - which means threat actors can remotely run unauthorized code on both the Honeywell servers and controllers. The vulnerabilities allow for unauthenticated access - this allows the threat actors to exploit the flaws without having to log into the controller. Honeywell had made patches available for the vulnerabilities and urged all affected organizations to promptly apply them. The Bangladesh government takes down exposed citizens’ data on the website. The Bangladeshi’s e-Government Computer Incident Response Team (CIRT) stated that they had taken down citizens’ sensitive data that was left exposed on a government website. In a press release, CIRT said that they had “promptly” addressed the data breach. The State Minister for Information and Communication Technology, Zunaid Ahmed Palak stated that citizens’ information was exposed not due to the government website being hacked but rather due to the vulnerability of the website. Bangladesh’s Home Minister, Asaduzzaman Khan Kamal reportedly said that the law enforcement agencies are investigating the incident. Colorado State University (CSU): Data breach impacts both staff and students. CSU has confirmed that the personal information of current and former staff and students were stolen during the MOVEit Transfer data-theft attack. CSU informed their students and staff on 12 July 2023 that the attackers have gained access to the personal data of staff and students. The personal information stolen include, full names, birth date, student or employee identification numbers, social security number, and demographic information (gender, ethnicity, level and area of education). The stolen data goes as far back as 2021. This data breach was due to a compromise of the University’s service vendors, and all these providers used the MOVEit Transfer platform. CSU is currently carrying out investigations to determine the impact of the stolen data, and will send out individual notification letters to those impacted. Microsoft is still unsure how hackers stole the Azure AD signing key. Microsoft have stated they are still unsure how Chinese hackers stole an inactive Microsoft account (MSA) consumer signing key that was used to breach the Exchange Online and Azure AD accounts of roughly 25 organizations, including government agencies, and they are still investigating this method. The incident was reported by the US government officials after they discovered unauthorized access to several government agencies’ Exchange Online email services. Microsoft has already revoked all valid MSA signing keys to block all attempts to generate new access tokens and moved the newly generated ones to the key store that they use for enterprise systems. While they no longer detected any key-related malicious activity, they have stated that attackers have now switched to other techniques. Microsoft: Unpatched Office zero-day exploited against NATO Summit attendees. On Tuesday, Microsoft disclosed that RomCom Russian cybercrime group exploited an Office zero-day that is yet to be patched in recent phishing attacks against NATO Summit attendees. The attackers used malicious documents impersonating the Ukrainian World Congress organization to install malware payloads including MagicSpell loader and the RomCom backdoor. Blackberry researchers stated that if successfully exploited, it will allow attackers to “conduct a remote code execution (RCE)- based attack by crafting malicious docx. or .rtf documents designed to exploit the vulnerability”. Unauthenticated attackers can exploit the vulnerability (tracked as CVE-2023-36884) in high-complexity attacks requiring user interaction. This vulnerability can allow attackers to access sensitive information, turn off system protection, and deny access to the compromised system. New APT RCE exploit targeting critical industries. Rockwell Automation, in coordination with CISA, has analyzed a new remote code executive (RCE) exploit linked to an unnamed Advanced Persistent Threat (APT) group could be utilized to target unpatched ControlLogix communications modules, which are commonly used in manufacturing, electric, oil and gas, and liquified natural gas industries. The targeted vulnerability (CVE-2023-3595) is caused by an out-of-bounds write weakness that will allow attackers to gain remote code execution or trigger denial-of-service through maliciously crafted CIP messages. If successful, attackers can manipulate the module’s firmware, wipe the module memory, alter data traffic, establish persistent control and this could potentially impact the industrial process it supports. Rockwell strongly recommends customers to apply the security patches they have released for all affected products. CISA warned Rockwell customers to patch the critical RCE vulnerability to foil potential attacks. Google Play to enforce organizations registration to curb malware submissions. Google Play is requiring all new developer accounts to register as an organization to provide a valid D-U-N-S (Data Universal Numbering System) number before submitting apps. This is a part of the effort to curb the constant invasion of malware on Google Play and hence to enhance the platform’s security and trustworthiness. By requiring a D-U-N-S