AuthorTAFA Archives
April 2024
Categories
All
|
Back to Blog
Weekly Cyber News Update: 6 May - 12 May13/5/2024 Last week, breaches and cyberattacks occurred across several industries from the public, technology, watch, physical security to the healthcare sector. Devastating consequences have been uncovered from earlier data breaches and attacks, such as the University System of Georgia determined that the 2023 Clop Moveit breach led to 800,000 individuals’ data stolen, and that the Ohio Lottery ransomware attack has led to over 500,000 individuals’ data compromised. Additionally, a massive webshop fraud ring has stolen credit card information from over 850,000 people. Furthermore, new vulnerabilities and patches for Citrix have also been found and released. It is highly recommended to not only be aware of them but to also update them as soon as possible. Read on to receive a quick summary of what happened this week in the space of cybersecurity. Dell data breach: 49 million customers’ personal data exposed. Dell disclosed via emails to their customers of a data breach that potentially exposed the personal information of approximately 49 million customers. The emails come after a threat actor, Menelik, claimed the breach on BreachForums and offered to sell the stolen data of 49 million customers and other information systems purchased from Dell between 2017-2024. In the email, Dell stated that an investigation is underway. The personal information stolen is believed to include customers’ name, physical address, and purchase order details. Menelik listed the stolen data which included customers’ full name, address, city, province, postal code, warranty plan, company name, Dell order number, Dell customer number, system shipped data, and unique 7-digit service tag of the system. However, the stolen information did not include any highly sensitive information such as financial information, email address and telephone number. Furthemore, the threat actor disclosed that the stolen database also contains entries from enterprise clients, partners, educational institutions, and other entries. It was also said that the top 5 countries with systems in the leaked database are the US, China, India, Australia and Canada. An investigation is currently underway, and have notified the relevant law enforcement. City of Witchia suffers a ransomware attack and is forced to shut down their IT network. The City of Wichita, Kansas, disclosed that they were forced to shut down some of their network after suffering a weekend ransomware attack. The City confirmed that they suffered an attack on 5 May 2024, whereby their IT systems were encrypted with ransomware. At this time, it’s unknown whether data has been stolen. As of now, Wichita continues to face disruption, with the latest status update saying the following services remain unavailable: autopayments for water bills, public Wi-Fi at certain locations, the Library’s online catalog, databases and some digital services, email communications for Library staff, self-service print release stations and self-check stations at the Library, automated materials handler at the Advanced Learning Library, most incoming phone call capability for the Library, Wi-Fi and phone services at neighborhood resource centers, public services including golf courses, parks, courts, and the water district, require residents to pay in cash or check while online payment platforms are shut down. In addition, some public safety services like the WFD and WPD have resorted to using “pen and paper” reports, and the Wichita Transit buses and landfill services can only accept cash payments. The LockBit ransomware gang has claimed responsibility for the attack as they have added Wichita to their extortion portal. They are threatening to publish all stolen files on the site by 15 May unless the City pays the ransom. Ascension suffers from a major cyberattack: Some of their systems were taken offline. Ascension, a U.S. healthcare provider, suffered a cyberattack that took down multiple essential systems including electronic health records, the MyChart platform for patient communication, and certain medication and test-ordering systems. Ascension disclosed the attack on 8 May, and stated that an investigation into the attack is underway. The provider has temporarily paused non-emergency medical procedures and appointments, and some hospitals are diverting emergency medical services. Patients were advised to bring relevant medical information to appointments due to system limitations. The company stated that investigation is currently underway to determine if any sensitive information was affected, and will notify and support impacted individuals according to all regulatory and legal guidelines. DocGo confirmed they suffered a cyberattack and patient health data were stolen. DocGo, a mobile medical care firm, confirmed that they suffered a cyberattack after threat actors breached their systems and stole patient health data. In a 8-K filing filed with the SEC, DocGo stated that they recently suffered a cyberattack, and are working with 3rd party cybersecurity experts to assist in the investigation. They have also notified relevant authorities. As part of their investigation, it was determined that hackers stole protected health information from a “limited number of healthcare records”. The company stresses that no other business units have been affected, and they have found no evidence of continued unauthorized access. Singapore’s watchdog investigating Citizen Watches data breach: Customers’ personal details stolen. The Personal Data Protection Commission (PDPC) is investigating a data breach that has resulted in the personal data of Citizen Watches customers stolen. In an email sent to impacted customers on 30 April, notified them of the 24 April 2024 breach that the company discovered on 25 April. The company stated that the attacker had stolen personal data from their remote server. The personal information stolen included customers’ name, contact details, email address, password, birth date, country/region, occupation, and income range. Citizen Watches stated that they had taken steps to prevent “any potential harm” to their customers, and had identified the root cause of the breach. MoD data breach: UK armed forces’ personal details compromised. A payroll system used by the UK’s Ministry of Defence has suffered from a data breach, which led to the personal information of an unknown number of current and past serving UK military personnel being compromised. The personal information compromised includes names and bank details. For a very small number of cases, the compromised data includes their personal addresses. The data relates to current and former members of the Royal Navy, Army, and Royal Air Force over a period of several years. As the system was managed by an external contractor, no operational MoD data has been obtained. MoD has taken immediate action and the system has been taken off-line, and