AuthorTAFA Archives
April 2024
Categories
All
|
Back to Blog
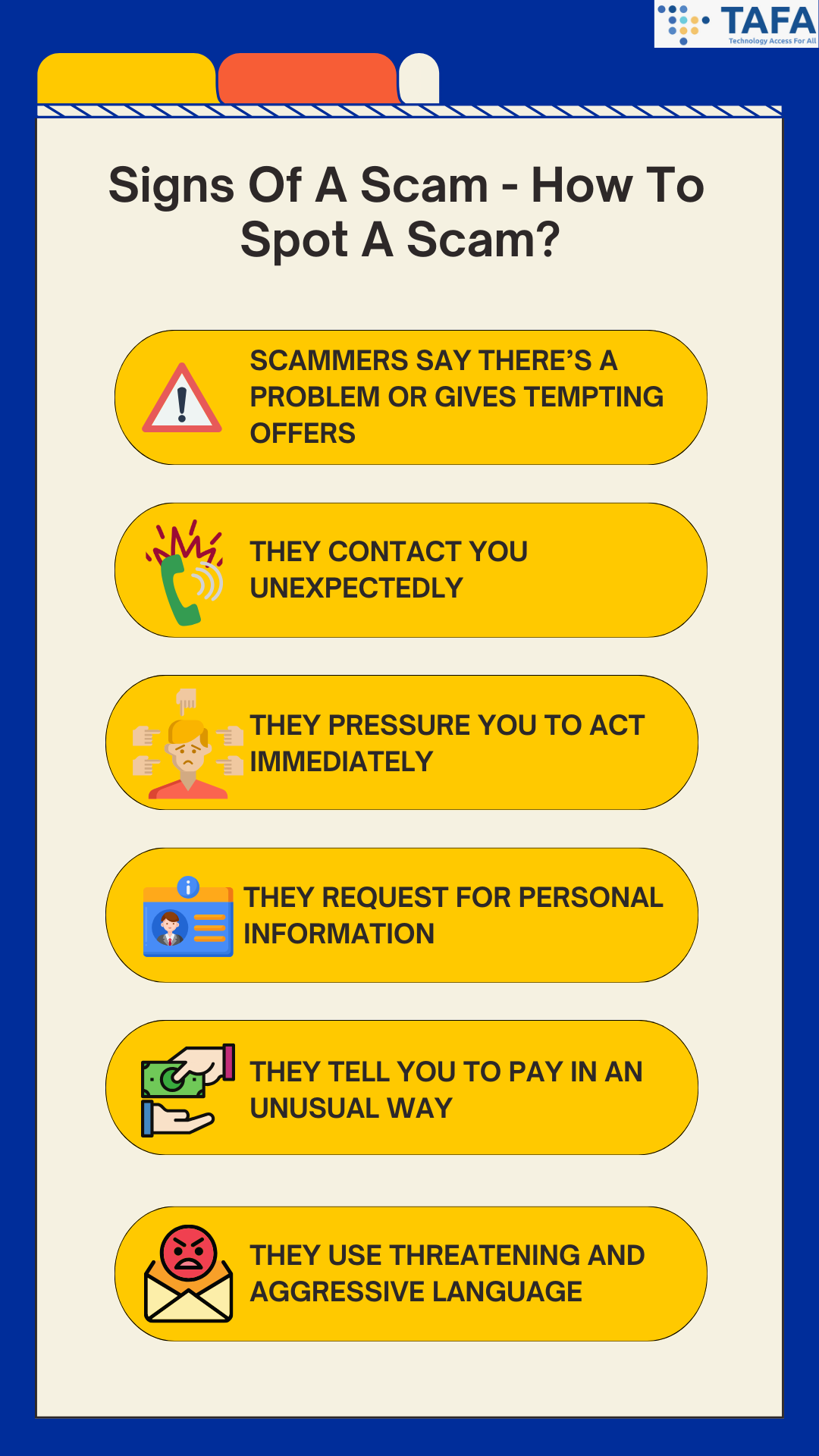
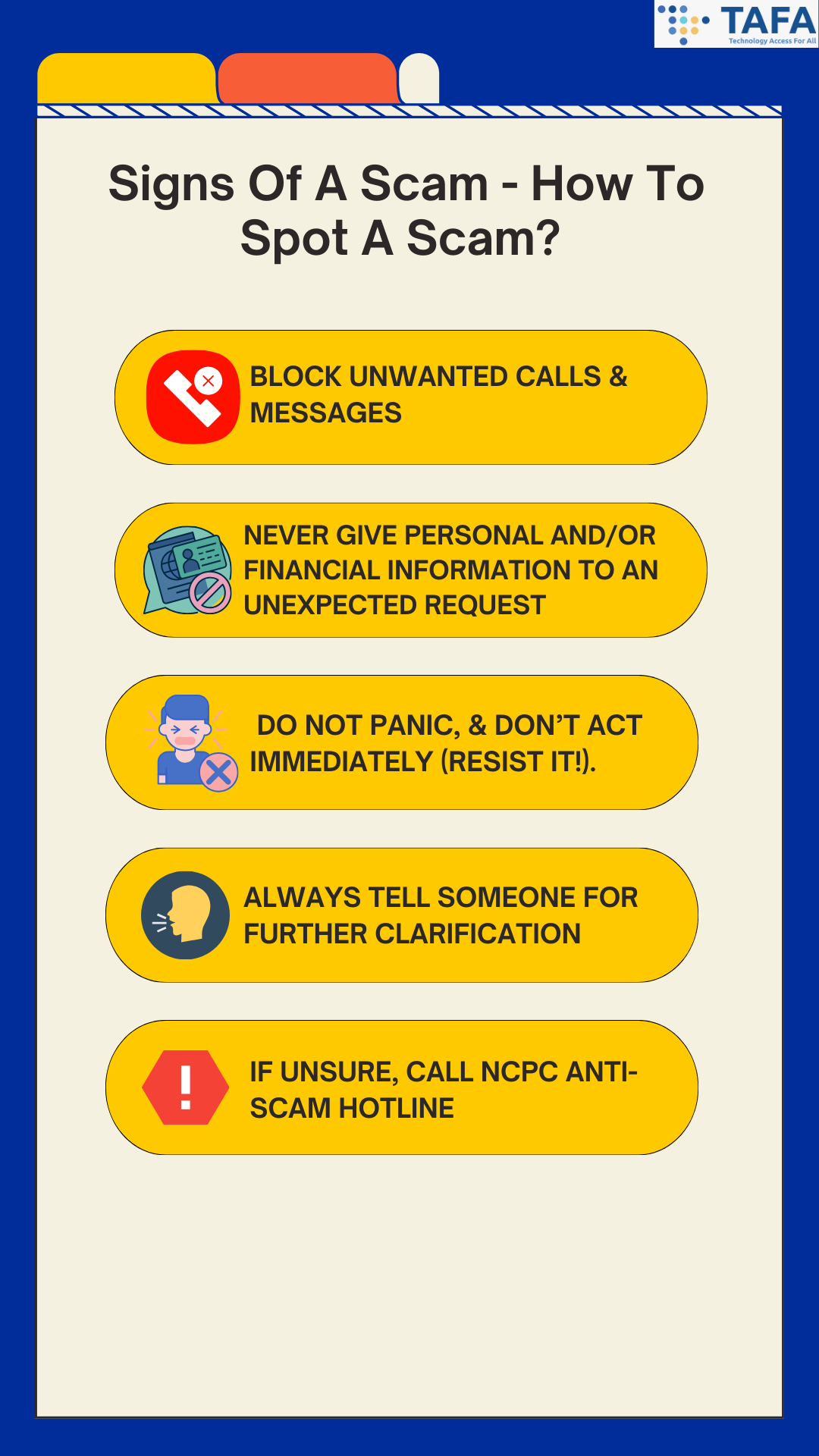
In the vast landscape of the internet, deception often lurks behind enticing offers and too-good-to-be-true deals. Scams have evolved into sophisticated forms, but so has our ability to recognize and thwart them. Read on to find out how to recognise the signs, and avoid getting scammed. Signs Of A Scam - How To Spot A Scam? 1) Scammers say there’s a problem or gives tempting offers Scammers might say you are in trouble with the government, money is owed, there’s a problem with your account (be it social media, email or banking accounts), a computer virus has been detected or someone in your family had an emergency. Or alternatively, they give you tempting offers - e.g. deals that are price way below market rates. If it sounds too good to be true, it probably is! This sign tends to appear in scams such as loan scams, e-commerce scams. Investment scams, job scams, and money laundering scams. 2) They contact you unexpectedly One of the easiest ways to spot a scammer is that they will tend to contact you first. If you receive any unexpected emails, messages or phone calls from someone you don’t know, it is best to verify they are who they said they are by contacting their business or agency directly. If you are not 100% convinced by the identity of the caller, hang up and contact the company directly. 3) They pressure you to act immediately Pressure can take all sorts of forms, the most common ones are asking you to act immediately before it’s too late (as you might get arrested, sued etc.), deals presented as limited time only or an urgent flash deal. Basically pressuring you into acting fast before you miss out. Scams use a sense of urgency to pressure you into either divulging your personal information or making fund transfers. They want you to react emotionally, instead of rationally. Instead of acting immediately, pause and think. Maybe even do a little bit of research. There is no need to act or decide immediately, as the only thing you might be missing out is being scammed. 4) They request for personal information Scammers are able to disguise themselves and create believable personas that will trick you into giving over sensitive personal and financial information, such as your PIN, OTP, account name and password. Scammers can disguise themselves as a government official or from a legitimate business, and there are scammers who impersonate your friends and family by taking over their accounts. 5) They tell you to pay in an unusual way For instance, they will ask you to pay via apple vouchers or through transfer services like oneyGram or Western Union. 6) They use threatening and aggressive language Along with urgency, scammers will also use threats to convince you to do what they say. Often, they will impersonate the police, FBI or tax collector, and threaten that you will be arrested. How To Avoid A Scam 1) Block Unwanted Calls & Messages. Do not reply to these unwanted calls and messages. 2) Never Give Personal and/or Financial Information To An Unexpected Request. Usually businesses and government agencies will not call, text or email you to ask for your sensitive personal information such as your bank account number, accounts, credit card numbers, PIN, your NRIC etc. 3) Do Not Panic, & Don’t Act Immediately (Resist it!). Businesses will give you time to make a decision. Anyone who pressures you to give them your sensitive personal information or to pay are scammers! 4) Always Tell Someone For Further Clarification. Before any action is taken, it is best to tell someone (e.g. family, friend, neighbour) about what happened. 5) If Unsure, Call NCPC Anti-Scam Hotline at 1800-722-6688. In Singapore, if you have any doubts or suspicions about a potential scam, you can seek a second opinion with the National Crime Prevention Council (NCPC) Anti-Scam hotline via calling them or by checking their website for further information. *This is only valid in Singapore. Conclusion In a digital world teeming with opportunities and pitfalls, our vigilance becomes the shield that guards against deception. By recognizing the subtle signs of scams and maintaining cyber hygiene, we fortify ourselves against malicious intentions. Let us navigate the online realm with discernment and wisdom, ensuring our digital lives remain secure and thriving. In the face of scams, knowledge is not just power—it's our strongest defence. Stay informed, stay safe, and together we can unmask deception. Related Topics A Personal Cybersecurity Checklist - How Cyber Secure Are You? 12 Tips For A Safer Online Shopping: How To Avoid Falling For Online Shopping Scams Password Security Tips: How To Fortify Your Password Security What is Multi-Factor Authentication (MFA) & Why Does It Matters?
