AuthorTAFA Archives
April 2024
Categories
All
|
Back to Blog
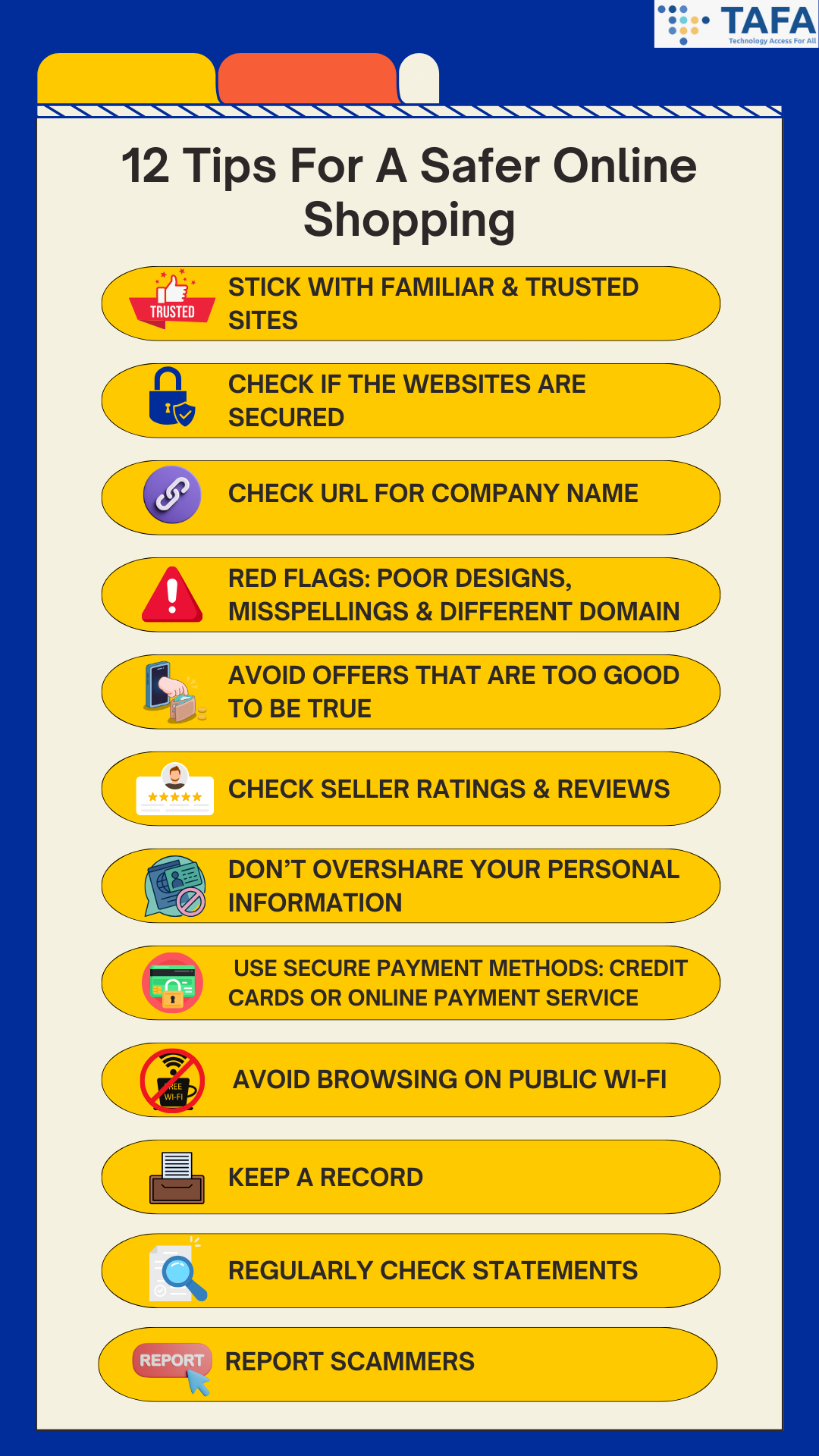
Online shopping has made possibilities endless. From the comfort of your home, you can browse, choose, and purchase anything you desire. However, as the digital marketplace expands, so do the perils that come with it. There are many threats that lurk online, and one such threat are online shopping scams (which can also be known as ecommerce fraud). From stealing personal and financial information to bogus returns, the highest numbers impacted by online shopping scams are consumers. Tips To Protect Yourself Against Online Shopping Scams 1) Stick With Familiar & Trusted Sites
It is highly recommended to shop directly from online retailers that you are familiar with and trust. Avoid typing the name of the retailer into your browser bar, as a tiny typo can lead you to a fake site that imitates the real one. These fake sites may lead you to divulging personal and financial information. It is best to bookmark your trusted and familiar sites to ensure you are going to their legitimate sites. 2) Check If The Websites Are Secured Remember ‘S’ stands for SECURE. Before you visit an e-commerce site, the first thing you must do is to inspect the URL of the page. Secure sites use HTTPS, and not HTTP. This indicates a secure, encrypted connection. A padlocked symbol should also appear at the address bar. This means that you are safely connected to the website. Ensure to share sensitive information (such as your personal and payment details) ONLY on official secured websites. However, this does not mean that you are completely safe, as many phishing sites do use HTTPS. 3) Check URL For Company Name In addition to checking for HTTPS, check the URL to ensure that the company name is included, and ensure that the company name is spelt correctly. This will help you determine if the site is actually operated by said company or it’s a scam site. 4) Red Flags: Poor Designs, Misspellings & Different Domain Check and recognize for signs of potentially fraudulent websites such as misspelt words, typos, unprofessional designs, and low resolution images. If the website does not contain any branding, be cautious of the website. Also beware of scam sites that will use different top-level domains (e.g. using .net instead of .com). 5) Avoid Offers That Are Too Good To Be True Do you always see ads on your social media that offer huge discounts, way cheaper than usual products, or free offers which you only have to pay shipping for? This is a common tactic that cybercriminals use to bait unsuspecting shoppers with incredible deals to entice them into falling for their scams. It is also recommended to compare prices before buying - as unusually low prices could alert you that this website could be a scam. Remember if an offer looks too good to be true, it usually is! 6) Check Seller Ratings & Reviews If you don’t know the online store, it is best to conduct background checks via looking at sites that review and rate e-stores. If there are no reviews of the e-store or do not have good ratings, it is best to steer clear from the e-store, and don’t order from them. 7) Don’t Overshare Your Personal Information No online shopping retailer will need your social security number, internet banking details and/or OTP. If a site requests this kind of sensitive information, EXIT the site immediately! As if they get your sensitive information, and credit card number, they can steal your identity. A good rule of thumb is to provide reputable websites as minimal information necessary to complete a purchase. 8) Use Secure Payment Methods: Credit Cards or Online Payment Service Always use a credit card or an online payment service such as Paypal or Google Wallet, instead of a debit card. As these payment methods do not give the seller direct access to your bank account. Furthermore, most credit cards do offer payment protection. This means that you will face zero liability for fraud. If you want to have added security, you can use a virtual credit card. As virtual credit cards generate a unique card number for each transaction made, hence protecting your real account number. Even if a cybercriminal got your virtual credit card number and attempted to use it, they won’t be able to. 9) Avoid Browsing On Public Wi-Fi Public Wi-Fi networks often lack a security measure - encryption, which encrypts your information sent from your device or computer to the router so strangers cannot read it. Without encryption, your information (e.g. your passwords, identity and financial information) that is sent over these networks can be intercepted by cybercriminals. If you have no choice but to use public Wi-Fi, it is highly recommended that you use VPN (virtual private network) to protect your privacy. As VPN helps encrypt the traffic between your device and the VPN server, which means that cybercriminals will find it much more difficult to obtain access to your data on your device. 