number from software developers, Google will increase the difficulty of malicious apps to re-register on the app store as they will have to create a new company to return to the platform. Additionally, more information about the developer will be added under the changed “App support” (from “Contact details) such as it will now include the company name, complete office address, website URL and phone number. This is additional to the current details available such as developer’s name, email and location. Google will also regularly verify information provided by app developers, and will suspend the account to publish apps if any inconsistencies are found. Zimbra urges admins to manually fix a zero-day vulnerability that can be exploited in attacks. Zimbra are urging admins to manually fix a zero-day vulnerability that can be actively exploited to target and compromise Zimbra Collaboration Suite (ZCS) email servers. The company warned of this vulnerability and stated that a patch is planned to be released in the July patch release. Although a patch was not provided yet, it did provide a fix that admins can manually apply to remove the attack vector. The fix can be found here. Admins must prioritize this as multiple Zimbra bugs have been explored to breach hundreds of vulnerable email servers globally in recent years. WordPress AIOS plugin used by over a million sites, logged plaintext passwords. The All-In-One Security WordPress security plugin, which is used by over a million WordPress sites, has been found to not only record user logins attempted but also to log plaintext passwords to the site’s database. This is especially dangerous as malicious admins could use people’s login details to take over their accounts, and attackers that gain access to the site’s database can exfiltrate user passwords in plaintext. Updraft have offered development builds of the upcoming patch release to concerned users 2 weeks ago, however those attempting to install this reported website problems and that the password logs weren’t removed. On 11 July, the AIOS vendor released version 5.2.0 which included a patch to prevent the record of plaintext passwords and to clear out old entries. As of 14 July, only a quarter of AIOS users have applied the update, which means 750,000 sites still remain vulnerable. Websites using AIOS must update to the latest version, and it is recommended to ask users to reset their passwords. Cisco SD-WAN vManage impacted by critical-severity vulnerability that affects REST API. Cisco published a security bulletin informing of a critical-severity vulnerability (tracked as CVE-2023-20214) in the request authentication validation for the REST API of Cisco-SD-WAN vManage software. This flaw can be exploited by sending a specially crafted API request to the affected vManage instances. This could allow attackers to “retrieve information from and send information to the configuration of the affected Cisco vManage instance”. This can enable attackers to read sensitive information from the compromised system, modify certain configurations, disrupt network operations, and more. Cisco SD-WAN vManage has released fixes for versions that are affected by this vulnerability. Read here for versions that have fixes. However, there won’t be any fixes for versions 20.7 and 20.8 (they are also impacted), hence users are advised to migrate to a different release. Versions between 18.x and 20.xd are not impacted by this vulnerability.
Back to Blog
In today's interconnected world, cybersecurity is of utmost importance to protect sensitive data and maintain the trust of customers and stakeholders. As cyber threats continue to evolve, businesses must take proactive measures to identify vulnerabilities and fortify their defenses. This is where vulnerability assessment and penetration testing play a pivotal role.
In this article, we will dive into the concepts of vulnerability assessment and penetration testing, explore their benefits and importance, and discuss why businesses need to incorporate them into their cybersecurity strategy. Understanding Vulnerability Assessment and Penetration Testing (VAPT): Vulnerability Assessment: Vulnerability assessment is a systematic process of identifying, quantifying, and prioritizing vulnerabilities within an organization's systems, networks, and applications. It involves conducting thorough scans and analysis to detect weaknesses and security gaps that may be exploited by cyber attackers. In short, a vulnerability assessment identifies and reports noted vulnerabilities. The assessment provides businesses with valuable insights into their security posture and enables them to take proactive steps to remediate identified vulnerabilities. Penetration Testing: Penetration testing, also known as ethical hacking, simulates real-world cyber attacks to evaluate the effectiveness of an organization's security controls. Certified professionals attempt to exploit vulnerabilities and gain unauthorized access to systems, networks, or applications, mimicking the tactics used by malicious hackers. Penetration testing helps identify weaknesses and provides actionable recommendations to enhance the overall security posture. Benefits of Vulnerability Assessment and Penetration Testing (VAPT): 1. Identifying Vulnerabilities These assessments help businesses identify vulnerabilities that may be present in their systems, networks, or applications. By uncovering weaknesses before malicious actors exploit them, organizations can implement appropriate controls and patch vulnerabilities to mitigate risks effectively. 