Back to Blog
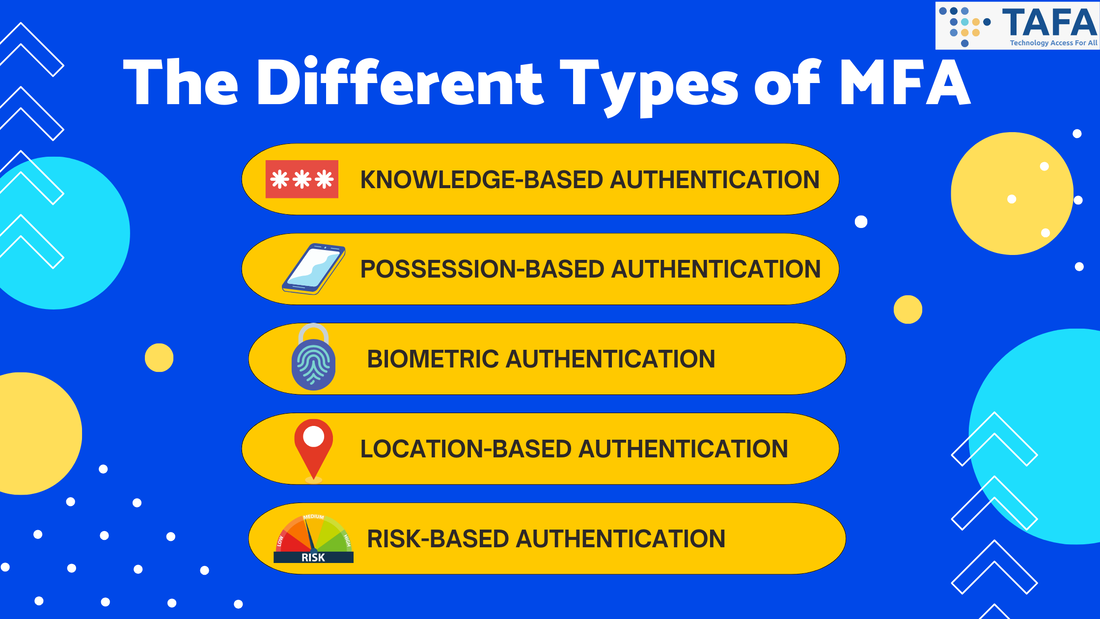
In a world where our lives are increasingly intertwined with the digital realm, fortifying our online presence has never been more critical. Passwords, once the stalwart guardians of our virtual kingdoms, are no longer enough to thwart the nefarious ambitions of cyber intruders. Enter Multi-Factor Authentication (MFA), a digital sentinel that provides an extra layer of protection. In this article, we unravel the mystery of MFA, illuminate its paramount importance in the modern era of cybersecurity, and provide instances of when the implementation of MFA is essential. What Is Multi-Factor Authentication (MFA)? MFA is a security measure that requires two or more verification vectors to gain access. MFA is a strong component of a strong identity and access management policy. Common examples of MFA include personal devices such as security tokens, biometrics, SMS authorisation codes and authenticator apps. By requiring one or more additional authentication vectors, this decreases the likelihood of a successful cyberattack. Most MFA authentication methodology is usually based on 1 of 3 types of additional information: something you know (like a password or PIN), something you have (like a mobile device), and something you are (biometrics like a fingerprint). Why Does MFA Matters? MFA helps you to escape from single-point vulnerability. Through the incorporation of various authentication factors, MFA mitigates the risk associated with a single compromised password. Especially now, authentication based on just your username and password is unreliable due to the fact how easily they can now be acquired by threat actors via hacking, phishing and malware. Furthermore, MFA is dynamic as it can adapt to evolving threats via offering a flexible security framework that remains robust against a plethora of attack vectors. The Different Types Of MFA
When Should I Use MFA? It is highly recommended to turn on MFA wherever possible, starting with very important accounts. Examples include:
Conclusion Multi-Factor Authentication stands as a sentinel guarding the gates to our digital lives. In this dynamic landscape of cyber threats, a single password is no longer sufficient to protect our valuable data. MFA, with its multifaceted approach, ensures that even if one defence falters, another stands strong. MFA is a necessity in fortifying our digital existence and standing firm against the tide of cyber threats. Remember, in the world of cybersecurity, it’s not just about having the key; it’s about having the right combination to unlock the future securely. Related Topics A Personal Cybersecurity Checklist - How Cyber Secure Are You? 12 Tips For A Safer Online Shopping: How To Avoid Falling For Online Shopping Scams Password Security Tips: How To Fortify Your Password Security What to Do When You've Fallen for a Phishing Scam The Risks of Public Wi-Fi & Tips On How To Stay Safe Is This QR Code Safe? Top Tips to Ensure Your QR Scans are Secure
Back to Blog
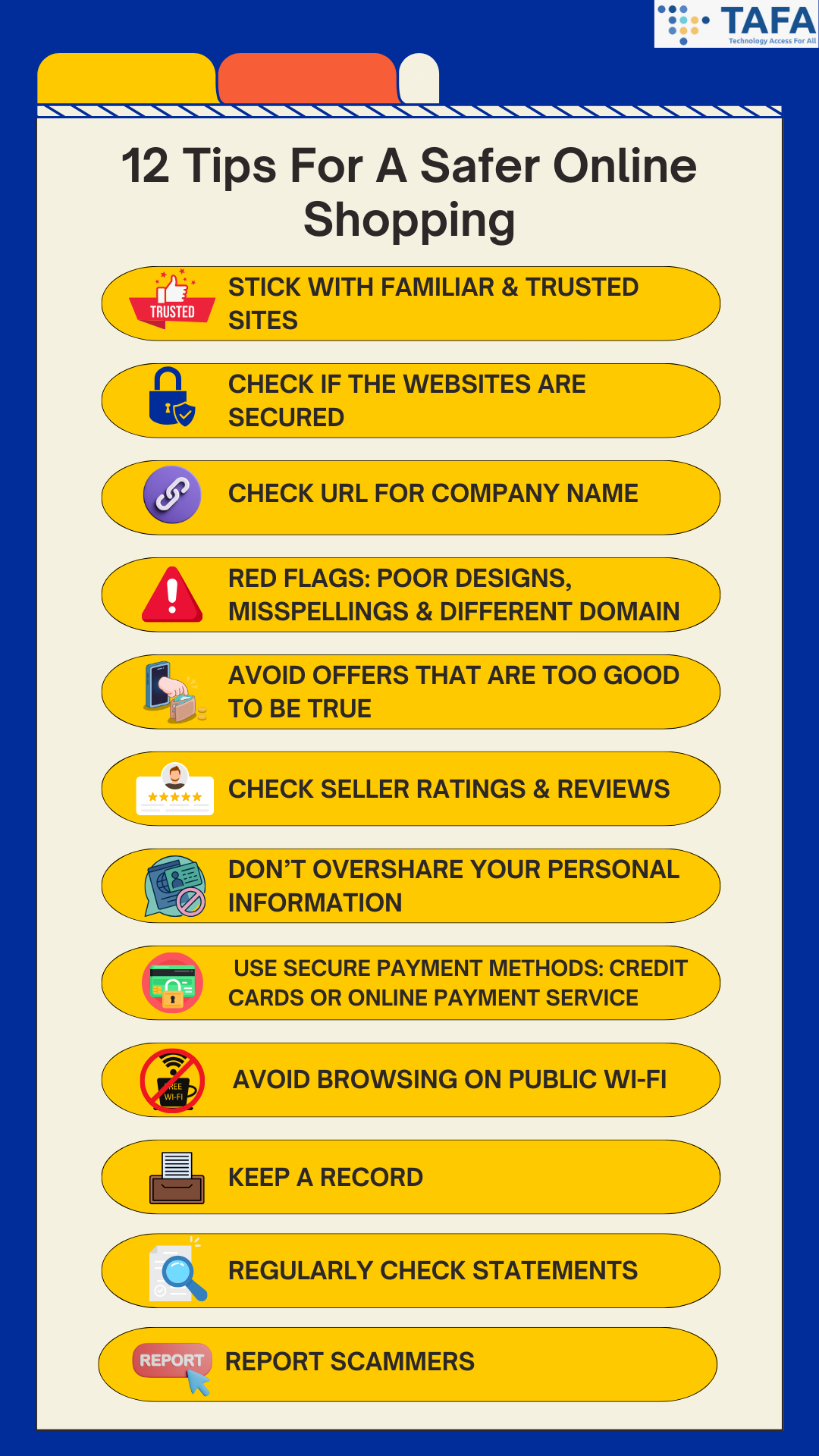
Online shopping has made possibilities endless. From the comfort of your home, you can browse, choose, and purchase anything you desire. However, as the digital marketplace expands, so do the perils that come with it. There are many threats that lurk online, and one such threat are online shopping scams (which can also be known as ecommerce fraud). From stealing personal and financial information to bogus returns, the highest numbers impacted by online shopping scams are consumers. Tips To Protect Yourself Against Online Shopping Scams 1) Stick With Familiar & Trusted Sites
It is highly recommended to shop directly from online retailers that you are familiar with and trust. Avoid typing the name of the retailer into your browser bar, as a tiny typo can lead you to a fake site that imitates the real one. These fake sites may lead you to divulging personal and financial information. It is best to bookmark your trusted and familiar sites to ensure you are going to their legitimate sites. 