10) Keep A Record Always keep records of your online transactions. Ensure to save the receipts, order confirmation number, tracking number, product description and price. It is also a good idea to save all emails you receive and send to the seller. As this will come into use if there is an issue later on. 11) Regularly Check Statements Do a weekly regular check of your bank and credit/debit card statements for any fraudulent charges. Do not wait for your bills to come at the end of the month! It is highly recommended to also set up alerts for any new activity on your card - this helps to keep up on top of any new charges made to your accounts. 12) Report Scammers Do not ever feel embarrassed for being scammed. Instead get very loud about it. (a) Contact the platform’s support team for assistance. (b) File a police report. In Singapore, you can file a report via calling the police hotline at 1800 255 0000, or using the I-Witness eService, or file at any nearest Neighbourhood Police Centre or Post. (c) Lodge a complaint with the Consumers Association of Singapore (CASE) Conclusion In the labyrinthine world of online shopping, vigilance and knowledge are your best allies. By arming yourself with information, staying cautious, and implementing best practices, you can navigate the digital marketplace with confidence and keep the predators of the virtual world at bay. Let your online shopping adventures be fruitful and secure, guarded by the wisdom imparted in this guide. Remember, in the digital realm, knowledge is power, and prudent choices are your most potent defence. Happy shopping! Related Topics A Personal Cybersecurity Checklist - How Cyber Secure Are You? Safeguarding Your Digital Fortress: Defending Against the Top 8 Password Attacks Password Security Tips: How To Fortify Your Password Security The Risks of Public Wi-Fi & Tips On How To Stay Safe Is This QR Code Safe? Top Tips to Ensure Your QR Scans are Secure Unmasking Phishing: Your Guide to Spotting The Signs of Phishing
Back to Blog
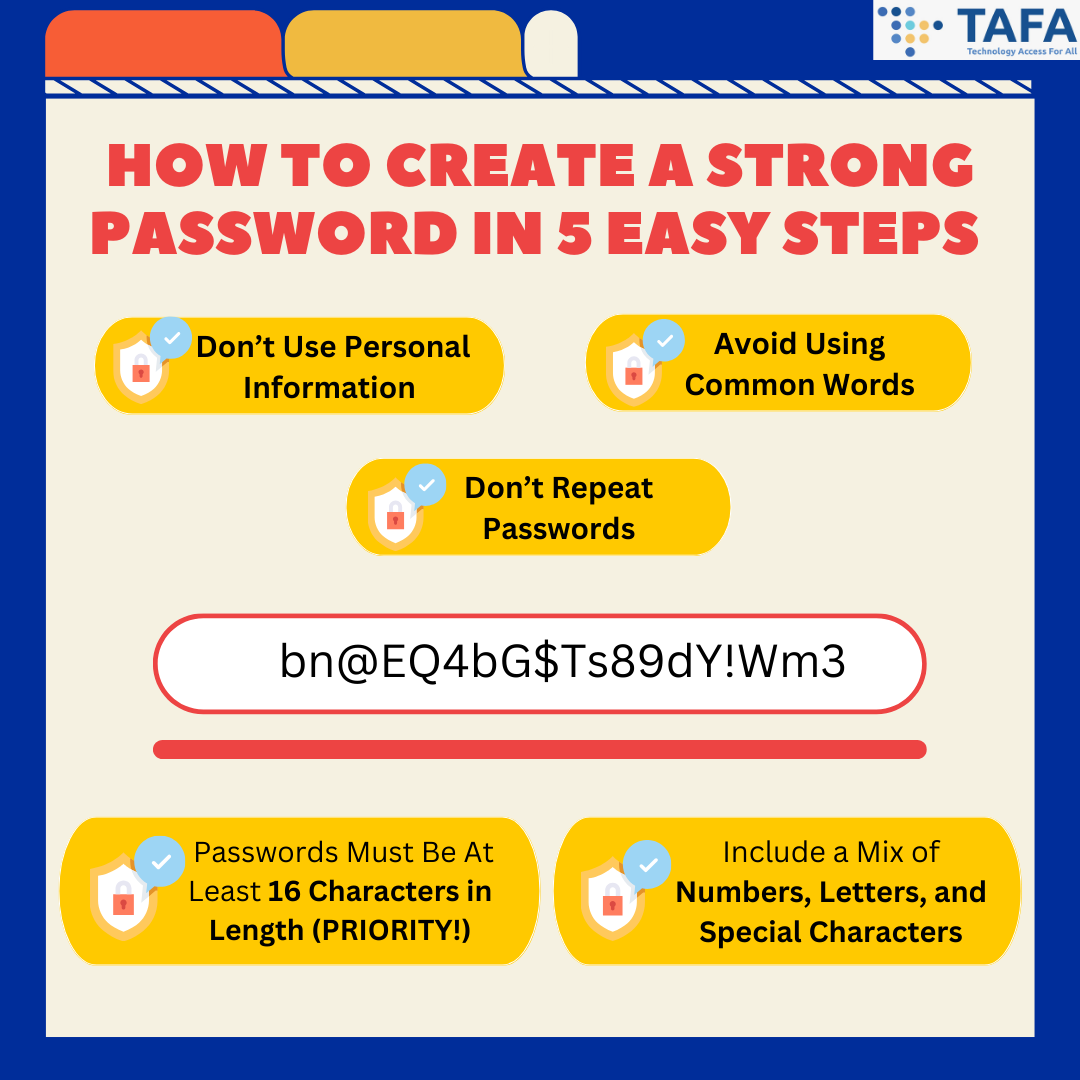
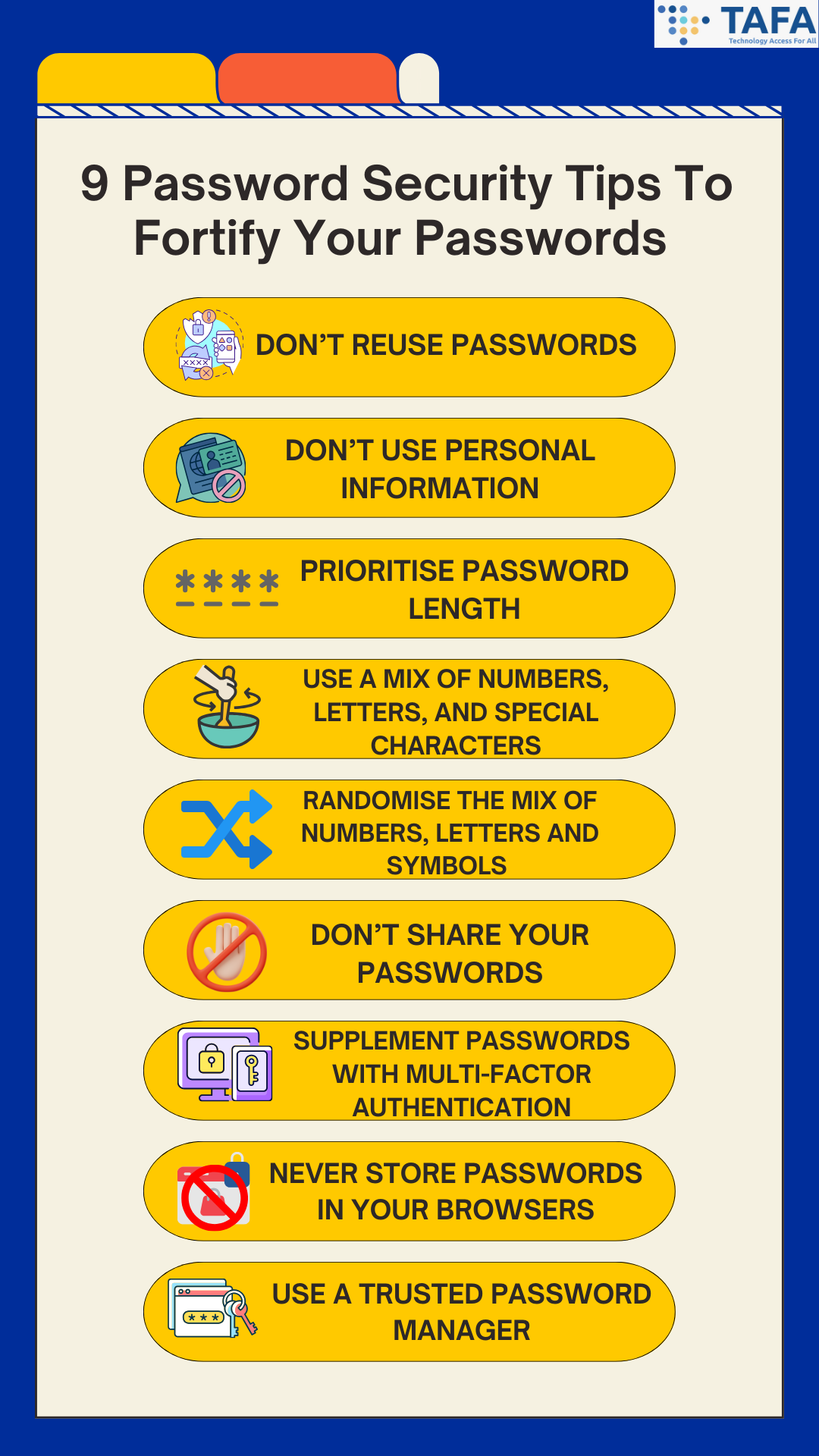
In the labyrinthine world of cyberspace, where opportunities abound, dangers also lurk. Your online identity is akin to a precious treasure, one that needs the staunchest defence. Passwords, the keys to protecting your online digital life, demand particular attention and vigilance. How do I create a strong password? How do I improve my password security? Don’t worry, this article is here to help you. We will first guide you on how to create a strong password, and then we will list down password security tips that can be easily followed to ensure you can fortify your security, thus helping you live a more cyber safe lifestyle. Why Do I Need Strong Passwords? You may wonder: why do I need strong passwords anyway? The reality is that even though most websites are secure, there is always a chance that cybercriminals may try to access or steal your personal information. Hence, password security is of utmost importance, especially with the consequences of what could happen if you have weak password security, such as identity theft and data breaches. To learn more about the top 8 types of password attacks, click here. A strong password is one of the best ways to defend your accounts and sensitive information from cybercriminals. How To Create A Strong Password In 5 Easy Steps 1. Don’t Use Personal Information. Never include personal information in your passwords, such as names and birthdates of your relatives, child or pets, phone numbers or phone numbers. As this information can be easily found especially on social media. Don’t make it easy for hackers to guess your passwords! 2. Include a Mix of Numbers, Uppercase and Lowercase Letters, and Special Characters. Strong passwords should be complex and include a combination of numbers, letters, and special characters. Ensure that there are no repetitive or sequential characters (e.g. ‘eeeeee’, ‘123abc’). 3. Passwords Must Be At Least 16 Characters in Length. Password length is extremely important as the longer the password, the less chance of hackers can easily crack your passwords. It is recommended that your passwords should be at least 16 characters in length. 4. Avoid Using Common Words. In common words, it is best to substitute letters with numbers and special characters (e.g. punctuation marks and/or symbols). Hackers can use malicious programs to process every word in the dictionary to crack passwords. 5. Don’t Repeat Passwords, Like Ever. Reusing the same password for different accounts will put you at risk of credential stuffing attacks, which is essentially where cybercriminals use the stolen usernames and passwords and test them against multiple sites. 9 Password Security Tips To Fortify Your Passwords Utilise these password security tips to help you improve your cyber security, and help you live a more cyber safe lifestyle. 1. Don’t Reuse Passwords. Recycling passwords will put you at risk of credential stuffing attacks.