2. Enhancing Security Posture VAPT provides insights into potential vulnerabilities and security gaps. Organizations can leverage these findings to strengthen their security infrastructure, improve security policies and procedures, and implement proactive measures to protect critical assets. 3. Meeting Compliance Requirements Many industry regulations and compliance frameworks mandate regular VAPT. By conducting these assessments, organizations can demonstrate compliance and ensure adherence to the required security standards. This helps you to avoid costly penalties and fines. 4. Safeguarding Reputation A successful cyber attack can severely damage an organization's reputation and erode customer trust. By proactively identifying vulnerabilities and addressing them, businesses can demonstrate their commitment to data security, protecting their brand image, and maintaining the trust of their stakeholders. 5. Cost Savings Identifying and addressing vulnerabilities at an early stage can prevent potential data breaches or system failures, saving businesses from significant financial losses associated with cyber attacks. Investing in vulnerability assessment and penetration testing can provide long-term cost savings by preventing potential breaches. Importance for Businesses: 1. Proactive Defense: VAPT helps businesses adopt a proactive approach to cybersecurity. By regularly assessing their systems and networks, organizations can identify weaknesses before they are exploited by threat actors, reducing the risk of successful cyber attacks. 2. Risk Mitigation: Understanding and mitigating risks is crucial for protecting valuable assets. VAPT provides actionable insights into potential vulnerabilities, allowing organizations to prioritize remediation efforts based on risk severity. 3. Continuous Improvement: The dynamic nature of cyber threats requires businesses to constantly evaluate and improve their security measures. Regular assessments enable organizations to stay up to date with emerging threats, identify new vulnerabilities, and implement necessary security enhancements. 4. Security Assurance: Conducting VAPT provides assurance to customers, partners, and stakeholders that an organization takes cybersecurity seriously. It demonstrates a commitment to protecting sensitive data and fostering a secure business environment. This then also helps protect your brand reputation by avoiding loss of consumer confidence and business reputation. Common Misconception about VAPT: One of the most common misconceptions on VAPT is that it is meant only for big companies and not small businesses. In reality, this is not the case. Large, medium and small businesses can all benefit from VAPT. 67% of companies with fewer than 1,000 employees have experienced a cyberattack, and 58% have experienced a data breach. More importantly, it was found that 60% of small businesses that suffer cyberattacks go out of business within 6 months. This shows that small businesses are also targets for cyberattackers, and compared to large businesses, SMEs are easier targets as security is more relaxed. Hence, no matter if you are a small business or large, VAPT is an important ongoing process to ensure that your networks, applications and systems remain secure. Another misconception that businesses may have is that firewalls and antivirus software is sufficient enough to protect their systems, networks and applications. These traditional tools are no longer sufficient to combat the sophisticated and evolving cyber threats. VAPT is an essential proactive security measure that can help businesses identify potential vulnerabilities and fortify your business defenses. Takeaway In the face of relentless cyber threats, vulnerability assessment and penetration testing have become integral components of a robust cybersecurity strategy. These proactive measures enable businesses to identify vulnerabilities, fortify their defenses, and mitigate risks effectively. By adopting vulnerability assessment and penetration testing, organizations can stay one step ahead of cybercriminals, protect their valuable assets, and maintain the trust of their customers and stakeholders. With the benefits of identifying vulnerabilities, enhancing security posture, meeting compliance requirements, safeguarding reputation, and cost savings, businesses cannot afford to overlook the importance of these assessments. Embracing vulnerability assessment and penetration testing as part of a comprehensive cybersecurity program empowers organizations to build a resilient defense against evolving cyber threats, ensuring a secure and resilient digital environment. Vulnerability Assessment and Penetration Testing with TAFA With the current cyber environment, organizations are facing increasingly sophisticated cyber threats. To protect against these threats, it is necessary to