AuthorTAFA Archives
April 2024
Categories
All
|
Back to Blog
The digital age has revolutionised the way we shop, but it has also opened the door to new threats. Europol has notified 443 online shops that they have been infected with credit card stealers in December 2023. This highlights the pervasive nature of cybercrime and the need for heightened vigilance. Join us as we explore the implications of this warning, the tactics used by cybercriminals, and steps businesses can make to protect themselves in an increasingly risky online shopping landscape. On Credit Card Stealers Threat actors have hacked online shops with malicious scripts that steal customers’ debit and credit cards. Skimmers (which are small snippets of JavaScript code) have been added to checkout pages or loaded from remote resources to evade detection. This is a major cybersecurity threat as digital skimming steals credit card information or payment card data from online stores’ customers. As the transaction data is intercepted during the online purchase checkout process, customers tend not to notice anything unusual. How Does Digital Skimming Work? Generally, there are 3 stages in a digital skimming attack:
What do these codes do? They intercept and steal payment card numbers, expiration dates, verification numbers, names and shipping addresses. This personal information will then be uploaded to the attackers’ servers. Consequences of Credit Card Stealers The consequences of the stolen data is that threat actors can use them to perform unauthorised transactions (e.g. online purchases) or resell them to other cybercriminals on the dark web. Unfortunately, these attacks can go undetected for weeks or even several months. Furthermore, cybercriminals can even collect large amounts of payment card details if the breached e-commerce platforms are highly popular. Scale of The Operation This 2 month international operation was coordinated by Europol and spearheaded by Greece, involved law enforcement from 17 countries and private entities such as Group-IB and Sansec. Tips for Business To Protect Themselves
What To Do If You Become A Victim?
Conclusion Europol's warning serves as a stark reminder of the ever-present threat of cybercrime in the digital age. By staying informed, exercising caution, and following best practices for online security, consumers can protect themselves from falling victim to credit card stealers and other malicious threats. Together, let us work towards a safer online shopping experience for all. Related Topics 26 Billion Records Compromised in Huge Data Leak - dubbed as “Mother of All Breaches”. 12.8 million authentication and sensitive secrets leaked on GitHub in 2023 Apple's Alarming Report: 2.6 Billion User Records Exposed By Data Breaches in Past 2 Years 71 Million Emails from Naz.API stolen account list added to Have I Been Pwned.
Back to Blog
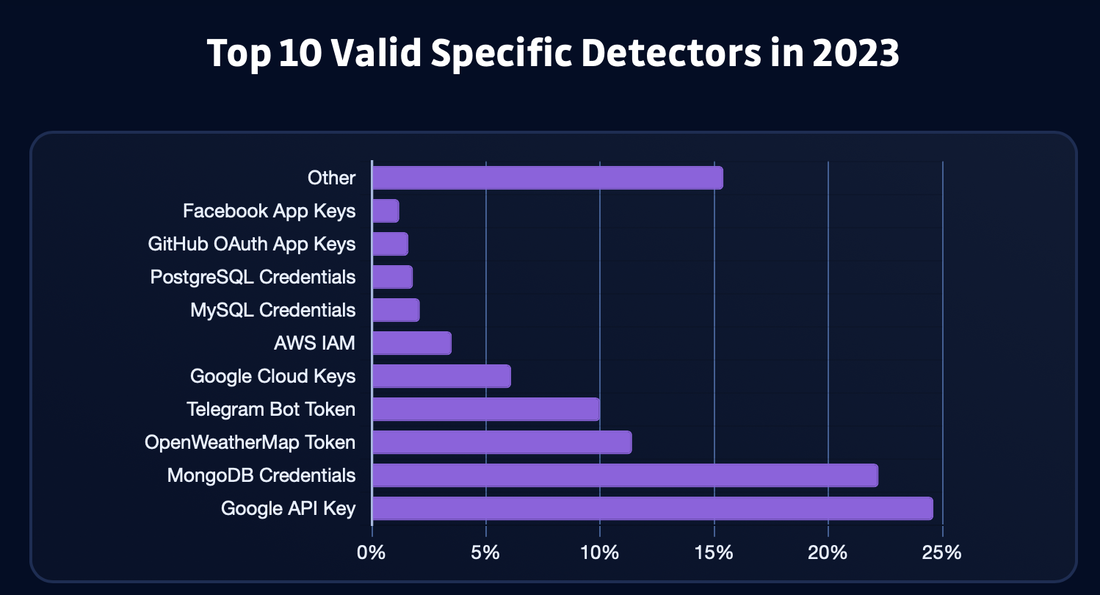
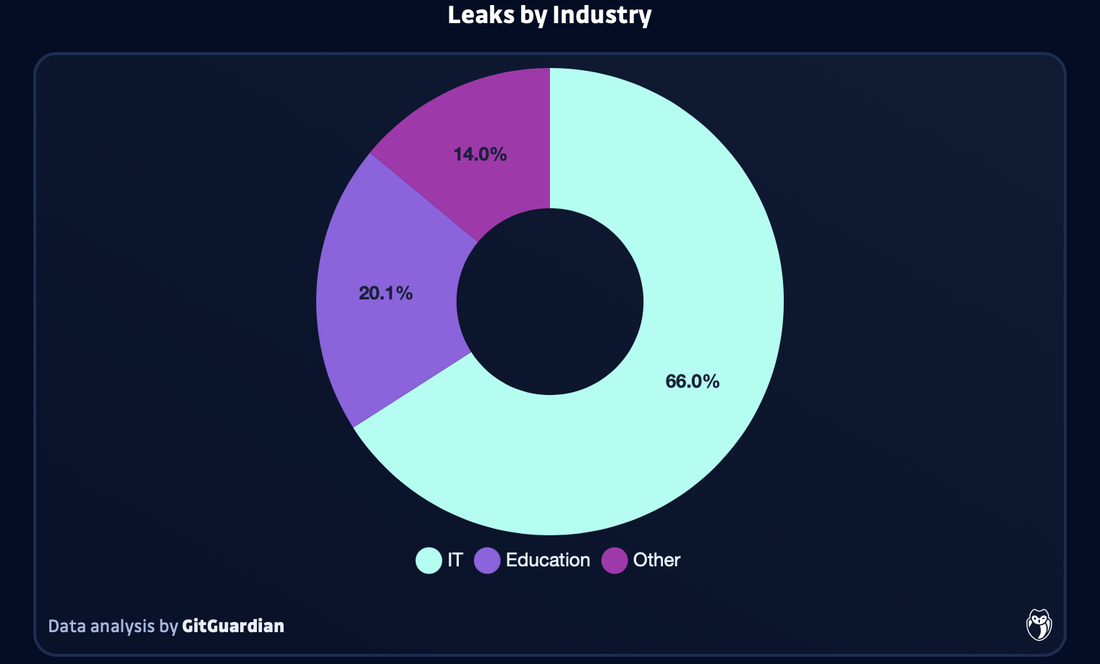
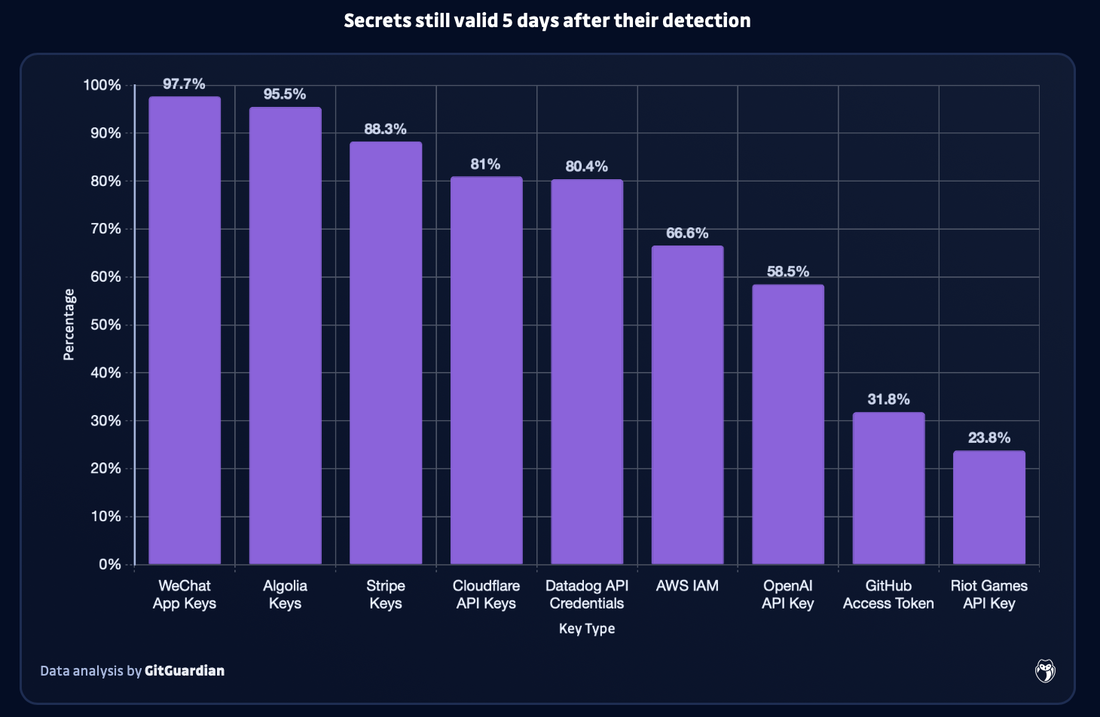
In the digital age, the protection of sensitive information is paramount. However, GitGuardian found that in 2023, GitHub users accidentally exposed 12.8 million authentication and sensitive secrets in over 3 million public repositories, with the vast majority of these secrets being still valid after 5 days. This incident serves as a stark reminder of the importance of robust cybersecurity measures and the need for increased vigilance. Join us as we delve into the details of this significant data breach, its implications for cybersecurity, and steps individuals and organisations can take to protect themselves. GitHub Leak: Unveiling the Scope In 2023, the number of authentication and