2. Don’t Use Personal Information. Never use names, birthdates, addresses or phone numbers in your passwords as this information can be easily found. This jeopardises the effectiveness of passwords against cyberattacks. 3. Prioritise Password Length. As length trumps complexity. The longer your password length is, the harder it is for cybercriminals to guess your password. As there are more possible permutations, making it harder for cybercriminals to crack. It is recommended that passwords should be at least 16 characters long. 4. Use A Mix of Numbers, Uppercase and Lowercase Letters, and Special Characters. Create a password that is at least 12 characters long, which includes a mix of uppercase, lowercase, numbers and special characters. This will help you create a strong unique password which is the blueprint to a rock-solid cybersecurity abode. 5. Randomise the Mix of Numbers, Uppercase and Lowercase Letters, and Special Characters. Ensure to randomise the mix of numbers, letters and special characters to protect against password spraying attacks, which is a hacking technique whereby cybercriminals use a list of frequently chosen passwords to guess the passwords of their potential victim. 6. Don’t Share Your Passwords. Never tell anyone your passwords even to family and friends, and be especially cautious of emails or messages that are trying to persuade you via urgency, to reveal your passwords. Usually it is a trick! 7. Supplement Passwords With Multi-Factor Authentication (MFA). Passwords should not be the sole method for authenticating an identity or verifying access authorisations. It is best to include MFA, such as biometrics or one-time codes as an additional layer of security and protection. 8. Never Store Passwords In Your Browsers. Many browsers do give the option of saving your passwords. Although this seems convenient, it is poor password management. Cybercriminals can access and steal these saved passwords via manipulation of cookies. 9. Use a Trusted Password Manager. Password managers are a secure way to store all your passwords as they help generate and remember different complex passwords for all of your accounts, and encrypt them for additional security. Conclusion In the vast digital realm, your passwords are the sentinels guarding your virtual kingdom. By understanding their significance, crafting robust defences, and employing best practices, you can reinforce these sentinels, ensuring a formidable defence against potential invaders. Let your online presence be a citadel, unassailable and secure. Embrace the art of password security, for in this age of digital innovation, your safety is the ultimate treasure worth protecting. Venture forth into the digital wilderness with wisdom, and may your passwords be your invincible guardians. Related Topics A Personal Cybersecurity Checklist - How Cyber Secure Are You? Safeguarding Your Digital Fortress: Defending Against the Top 8 Password Attacks The Risks of Public Wi-Fi & Tips On How To Stay Safe Is This QR Code Safe? Top Tips to Ensure Your QR Scans are Secure Unmasking Phishing: Your Guide to Spotting The Signs of Phishing
Back to Blog
Last week, breaches and cyberattacks occurred across several industries from electronics, to insurance to criminal courts. Devastating consequences of past cyberattacks on organisations have also been reported - with 4 million more 23andMe user records being leaked. Furthermore, an advisory from CISA to patch the latest vulnerability has been issued. It is highly recommended to not only be aware of the flaw but to also update them as soon as possible.
Read on to receive a quick summary of what happened this week in the space of cybersecurity. Hacker has now leaked 4 million more 23andMe user records. The hacker, Golem, has published a new 23andMe dataset which contains records of 4 million users on BreachForum, a cybercrime forum. TechCrunch has found that some of the newly leaked stolen data matches the known and public 23andMe user and genetic information. Golem claimed this dataset contains information on people from Great Britain as well as data from “the wealthiest people living in the U.S and Western Europe”. Casio’s data breach impacts customers from 149 countries. Casio, a Japanese electronic manufacturer, disclosed a data breach that impacts customers from 149 countries. Casio detected the incident on 11 October following the failure of a ClassPad database within the company’s development environment. On 12 October, there was evidence that suggests that the cybercriminals have accessed their customers’ personal information. The exposed personal information includes their names, email addresses, countries of residence, service usage details, and purchase information such as payment methods, order specifics, and licence codes. Casio emphasised that no credit card information was stored in the compromised database. In total, it was found that the cybercriminals accessed 91,921 items belonging to Japanese customers (this includes individuals and 1,108 educational institutional customers), and 35,049 records of customers from 148 countries outside of Japan. D-Link confirms data breach: Compromised information found for sale on a dark web forum. D-Link, a Taiwanese networking equipment manufacturer, confirmed a data breach after stolen information from their network was found for sale on BreachForums earlier this month. The attacker claims to have stolen source code for D-Link’s D-View network management software, as well as millions of entries that contains the personal information of customers and employees, this includes details on the company’s CEO. The stolen personal information includes names, emails, addresses, phone numbers, account registration dates, and users’ last sign-in dates. The data has been available for purchase on the hacking forum since 1st October, and the attackers demand $500 for the stolen information. However, D-Link has stated that from their investigation, the compromised system contains roughly 700 records that are outdated and fragmented, and has been inactive for at least 7 years. D-Link stated that this breach occurred due to an employee falling for a phishing attack, which granted the attacker access to the company’s network. In response to the breach, D-Link shut down all potentially impacted servers and disabled all but 2 user accounts used during the investigation. Henry Schein discloses data breach. Henry Schein, an American distributor of health care products and services, disclosed that part of their manufacturing and distribution business has been data breached. In response, the company took certain systems offline and is working to resolve the issue. They are working with 3rd party experts to investigate the impact of data breach on data and to respond to the breach. Furthermore, relevant law enforcement authorities were notified. The International Criminal Court breached for espionage purposes. The International Criminal Court has disclosed that the 19 September cyberattack was a targeted operation for espionage purposes. However, in the statement ICC did add that current evidence is insufficient to attribute the attack, but the Dutch law enforcement is currently running the criminal investigation. The impact of the attack remains unclear, and no evidence so far points that the Court’s data has been compromised. The ICC says that they have taken measures to address any compromise to data belonging to individuals, organisations, and States. ICC is reinforcing their risk management framework and preparing for potential repercussions from the cyberattack, such as security risks to victims and witnesses. Steps for improving digital security have also been accelerated. Over 40,000 Cisco IOS XE devices have been compromised after hackers exploited a vulnerability. More than 40,000 Cisco devices that run the IOS XE operating system have been compromised after hackers exploited a recently disclosed maximum severity vulnerability (tracked as CVE-2023-20198). As of now, there is no patch or workaround available, and the only recommendation is for customers to “disable the HTTP Server feature on all internet-facing systems” to secure the devices. Threat actors via this vulnerability, create a high-privilege account on affected hosts and take full control of the device. Based on Cisco’s analysis, the threat actor collects details about the device and carries out preliminary reconnaissance activity. The threat actors also clear logs and remove users to perhaps hide their activity. Update: As of 22 October, the number of Cisco IOS XE devices hacked with a malicious backdoor malware has decreased from over 50,000 impacted devices to only a few hundred (100-1,200), with researchers unsure what caused the sharp decline. It was hypothesised that this could be because threat actors behind the attacks are deploying an update to hide their presence, thus causing the implants to no longer be seen on scans. Kansas courts IT systems still offline after “security incident”. Information systems of state courts across Kansas are still offline as of 16 October after it was disrupted after a “security incident”. Multiple systems crucial to daily court operations across the state have been impacted, this includes the Kansas Courts’ eFiling system used by attorneys to submit case documents, the electronic payments system (includes credit card transactions and electronic checks), and the case management systems employed by district and appellate courts for case processing. In response, the state’s Supreme Court issued an administrative order on 16 October to confirm that the clerk offices in appellate courts and most district courts are offline. Despite this issue, courts remain operational. However, clerks are currently unable to accept electronic filings or payments, but they do accept pape4r filings and filings by fax. American Family Insurance confirms cyberattack is behind IT outages. American Family Insurance, an insurance giant, has confirmed they suffered a cyberattack and had to shut down some of their IT systems to prevent the spread of the cyberattack. This comes after customers reported website outages all week. Since the past weekend, American Family Insurance has suffered IT outages that impact their phone service, building connectivity, and online services. Customers have reported being unable to pay bills or file claims online, and were only met with messages that state that their online site is down and to contact them via phone instead. CISA, FBI urge administrators to patch Atlassian Confluence immediately. CISA, FBI and MS-ISAC warned network administrators to immediately patch their Atlassian Confluence servers against a maximum severity vulnerability (tracked as CVE-2023-22515) that is exploited in attacks. This flaw affects Confluence Data Center and Server 8.o.o and later, and is remotely exploitable in low-complexity attacks that don’t require user interaction. Atlassian highly advised customers to upgrade their Confluence instances as soon as possible, after they release security updates to fix this vulnerability. Those who can’t upgrade were encouraged to shut down impacted instances or isolate them from Internet access. Administrators were also highly advised to check for indicators of compromise - this includes new or suspicious admin user accounts. That is all! Enjoy the rest of the week and don't forget to update your devices and systems to the latest patches!
Back to Blog
In the vast ocean of the internet, phishing scams are the lurking predators waiting for an unsuspecting click. Despite our best efforts to stay vigilant, it's possible to fall into the trap of a phishing scam. Fear not! This article will guide you on what to do if you find yourself fallen for a phishing scam. What is Phishing? Phishing is one of the most popular and common cyber scams, whereby cybercriminals either send malware or steal your sensitive information by pretending to be a legitimate sender (i.e. online store, a bank, your family or friends). Phishing is a form of social engineering, which means that cybercriminals use psychology to convince their victims to take an action they may not normally take. Here is a guide to spot the signs of phishing, click here. What To Do If I Fell For A Phishing Scam Here are some simple steps you can take: 1) Change Affected Passwords
Immediately change the passwords for the affected accounts to prevent further unauthorised access. It is also best to change all accounts' passwords (if you can). Ensure that your passwords are strong and unique for extra security. They must be at least 12 characters long, which includes a mix of uppercase, lowercase, numbers and special characters. 2) Enable Multi-Factor Authentication (MFA) MFA isn't just an option; it's a necessity. By using another form of ID, such as security tokens, biometrics, SMS authorisation codes or authenticator apps will help add an extra layer of security. This will make it harder for hackers to gain unauthorised access to your online accounts, even if they steal your password. 3) Contact Affected Institutions If you share any financial information (such as your bank account number, passwords, PIN number), notify your bank and credit card companies. This can help you recover any lost finances but also prevent any further losses. The bank and credit card providers will also monitor for any suspicious transactions. It is also important to alert relevant social media platforms and request assistance in securing or closing compromised accounts. 4) Scan your device for malware or viruses If there was a suspicious link or attachment in the email or text message, it is best to run a thorough scan of your device to detect and remove any malware or viruses that might have been downloaded during the phishing incident. 5) Report the Phishing Incident If you have incurred monetary loss, loss of personal information, or discovered that your online account has been compromised or hacked, file a police report IMMEDIATELY. In Singapore, you can file a report via calling the police hotline at 1800 255 0000, or using the I-Witness eService, or file at any nearest Neighbourhood Police Centre or Post. If you are in Singapore and need to seek any scam-related advice, you can call the anti-scam hotline: 1800-772 6688 or visit scamalert.sg 6) Regularly Monitor Your Accounts Keep a close eye on your bank statements, credit reports, and other sensitive accounts for any unauthorised activity. If you notice anything unusual, report it immediately to the respective institution and take necessary action. Conclusion Falling victim to a phishing scam doesn't mark the end of your cybersecurity journey; it's a crucial lesson to learn from. By acting swiftly, reporting the incident, and fortifying your digital defences, you can rise stronger and wiser from the experience. Remember, in the face of a phishing scam, your resilience and proactive response can set you on the path to a safer and more secure online voyage. Stay vigilant, stay educated, and let adversity be the wind in your cybersecurity sails. Related Topics Unmasking Phishing: Your Guide to Spotting The Signs of Phishing The Rise Of Phishing: Safeguarding Against Digital Deception Protect Yourself: Best Practices to Combat Phishing Attack The Risks of Public Wi-Fi & Tips On How To Stay Safe Is This QR Code Safe? Top Tips to Ensure Your QR Scans are Secure
Back to Blog
Last week, breaches and cyberattacks occurred across several industries from airlines to construction to government agencies. Devastating consequences of past cyberattacks on organisations have also been reported - with Equifax being fined $13.4 million by UK regulators for the 2017 data breach, and 23andMe facing multiple class action lawsuits. Furthermore, new vulnerabilities and patches have also been found and released. It is highly recommended to not only be aware of them but to also update them when possible.