2) Check If The Websites Are Secured Remember ‘S’ stands for SECURE. Before you visit an e-commerce site, the first thing you must do is to inspect the URL of the page. Secure sites use HTTPS, and not HTTP. This indicates a secure, encrypted connection. A padlocked symbol should also appear at the address bar. This means that you are safely connected to the website. Ensure to share sensitive information (such as your personal and payment details) ONLY on official secured websites. However, this does not mean that you are completely safe, as many phishing sites do use HTTPS. 3) Check URL For Company Name In addition to checking for HTTPS, check the URL to ensure that the company name is included, and ensure that the company name is spelt correctly. This will help you determine if the site is actually operated by said company or it’s a scam site. 4) Red Flags: Poor Designs, Misspellings & Different Domain Check and recognize for signs of potentially fraudulent websites such as misspelt words, typos, unprofessional designs, and low resolution images. If the website does not contain any branding, be cautious of the website. Also beware of scam sites that will use different top-level domains (e.g. using .net instead of .com). 5) Avoid Offers That Are Too Good To Be True Do you always see ads on your social media that offer huge discounts, way cheaper than usual products, or free offers which you only have to pay shipping for? This is a common tactic that cybercriminals use to bait unsuspecting shoppers with incredible deals to entice them into falling for their scams. It is also recommended to compare prices before buying - as unusually low prices could alert you that this website could be a scam. Remember if an offer looks too good to be true, it usually is! 6) Check Seller Ratings & Reviews If you don’t know the online store, it is best to conduct background checks via looking at sites that review and rate e-stores. If there are no reviews of the e-store or do not have good ratings, it is best to steer clear from the e-store, and don’t order from them. 7) Don’t Overshare Your Personal Information No online shopping retailer will need your social security number, internet banking details and/or OTP. If a site requests this kind of sensitive information, EXIT the site immediately! As if they get your sensitive information, and credit card number, they can steal your identity. A good rule of thumb is to provide reputable websites as minimal information necessary to complete a purchase. 8) Use Secure Payment Methods: Credit Cards or Online Payment Service Always use a credit card or an online payment service such as Paypal or Google Wallet, instead of a debit card. As these payment methods do not give the seller direct access to your bank account. Furthermore, most credit cards do offer payment protection. This means that you will face zero liability for fraud. If you want to have added security, you can use a virtual credit card. As virtual credit cards generate a unique card number for each transaction made, hence protecting your real account number. Even if a cybercriminal got your virtual credit card number and attempted to use it, they won’t be able to. 9) Avoid Browsing On Public Wi-Fi Public Wi-Fi networks often lack a security measure - encryption, which encrypts your information sent from your device or computer to the router so strangers cannot read it. Without encryption, your information (e.g. your passwords, identity and financial information) that is sent over these networks can be intercepted by cybercriminals. If you have no choice but to use public Wi-Fi, it is highly recommended that you use VPN (virtual private network) to protect your privacy. As VPN helps encrypt the traffic between your device and the VPN server, which means that cybercriminals will find it much more difficult to obtain access to your data on your device. 10) Keep A Record Always keep records of your online transactions. Ensure to save the receipts, order confirmation number, tracking number, product description and price. It is also a good idea to save all emails you receive and send to the seller. As this will come into use if there is an issue later on. 11) Regularly Check Statements Do a weekly regular check of your bank and credit/debit card statements for any fraudulent charges. Do not wait for your bills to come at the end of the month! It is highly recommended to also set up alerts for any new activity on your card - this helps to keep up on top of any new charges made to your accounts. 