sensitive secrets leaked on GitHub was 12.8 million. This is a 28% increase as compared to the previous year (10 million in 2022). Unfortunately, this is not surprising due to hard-coded credentials have always been one of the primary causes of security incidents in the software world. This is being exacerbated with the increasing complexity of digital supply chains. For instance, Sophos 2023 Report found that in 2023 compromised credentials was the top root cause of attacks for the first time. It was found that in the first half of the year, compromised credentials accounted for 50% of root causes, followed by vulnerability at 23%. What was Leaked The exposed secrets include account passwords, API keys, TLS/SSL certificates, encryption keys, cloud service credentials, OAuth tokens, as well as other sensitive data that could give external actors unlimited access to a range of private resources and services. All of this can lead to data breaches and financial damage. In 2023 alone, over 1 million valid occurrences of Google API secrets, 250,000 Google Cloud secrets, and 140,000 AWS secrets were detected.The reasoning for this is that there has been an increase in the number of code repositories on Github, with a 22% increase (50 million) in new repositories added in the past year. Therefore, this enhances the risk of accidental and deliberate exposure of sensitive information. Countries with the Most Leaks The top 10 countries with the most leaks are India, United States, Brazil, China, France, Canada, Vietnam, Indonesia, S.Korea and Germany. Sectors with the Most Leaks The most affected sector was the IT sector (this also includes software vendors), as it encompasses 65.9% of all detected leaks. This is then followed by Education (20.1%), Science & Tech (7%), Retail (1.5%), Manufacturing (1.2%), and Finance & Insurance (1%). Generative AI Leaks Trend Generative AI tools are exponentially growing in terms of their use in 2023 as many businesses and employees utilise them. However, this has also led to an exponential growth in generative AI leaks on GitHub last year as well. GitGuardian observed that in 2023, there was a 1,212 increase in the number of OpenAI API keys leaked on GitHub as compared to 2022. It was averaged that 46,441 API keys were leaked per month - this was the highest growing data point in GitGuardian’s report. Although OpenAI leads drastically in the number of leaks detected on GitHub, open-source AI models repository HuggingFace had a steep increase in leaked secrets month after month. This could indicate that there is a growing interest among developers and researchers of this AI tool. Other AI tools that were found to have leaks include Cohere, Claude, Clarifai, Google Bard, Pinecone, and Replicate. Although these AI tools were found to have leaks at a much lower level as compared to OpenAI and HuggingFace. Troubling Trend of Leaks GitGuardian monitored how well authors fixed leaks via revoking the secret as soon as possible to reduce the impact of the incident. Unfortunately, more than 90% of the secrets still remained valid 5 days after being leaked. Furthermore, only 2.6% of the leaks were revoked within 1 hour after GitGuardian notified them of the leak via email. However, not all types of leaked secrets were revoked at the same rate. Based on their analysis, leaked WeChat App (97.7% still remain valid after 5 days) and Algolia keys (95.5% still remain valid after 5 days) were the most likely to remain exposed for over 5 days. This is then followed by Strip keys (88.3%) and Cloudflare API keys (81%). Developers should be more concerned about these keys as they would be prime targets in credential harvesting campaigns.