Read on to receive a quick summary of what happened this week in the space of cybersecurity. Spanish Airline, Air Europa hit by credit card system breach: Customers warned to cancel credit cards. Air Europa warned affected customers on Monday to cancel their credit cards after cybercriminals managed to breach one of their systems which consisted of customers’ bank card data. The credit card details exposed include card numbers, expiration dates, and the 3 digit CVV (Card Verification Value) code on the back of the payment cards. Affected customers were warned to cancel their cards used on their website due to the “risk of card spoofing and fraud” and to “prevent fraudulent use”. Air Europa has also said in the email that they have secured their systems, and have reported to the relevant authorities. Simpson Manufacturing, U.S. construction giant, cyberattacked: Forced to shut down their IT systems. Simpson Manufacturing Company were forced to shut down some of their IT systems to contain a cyberattack, which caused disruptions in their IT infrastructure and applications. The company has taken steps to stop and address this issue, and have also reported this incident to relevant authorities. However, Simpson also stated that this cyberattack is expected to continue to cause disruption to parts of their business operations. BlackCat ransomware gang claims Florida circuit court attack. BlackCat ransomware gang (also known as ALPHV) claimed an attack that affected state courts across Northwest Florida (which is part of the First Judicial Court) last week. The ransomware gang have allegedly acquired personal details of employees (this includes judges) such as their social security number and CVs. BlackCat also claimed that they have a comprehensive network map of the court’s systems. This includes local and remote service credentials. Based on the presence of Florida’s First Judicial Circuit on their data leak page, it can be suggested that the court has either not engaged with BlackCat on ransom negotiations or decided to not meet their demands. BianLian extortion group claims recent Air Canada breach. The BianLian extortion group claims to have breached the network of Air Canada and stole 210GB of data. Although the company stated in a statement that only “limited personal information of some employees and records” were compromised, the extortion group now claims that the stolen documents contained much more extensive information. They have also shared screenshots of the stolen data on their data leak site, and detailed description of what was stolen from the airline’s network. BianLian claimed to have stolen technical and operational data from 2008 to 2023. This includes details about the company’s technical and security challenges, SQL backups, employees’ personal information, data relating to vendors and suppliers, confidential documents, and archives from company databases. Air Canada is aware of BianLian extortion threats, but will not comment on any claims made, and will not add anything to what they had stated publicly. Air Canada also warned some of their customers in emails sent on 11 October to enable SMS multi-factor authentication on their Aeroplan accounts, and use strong passwords. UK Regulator fines Equifax $13.4 million for 2017 data breach. The UK’s Financial Conduct Authority (FCA) has fined Equifax Ltd. $13.4 million for failing to take the appropriate steps to protect the personal data of 13.8 million UK consumers that was stolen in the 2017 data breach. The personal data compromised were names, birth dates, phone numbers, residential addresses, Equifax membership login details, and partially exposed credit card details. The FCA ruled that the theft of UK consumers data was “entirely preventable” as Equifax did not treat their relationship with their parent company in the U.S. as outsourcing, hence they did not provide sufficient oversight how the data sent was managed and protected. The FCA also said that Equifax public statements on the incident’s impact “gave an inaccurate impression of the number of consumers affected.” They also added the company mishandled complaints from UK consumers as they failed to maintain quality assurance checks for the complaints. Shadow PC warns customers of data breach as cybercriminal claims to be selling stolen customers’ data. Shadow PC, a provider of high-end cloud computing services, is warning customers of a data breach that has compromised and exposed customers’ private information. This came out as a cybercriminal claims to be selling the stolen data of 533,624 Shadow customers. According to multiple tips sent to BleepingComputer, the company has begun to send data breach notifications to their customers after a successful social engineering attack which targeted one of their employees. This attack began on the Discord platform with the downloading of malware under cover of a game on the Steam platform, which was proposed by an acquaintance of the employee. The compromised customer’s information includes full name, email address, birth date, billing address and credit card expiry date. However, Shadow did clarify that no passwords or sensitive banking data were compromised. Shadow stated they had revoked the stolen authentication cookie, and that the hacker’s access to their systems has been blocked. They have also implemented additional defences to prevent similar incidents from occurring in the future. Philippine Statistics Authority says alleged data breach limited to one system. The Philippine Statistic Authority (PSA) said on Wednesday that the alleged data breach is limited to their Community-Based Monitoring System (CBMS). They are currently assessing what personal data from the CBMS has been compromised. They stated that they will share information with the relevant authorities and the public in “due course”.The PSA has also activated their Data Breach Response Team (DBRT) following the alleged data leak posted on social media. The PSA reassured that the Philippine Identification System and the Civil Registration System are not affected. The Department of Information and Communications Technology (DICT) confirmed that they are now looking at possible suspects behind this data breach. This data breach comes after the PhilHealth data breach which may have impacted millions of members. Last month, over 17,000 WordPress sites were hacked in Balada Injector campaigns. Multiple Balada Injector campaigns have compromised and infected over 17,000 WordPress sites via leveraging known flaws in premium theme plugins to inject a Linux backdoor. This backdoor redirects visitors of the compromised sites to fake tech support pages, fraudulent lottery wins, and push notification scams. It was found that more than half (9,000) were compromised via the exploitation of CVE-2023-3169, which is a cross-site scripting flaw in tagDIV Composer - a companion tool for tagDIV’s Newspaper and Newsmag themes for WordPress sites. It is highly recommended to upgrade the tagDIV Composer plugin to version 4.2. Or later as they address the mentioned vulnerability. 23andMe faces multiple class action lawsuits after hackers leaked stolen genetic data. 23andMe, a genetic testing provider, faces multiple class action lawsuits in the U.S. due to a large-scale data breach that is believed to impact millions of their customers. At least 4 class action complaints have been submitted in California that are seeking relief for the damage done by 23andMe’s failure to protect their data. The lawsuits highlight the lack of information in the official statement of the breach such as the current status of customer data safety, the breach duration, the exact mechanism of the cyberattack. They also criticise the lack of adequate security measures implemented. Especially so for a company that manages sensitive medical data. One of the complaints defines the nominal damages to $1,000 and punitive damages to $3,000 per class action lawsuit member. Unpatched WS_FTP servers are now targeted in ransomware attacks. Unpatched internet-exposed WS_FTP servers against a maximum severity vulnerability are being targeted in ransomware attacks. Sophos X-Ops incident responders have detected ransomware actors abusing the recently reported vulnerability in WS_FTP Server software, via attempts to deploy ransomware through the unpatched services. Even though Progress Software released a patch for this vulnerability in September 2023, not all of the servers have been patched. It is highly recommended for admins to upgrade to the latest version (8.8.2) as this will help to remediate the issue. That is all! Enjoy the rest of the week and don't forget to update your devices and systems to the latest patches!