utilize cybersecurity solutions that can prevent zero-day and advanced cyber threats and help ensure regulatory compliance. With our vulnerability assessment and penetration testing services, we will help you to identify vulnerabilities and protect your organization from potential security threats. Our comprehensive VAPT service will also evaluate your organization’s security defenses against modern cyber threats, and provide you with actionable insights and recommendations to enhance your organization’s security posture. To learn more information about TAFA’s VAPT services and how we can help your company, do not hesitate to contact us for more information. Related Topics The Common Signs Of Being Cyberattacked 7 Types of Cyber Security Measures SMEs Need to Protect Their Business
Back to Blog
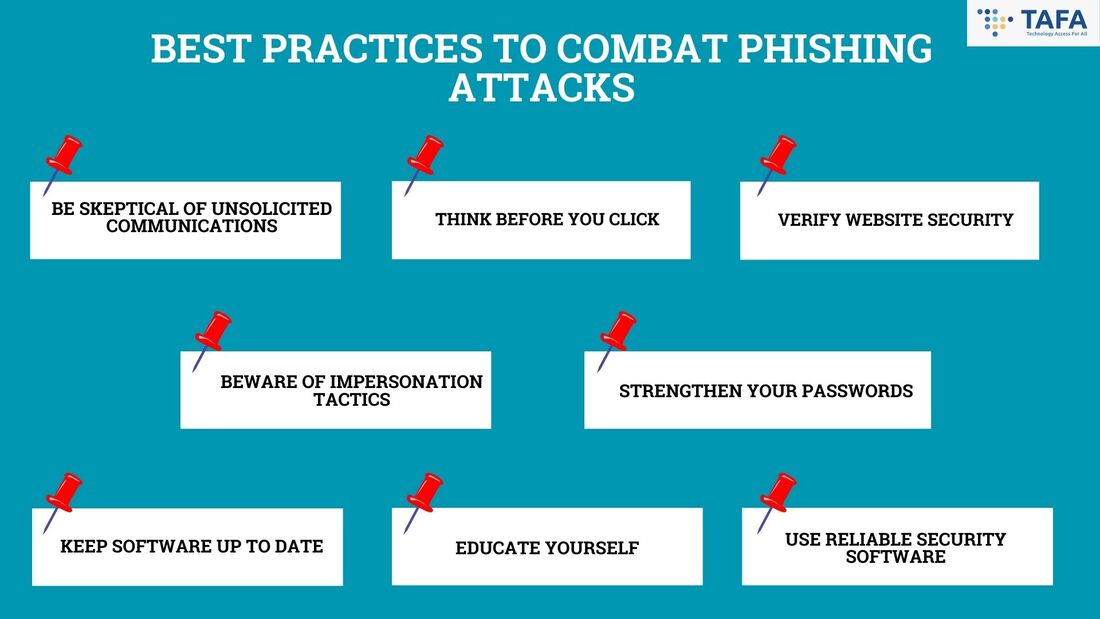
In today's digital world, phishing attacks have become a pervasive threat, targeting individuals from all walks of life. These deceptive attempts to steal sensitive information can have devastating consequences for personal finances, privacy, and online security. In this article, we will explore best practices that everyday people can adopt to defend themselves against phishing attacks and ensure their online safety. 1. Be Skeptical of Unsolicited Communications: Phishing attacks often begin with unsolicited emails, text messages, or phone calls. Exercise caution when encountering such communications, especially if they request personal information, financial details, or account credentials. Always verify the authenticity of the sender before responding or sharing any sensitive data. 2. Think Before You Click: Phishing emails often contain malicious links that can lead to fake websites designed to collect your information. Avoid clicking on links in suspicious emails or messages, particularly those with unexpected or urgent requests. Instead, manually enter the website address in your browser or use bookmarks for trusted websites. 3. Verify Website Security: Before entering any personal or financial information on a website, ensure it is secure. Look for the padlock icon in the address bar and ensure the website's URL begins with "https://" instead of "http://". This indicates that data transmission is encrypted and helps protect your information from interception. 4. Beware of Impersonation Tactics: Phishers often impersonate trusted entities like banks, government agencies, or popular online services. Pay attention to details such as email addresses, domain names, and spelling errors. Legitimate organizations rarely ask for sensitive information via email, so be wary of any requests for passwords, Social Security numbers, or credit card details. 5. Strengthen Your Passwords: Creating strong and unique passwords is crucial in thwarting phishing attempts. Use a combination of upper and lowercase letters, numbers, and special characters. Avoid using easily guessable information like birth dates or common phrases. Additionally, enable two-factor authentication whenever possible to add an extra layer of security. 6. Keep Software Up to Date: Regularly updating your operating system, web browsers, and other software is vital in staying protected against known vulnerabilities. Software updates often include security patches that address potential weaknesses that cybercriminals could exploit. 7. Educate Yourself: Stay informed about the latest phishing techniques and scams. Be aware of the common tactics used by cybercriminals, such as urgent requests for money, prize notifications, or job offers that seem too good to be true. Regularly educate yourself on phishing trends and share this knowledge with friends and family to create a safer online environment for everyone. 8. Use Reliable Security Software: Install reputable antivirus and anti-malware software on your devices and keep them updated. These tools can help detect and prevent phishing attacks, as well as provide real-time protection against various other online threats. Takeaway Phishing attacks continue to evolve, becoming increasingly sophisticated and difficult to detect. By following these best practices, you can significantly reduce your risk of falling victim to these scams. Remember to stay vigilant, think twice before sharing sensitive information, and keep yourself informed about the latest phishing trends. By taking these proactive steps, you can protect your personal information, financial well-being, and online security in an ever-changing digital landscape. Related Topics The Rise Of Phishing: Safeguarding Against Digital Deception The Common Signs Of Being Cyberattacked 7 Types of Cyber Security Measures SMEs Need to Protect Their Business
Back to Blog
Last week, there were data breaches and ransomware attacks from a range of industries and countries, with a few resulting in personal information of victims being leaked. Furthermore, an advisory from the US and Canada has been issued in regards to the rising usage of malware variants, and new patches have been released to address the vulnerabilities found in MOVEit Transfer. Not only that, companies that breached privacy and security laws were fined. To add on, new ransomware and malware have been discovered.