GitHub Rectification In February, Github enabled push protection as a default for all public repositories to prevent accidental exposure of secrets when pushing new code. Related Topics 26 Billion Records Compromised in Huge Data Leak - dubbed as “Mother of All Breaches”. Apple's Alarming Report: 2.6 Billion User Records Exposed By Data Breaches in Past 2 Years 71 Million Emails from Naz.API stolen account list added to Have I Been Pwned.
Back to Blog
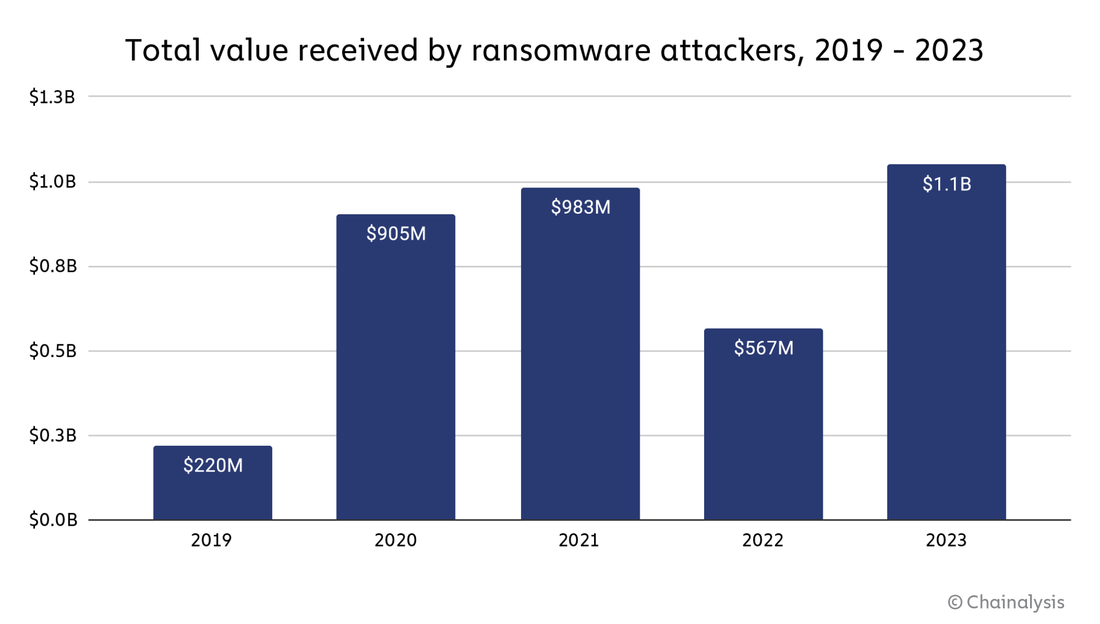
In the ever-evolving landscape of cybercrime, ransomware has emerged as a formidable threat, with cybercriminals raking in record-breaking sums through their malicious activities. The year 2023 saw a staggering $1.1 billion paid in ransom payments, underscoring the urgent need for heightened cybersecurity measures and increased awareness. Join us as we delve into the intricacies of this alarming trend, uncover the factors driving the surge in ransom payments, and explore strategies to combat this growing menace. On 2023 Ransomware Payments Ransomware payments soared in 2023 to $1.1 billion, and broke the previous record of $983 million in 2021. Unfortunately, this indicates that the decrease in ransomware activities in 2022 was an anomaly. This anomaly could be attributed to several reasons such as geopolitical events (e.g. Russian-Ukrainian conflict), an overall reluctance to pay ransoms due to potential sanction risks, and also law enforcement taking on ransomware groups (e.g. Hive intervention). This overall trend line, created by Chainalysis, from 2019 to 2023 indicates that ransomware is an escalating issue. Furthermore, it is important to note that the numbers calculated did not reflect the monetary impact in terms of productivity loss and repair costs. For instance, the MGM ransomware attack was estimated to cost MGM over $100 million. Furthermore, not all ransom payments, especially cryptocurrencies payments, were traceable. Hence, the figures made are all conservative estimates, and are likely to increase when new ransomware addresses are found.
Ransomware Resurgence: Understanding the Surge in Payments According to a new Chainalysis report, the 2023 record can be attributed to:
Combating the Ransomware Epidemic: Strategies for Prevention & Mitigation
Conclusion The surge in ransom payments in 2023 serves as a stark reminder of the evolving nature of cyber threats and the critical need for proactive cybersecurity measures. The ransomware landscape in particular has evolved significantly in 2023 via the changes in tactics and affiliations among threat actors which has led to a more aggressive and efficient approach. Although ransomware attackers have innovated and adapted to regulatory changes and law enforcement actions, there were also significant steps made against ransomware via collaboration of government agencies, affected organisations, and blockchain intelligence. By understanding the factors driving this trend, implementing robust security practices, and fostering a culture of awareness and collaboration, we can collectively combat the ransomware epidemic and protect our digital future. Related Topics 71 Million Emails from Naz.API stolen account list added to Have I Been Pwned. 26 Billion Records Compromised in Huge Data Leak - dubbed as “Mother of All Breaches”. Apple's Alarming Report: 2.6 Billion User Records Exposed By Data Breaches in Past 2 Years
Back to Blog
This massive stolen account list, with a list of 1 billion credentials, was compiled via credential stuffing lists and data stolen through the use of information-stealing malware.