12) Report Scammers Do not ever feel embarrassed for being scammed. Instead get very loud about it. (a) Contact the platform’s support team for assistance. (b) File a police report. In Singapore, you can file a report via calling the police hotline at 1800 255 0000, or using the I-Witness eService, or file at any nearest Neighbourhood Police Centre or Post. (c) Lodge a complaint with the Consumers Association of Singapore (CASE) Conclusion In the labyrinthine world of online shopping, vigilance and knowledge are your best allies. By arming yourself with information, staying cautious, and implementing best practices, you can navigate the digital marketplace with confidence and keep the predators of the virtual world at bay. Let your online shopping adventures be fruitful and secure, guarded by the wisdom imparted in this guide. Remember, in the digital realm, knowledge is power, and prudent choices are your most potent defence. Happy shopping! Related Topics A Personal Cybersecurity Checklist - How Cyber Secure Are You? Safeguarding Your Digital Fortress: Defending Against the Top 8 Password Attacks Password Security Tips: How To Fortify Your Password Security The Risks of Public Wi-Fi & Tips On How To Stay Safe Is This QR Code Safe? Top Tips to Ensure Your QR Scans are Secure Unmasking Phishing: Your Guide to Spotting The Signs of Phishing
Back to Blog
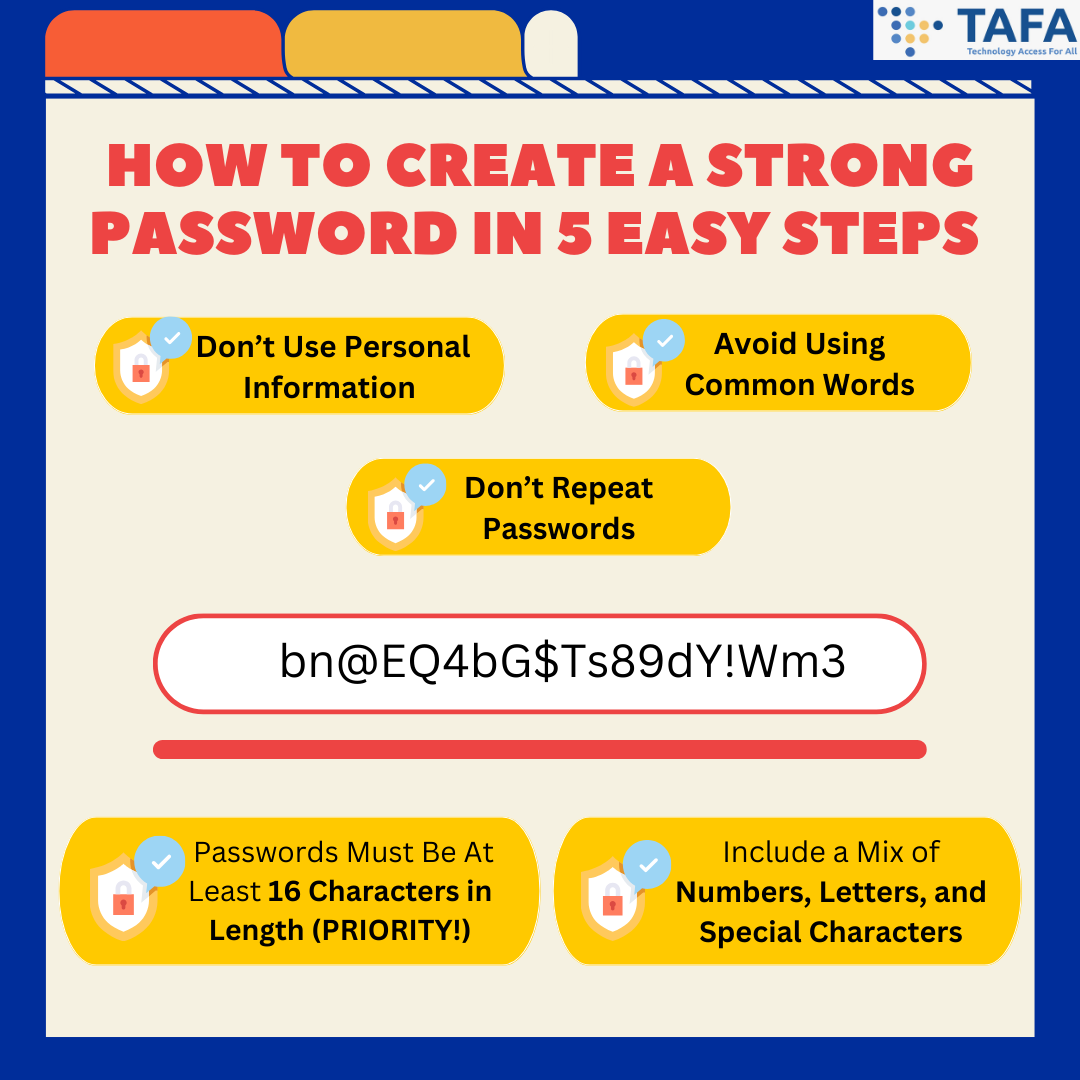
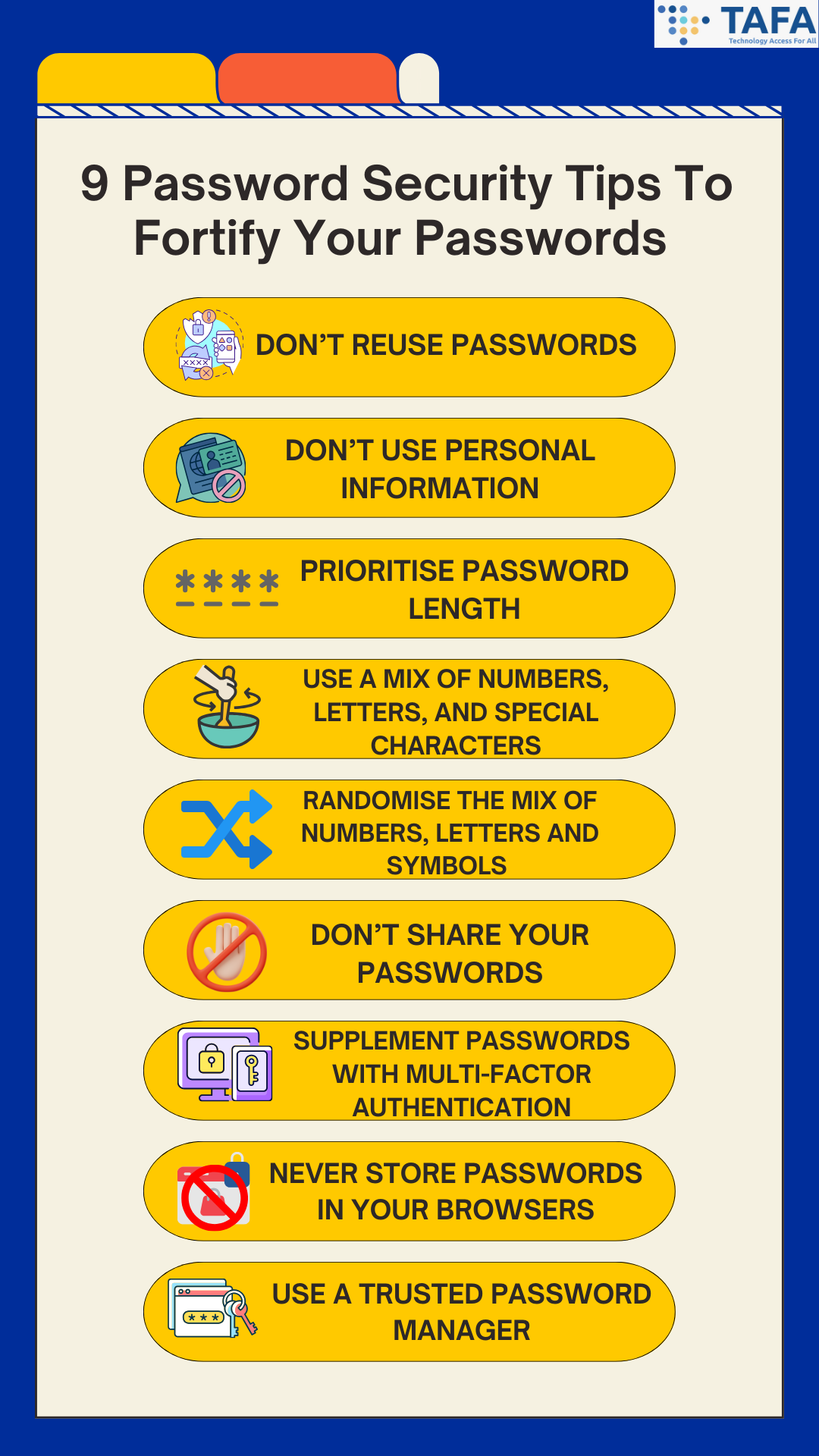
In the labyrinthine world of cyberspace, where opportunities abound, dangers also lurk. Your online identity is akin to a precious treasure, one that needs the staunchest defence. Passwords, the keys to protecting your online digital life, demand particular attention and vigilance. How do I create a strong password? How do I improve my password security? Don’t worry, this article is here to help you. We will first guide you on how to create a strong password, and then we will list down password security tips that can be easily followed to ensure you can fortify your security, thus helping you live a more cyber safe lifestyle. Why Do I Need Strong Passwords? You may wonder: why do I need strong passwords anyway? The reality is that even though most websites are secure, there is always a chance that cybercriminals may try to access or steal your personal information. Hence, password security is of utmost importance, especially with the consequences of what could happen if you have weak password security, such as identity theft and data breaches. To learn more about the top 8 types of password attacks, click here. A strong password is one of the best ways to defend your accounts and sensitive information from cybercriminals. How To Create A Strong Password In 5 Easy Steps 1. Don’t Use Personal Information. Never include personal information in your passwords, such as names and birthdates of your relatives, child or pets, phone numbers or phone numbers. As this information can be easily found especially on social media. Don’t make it easy for hackers to guess your passwords! 2. Include a Mix of Numbers, Uppercase and Lowercase Letters, and Special Characters. Strong passwords should be complex and include a combination of numbers, letters, and special characters. Ensure that there are no repetitive or sequential characters (e.g. ‘eeeeee’, ‘123abc’). 3. Passwords Must Be At Least 16 Characters in Length. Password length is extremely important as the longer the password, the less chance of hackers can easily crack your passwords. It is recommended that your passwords should be at least 16 characters in length. 4. Avoid Using Common Words. In common words, it is best to substitute letters with numbers and special characters (e.g. punctuation marks and/or symbols). Hackers can use malicious programs to process every word in the dictionary to crack passwords. 5. Don’t Repeat Passwords, Like Ever. Reusing the same password for different accounts will put you at risk of credential stuffing attacks, which is essentially where cybercriminals use the stolen usernames and passwords and test them against multiple sites. 9 Password Security Tips To Fortify Your Passwords Utilise these password security tips to help you improve your cyber security, and help you live a more cyber safe lifestyle. 1. Don’t Reuse Passwords. Recycling passwords will put you at risk of credential stuffing attacks.