Read on to receive a quick summary of what happened this week in the space of cybersecurity. Japan’s largest and busiest port suffers a ransomware attack. The Port of Nagoya has suffered a ransomware attack, and the attack has currently impacted the operation of container terminals. The administrative authority of the Port of Nagoya issued a statement on 5th July on the malfunction in the “Nagoya Port Unified Terminal System” (NUTS), which is the central system controlling all of their container terminals. They stated upon investigating the cause, the issue was due to a ransomware attack. Operations at the port have gradually resumed after an outrage of more than 48 hours - with operations at one cargo terminal resumed on Thursday at 3pm. The association stated that they aim to restart another terminal by 5:30pm, and the three others by 6:30pm. The longer than anticipated restoration of the port was due to the large amounts of deleted data they needed to recover. More than 34 million Indonesian passport holders leaked. A cybersecurity researcher, Teguh Aprianto, has found that the data of 34.9 million Indonesian passport holders at the Immigration Directorate General have been reportedly breached by a hacker, Bjorka. The 4GB of data was offered for sale for US$10,000. The leaked data include full names, passport numbers, expiry dates, birth dates and gender. The ministry’s Director General for Applications and Informatics, Semuel A. Pangerapan stated that their investigation has not yet concluded that there is in fact a data leak, and that the results of the investigation would be announced soon. 2 Swedish companies fined $1.1 million for using Google Analytics data transfer to the U.S. The Swedish Authority for Privacy Protection has fined 2 companies US$1.1 million for using Google Analytics and have warned 2 other companies for the same thing. The agency explained that the firms breached the European Union’s General Data Protection Regulation (GDPR) via using Google Analytics to generate web statistics. Specifically, the firms violated GDPR Article 46(1), which forbids the transfer of personal data to countries or international organizations that lack safeguards that warrant safety and legal remediation mechanisms. The Court of Justice of the European Union has deemed the United States as a risky location for the storage of data of European users, and that any data transfers to the U.S in the context of the then-existing mechanism, “Privacy Shield” were illegal. Furthermore, the agency stated that the technical security measures these firms have taken are “”not sufficient to ensure a level of protection that essentially corresponds to that guaranteed within the EU/EEA”. Capita’s pension fund suffers data breach during March cyberattack. Members of Capita’s pension fund have been notified that their data has been stolen during a cyberattack in March on the outsourced company that provides administration services. The notification was sent to Capita’s pension fund members more than 3 months after the hack. In May, early investigations indicated that 4% of its servers were accessed during the 9 days the criminals were in the servers, but later the outsourcer revised this to 0.1% and also admitted that it had “evidence” customer data was stolen. Capita administers 450 pension schemes with 3.5 million members. The outsourcing company warned the members of the potential unauthorised access to their data on servers that were breached during the cyberattack. Capita is already facing their first legal claim over the data breach, with law firm Barings Law sent a Letter of claim to Capita last month. Nickelodeon suffered a data breach - ‘Decades old’ data leaked. Nickelodeon has confirmed that they had suffered a data breach which caused a data leak whereby some of it appears to be decades old. Proof of the data leak started circulating on social media, which reportedly has 500GB in documents and media files. A Nickelodeon spokesperson has stated that there is an investigation currently underway, and that the files leaked does not appear to be from the recent breach of their systems. Also they had assured that the leaked data does not contain user or employee data, and the leaked data is limited to production resources and other intellectual property. Over 130,000 solar panels are exposed online. Security researchers warned that tens of thousands of PV monitoring and diagnostic systems are easily reachable on the public web, making them potential targets for cybercriminals. Cyble’s threat analysts found 134,634 products from various vendors exposed. The vendors include Solar-Log, Danfoss Solar Web Server, SolarView Contec, SMA Sunny Webbox, SMA Cluster Controller, SMA