Credential stuffing is a type of cyberattack in which credentials that have been previously obtained from a data breach are used to attempt to log into other services/systems. The Naz.API dataset allegedly contains over 1 billion lines of stolen credentials. This dataset garnered attention after it was used as part of an open-source intelligence (OSINT) platform called illicit.services, although the data list has been shared around the data breach community for a while. Illicit.services allows one to search for stolen information, which includes victims’ names, phone numbers, email addresses, and other personal data. Fortunately, the service was shut down in July 2023 due to concerns for cyberattacks such as Doxxing and SIM-swapping attacks. However, the service was once again made available in September. From a screenshot of the dataset, each line consists of a login URL, login name, and an associated stolen password. Understanding the Risks
Stolen Dataset Added to HIBP On 17 January 2024, it was announced that Naz.API dataset was added to Have I Been Pwned, a data breach notification service, after they received the data list from a well-known tech company. According to them, the dataset consists of 319 files, which totals to 104 GB, and contains 70,840,771 unique email addresses. It is important to note that although there are 70,840,771 unique email addresses, for each email, there are likely many other records for the different sites’ credentials that were stolen from. It was also noted that the Naz.API data is likely old as it contained some of their own and subscribers’ passwords that were used in the past. From this, they were able to extrapolate that some of the data were over 13 years old. It is recommended that you should check if your credentials are in the Naz.API dataset, via searching your credentials on Have I Been Pwned. If it is found that your email is part of the stolen data list set, the site will warn you. This indicates that at some point your computer has been compromised with information-stealing malware. If your email address is part of the stolen data list, we do highly recommend you to change passwords for all of your saved accounts, especially those accounts that are highly confidential. This includes passwords for your email accounts, bank accounts, and other personal accounts. Other Steps to Safeguard Your Digital Identity Other than checking the Have I Been Pwned, it is also important to:
Conclusion As we navigate the digital landscape, the Naz.API data breach serves as a stark reminder of the importance of cybersecurity. By taking proactive steps to protect ourselves, staying informed, and spreading awareness, we can mitigate the risks posed by data breaches and safeguard our digital identities. Remember, in the digital age, vigilance is key, and knowledge is your shield against cyber threats. Stay safe, stay secure, and empower yourself in the digital realm. Related Topics 26 Billion Records Compromised in Huge Data Leak - dubbed as “Mother of All Breaches”. Apple's Alarming Report: 2.6 Billion User Records Exposed By Data Breaches in Past 2 Years Unmasking Phishing: Your Guide to Spotting The Signs of Phishing Protect Yourself: Best Practices to Combat Phishing Attacks
Back to Blog
In a digital era where information is currency, a newly released Apple commissioned report sends shockwaves through the cybersecurity landscape. According to the study, a staggering 2.6 billion personal records have been compromised in data breaches over the past two years. Furthermore, many indicators show that the number of data breaches has gotten worse in 2023. This isn't just a statistic; it's a stark reminder of the relentless onslaught that our digital identities face. As stated, this report shows compelling evidence that data breaches “have become an epidemic” that endangers sensitive and personal information globally. The Magnitude of Breach The study titled ‘The Continued Threat to Personal Data: Key Factors Behind the 2023 Increase’ was conducted by MIT professor Dr Stuart Madnick. It provides a summary of the major data breaches, and highlights some trends. The report shows that data breaches have more than tripled between 2013-2022 - exposing 2.6 billion personal records in the past 2 years alone (1.1 billion in 2021 and 1.5 billion in 2022) - and have continued to get worse in 2023. In the first 9 months of 2023, the number of data breaches in the U.S. have already increased by nearly 20% as compared to all of 2022. For US organisations, this is an all-time high. This trend of sharp increases in data breach can also be seen globally. The report also shows that attacks targeting cloud infrastructure nearly doubled from 2021 to 2022. According to a 2023 report, over 80% of data breaches involved data stored in the cloud. This occurs as (1) there's a mass migration of data to the cloud due to the various benefits it offers, and (2) as cloud services are based on new technology, cloud misconfigurations caused by errors that expose a cloud environment, tend to occur. According to the NSA, “cloud misconfigurations are the most prevalent cloud vulnerability”. In this report, a list of examples of major data breaches that occurred globally in 2023 were compiled. For instance, in Asia Pacific, Toyota (cloud misconfiguration) led to over 2.15 million customers’ location data over 10 years being compromised, PhilHealth in the Philippines (corporate ransomware) led to over 13 million customers’ personal data being compromised, and Latitude Financial (vendor exploitation) led to over 14 million customers’ personal data being compromised. To read the study in full, here’s the link: The Continued Threat to Personal Data: Key Factors Behind the 2023 Increase Key Factors That Contributed to The Increased Threat to Personal Data: 1. Ransomware attacks have increased in quantity and are more dangerous than ever. In 2023, ransomware attacks increased quantitatively like never before, and have become more sophisticated and aggressive. This is easily reflected in which it was found that more ransomware attacks were reported through September 2023 than in all of 2022. Additionally, in the first 3 quarters of 2023, the number of ransomware attacks increased by nearly 70% as compared to the first 3 quarters of 2022. Furthermore, hackers are becoming more organised, often through ransomware gangs. Hackers are relying on more sophisticated tools including generative AI, have higher budgets and on more efficient organisational structures. Ransomware gangs behave like companies - crafting a public web presence, providing customer service, and offering opportunities to other threat actors to rent out ransomware software. Cyberattacks have also become more threatening, and more likely to target organisations with sensitive data - e.g. healthcare facilities, education institutions, governments. Unlike before, hackers have shifted their strategies to cause the most harm possible. They are now more likely to leak corporate and consumers’ personal data when a ransom is not paid. This shift has caused ransomware attacks to be detrimental to consumers, as their data has been exposed more often. To make things worse, it has been found that in recent years, hackers are more likely to leak data even after receiving a ransom. Hence, even if organisations did pay the ransom, it is often not enough to protect consumers. 2. Cyberattacks On Vendors Are Increasing. Attacks on vendors often lead to many other organisations that depend on these vendors being data breaches. As virtually every organisation globally relies on a wide range of vendors and software for daily operations. In many cases, these vendors are small or medium sized companies that do not have sufficient resources to allocate to security. Hence, vendor attacks can impact virtually all organisations, even those with the strongest security measures. This is evident from the report which shows that 98% of organisations that work with a vendor that experienced a data breach in the last 2 years. The wide-reaching impacts of a vendor attack can be seen by the MOVEit transfer service data breach. In which, an unpatched vulnerability led to hackers compromising the data of organisations that utilised their service and steal sensitive data from their customers. The hackers were able to infiltrate more than 2,300 organisations globally (this included private companies such as Shell, IBM, government entities and contractors, financial & public institutions), and more than 65 million individuals have been impacted so far. A Call For Action: End-To-End Encryption This report highlights the prevalence of data breaches and the detrimental consequences these will have for individuals. Therefore, keeping personal data safe must be at the forefront of organisations’ priorities. This message is further brought back to home as recent cyberattacks have shown that organisations can only be as secure as their “least secure link”. This is why, in the last year, technology platforms and other industry players have expanded the use of end-to-end encryption. This is a method in which companies can protect their data by ensuring that only the sender and receiver can access and modify the data. Hence, it protects sensitive information such as personal and financial information. Navigating the Digital Storm As individuals and businesses grapple with the repercussions of this data breach tsunami, the report serves as a guidepost. It not only elucidates the scale of the challenge but empowers readers with insights to fortify their defences. Cybersecurity is no longer a luxury; it's a necessity. Let us navigate the digital storm armed with knowledge, fortified by encryption, and united in our commitment to a more secure digital future. Related Topics 26 Billion Records Compromised in Huge Data Leak - dubbed as “Mother of All Breaches”. Unmasking Phishing: Your Guide to Spotting The Signs of Phishing The Rise Of Phishing: Safeguarding Against Digital Deception Protect Yourself: Best Practices to Combat Phishing Attacks
Back to Blog
It was revealed by security researchers that a massive database that contains no less than 26 billion leaked records were found on an unsecured page dubbed “Mother of all Breaches (MOAB)”, and runs to 12 terabytes in size. It contains 26 billion records, over 3,800 folders, with each folder corresponding to a separate data breach.