2. Don’t Use Personal Information. Never use names, birthdates, addresses or phone numbers in your passwords as this information can be easily found. This jeopardises the effectiveness of passwords against cyberattacks. 3. Prioritise Password Length. As length trumps complexity. The longer your password length is, the harder it is for cybercriminals to guess your password. As there are more possible permutations, making it harder for cybercriminals to crack. It is recommended that passwords should be at least 16 characters long. 4. Use A Mix of Numbers, Uppercase and Lowercase Letters, and Special Characters. Create a password that is at least 12 characters long, which includes a mix of uppercase, lowercase, numbers and special characters. This will help you create a strong unique password which is the blueprint to a rock-solid cybersecurity abode. 5. Randomise the Mix of Numbers, Uppercase and Lowercase Letters, and Special Characters. Ensure to randomise the mix of numbers, letters and special characters to protect against password spraying attacks, which is a hacking technique whereby cybercriminals use a list of frequently chosen passwords to guess the passwords of their potential victim. 6. Don’t Share Your Passwords. Never tell anyone your passwords even to family and friends, and be especially cautious of emails or messages that are trying to persuade you via urgency, to reveal your passwords. Usually it is a trick! 7. Supplement Passwords With Multi-Factor Authentication (MFA). Passwords should not be the sole method for authenticating an identity or verifying access authorisations. It is best to include MFA, such as biometrics or one-time codes as an additional layer of security and protection. 8. Never Store Passwords In Your Browsers. Many browsers do give the option of saving your passwords. Although this seems convenient, it is poor password management. Cybercriminals can access and steal these saved passwords via manipulation of cookies. 9. Use a Trusted Password Manager. Password managers are a secure way to store all your passwords as they help generate and remember different complex passwords for all of your accounts, and encrypt them for additional security. Conclusion In the vast digital realm, your passwords are the sentinels guarding your virtual kingdom. By understanding their significance, crafting robust defences, and employing best practices, you can reinforce these sentinels, ensuring a formidable defence against potential invaders. Let your online presence be a citadel, unassailable and secure. Embrace the art of password security, for in this age of digital innovation, your safety is the ultimate treasure worth protecting. Venture forth into the digital wilderness with wisdom, and may your passwords be your invincible guardians. Related Topics A Personal Cybersecurity Checklist - How Cyber Secure Are You? Safeguarding Your Digital Fortress: Defending Against the Top 8 Password Attacks The Risks of Public Wi-Fi & Tips On How To Stay Safe Is This QR Code Safe? Top Tips to Ensure Your QR Scans are Secure Unmasking Phishing: Your Guide to Spotting The Signs of Phishing
Back to Blog
In the vast ocean of the internet, phishing scams are the lurking predators waiting for an unsuspecting click. Despite our best efforts to stay vigilant, it's possible to fall into the trap of a phishing scam. Fear not! This article will guide you on what to do if you find yourself fallen for a phishing scam. What is Phishing? Phishing is one of the most popular and common cyber scams, whereby cybercriminals either send malware or steal your sensitive information by pretending to be a legitimate sender (i.e. online store, a bank, your family or friends). Phishing is a form of social engineering, which means that cybercriminals use psychology to convince their victims to take an action they may not normally take. Here is a guide to spot the signs of phishing, click here. What To Do If I Fell For A Phishing Scam Here are some simple steps you can take: 1) Change Affected Passwords
Immediately change the passwords for the affected accounts to prevent further unauthorised access. It is also best to change all accounts' passwords (if you can). Ensure that your passwords are strong and unique for extra security. They must be at least 12 characters long, which includes a mix of uppercase, lowercase, numbers and special characters. 2) Enable Multi-Factor Authentication (MFA) MFA isn't just an option; it's a necessity. By using another form of ID, such as security tokens, biometrics, SMS authorisation codes or authenticator apps will help add an extra layer of security. This will make it harder for hackers to gain unauthorised access to your online accounts, even if they steal your password. 3) Contact Affected Institutions If you share any financial information (such as your bank account number, passwords, PIN number), notify your bank and credit card companies. This can help you recover any lost finances but also prevent any further losses. The bank and credit card providers will also monitor for any suspicious transactions. It is also important to alert relevant social media platforms and request assistance in securing or closing compromised accounts. 4) Scan your device for malware or viruses If there was a suspicious link or attachment in the email or text message, it is best to run a thorough scan of your device to detect and remove any malware or viruses that might have been downloaded during the phishing incident. 