Back to Blog
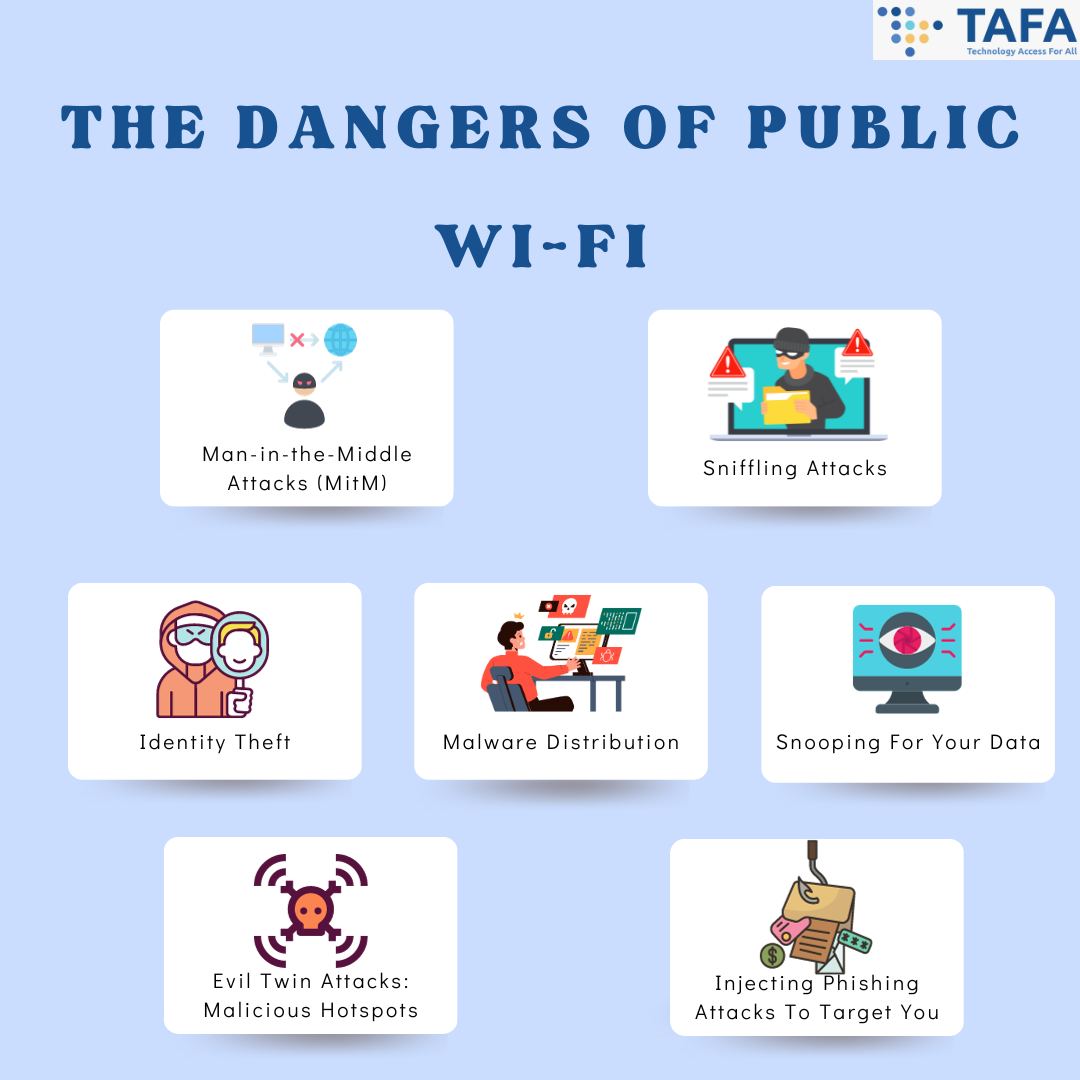
In today's hyper-connected world, public Wi-Fi has become an essential aspect of our daily lives. They are nearly everywhere - whether at a coffee shop, airport, or shopping mall, it's easy to connect to the internet without using our cellular data. However, beneath the convenience lies a shadowy realm of risks, and could leave you vulnerable to cyberattacks. Let’s embark on a journey to unmask the real dangers of public Wi-Fi and how to stay safe on public Wi-Fi when it is necessary. Why Is Public Wi-Fi Not Safe To Use? Public Wi-Fi networks often lack a security measure - encryption, which encrypts your information sent from your device or computer to the router so strangers cannot read it. Without encryption, your information (e.g. identity information, banking, social media accounts and passwords) that is sent over these networks can be intercepted by cybercriminals, they can spy on you, and even take over your online accounts. Did you know? That 43% of respondents had their online security compromised while using public Wi-Fi? This includes either their information being compromised or had malicious software unknowingly installed by the cybercriminals. Furthermore, the majority of respondents had their online security compromised on airport (23%) and cafe/restaurant public Wi-Fi (25%). The Dangers of Public Wi-Fi 1. Man-in-the-Middle Attacks (MitM) This is one of the most common threats in Public Wi-Fi. Essentially, a MitM attack is a form of eavesdropping, whereby bad actors break into a network and “read” the data that is transmitted between the connected devices and the Wi-Fi router. What does this mean? This means that what you thought is private, is no longer private. They can “read” your passwords as soon as you enter into any of your online accounts. 2. Sniffling Attacks Public Wi-Fi networks are a goldmine for hackers who can intercept and analyse unencrypted data packets, which are data units that are sent across unsecured Wi-Fi. This can potentially reveal your sensitive information as they can unpack the data to extract your login credentials or financial information. 3. Identity Theft One of the greatest risks of using public Wi-Fi is getting your identity stolen. Cybercriminals can easily retrieve your information via public Wi-Fi to create targeted cyberattacks and phishing attacks, or enter into your online accounts. What can cybercriminals do via public Wi-Fi? They can:
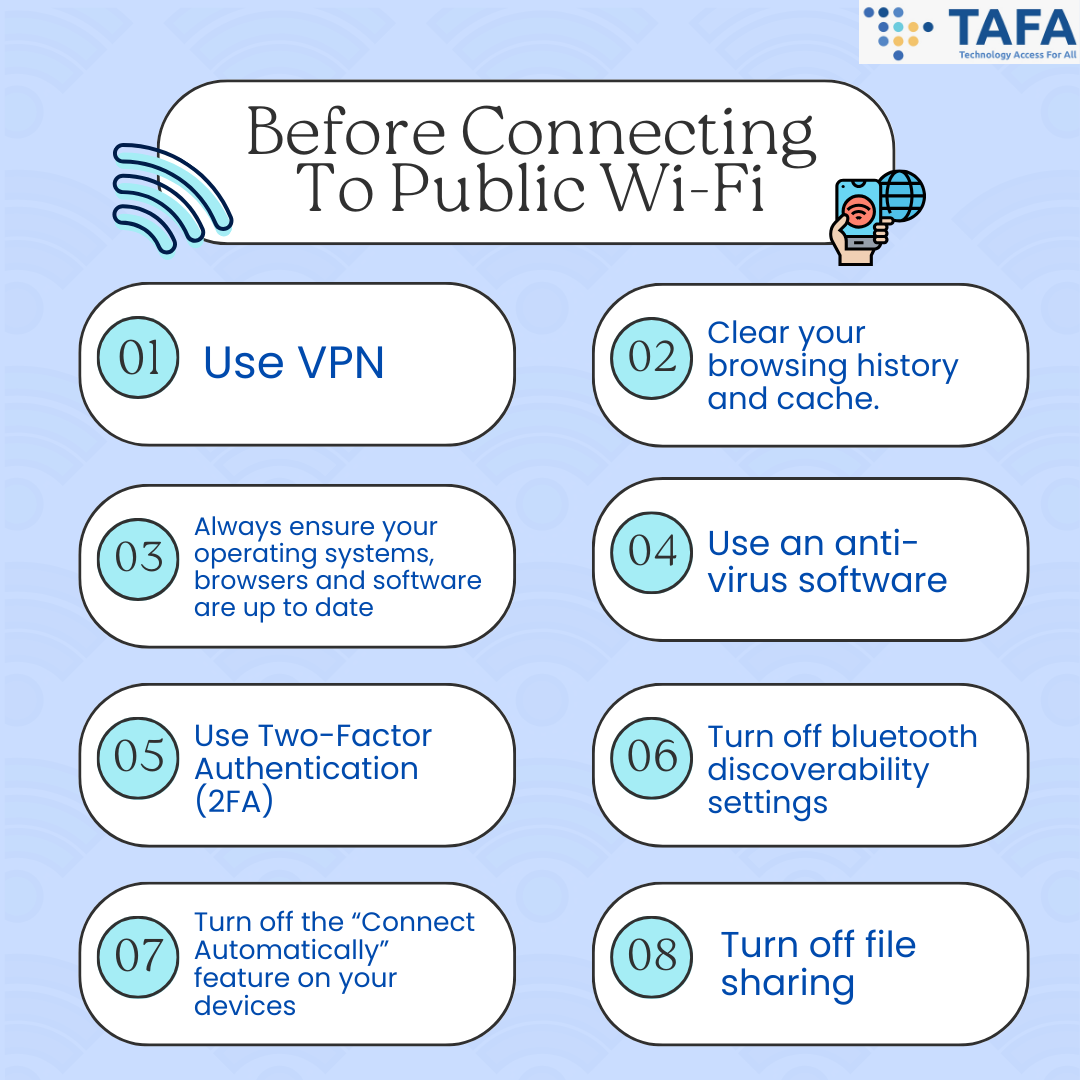
4. Malware Distribution Using public Wi-Fi without any protection (such as VPN) makes it easy for cybercriminals to infect your device with malware, a malicious software without your knowledge. What can also happen is that malicious websites can automatically download malware to your devices that are connected to the public Wi-Fi, compromising your security. 5. Snooping For Your Data Public Wi-Fi networks are very vulnerable to cybercriminals looking for sensitive documents such as 2FA codes, your banking passwords and account, and confidential documents. 6. Evil Twin Attacks: Malicious Hotspots Hackers set up fake malicious hotspots with similar names to reputable ones or ones that look trustworthy such as Cafe Free Wi-Fi. This tricks users into connecting and exposing your data. Once you connect to these malicious hotspots, they can easily intercept your data. Hackers can then harvest the personal and financial data from devices connected to these malicious hotspots. 7. Inject Phishing Attacks To Target You Attackers can intercept network traffic and bombard users with phishing attacks in the form of phishing emails, voicemails, text messages. Attackers can also prompt users to enter login credentials, which are then stolen for malicious purposes. How Do We Stay Safe On Public Wi-Fi? Ideally, if we want to stay completely safe, the best thing to do is NOT connect to public Wi-Fi. However, there are instances whereby we have no choice but to use public Wi-Fi, so here are some ways in which you can do to ensure that your data and accounts stay secure and safe: Before Connecting To Public Wi-Fi
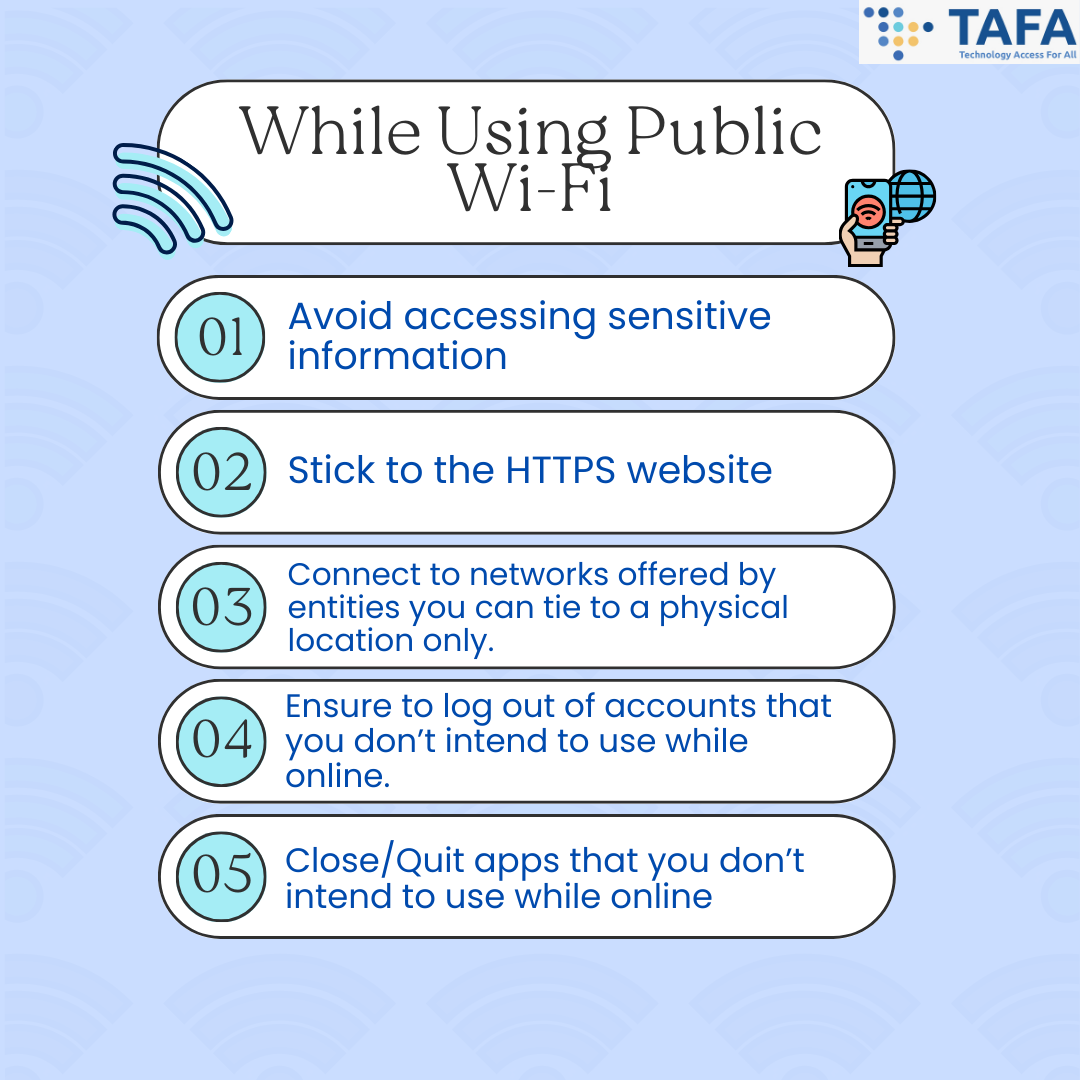
While Using Public Wi-Fi
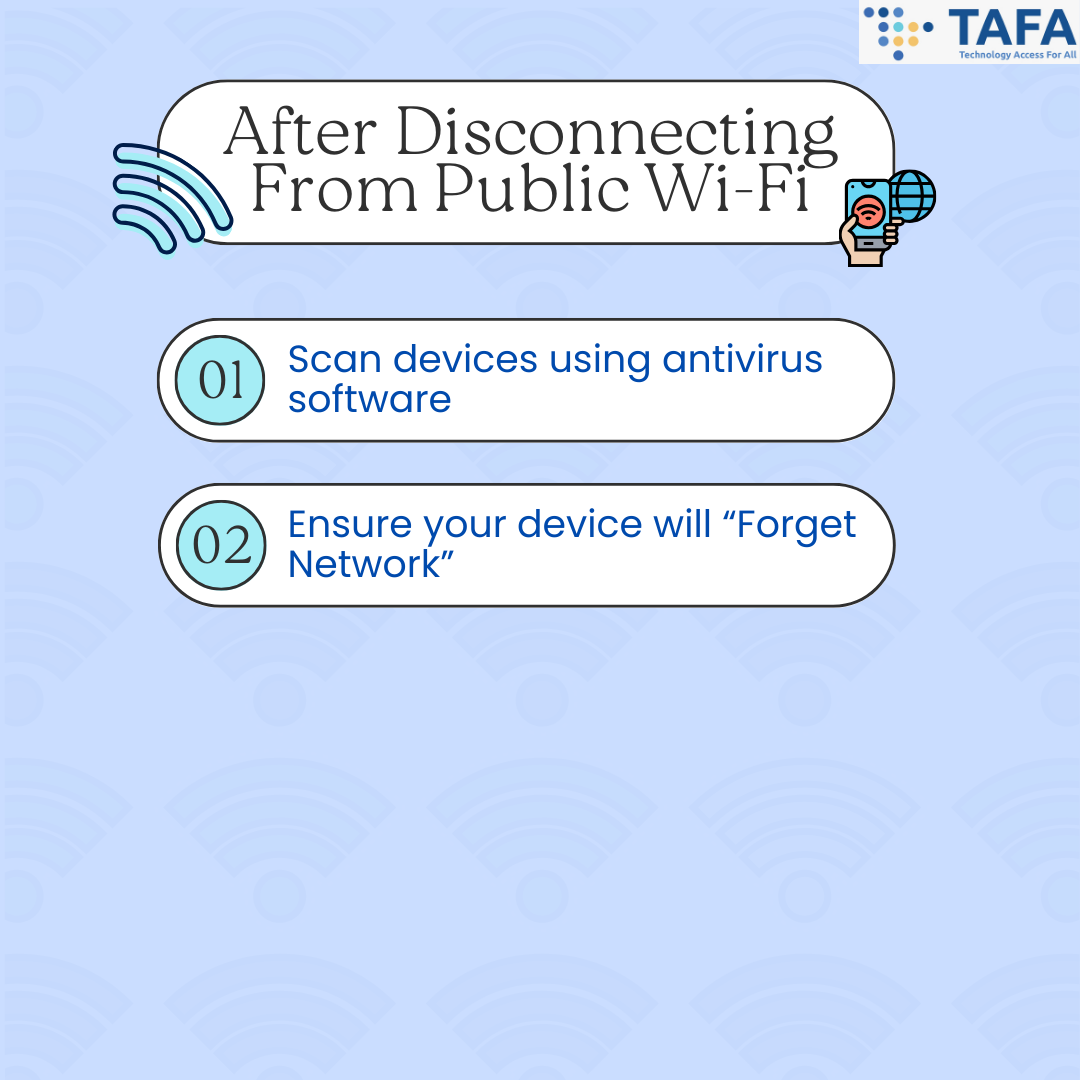
After Disconnecting From Public Wi-Fi
Conclusion While the convenience of public Wi-Fi is alluring, it's crucial to recognize the risks that come with it. By understanding the hidden dangers and implementing prudent cybersecurity measures, you can navigate the digital landscape securely. Remember, awareness is your strongest armour against the unseen threats that lurk in the shadows of free internet. Stay informed, stay vigilant, and safeguard your online journey. Related Topics A Personal Cybersecurity Checklist - How Cyber Secure Are You? Is This QR Code Safe? Top Tips to Ensure Your QR Scans are Secure Unmasking Phishing: Your Guide to Spotting The Signs of Phishing
Back to Blog
In the modern digital era, QR codes have become ubiquitous, seamlessly integrating into our lives. QR codes have become even more widely used, especially after the pandemic. QR codes are the latest form of digital technology that has become common. Yet, amid the convenience they offer, lies a lurking threat--malicious QR codes. Not all QR codes are safe! Just as a seasoned explorer navigates a maze, detecting safe QR codes requires vigilance and a keen eye. In this article, we will explain the different types of QR codes scam and give you tips on how to check if a QR code is safe or fraudulent. Types of QR Codes Scam The types of QR Code scams includes:
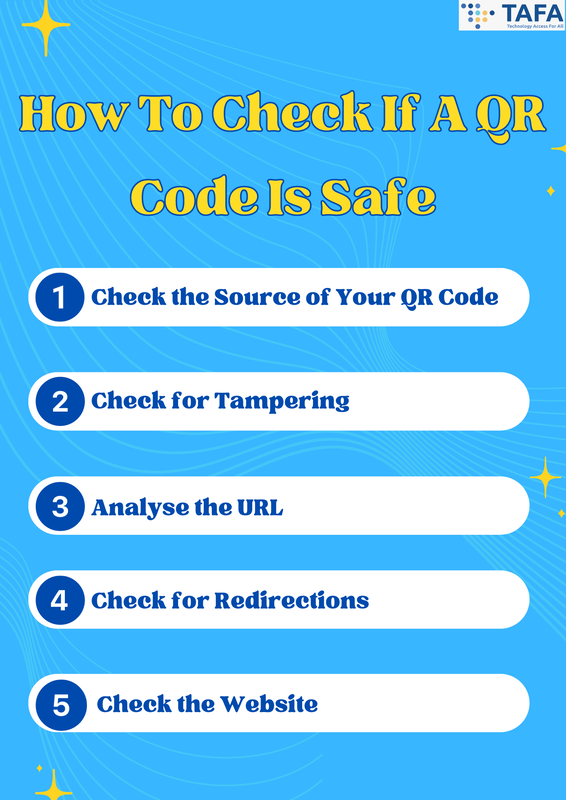
How to Check if a QR Code is Safe 1. Check the Source of Your QR Code
2. Check for Tampering
3. Analyse the URL
4. Check for Redirections
5. Check the Website
What Do I Do If I Scan A Scam QR Code? Presently, making QR codes are super easy, hence there is a huge variety and abundance of QR scams out there. And sometimes, there is almost no way to differentiate between a scam QR code and a real one till you open the link. If you have entered sensitive information:
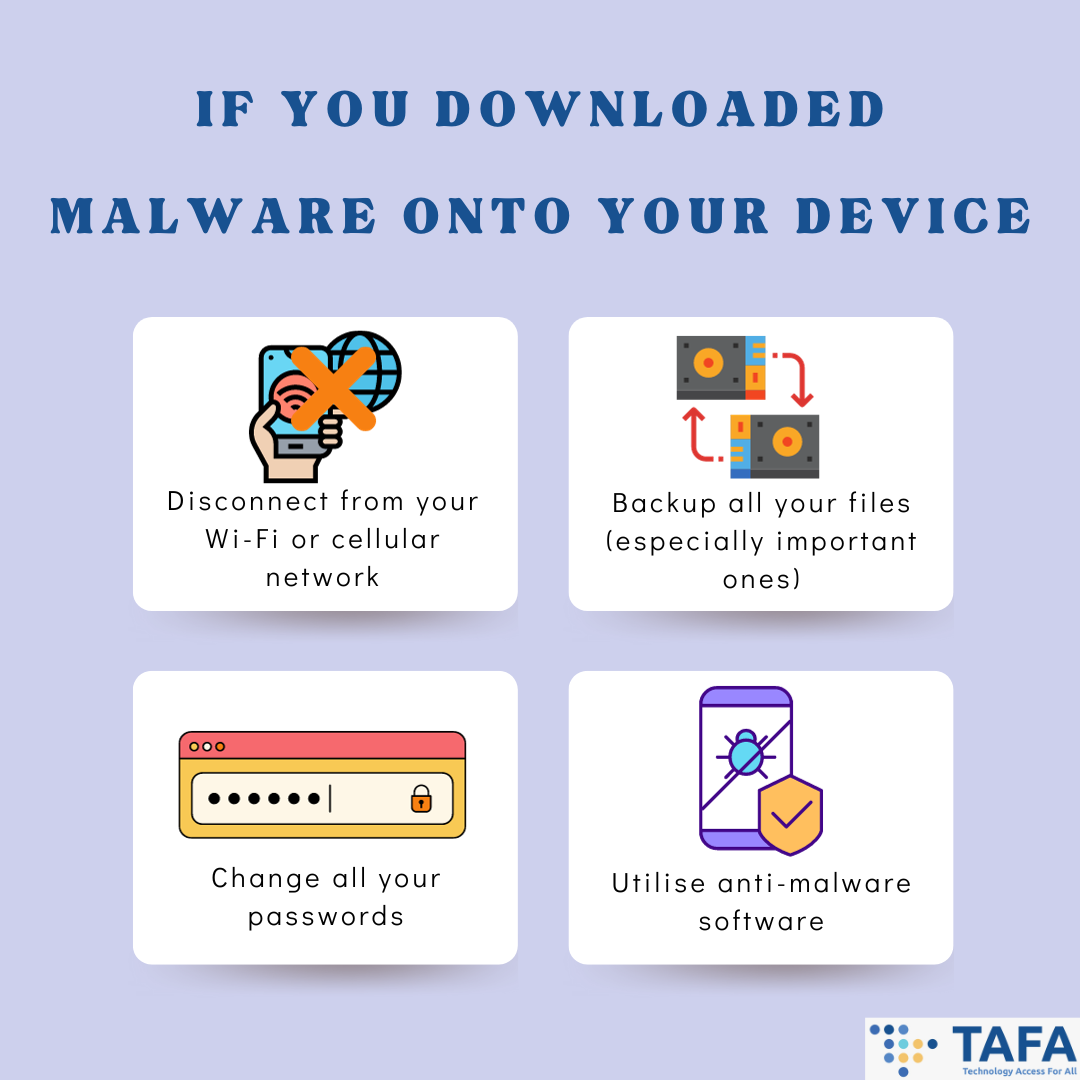
If you have downloaded malware onto your device via scanning QR code:
In the realm of QR codes, safety is the ultimate treasure, and with the right tools and knowledge, you can unlock it. Always scrutinise and look out for any signs of a scam QR code to ensure you can navigate through this digital landscape safely and securely. Vigilance is Key! Related Topics A Personal Cybersecurity Checklist - How Cyber Secure Are You? Unmasking Phishing: Your Guide to Spotting The Signs of Phishing
Back to Blog