According to the research team, although the leaked data contains mostly information from past data breaches, it still holds new data that were not published before. Who is affected by this data leak? Many companies and organisations have been impacted by this breach.
The leak also includes records of various government organisations in the U.S., Germany, Brazil, Philippines, Turkey and more. Why Is This Important? A data leak of this scale has never occurred before, and the consequences of this breach will be detrimental. As many people do reuse their usernames and passwords, malicious threat actors can embark on credential-stuffing attacks (where hackers take leaked passwords and email addresses, use those combinations across the web and see what accounts they can get into). For instance, if users use the same passwords for their Twitter account and their Gmail account, attackers can use these leaked credentials to attack your more vital or sensitive accounts. To add on, this massive data leak can cause users whose data has been leaked to become victims of spear-phishing attacks or receive high level spam emails. How Do I Protect Myself Now? 1. Change Passwords On All Impacted Sites Immediately change the passwords for the affected accounts to prevent further unauthorised access. As a rule of thumb, you should change your passwords frequently for all your accounts. It is important that your passwords are strong. This includes ensuring that your passwords are at least 16 characters in length, including a mix of numbers, lower and uppercase, and special characters. Read more: Password Security Tips: How To Fortify Your Password Security 2. Turn on MFA (Multi-Factor Authentication) or 2FA (Two-Factor Authentication). MFA isn't just an option; it's a necessity. By using another form of ID, such as security tokens, biometrics, SMS authorisation codes or authenticator apps will help add an extra layer of security. This will make it harder for hackers to gain unauthorised access to your online accounts, even if they steal your password. It is highly recommended to turn on MFA wherever possible, starting with very important accounts such as your email, social media and financial services accounts. 3. Check if your data has been leaked. Do check if you have been victims to this breached data through services like Have I Been Pwned. These services can help you check if your details have already been made public or in danger of being used maliciously. 4. Stay alert and regularly monitor your accounts. Keep a close eye on your bank statements, credit reports, and other sensitive accounts for any unauthorised activity. If you notice anything unusual, report it immediately to the respective institution and take necessary action. Be vigilant against any phishing and spear phishing attempts that might occur. Always be suspicious of calls or emails from unknown sources. Related Topics Unmasking Phishing: Your Guide to Spotting The Signs of Phishing The Rise Of Phishing: Safeguarding Against Digital Deception Protect Yourself: Best Practices to Combat Phishing Attacks
Back to Blog
Striking a Balance: Singapore's May Split Liability For Financial Scams Between Banks & Victims29/9/2023 The digital age has brought tremendous convenience, but it has also birthed new forms of crime. Financial scams, such as phishing, have been a persistent issue causing substantial losses to both individuals and financial institutions. In response to this growing concern, Singapore is delivering a consultation paper detailing a split liability scheme, which aims to ensure that the burden of financial losses due to scams is shared between consumers and banks. This article delves into the details of this approach, its implications, and the need for such measures in today's digital landscape. How Did The Idea of Split Liability Come About? The catalyst of a shared liability strategy came about in February 2022 after cybercriminals stole a combined SG$13.7 million (US$10.2 million) from around 800 customers of a single bank [the Overseas-Chinese Banking corporation (OCBC)] via the use of spoofing text messages. These SMS disguised as messages sent from OCBC, asked account holders to click a link to resolve account issues that redirected them to a fake bank website. This allowed the cybercriminals to collect their logins and passwords. This resulted in the cybercriminals being able to transfer the digital token over to their own devices, and drain the victims’ accounts. Initially, OCBC offered “goodwill” payments to only 6.4% of victims. It was only when the Monetary Authority of Singapore (MAS) threatened action, did OCBC change their stance and stated that they would issue “full goodwill payouts” to all victims. The sheer amount of required payouts make Singapore rethink their anti-scam measures. The then-minister of finance, now deputy prime minister, Lawrence Wong stated that there would be a shared responsibility for any losses by both banks and customers. This is to prevent customers having a “weaken[ed] incentive to be vigilant” against phishing scams, in particular social engineering scams. What About Other Countries? The UK will enforce a mandatory reimbursement by banks within 48 hours to customers that have been scammed to send money to scammers in 2024. This new mandatory reimbursement system by the Payments Systems Regulators (PSR) are designed to ensure that customers will get a refund if they fall victim to authorized push payment fraud (APP), which is where a victim is tricked into making a payment to scammers posing as a legitimate organization such as a bank or police. The PSR proposed that banks must reimburse payments over 100 pounds to a maximum of a million pounds, although many banks have lower limits. This reimbursement bill will be shared between the sending and receiving banks. Australia seems to be adopting similar measures, whereby the country’s financial services minister, Stephen Jones, has said the government is “going to ensure that the banks are accountable for much more”, and that they will “probably look at something which travels in the same direction” as the UK. This comes after a recent report whereby they found that Australia’s big banks reimburse less than 5% of scam victims. Similarly, the European Commission has also proposed refunding victims of authorized payment fraud in certain circumstances. Why is Singapore Going Forward With the Liability Scheme? Based on the views of other countries, it seems that Singapore is going in a different direction. As Alvin Tan, Singapore’s minister of state, told the Parliament, it seems that some have the perception that banks can easily absorb losses from these scams. However, making banks fully responsible for these losses without considering culpability “is neither fair nor desirable”. And as talked about above, they are afraid that if banks become fully responsible for the losses, this could de-motivate customers to be vigilant towards scams, making customers complacent. Tan did also state that in scam cases, banks have to “consider if they have fulfilled their obligations, and whether the victim had acted responsibly.” Elaborating further, Tan did state that victims who did practice good cyber hygiene, and did their best such as “preventing their login information and [one-time passwords] from being divulged to third parties, should not have to bear losses”. What This Means… Based on this, it seems that under the new scheme, consumers are expected to exercise due diligence in their