5) Report the Phishing Incident If you have incurred monetary loss, loss of personal information, or discovered that your online account has been compromised or hacked, file a police report IMMEDIATELY. In Singapore, you can file a report via calling the police hotline at 1800 255 0000, or using the I-Witness eService, or file at any nearest Neighbourhood Police Centre or Post. If you are in Singapore and need to seek any scam-related advice, you can call the anti-scam hotline: 1800-772 6688 or visit scamalert.sg 6) Regularly Monitor Your Accounts Keep a close eye on your bank statements, credit reports, and other sensitive accounts for any unauthorised activity. If you notice anything unusual, report it immediately to the respective institution and take necessary action. Conclusion Falling victim to a phishing scam doesn't mark the end of your cybersecurity journey; it's a crucial lesson to learn from. By acting swiftly, reporting the incident, and fortifying your digital defences, you can rise stronger and wiser from the experience. Remember, in the face of a phishing scam, your resilience and proactive response can set you on the path to a safer and more secure online voyage. Stay vigilant, stay educated, and let adversity be the wind in your cybersecurity sails. Related Topics Unmasking Phishing: Your Guide to Spotting The Signs of Phishing The Rise Of Phishing: Safeguarding Against Digital Deception Protect Yourself: Best Practices to Combat Phishing Attack The Risks of Public Wi-Fi & Tips On How To Stay Safe Is This QR Code Safe? Top Tips to Ensure Your QR Scans are Secure
Back to Blog
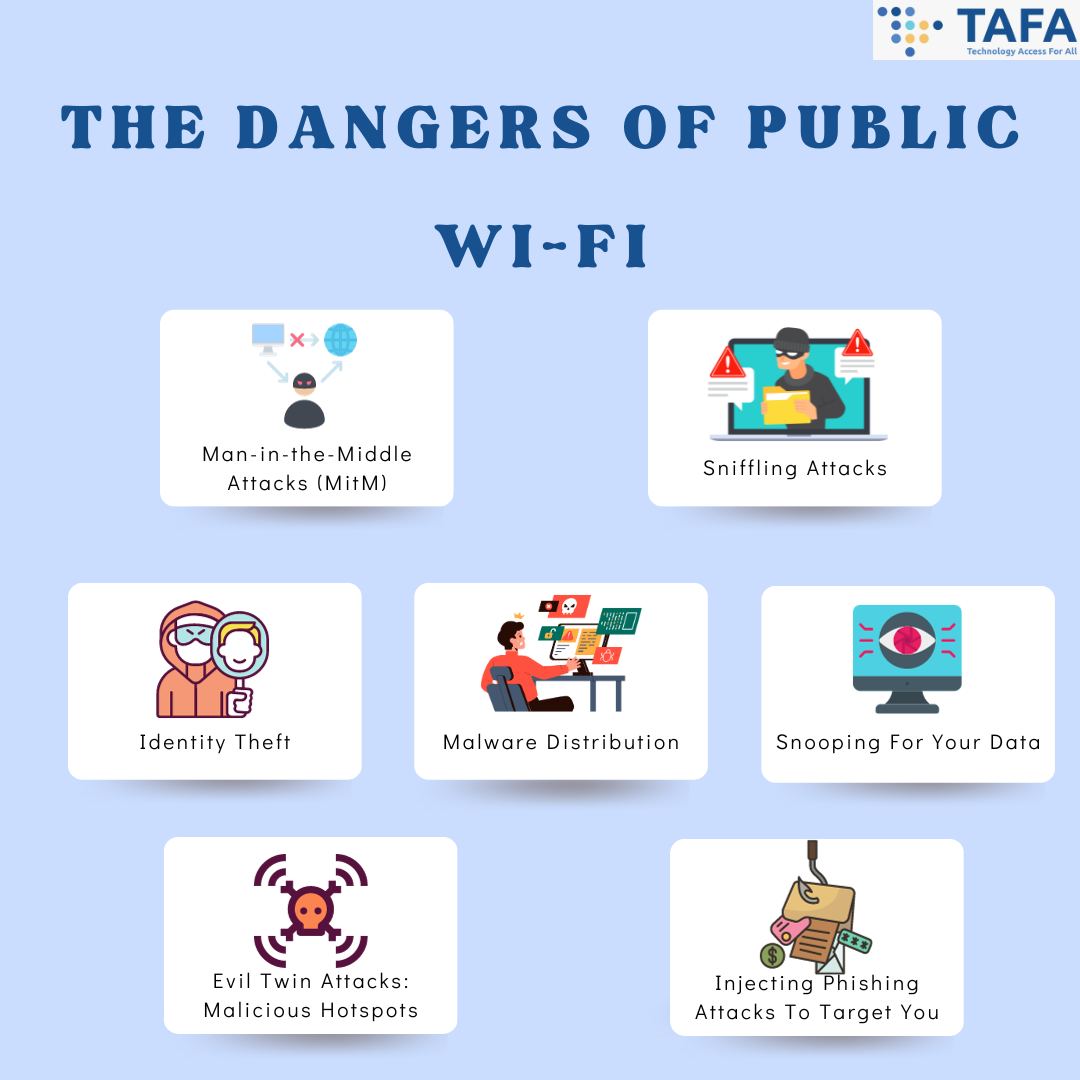
In today's hyper-connected world, public Wi-Fi has become an essential aspect of our daily lives. They are nearly everywhere - whether at a coffee shop, airport, or shopping mall, it's easy to connect to the internet without using our cellular data. However, beneath the convenience lies a shadowy realm of risks, and could leave you vulnerable to cyberattacks. Let’s embark on a journey to unmask the real dangers of public Wi-Fi and how to stay safe on public Wi-Fi when it is necessary. Why Is Public Wi-Fi Not Safe To Use? Public Wi-Fi networks often lack a security measure - encryption, which encrypts your information sent from your device or computer to the router so strangers cannot read it. Without encryption, your information (e.g. identity information, banking, social media accounts and passwords) that is sent over these networks can be intercepted by cybercriminals, they can spy on you, and even take over your online accounts. Did you know? That 43% of respondents had their online security compromised while using public Wi-Fi? This includes either their information being compromised or had malicious software unknowingly installed by the cybercriminals. Furthermore, the majority of respondents had their online security compromised on airport (23%) and cafe/restaurant public Wi-Fi (25%). The Dangers of Public Wi-Fi 1. Man-in-the-Middle Attacks (MitM) This is one of the most common threats in Public Wi-Fi. Essentially, a MitM attack is a form of eavesdropping, whereby bad actors break into a network and “read” the data that is transmitted between the connected devices and the Wi-Fi router. What does this mean? This means that what you thought is private, is no longer private. They can “read” your passwords as soon as you enter into any of your online accounts. 2. Sniffling Attacks Public Wi-Fi networks are a goldmine for hackers who can intercept and analyse unencrypted data packets, which are data units that are sent across unsecured Wi-Fi. This can potentially reveal your sensitive information as they can unpack the data to extract your login credentials or financial information. 3. Identity Theft One of the greatest risks of using public Wi-Fi is getting your identity stolen. Cybercriminals can easily retrieve your information via public Wi-Fi to create targeted cyberattacks and phishing attacks, or enter into your online accounts. What can cybercriminals do via public Wi-Fi? They can:
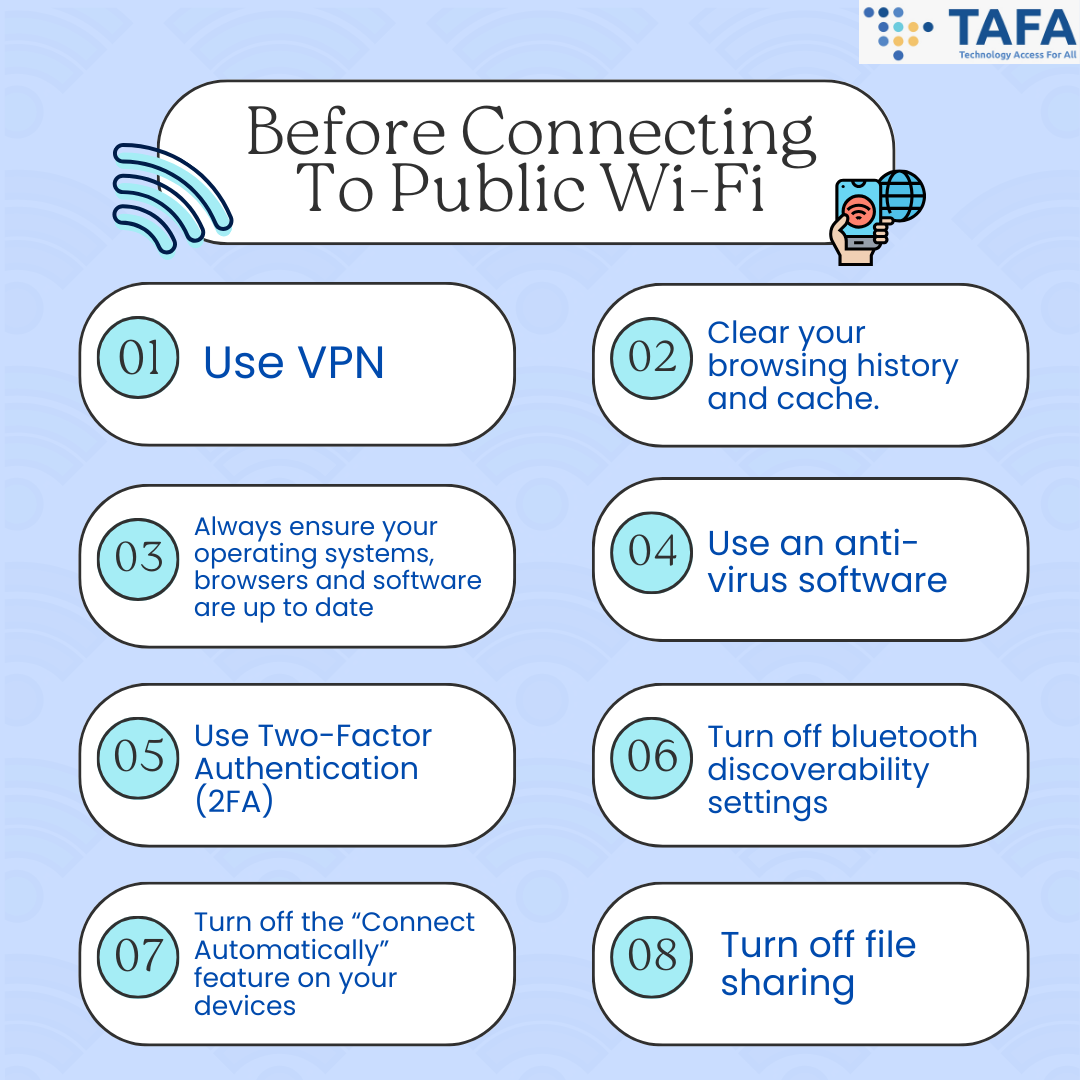
4. Malware Distribution Using public Wi-Fi without any protection (such as VPN) makes it easy for cybercriminals to infect your device with malware, a malicious software without your knowledge. What can also happen is that malicious websites can automatically download malware to your devices that are connected to the public Wi-Fi, compromising your security. 5. Snooping For Your Data Public Wi-Fi networks are very vulnerable to cybercriminals looking for sensitive documents such as 2FA codes, your banking passwords and account, and confidential documents. 6. Evil Twin Attacks: Malicious Hotspots Hackers set up fake malicious hotspots with similar names to reputable ones or ones that look trustworthy such as Cafe Free Wi-Fi. This tricks users into connecting and exposing your data. Once you connect to these malicious hotspots, they can easily intercept your data. Hackers can then harvest the personal and financial data from devices connected to these malicious hotspots. 7. Inject Phishing Attacks To Target You Attackers can intercept network traffic and bombard users with phishing attacks in the form of phishing emails, voicemails, text messages. Attackers can also prompt users to enter login credentials, which are then stolen for malicious purposes. How Do We Stay Safe On Public Wi-Fi? Ideally, if we want to stay completely safe, the best thing to do is NOT connect to public Wi-Fi. However, there are instances whereby we have no choice but to use public Wi-Fi, so here are some ways in which you can do to ensure that your data and accounts stay secure and safe: Before Connecting To Public Wi-Fi