Last week, more data breaches and cyberattack occurred across several industries. Devastating impacts of cyberattacks have also been reported- from MGM Resorts reporting a loss of $100 million due to the September attack to PhilHealth being fully investigated by Philippines' authorities, which are recommending legal prosecution to the fullest extent allowed by law. Furthermore, new malware-as-a-service, phishing campaigns, vulnerabilities and patches have also been found and released. It is highly recommended to not only be aware of them but to also update them when possible.
Read on to receive a quick summary of what happened this week in the space of cybersecurity. Sony confirms data breach that affected 6,800 current and former employees. Sony is sending out notices to affected current and former Sony Interactive Entertainment (SIE) employees that their personal information has been compromised in a system breach that occurred in May. It was reported that the letters went out to about 6,800 affected employees. Sony disclosed in the letter that the breach was due to the exploitation of the zero-day vulnerability in the MOVEit Transfer platform. In the letter, Sony admitted that the data breach occurred on 28 May, 3 days before Sony was informed about the MOVEit breach. They also detected another breach on 2 June, whereby they detected unauthorised downloads. In response, they immediately took the platform offline, and remediated the vulnerability. Sony has also informed the affected employees that they are given Equifax credit monitoring and identity restoration services. Late last month, following allegations on hacking forums that Sony has been breached again, and 3.14GB of data has been stolen, Sony responded that they are investigating these recent claims. They told BleepingComputer that they “have identified activity on a single server located in Japan used for internal testing for the Entertainment, Technology and Services (ET&S) business. They took the server offline while investigations are ongoing, and so far they found no indications that their customers’ or business partners’ data were affected by this breach. NPC: More than 730GB of PhilHealth leaked which includes sensitive personal information. The National Privacy Commission (NPC) launched further investigation into the ransomware attack and data breach on the state health insurer, the Philippine Health Insurance Corp (PhilHealth).In a statement, the NPC stated that they had completed its initial analysis of 650GB worth of compressed files originating from the data dump claimed by Medusa, a ransomware group that admitted hacking into PhilHealth computers, and held the stolen information on a US$300,000 ransom. These data surfaced online on the dark web after the government did not meet their ransom demands. Upon extraction, the files revealed 734 GB worth of data, which includes sensitive personal information. Department of Information & Communications Technology undersecretary, Jeffrey Dy, observed copies of employees’ payroll, and details such as regional offices, memos, directives, working files and hospital bills. In terms of personal information, IDs and pictures were found. Although, a full inventory of the number of compromised personal information will take some time due to the sheer volume. Due to the findings, the NPC “has launched a sua sponte investigation to determine the full scope of the breach, identify the responsible officials, and recommend legal prosecution to the fullest extent permissible by law”. The NPC also initiated an immediate proactive investigation into PhilHealth’s potential violations of the Data Privacy Act of 2012. The NPC has noted that PhilHealth have “implicitly acknowledged a degree of negligence on their part”, as an official admitted that the antivirus software PhilHealth was using was expired. The NPC also issued a public warning to those who try to access or download the leaked data as they will be held accountable and may face criminal charges. 23andMe, a genetics firm, suffered a credential stuffing attack: Confirms user data was stolen. 23andMe confirmed that they are aware of their users’ data circulating on hacker forums, and stated that this leak was due to a credential stuffing attack. The 23andMe spokesperson stated that the threat actors used exposed credentials from other breachers to access 23andME accounts and stole the sensitive data. A threat actor has leaked samples of data that was allegedly stolen from 23andMe, and offered to sell these data packs. The threat actor has offered to sell data profiles in bulk for $1-$10 per 23andMe account, depending on how many one purchased. The compromised information includes full names, usernames, profile photos, sex, birthdates, genetic ancestry results, and geographical location. It was found that the compromised accounts had opted in the ‘DNA Relatives’ feature, which allows users to find genetic relatives and connect with them. Users of 23andMe are encouraged to enable 2-factor authentication on the platform, and refrain from re-using passwords. Motel One Group disclosed data breach - payment card details accessed. Motel One, a low-budget hotel chain, suffered a ransomware attack and a subsequent data breach. Data exposed includes customers’ address data and 150 credit card details. The hotel chain also stated they had notified all customers impacted by the data breach, and notified relevant authorities. They also started an investigation into this breach. ALPHV (also known as BlackCat), a ransomware gang, claimed responsibility for the attack, and claimed they stole 5.5 terabytes of data, this includes nearly 24.5 million files. According to them, the stolen data includes “PDF and RTF booking confirmations for the past 3 years containing names, addresses, reservation dates, payment method and contact information”, as well as “customers’ credit card data and internal company documents.” European Telecommunications Standards Institute disclosed data breach: A database containing their online users stolen. The European Telecommunications Standards Institute (ETSI), a not-for-profit organisation that supports the development and testing of technical standards in the information and communication fields, has disclosed a data breach following a cyberattack on their member’s portal. ETSI has over 900 member organisations from 65 countries. ETSI announced that the cybercriminals had breached the “IT system dedicated to its members’ work”, stealing the list of their online members. ETSI believes that the users database has been exfiltrated. ETSI has fixed the vulnerability, and strengthened their IT security procedures. The organisation has also encouraged all online users to reset their passwords as a precautionary measure. D.C. Board of Elections confirms data breach: Voter information stolen. The District of Columbia Board of Elections (DCBOE) announced on Friday