financial transactions, and banks are expected to enhance their security measures and educate consumers on potential risks. Banks are accountable for ensuring a safe banking environment, and have to promptly investigate and resolve scam cases. However, they will not be the sole bearers of financial losses. Consumers who follow best practices are less likely to suffer losses and therefore share in the responsibility for any financial setback. Disagreement to the Scheme However, there are disagreements within the parliament itself on this stance. Slyvia Lim, a parliament member, said that “banks should take on an outsized role in preventing [scams]”, and that banks in Singapore should be required by law to fully reimburse scam victims. Her underlying argument was that customers are not well-equipped as compared to banks to combat scams, as customers do not have the resources and position that banks have. Furthermore, she states that Singapore should adopt the UK system of mandatory reimbursement that will be implemented in 2024, and it can be “scoped to protect customers who are consumers, small businesses and charities.” Lim also said that more has to be done for scam victims, as currently some Singapore banks’ goodwill payments are “paltry” compared to the victims’ losses. Such goodwill offers are usually tied to non-disclosure agreements, which not only needs customers to maintain confidentiality but also forgo all rights to recover further sums. Lim called these agreements to be one-sided, and pushed MAS to consider establishing regulatory guidelines in the settlement of consumer disputes. As of today, the consultation paper on the framework of the liability scheme has not yet been published due to the complexity of issues involved. The government aims to issue the public consultation paper in the 3rd quarter of 2023. Implications of the Split Liability Scheme The split liability scheme brings several implications to the fore: 1. Promoting Awareness and Responsiveness This approach encourages consumers to be vigilant and take precautions when engaging in financial transactions, fostering a safer digital ecosystem. 2. Financial Prudence Consumers are incentivized to exercise caution and implement security measures, fostering financial prudence and minimizing potential losses. 3. Shared Responsibility By distributing accountability, both consumers and banks must actively collaborate to mitigate the risks of financial scams. This strengthens the overall security landscape. Takeaway The introduction of the split liability scheme in Singapore represents a fundamental shift in how financial losses due to scams are perceived and managed. By distributing accountability, this approach aims to instill responsibility, awareness, and prudence within the financial ecosystem. Striking a balance between consumer caution and enhanced bank security, the split liability scheme is a step towards a more secure and informed digital future for Singapore. As technology continues to evolve, so do the strategies to combat cyber threats. The split liability scheme is a testament to Singapore's commitment to adapting and innovating in the face of modern challenges. It's a paradigm shift that could set the tone for similar initiatives globally, as societies grapple with the ever-changing landscape of digital risks and financial scams. Related Topics Navigating the Digital Peril in Singapore: Phishing & Ransomware Continue To Pose Significant Risk Singapore Healthcare Cybersecurity Compliances You Must Know
Back to Blog
Ransomware has emerged as a digital epidemic, disrupting businesses, organizations, and individuals on an unprecedented scale. The year 2023 has witnessed an alarming trend: ransomware payments are soaring to new heights. According to Chainanalysis, ransomware is the only cryptocurrency crime category that has seen a rise in revenue, with all the others (hacks, malware, scams, abuse material sales, darknet market and fraud shops) recording a decline.
The trajectory of these payments is a cause for concern, shedding light on the evolving tactics of cybercriminals and the challenges faced by victims. In this blog post, we delve into the details of this disconcerting trend, explore the factors contributing to the surge, and discuss strategies to mitigate the impact of ransomware attacks. The Ransomware Payments Surge: A Disturbing Reality Chainanalysis report revealed a startling reality: ransomware payments are reaching record-breaking levels in 2023. In fact they state that ransomware attackers are on their way to their second-biggest year ever, as they have extorted at least $449.1 million through June. It was even revealed that the cumulative yearly ransomware revenue for 2023 has reached 90% of the 2022 total figure in the first half of the year. Understanding the Ransomware Ecosystem Why was there such a huge surge in ransomware payments? As it turns out, analysts believe that the driving force behind this steep increase in revenue is that cybercriminals have returned to targeting large organizations that can be extorted for large sums of money. Infamous ransomware groups like Clop, LockBit, BlackBasta, ALPHV/Blackcat, are leading this trend of high-range payments. For instance, Clop has an average payment size of $1.7million, and a median payment figure of $1.9 million. Clop ransomware gang is responsible for the MOVEit transfer theft-attack, which has impacted over 601 organizations as of 8 August 2023. This number of impacted organizations are still increasing! However, this is not to say that small ransomware payments are decreasing. Rather, small ransomware payments have also been observed to have grown. These ransomware as a service (RaaS) operations include Dharma, Phobos, and STOP/DJVU, with their average payment size of 2023 are $265, $1,719, and $619 respectively. Although it is important to note that these ransom amounts do vary depending on the target’s organizational size. The Tug of War: To Pay or Not to Pay Victims of ransomware attacks often find themselves caught in a moral and financial dilemma. Paying the ransom can facilitate data recovery, but it also fuels the cybercriminal economy and emboldens attackers. However, it is important to note that government agencies such as CISA, NCSC, FBI, ANSSI and CSA warn against paying the ransom. As payments do not guarantee that cybercriminals would provide decryption and that all files will be recovered. Furthermore, this will embolden cybercriminals to target more organizations, and even further encourage other threat actors to engage in the distribution of ransomware. Additionally, experts in the field also hypothesize that with this yearly decrease of organizations that are willing to pay the ransom, cybercriminals might further increase their ransom demands, and will aim to compensate these losses via huge payments from those that give into the demands. The Importance of Robust Cybersecurity Measures Prevention is the first line of defense against ransomware attacks. Organizations need to implement robust cybersecurity measures such as ensuring to regularly update their software, maintain secure and up-to-date data backups, carry out employee training, utilize advanced threat detection tools, and endpoint security solutions such as Endpoint Protection Platform (EPP) and Endpoint Detection and Response (EDR). These measures would help to fortify an organization’s defenses by helping to detect and neutralize ransomware attacks before they propagate within the network.