Power Reducer Box, Kaco New Energy & Web, Fronis Datamanager, Saj Solar Inverter, and ABB Solar Inverter Web GUI. Their research shows that unauthenticated visitors can find information including settings that could be used to organize an attack. Exploiting vulnerabilities in the PV systems has happened recently, hence these vulnerabilities found for the above products should not be taken lightly. Bangladesh citizen’s personal data leaked by Bangladesh government website. A Bangladeshi government website has leaked the citizen’s personal information which include, full names, phone numbers, email addresses and national ID numbers. Viktor Markopoulos, a researcher who accidentally discovered the leak, has said that the leaked data included data of millions of Bangladeshi citizens. TechCrunch was able to verify the leaked data as legitimate. Markopoulos even stated that the data “was too easy” to find as they just appear as Google results. On Sunday, the State Minister of Information and Technology (ICT), Junaid Ahmed Palak, acknowledged the data leak and assumed full responsibility for the data breach. He also emphasized the need to address the issue promptly. U.S and Canadian authorities warn about rising Truebot malware variants. U.S and Canadian authorities - the CISA and CCCS - issued a joint advisory last Thursday about the increasing widespread use of Truebot malware variants that are being utilized by threat actors against organizations in these 2 countries. Truebot is a botnet used by malicious cyber groups such as the Clop ransomware gang. Newer versions of the malware allow threat actors to gain initial access via the exploitation of a remote code execution vulnerability in Netwrix auditor - listed as CVE-2022-31199. Threat actors also use phishing campaigns with malicious links to deliver their Truebot variants. MOVEit Transfer customers warned to patch new critical flaws. MOVEit transfer, the epicenter of the recent massive spread of Clop ransomware breaches, has got an update that would fix a critical-severity SQL injection bug and 2 other less severe vulnerabilities. This SQL injection vulnerability would allow an unauthenticated attacker to gain unauthorized access to the MOVEit transfer database, as well as modify and disclose the database content. Users of MOVEit transfer are highly recommended to upgrade to the new available versions to help address the vulnerabilities found. New information stealer - Meduza Stealer discovered: Targets 19 password managers and 76 crypto wallets. Cybersecurity researchers have discovered a new Windows-based information stealer - Meduza Stealer that is being actively developed to evade detection by software solutions. Uptycs stated that “the Meduza Stealer has a singular objective: comprehensive data theft”. He stated that no digital artifact is safe, from login credentials to your browsing history, to even your crypto wallet extensions, password managers and 2FA extensions. Medeuza Stealer gathers data from 19 password managers, 76 crypto wallets, 95 web browsers, Discord, Steam, system metadata, harvests miner-related Window Registry entries and list of installed games. It is currently offered for sale on the dark web and on a dedicated Telegram channel. New ‘Big Head’ ransomware spread through fake Windows updates and Microsoft Word installers. Security researchers have analyzed a recently emerged ransomware strain called ‘Big Head’ that may be spreading via the promotion of fake Windows updates and Microsoft Word installers. ‘Big Head’ ransomware installs 3 AES-encrypted files on the target system - the first file is used to propagate the malware, the second file for Telegram bot communication, and the third files encrypts files and can also show the user a fake Windows update. During the encryption process, the ransomware displays a screen that looks like a legitimate Windows update. After the encryption process is completed, the victim’s wallpaper will be changed to alert of the infection, and ransom will be dropped on multiple directories. Other variants of this ransomware have also been found with some differences. One variant has the capability to collect and exfiltrate sensitive data from the victim’s system, and another inserts malicious codes on the breached system although the exact purpose of this is currently unknown. Trend Micro commented that Big Head is not a sophisticated ransomware strain. However, it appears to focus on consumers who can be easily fooled with easy tricks such as the fake Windows update or those who have difficulty understanding the safeguards necessary to avoid the cybersecurity risks. |
|
© 2021, TAFA HOLDINGS (S) PTE LTD. ALL RIGHTS RESERVED
|

 RSS Feed
RSS Feed