that hackers were able to access thousands of D.C. residents’ voter records in a data breach. In a release, DCBOE stated they were aware that RansomVC, a hacking group, allegedly got access to 600,000 lines of U.S. voter data on Thursday. The threat actor claims that stolen data includes but is not limited to the names, registration ID, voter ID, partial social security number, driver’s licence number, birth date, phone number, email. The board said it discovered a breach through their website and its hosting provider DataNet, and has since taken down its website as a precautionary measure. Notably, the breach did not involve a direct compromise of DCBOE’s servers and internal systems. D.C. Board of Elections confirms data breach: Voter information stolen. The District of Columbia Board of Elections (DCBOE) announced on Friday that hackers were able to access thousands of D.C. residents’ voter records in a data breach. In a release, DCBOE stated they were aware that RansomVC, a hacking group, allegedly got access to 600,000 lines of U.S. voter data on Thursday. The threat actor claims that stolen data includes but is not limited to the names, registration ID, voter ID, partial social security number, driver’s licence number, birth date, phone number, email. The board said it discovered a breach through their website and its hosting provider DataNet, and has since taken down its website as a precautionary measure. Notably, the breach did not involve a direct compromise of DCBOE’s servers and internal systems. MGM Resort reveals last month ransomware attack led to $100 million data loss. MGM Resorts reveals that September’s ransomware attack cost them approximately $100 million. In addition to losing $100 million in earnings, MGM also suffered approximately a little less than $10 million in expenses for risk remediation, legal fees, third-party advisory, and incident response measures. However, MGM Resorts did say they expect the latter costs to be covered by its cybersecurity insurance. MGM emphasises that this financial impact will be predominantly confined to Q3 2023, and does not expect a negative impact on their annual financial performance. Lyca Mobile investigates for data breach after cyberattack causes network disruption. Lyca Mobile disclosed that a cyberattack has caused an unexpected disruption on their network, and that the cybercriminals may have also compromised their customer’s data. The attack caused service provision interruptions in all but 4 countries. Customers and retailers reported that they were unable to access the company’s top-up portal. According to the press release, national and international calling services have also been affected. Lyca Mobile has launched an investigation to determine the impact of the cyberattack. The company also emphasised that all of their records are fully encrypted, which indicates that the firm suspects or has verified unauthorised access to their databases. Lyca Mobile says restoration efforts are underway, however certain operational services remained unavailable in some impacted markets. Hundreds of malicious info-stealing Python packages found stealing sensitive data. Researchers observed a malicious campaign that has been planting hundreds of info-stealing packages on open-source platforms that has counted to about 75,000 downloads. Researchers discovered 272 packages with code for stealing sensitive data from targeted systems. Package authors have been implementing more sophisticated layers and detection evading techniques, making the attack evolve more significantly since it was first discovered. Once the packages launch, it targets information such as: (1) running antivirus tools; (2) task lists, Wi-Fi passwords and system information; (3) credentials, browsing history, cookies and payment information stored on web browsers; (4) cryptocurrency wallet apps’ data; (5) discord badges, phone numbers, email addresses, and nitro status; (6) Minecraft and Roblox user data. The malware can also take screenshots and steal individual files from the compromised system such as Desktop, Pictures, Documents, Music, Videos and Downloads directories. It has also been reported that the malware also engages in app data manipulation. A list of the malicious packages can be found here. Researchers warn that about 100,000 industrial control systems are exposed online. It has been found that about 100,000 industrial control systems (ICS), which includes power grids, traffic light systems, security and water systems, were found on the public web. This exposed them to attackers who are finding vulnerabilities, and are at risk of unauthorised access. Exposed ICS also include units for critical infrastructure systems (such as sensors, actuators, switches, building management systems, and automatic tank gauges). BitSight, a cybersecurity company, alerted to the threat after identifying this issue in multiple sectors, impacting many Fortune 1000 companies in 96 countries. Phishing campaign targets Microsoft 365 accounts by abusing open redirects from indeed.com. A phishing campaign has been found to be targeting Microsoft 365 accounts of key executives in U.S. based organisations by abusing open redirects from Indeed.com, a job listing website. The threat actor uses EvilProxy, a phishing service, that can bypass multi-factor authentication (MFA) mechanisms. The targets of this phishing campaign are executives and high-ranking employees from various industries - electronic manufacturing, banking and finance, real estate, insurance and property management. Open redirects allow redirection to arbitrary locations which threat actors use to direct to a phishing page. As the link comes from a trustworthy party, it can bypass email security measures or be promoted on search engines without any suspicion raised. The targets receive emails with an indeed.com link that looks legitimate. However, when clicked, the URL will take the target to a phishing site that looks like the Microsoft authentic login page. When the user accesses their account via this server, the threat actor can capture the authentication cookies, which then allow them full access to the victim’s account. New feature-rich malware-as-a-service, named BunnyLoader emerges. Researchers found a new malware-as-service (MaaS) called BunnyLoader, which has been advertised on various hacker forums as a fileless loader that can steal and replace system clipboard contents. The malware has been developing rapidly, with updates adding new features and bug fixes. Their developers have been adding new functions such as multiple anti-detection mechanisms, and more info-stealing capabilities. Currently it can download and execute payloads, log keys, steal sensitive data and cryptocurrency, and execute