Takeaway The surging trajectory of ransomware payments in 2023 underscores the urgent need for robust cybersecurity measures and proactive defense strategies. By understanding the ransomware ecosystem, making informed decisions about payment, and investing in preventive measures, organizations and individuals can stand strong against the onslaught of cyber threats. Let us unite in our commitment to cybersecurity excellence, fortifying our digital landscapes and working together to create a safer and more resilient online world. Securing Your Organization With TAFA With the current cyber environment, organizations are facing increasingly sophisticated cyber threats. To protect against these threats, it is necessary to utilize cybersecurity solutions that can prevent zero-day and advanced cyber threats, and help ensure regulatory compliance. With our prevention first and zero-trust approach to security using Machine Learning (ML) and Artificial Intelligence (AI), TAFA Shield will strengthen your company's ability to prevent and block cyber attacks and threats. Not only do we protect your endpoints, but we also proactively detect and respond to cyber threats, provide managed SOC services to further improve your security posture, and lastly provide you with professional cybersecurity services that delivers guidance, support and expertise in designing, implementing and managing cybersecurity solutions tailored to your specific needs. Furthermore, with our comprehensive customized vulnerability assessment and penetration testing (VAPT) service, not only do we ensure the safety and security of your organization’s operation and data, but also we ensure that you will meet the required industrial and regulatory compliances. To learn more information about TAFA Shield ,our MSSP service, and our VAPT service, and how we can help your company, do not hesitate to contact us for more information. Related Topics Unraveling the MOVEit Data Breach: More Than 554 Organisations & 37 Million Individuals Affected Cybersecurity Wake-up Call: The Skyrocketing Breach Costs of 2023 At All-Time High The Common Signs Of Being Cyberattacked 7 Types of Cyber Security Measures SMEs Need to Protect Their Business
Back to Blog
As technology continues to transform the business landscape, the threat of data breaches looms larger than ever before. In an era marked by escalating cyber threats and data breaches, businesses worldwide find themselves at a crossroads when it comes to cybersecurity investment. The 2023 Cost of a Data Breach report by IBM reveals that the average data breach costs have reached an all-time high globally - US $4.45 million in 2023. This is a 15% increase over the last 3 years. However, only 51% of the surveyed organizations that have experienced more than 1 breach plan to increase their security investments, which includes incident response planning and testing, employee training and threat detection and response tools. Rather, 57% of the surveyed organizations are more likely to pass incident costs onto their consumers. This is worrying due to the escalating sophisticated tactics that cybercriminals are employing. In ASEAN The average data breach costs in ASEAN have also reached a record high of US$3.05 million per incident. With the financial and energy sectors having the average highest cost per breach - US$4.81 million and US$3.60 million respectively. Key Findings 1. Security AI & Automation Speeds Breach Identification & Containment “Time is the new currency in cybersecurity both for the defenders and the attackers” Chris McCurdy, General Manager, IBM Early detection and a fast response do help to significantly reduce the impact of a breach. Security AI & Automation had the biggest impact on speed of breach identification and containment for the surveyed organizations. Organizations that heavily utilized both AI and automation experienced a data breach lifecycle that was 108 shorter compared to organizations that did not deploy these technologies (214 days versus 322 days). Hence, investments in threat detection and response that help accelerate speed and efficiency, such as security AI and automation, are essential. As AI and automation is one of the biggest cost and time saving factors in the report. 2. Security AI & Automation Are Cost Saving Organizations that deployed security AI and automation, on average, shortens the breach lifecycle, as compared to those who do not, experienced significantly lower incident costs. They saved an average of US$1.76 million compared to those that had limited or no use. This is the biggest cost saver identified in the IBM report. This is especially important as threat actors have reduced the average time to complete a ransomware attack. With 40% of surveyed organizations not deploying security AI and automation, there are gaps in which organizations can boost their security posture through boosting detection and response speed. 3. Reporting to Law Enforcement Lower Costs Many organizations that have been ransomware, have this misconception that by involving law enforcement, this would drive up their incident costs. Surveyed organizations that were ransomware victims showed that: 37% preferred not to involve law enforcement, and 47% paid the ransom. Rather it’s the opposite, paying the ransom and avoiding law enforcement drives up the cost. The IBM report found that ransomware victims that involved law enforcement saved US$470,000 in average costs of a breach, compared to those that did not involve law enforcement. Furthermore, they also experienced a shorter average breach life cycle that was 33 days shorter, compared to those that did not involve law enforcement. This shows that paying the ransom and not involving law enforcement, not only drives up your data breach cost but also slows your response to the breach. 4. Detection Gaps Although defenders were able to stop a higher proportion of ransomware attacks, threat actors are still consistently finding ways to slip through the security defense. IBM reports that the surveyed organization's internal security identified just 33% of breaches, while neutral 3rd parties such as law enforcement identified 40% of breaches, and the remaining 27% of breaches were disclosed by the attackers. However, organizations that discovered the breach themselves saved nearly US$1million in breach costs than those disclosed by the attacker (US$4.3 million and US$5.23 million respectively). Furthermore, breaches disclosed by the attacker had a lifecycle nearly 80 days longer compared to organizations that discovered the breach internally (320 days vs 241 days). The significant cost and time savings that comes with early detection does show that investing in strategies that can help you do so will pay off in the long run. Usage of threat detection and response tools, employee training, and incident response planning and testing, are good strategies to do so. Other Important Findings 1. Multiple Environments Led To Higher Breach Costs
39% of data breaches studied resulted in the loss of data stored across multiple environments - the cloud, on premise. These data breaches were not only costlier but also more difficult to contain than other types of breaches (i.e. just the cloud or just solely on-premise storage). It took 292 days, 15 days LONGER than the global average, to contain the breach, and also it contributed about US$750,000 more in average breach costs. Hence, organizations need to ensure that they are protecting their multiple environments - all of them! 2. Healthcare Breaches Cost Escalates The average costs of the studied breach in healthcare reached nearly US$11 million in 2023. This is a 53% increase in cost since 2020. This coincides with reports about the healthcare industry facing an alarming rise in cyber threats, with healthcare organizations becoming the top target for ransomware gangs. For more information do see this article: The Vital Importance of Cybersecurity in Healthcare: Safeguarding Lives and Data 3. Critical Infrastructure Breach Costs Escalates As Well Surveyed critical infrastructure organizations experienced a 4.5% increase in the average breach cost compared to the previous year - from US$4.82 million to US$5.04 million. This is US$590,000 higher than the global average breach cost. 4. DevSecOps Approach Lowers Data Breach Cost Surveyed organizations with a high level of DevSecOps had a lower global average cost of a data breach by nearly US$1.7 million than those with a low level or does not use the DevSecOps approach. About the Report This report is based on the analysis of real-world data breaches at 553 organizations globally between March 2022 - March 2023, with thousands of individuals interviewed and cost factors analyzed. Takeaway The 2023 Cost of a Data Breach Report by IBM offers valuable insights into the current state of data breaches and their financial impact. As the cyber threat landscape continues to evolve, organizations must prioritize cybersecurity measures to protect sensitive data and their reputation. By understanding the key factors influencing breach costs and embracing proactive cybersecurity strategies, businesses can bolster their resilience and defend against cyber adversaries. Let us heed the lessons from this report and work together to fortify our digital defenses, securing a safer and more prosperous digital future for businesses and consumers alike. Securing Your Organization With TAFA With the current cyber environment, organizations are facing increasingly sophisticated cyber threats. To protect against these threats, it is necessary to utilize cybersecurity solutions that can prevent zero-day and advanced cyber threats, and help ensure regulatory compliance. With our prevention first and zero-trust approach to security using Machine Learning (ML) and Artificial Intelligence (AI), TAFA Shield will strengthen your company's ability to prevent and block cyber attacks and threats. Not only do we protect your endpoints, but we also proactively detect and respond to cyber threats, provide managed SOC services to further improve your security posture, and lastly provide you with professional cybersecurity services that delivers guidance, support and expertise in designing, implementing and managing cybersecurity solutions tailored to your specific needs. Furthermore, with our comprehensive customized vulnerability assessment and penetration testing (VAPT) service, not only do we ensure the safety and security of your organization’s operation and data, but also we ensure that you will meet the required industrial and regulatory compliances. To learn more information about TAFA Shield and our VAPT service, and how we can help your company, do not hesitate to contact us for more information. Related Topics The Vital Importance of Cybersecurity in Healthcare: Safeguarding Lives and Data The Common Signs Of Being Cyberattacked 7 Types of Cyber Security Measures SMEs Need to Protect Their Business Unraveling the MOVEit Data Breach: More Than 554 Organisations & 37 Million Individuals Affected
Back to Blog
Unraveling the MOVEit Data Breach: More Than 554 Organizations & 37 Million Individuals Affected2/8/2023 Cybersecurity breaches have sadly become an all-too-common occurrence in today's digital landscape, with organizations of all sizes and industries falling victim to cyberattacks.