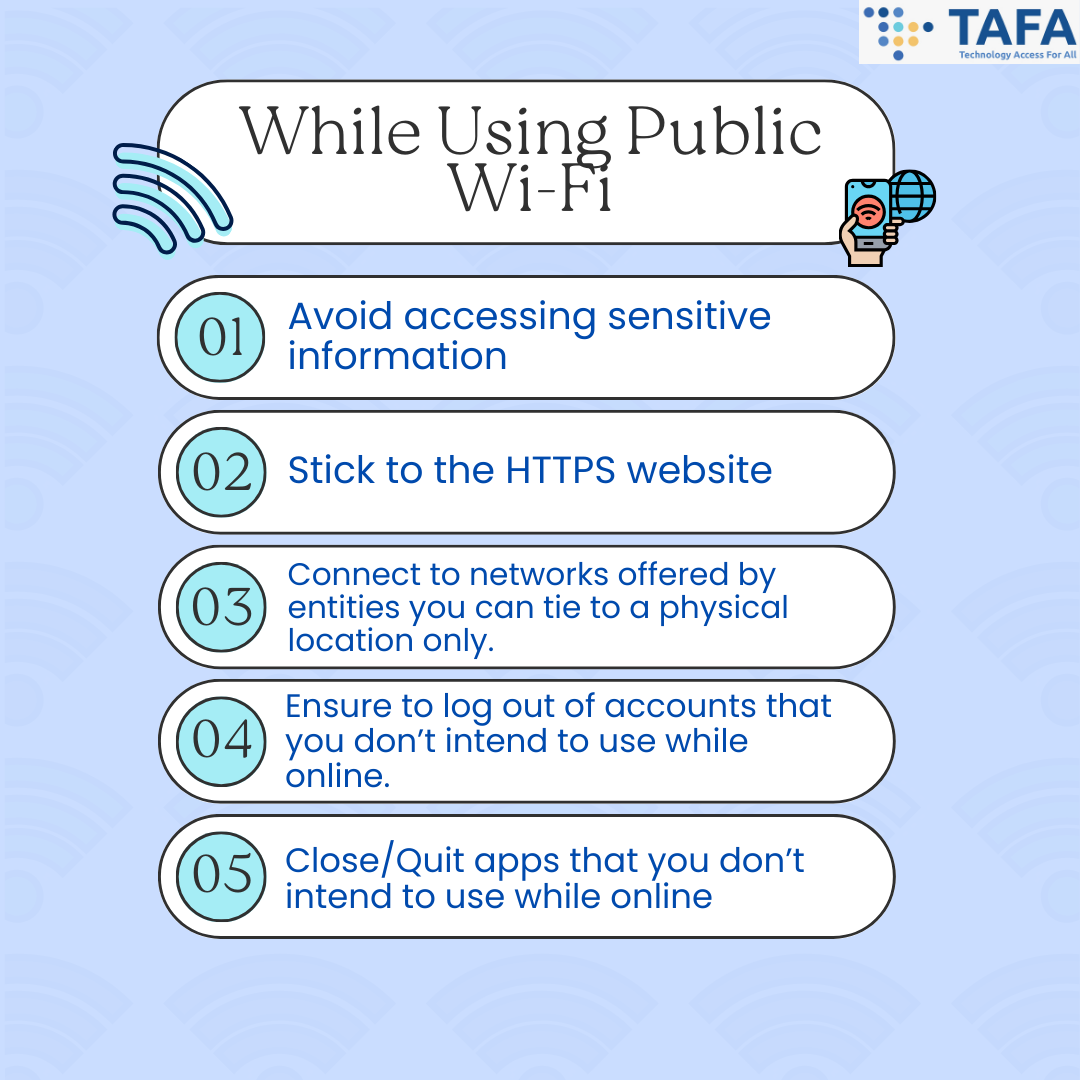
While Using Public Wi-Fi
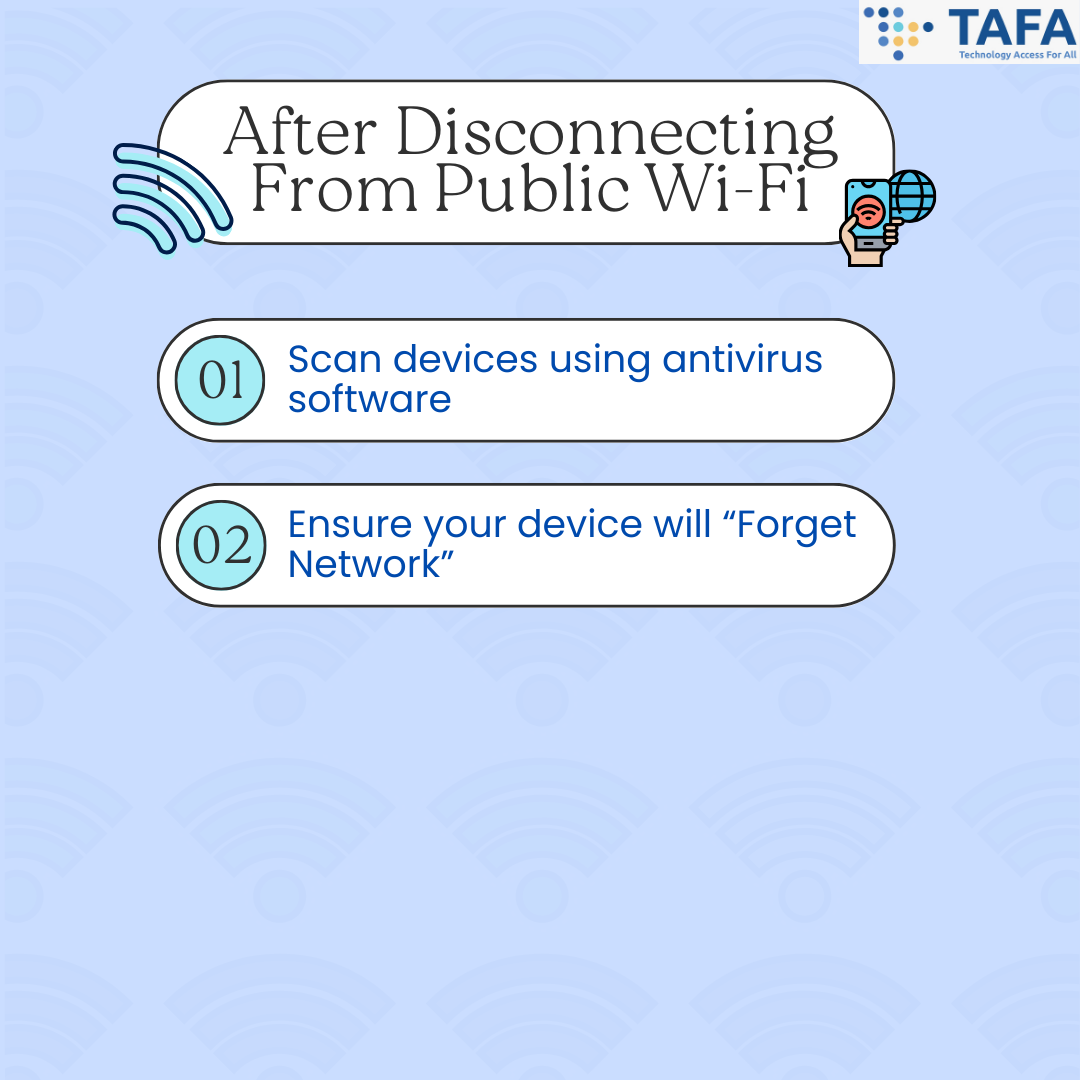
After Disconnecting From Public Wi-Fi
Conclusion While the convenience of public Wi-Fi is alluring, it's crucial to recognize the risks that come with it. By understanding the hidden dangers and implementing prudent cybersecurity measures, you can navigate the digital landscape securely. Remember, awareness is your strongest armour against the unseen threats that lurk in the shadows of free internet. Stay informed, stay vigilant, and safeguard your online journey. Related Topics A Personal Cybersecurity Checklist - How Cyber Secure Are You? Is This QR Code Safe? Top Tips to Ensure Your QR Scans are Secure Unmasking Phishing: Your Guide to Spotting The Signs of Phishing
Back to Blog
In the modern digital era, QR codes have become ubiquitous, seamlessly integrating into our lives. QR codes have become even more widely used, especially after the pandemic. QR codes are the latest form of digital technology that has become common. Yet, amid the convenience they offer, lies a lurking threat--malicious QR codes. Not all QR codes are safe! Just as a seasoned explorer navigates a maze, detecting safe QR codes requires vigilance and a keen eye. In this article, we will explain the different types of QR codes scam and give you tips on how to check if a QR code is safe or fraudulent. Types of QR Codes Scam The types of QR Code scams includes:
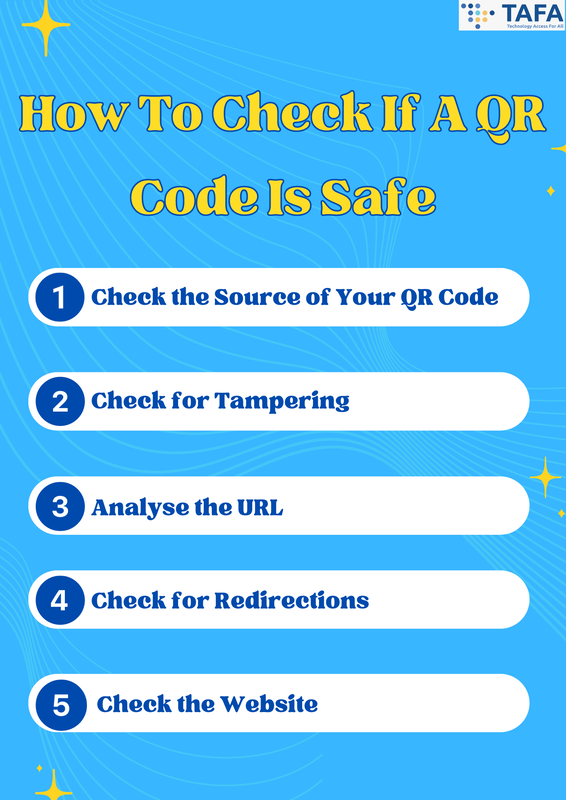
How to Check if a QR Code is Safe 1. Check the Source of Your QR Code
2. Check for Tampering
3. Analyse the URL
4. Check for Redirections
5. Check the Website
What Do I Do If I Scan A Scam QR Code? Presently, making QR codes are super easy, hence there is a huge variety and abundance of QR scams out there. And sometimes, there is almost no way to differentiate between a scam QR code and a real one till you open the link. If you have entered sensitive information:
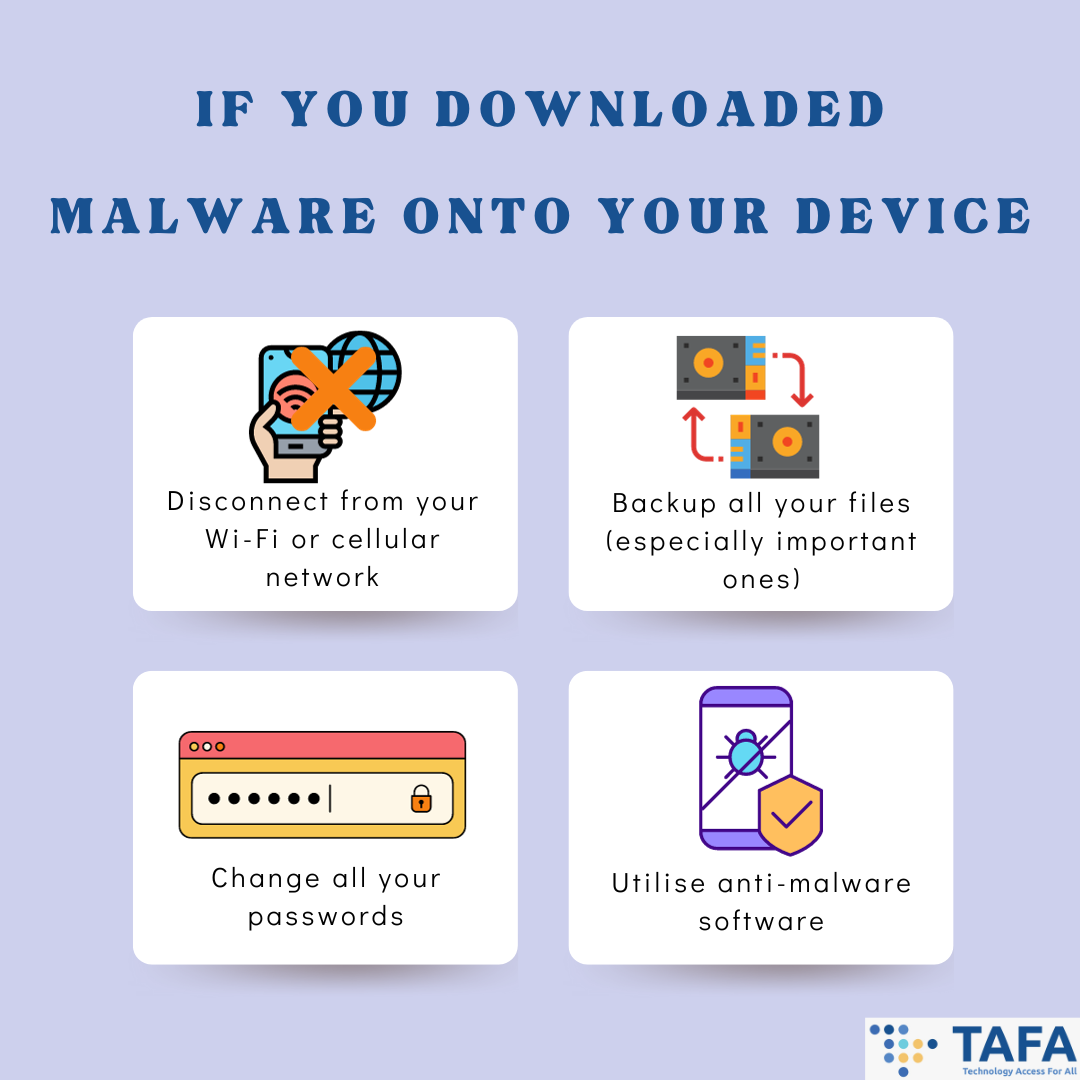
If you have downloaded malware onto your device via scanning QR code:
In the realm of QR codes, safety is the ultimate treasure, and with the right tools and knowledge, you can unlock it. Always scrutinise and look out for any signs of a scam QR code to ensure you can navigate through this digital landscape safely and securely. Vigilance is Key! Related Topics A Personal Cybersecurity Checklist - How Cyber Secure Are You? Unmasking Phishing: Your Guide to Spotting The Signs of Phishing
Back to Blog
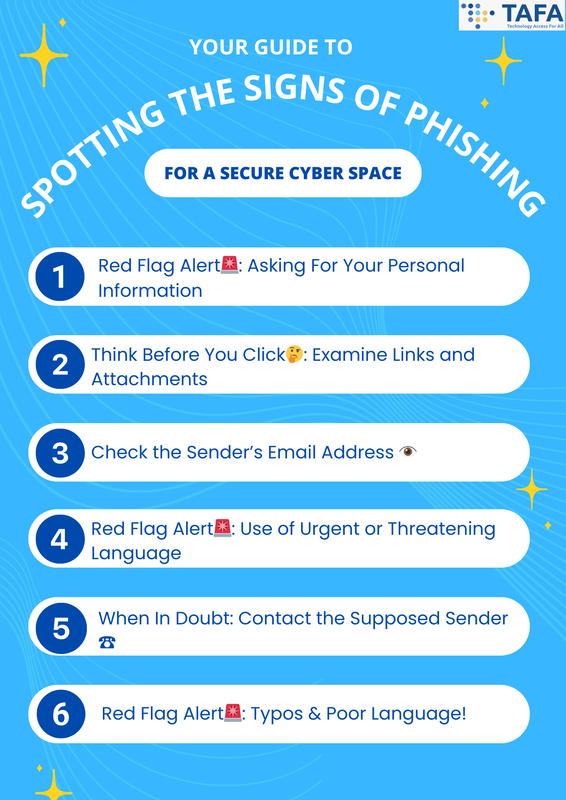
In today's interconnected world, every click and every link could potentially lead to unforeseen dangers. Phishing, a form of cyber threat, lurks beneath the surface, waiting to lure unsuspecting victims into its net of deceit. Through phishing, cybercriminals can obtain your personal and financial information such as your bank account numbers, credit card numbers and login details. Even worse, utilising your personal information, cybercriminals could gain access to your online accounts, and impersonate you to scam the people around you. Therefore recognizing the signs of phishing is essential for a safe online environment. Below we present a guide on spotting the signs of phishing and securing your online environment. How To Spot The Signs Of Phishing 1. Red Flag Alert🚨: Asking For Your Personal Information
2. Think Before You Click🤔: Examine Links and Attachments
3. Check the Sender’s Email Address 👁️
4. Red Flag Alert🚨: Use of Urgent or Threatening Language
5. When In Doubt: Contact the Supposed Sender ☎️
6. Red Flag Alert🚨: Typos & Poor Language!
Conclusion The internet is a vast landscape with both perilous threats and incredible opportunities. It is crucial to remember that dangers, like phishing, often lurk in the digital landscape. By honing your skills to recognize the signs of phishing, you arm yourself with the tools needed to steer through this space safely. Stay informed, stay vigilant, and let your knowledge guide you safely to have a secure cyberspace. Related Topics A Personal Cybersecurity Checklist - How Cyber Secure Are You?
Back to Blog
It’s October! This means it’s Cybersecurity Awareness Month! In an age where our lives are increasingly intertwined with the digital realm, ensuring our cybersecurity is paramount. A personal cybersecurity checklist can be your armour, defending against cyber threats and providing you with peace of mind. Personal Cybersecurity Checklist 1. Create Secure Passwords: The First Line of Defense
A strong unique password is now more essential than ever before:
2. Two-Factor Authentication (2FA): Adding an Extra Layer of Security
3. Regular Software Updates: Keeping the Gate Locked
4. Ensure website URL starts with HTTPS://
5. Phishing Awareness: Spotting the Hooks
6. Regular Data Backups: A Safety Net for Your Data
7. Be Careful on Social Media: Guarding Your Digital Persona Social media is a great way to connect and share information. However, do beware of what you share online. Cybercriminals can gain a lot of information from you from these social media platforms, and they will use this information for phishing attacks and identity theft.