remote commands. Zscaler researchers note that BunnyLoader has been gaining popularity among cybercriminals as a low-price, feature-rich malware. Atlassian released emergency security updates to patch critical zero-day vulnerability exploited in attacks. Atlassian, an Australian software company, released emergency security updates to fix a maximum severity zero-day vulnerability (tracked as CVE-2023-22515) in their Confluence Data Center and Server software. This vulnerability has been exploited in attacks. Atlassian Cloud sites are not affected by this vulnerability. Customers using the vulnerable versions are highly encouraged to immediately update to one of the fixed versions (i.e. 8.3.3. or later, 8.4.3 or later, 8.5.2 or later). Atlassian also urges customers that aren’t able to immediately update to shut down impacted instances or isolate them from Internet access. The company also recommends admins to check all Confluences instances for indicators of compromise. Indicators of compromise can be found here. Android released October security updates addressing zero-days flaws exploited in attacks. Google has released the October security updates for Android which addresses 54 unique vulnerabilities – including 2 that are known to be actively exploited (tracked as CVE-2023-4863 and CVE-2023-4211). Of the 54 fixes concerning Android 11-13, 5 are rated critical, and 2 concern remote code execution problems. Users of older Android systems are recommended to either upgrade to a newer model (as versions 10 or older are no longer supported) or use a 3rd party Android distribution that offers security updates for their models. Apple released new emergency security updates to patch new zero-days used to hack iPhones. Apple released new emergency security updates on Wednesday to patch 2 new zero-day vulnerabilities that are being actively exploited against versions of iOS before iOS 16.6. CVE-2023-42824 enables attackers to escalate privileges on unpatched iPhones and iPads. The list of impacted devices is quite extensive, and it includes iPhone XS and later, iPad Pro 12.9-inch 2nd generation and later, iPad Pro 10.5-inch, iPad Pro 11-inch 1st generation and later, iPad Air 3rd generation and later, iPad 6th generation and later, and iPad mini 5th generation and later. Apple also addressed CVE-2023-5217 which could allow arbitrary code execution (which means attackers can run any commands or code) after successful exploitation. Microsoft released emergency security updates for Edge, Teams and Skype to patch zero-days in open-source libraries. Microsoft released emergency security updates for Edge, Teams and Skype to patch 2 zero-day vulnerabilities in open-source libraries used in these 3 products. Both of which (CVE-2023-4683 and CVE-2023-5217) lead to crashes or allow arbitrary code execution after successful exploitation. The two security flaws only affect a limited number of Microsoft products, with the company patching Microsoft Edge, Microsoft Teams for Desktop, Skype for Desktop, and Webp Image Extensions against CVE-2023-4863 and Microsoft Edge against CVE-2023-5217. The Microsoft Store will automatically update all affected Webp Image Extensions users. However, the security update will not be installed if Microsoft Store automatic updates are disabled. That is all! Enjoy the rest of the week and don't forget to update your devices and systems to the latest patches!
Back to Blog
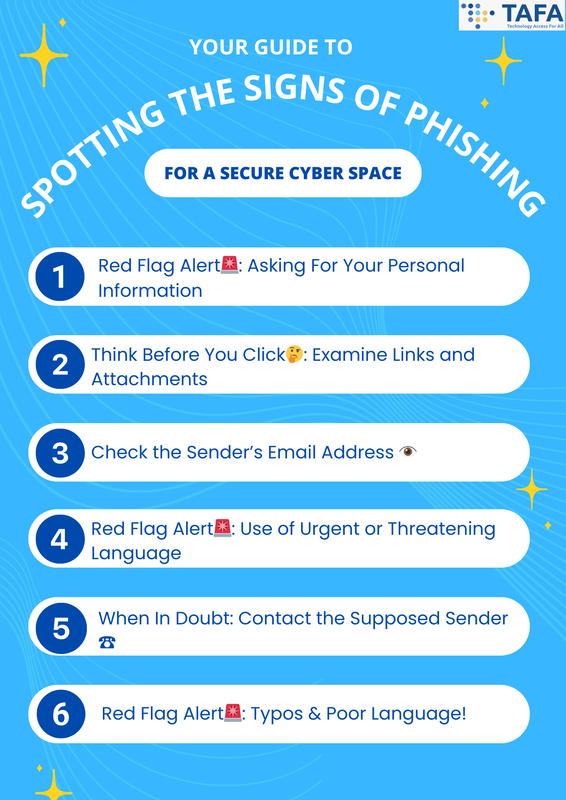
In today's interconnected world, every click and every link could potentially lead to unforeseen dangers. Phishing, a form of cyber threat, lurks beneath the surface, waiting to lure unsuspecting victims into its net of deceit. Through phishing, cybercriminals can obtain your personal and financial information such as your bank account numbers, credit card numbers and login details. Even worse, utilising your personal information, cybercriminals could gain access to your online accounts, and impersonate you to scam the people around you. Therefore recognizing the signs of phishing is essential for a safe online environment. Below we present a guide on spotting the signs of phishing and securing your online environment. How To Spot The Signs Of Phishing 1. Red Flag Alert🚨: Asking For Your Personal Information
2. Think Before You Click🤔: Examine Links and Attachments
3. Check the Sender’s Email Address 👁️
4. Red Flag Alert🚨: Use of Urgent or Threatening Language
5. When In Doubt: Contact the Supposed Sender ☎️
6. Red Flag Alert🚨: Typos & Poor Language!
Conclusion The internet is a vast landscape with both perilous threats and incredible opportunities. It is crucial to remember that dangers, like phishing, often lurk in the digital landscape. By honing your skills to recognize the signs of phishing, you arm yourself with the tools needed to steer through this space safely. Stay informed, stay vigilant, and let your knowledge guide you safely to have a secure cyberspace. Related Topics A Personal Cybersecurity Checklist - How Cyber Secure Are You?
Back to Blog
It’s October! This means it’s Cybersecurity Awareness Month! In an age where our lives are increasingly intertwined with the digital realm, ensuring our cybersecurity is paramount. A personal cybersecurity checklist can be your armour, defending against cyber threats and providing you with peace of mind. Personal Cybersecurity Checklist 1. Create Secure Passwords: The First Line of Defense
A strong unique password is now more essential than ever before:
2. Two-Factor Authentication (2FA): Adding an Extra Layer of Security
3. Regular Software Updates: Keeping the Gate Locked
4. Ensure website URL starts with HTTPS://
5. Phishing Awareness: Spotting the Hooks
6. Regular Data Backups: A Safety Net for Your Data
7. Be Careful on Social Media: Guarding Your Digital Persona Social media is a great way to connect and share information. However, do beware of what you share online. Cybercriminals can gain a lot of information from you from these social media platforms, and they will use this information for phishing attacks and identity theft.
8. Use Your Mobile Device Securely: Locking Down Your Digital Pocket
9. Don’t Use Public Wi-Fi: Safeguarding Your Online Journey
10. Review Your Credit Accounts Regularly: Keeping a Watchful Eye
🗒️By following this personal cybersecurity checklist, you're well on your way to fortifying your digital presence. The internet is a vast landscape with both perilous threats and incredible opportunities. Empower yourself with knowledge, awareness, and proactive measures to navigate this space safely. Your cyber fortress awaits - fortify it and ensure your online experiences are secure, seamless, and rewarding. . |
|
© 2021, TAFA HOLDINGS (S) PTE LTD. ALL RIGHTS RESERVED
|

 RSS Feed
RSS Feed