The recent MOVEit theft-attack carried out by a notorious ransomware group has sent shockwaves through the cybersecurity community, exposing a rapidly expanding threat landscape. With the number of known impacted organizations so far surpassing 554 and the number of individual victims being at least 37 million as of 1 August 2023. The Scale Of Impact From Corvus research, the number of ransomware attacks increased by roughly 180% in June 2023 as compared to the same month last year. This is fueled by the MOVEit transfer attack whereby nearly 20% of the alleged June victims were associated with the MOVEit breach. Based on Clop’s website, 206 organizations have been listed as of 26 July, whereby 2 in 5 victims have yet to publicly disclose that they have been compromised. Affected organizations come from all over the world. As of 1 August the top affected organizations came from the U.S. with 398 affected organizations, followed by 35 organizations from Germany, 25 organizations from Canada, and 24 organizations from the UK. The most heavily impacted sectors are the education and the finance & professional services, which accounts for 23.8% and 22% of the total incidents respectively. Many organizations have been impacted due to their direct-use of MOVEit, while others have been impacted due to third-party vendors’ use of MOVEit. At least 136 organizations that did not use MOVEit directly have been compromised through third-party vendors. As Emsisoft reported, based on the figures released by affected organizations, at least 37 million individuals’ personal details have been compromised and have been held to ransom. The number of individual victims are actually much higher than that as only a fifth of the affected organizations have publicly released the total number of individuals who had their personal information exposed. What Happened? MOVEit is a file transfer platform, which is used by thousands of both private and public sectors globally, which includes governments, healthcare organizations, law firms, education service providers and financial institutions. Around 29 May 2023, MOVEit was hacked by the Clop ransomware group via the use of a zero-day vulnerability in Progress Software’s MOVEit, and data was stolen from many organizations, whose numbers are not yet confirmed. On 31 May, Progress disclosed a zero-day vulnerability and issued a patch. By 5 June, the first wave of victims started to disclose the breaches related to the MOVEit theft-attack, which included the BBC, British Airways and the Nova Scotia government. On 6 June, Clop published a statement on their dark web website claiming responsibility for the attack, and set a deadline (14 June) for victims to contact the group to begin negotiations. Although they stated that the data stolen from governments and police services were deleted, the claim was proven to be inaccurate when Clop listed the UK’s Office of Communications (Ofcom) and Ireland’s Commission for Communications Regulation (Comreg) on their website. Since then, the number of disclosures from organizations affected by this attack has been continually increasing, and there seems to be no sign of stopping as of now. With the Clop ransomware group continuing to name more alleged victims on their website. What Victims Have To Beware Of It is important to be aware that with the large amounts of data that Clop possessed, individuals and organizations need to be cautious for phishing attacks and business email compromise (BEC) attacks. Some of the best practices against phishing are being skeptical of unsolicited communications, beware of impersonation tactics, think before you click, verify website security, strengthen your passwords, always keep software up to date, education, use reliable security software. For more information on the above best practices do see this article: Protect Yourself: Best Practices to Combat Phishing Attacks For organizations, this highlights that not only do they have to be aware of their own security, but also they need to be concerned about the security of their third-party vendors. Affected organizations will definitely find this incident to be costly as not only do they need to provide remediation, but also they will need to provide credit monitoring to the affected individuals, and also account for lawsuits. Countering the Threat: A Proactive Cyber Defense This MOVEit mass theft-attack serves as a wake-up call for organizations to reassess their cybersecurity posture and strengthen their defenses against cyber threats. To effectively combat such sophisticated attacks, businesses must adopt a proactive approach centered around cyber resilience:
Takeaway The MOVEit theft-attack underscores the ever-present and evolving threat landscape that businesses face in the digital age. With the number of impacted organizations soaring beyond 516 and the devastating impacts this has on individual victims, it is imperative that organizations remain vigilant and proactive in defending against ransomware attacks. By adopting robust security practices, staying informed, regularly backup critical data, collaborating with experts, and regularly updating all software and systems, organizations can shield themselves from the ominous ransomware spree and ensure a secure and promising digital future. To emphasize,fostering a proactive and resilient approach to thwart cyber extortion attempts is of paramount importance. Through these approaches, we can safeguard our organizations from the relentless attacks of cybercriminals. Securing Your Organization With TAFA With the current cyber environment, organizations are facing increasingly sophisticated cyber threats such as the MOVEit theft-attack. To protect against these threats, it is necessary to utilize cybersecurity solutions that can prevent zero-day and advanced cyber threats, and help ensure regulatory compliance. With our prevention first and zero-trust approach to security using Machine Learning (ML) and Artificial Intelligence (AI), TAFA Shield will strengthen your company's ability to prevent and block cyber attacks and threats. Not only do we protect your endpoints, but we also proactively detect and respond to cyber threats, provide managed SOC services to further improve your security posture, and lastly provide you with professional cybersecurity services that delivers guidance, support and expertise in designing, implementing and managing cybersecurity solutions tailored to your specific needs. Furthermore, with our comprehensive customized vulnerability assessment and penetration testing (VAPT) service, not only do we ensure the safety and security of your organization’s operation and data, but also we ensure that you will meet the required industrial and regulatory compliances. To learn more information about TAFA Shield and our VAPT service, and how we can help your company, do not hesitate to contact us for more information. Related Topics What is Vulnerability Assessment & Penetration Testing (VAPT)? Definition, Benefits & It's Importance The Common Signs Of Being Cyberattacked 7 Types of Cyber Security Measures SMEs Need to Protect Their Business |
|
© 2021, TAFA HOLDINGS (S) PTE LTD. ALL RIGHTS RESERVED
|

 RSS Feed
RSS Feed