8. Use Your Mobile Device Securely: Locking Down Your Digital Pocket
9. Don’t Use Public Wi-Fi: Safeguarding Your Online Journey
10. Review Your Credit Accounts Regularly: Keeping a Watchful Eye
🗒️By following this personal cybersecurity checklist, you're well on your way to fortifying your digital presence. The internet is a vast landscape with both perilous threats and incredible opportunities. Empower yourself with knowledge, awareness, and proactive measures to navigate this space safely. Your cyber fortress awaits - fortify it and ensure your online experiences are secure, seamless, and rewarding. .
Back to Blog
In the digital landscape of cybersecurity, 2 common nefarious software tend to pop out the most - Malware and Ransomware. Both software are designed to infiltrate, infect, and wreak havoc on your digital life. In this article, we'll pull back the curtain on these digital adversaries, exploring what sets them apart and why they're such a significant threat in today's interconnected world.
Unmasking Malware: The Sneaky Saboteur Malware, a portmanteau of malicious software, is a software designed to achieve malicious purposes on an infected computer. Essentially, it is a broad term encompassing various types of unwanted software designed to infiltrate or damage your system without your consent. It includes adware, cryptominers, botnets, ransomware, infostealers, mobile malware, trojans, viruses, worms, wipers, and more. These different types of malware are designed differently depending on their goals. For example, malware designed to serve unwanted advertisements is vastly different from ransomware, which encrypts files on infected systems. Although, these malware variants do use many of the same techniques to achieve their different goals. Malware can stealthily enter your system through email attachments, infected websites, or software downloads, often exploiting vulnerabilities in outdated software and human vulnerabilities. Malware's motives range from simply causing chaos to stealing sensitive information like passwords or financial data. Some disguise themselves as legitimate programs, lurking in the background and siphoning off your data, while others might bombard you with unwanted ads or even encrypt your files like ransomware. Ransomware: The Digital Kidnapper Ransomware is a specific type of malware that takes digital extortion to a whole new level. Essentially, all ransomware is malware, but not all malware is ransomware. The goal of ransomware is to deny the victim access to their files via encryption, and demand a ransom in exchange for the decryption key, which restores access. Once ransomware gains access to a computer, it will work its way through the filesystem, checking the types of files found. If a file matches the built-in list of file extensions, the malware will encrypt the file data, and will replace the original data with the encrypted version, and wipe any record of the original in the system. Many ransomware variants will also work to spread beyond the initial target. This allows cybercriminals to infect a greater number of systems, access higher-value systems, and increase their ransom demand. After the ransomware completes the encryption process, a ransom demand will be presented to the users - either pay the ransom within a specified time or risk losing their files forever. If the user pays the ransom demand, the cybercriminal will give them the decryption key for their files. This key should allow the victim to be able to decrypt most or all of their files, hence restoring access. Recent years, there has been an alarming rise in ransomware attacks, impacting individuals, businesses, and even critical infrastructure. Attackers have refined their tactics, often employing phishing emails and social engineering to deceive victims into triggering the ransomware. Ransomware: It’s Evolution With Other Malware Ransomware has been evolving, whereby hybrids have been created with ransomware and other types of malware are being used together. Examples include:
Ransomware VS Malware: How They Differ The critical difference between malware and ransomware lies in their intent and impact. Malware has a broader agenda, from data theft to system disruption. It can be covert, stealthily spying on your activities, or overt, bombarding you with pop-ups and ads. On the other hand, ransomware has a singular, malicious goal: encrypting your data and demanding a ransom. It's a direct, in-your-face attack that leaves you with a chilling choice: pay or lose your valuable files. Protecting Your Digital Realm Against Malware The best way to protect against malware attacks is via prevention.
Takeaway In the ever-evolving digital landscape, understanding the distinctions between malware and ransomware is crucial for fortifying your defenses. Both are formidable foes, but with the right knowledge and security measures, you can tilt the odds in your favor. Stay vigilant, stay informed, and let your digital fortress stand strong against the relentless tide of cyber threats. Related Topics Ransomware - A Growing Problem & Best Practices For You and Your Company Ransomware Payments Skyrocket in 2023: The Unprecedented Surge and its Implications What Is A Ransomware Attack? How does it Work? & Best Practices What is Ransomware as a Service (RaaS)? Unmasking The Dark Side Of Cybercrime-as-a-Business |
|
© 2021, TAFA HOLDINGS (S) PTE LTD. ALL RIGHTS RESERVED
|

 RSS Feed
RSS Feed