investigations are ongoing. British Columbia investigating multiple cyberattacks on government networks. The Government of British Columbia is investigating multiple cyberattacks that have impacted the Canadian province’s government networks. Premier David Eby stated that there is no evidence that the attackers had accessed or stolen sensitive information from the compromised networks. The government is working with the Canadian Centre for Cyber Security and other agencies to determine the extent of the incidents and to implement additional security measures. The government has yet to disclose the number of cyberattacks that impacted their networks and when they were detected. Amberstone Security exposed nearly 1.3 million documents via an unprotected database. Amberstone Security, a UK-based physical security business, exposed 1,274,086 documents due to an unprotected database, according to an infosec researcher. A researcher stated that they stumbled upon data belonging to the company, which included thousands of pictures of its guards and pictures of individuals suspected of offenses including shoplifting. Among the exposed data, which dates back to 2017, was a folder that contained 99,151 snapshots of guards checking in their shifts, either by using a picture of themselves, their ID cards or both. The pictures taken of the ID cards displayed basic information such as their name, headshot, and the card’s expiry data. In some cases, their signature was shown too. In terms of suspected offenders, images of offenders were found seemingly caught in the act via CCTV or photographed by security personnel afterward. Many images clearly depicted the suspects and were captioned with information such as their names, birthdate, and nature of their alleged offense. In some cases, detailed descriptions of how a suspect operates were found. Spreadsheets with information about offenses, how they were committed, and whether violence was used or not were found. It is unclear if the exposed data has been accessed by threat actors. A day after being alerted to the exposed database, the company revoked public access to the database, and an investigation into this incident is underway. Massive webshop fraud ring stole credit card information from over 850,000 people. A massive network of 75,000 fake online shops called ‘BogusBazaar’ has tricked over 850,000 people in the US and Europe into making purchases, allowing criminals to steal their credit card information and attempt to process an estimated $50 million in fake orders. Furthermore, millions of stolen credit card details have been resold on dark web marketplaces. This allows other threat actors to purchase them and perform unauthorised online purchases. According to SRLabs’ report, the BogusBazaar network has attempted to process an estimated $50 million in fake purchases since the operation launched 3 years ago. Most of the victims are concentrated in the US and Western Europe. It is highly recommended for consumers to check the authenticity of an online shop by reading online reviews, checking for contact information, examining the return policy, checking for trust seals, browsing the website content in general, and checking its social media presence. University System of Georgia: Clop MOVEit breach led to the exposure of 800,000 individuals’ data. The University System of Georgia (USG) is sending data breach notifications to 800,000 affected individuals whose data was exposed in the 2023 Clop MOVEit attacks. USG determined that Clop had stolen sensitive files from their systems and began notifying impacted people. The notices were sent between 15 April - 17 April 2024 and it informed affected individuals that the threat actors had accessed their full or partial (last 4 digits) of their social security number, birth date, bank account number(s), and federal income tax documents with Tax ID number. It is presumed that this breach affects current and prior students, academic staff, contractors and other personnel. Also, the entry of the Office of the Maine Attorney General portal lists as well driver’s license number or identification card number as exposed data types, although these were not mentioned in the notice. USG is offering impacted individuals 12 months of identity protection and fraud detection services, and recipients are given until 31 July 2024 to enroll. Ohio Lottery ransomware attack: Over 500,000 individuals’ data compromised. The Ohio Lottery is sending data breach notification letters to 538,959 individuals that were affected by a cyberattack that hit their internal office network on Christmas Eve. The attackers managed to access affected people’s names, social security numbers, and other personal identifiers. The Ohio Lottery stated that no evidence was found that the stolen information had been used for fraud. However, they will provide free credit monitoring and identity theft protection services to all potentially affected individuals. The breach was claimed by the DragonForce ransomware gang, and claimed that they encrypted devices and stole documents that belonged to Ohio Lottery customers and employees. Citrix warns admins to manually mitigate PuTTY SSH client vulnerability. Citrix notified customers to manually mitigate a PuTTY SSH client vulnerability (tracked as CVE-2024-31497) that could allow attackers to steal a XenCenter admin’s private SSH key. This vulnerability impacts multiple versions of XenCenter for Citrix Hypervisor 8.2 CU1 LTSR, which bundle and use PuTTY to make SSH connections to guest VMs when clicking the “Open SSH Console” button. Citrix stated that the PuTTY components have been removed starting with XenCenter 8.2.6 and any versions after 8.2.7 will no longer include it. Those who want to mitigate the vulnerability can download the latest version of PuTTY and install it in place of the version bundled with older XenCenter releases. Those who do not wish to use the “Open SSH Console” functionality can remove the PuTTY component completely. Customers who wish to maintain the existing usage of PuTTY should replace the version installed on their XenCenter system with an updated version (version number of at least 0.81). That is all! Enjoy the rest of the week and don't forget to update your devices and systems to the latest patches!
Back to Blog
Alert/Advisory: Progress Flowmon Critical Vulnerability Allows Remote Unauthenticated Access8/5/2024 A critical vulnerability (tracked as CVE-2024-2389), that has been scored 10 out of 10 in the Common Vulnerability, has been found to affect Progress Flowmon web interfaces. Fortunately, Progress has released security updates to address this vulnerability. This vulnerability when exploited successfully can allow attackers unauthenticated remote access via API to execute arbitrary system commands. Recently, multiple proof-of-concepts exploits have been published for this vulnerability. The affected product versions are: Flowmon v12.x and Flowmon v11.x. But it does not affect versions 10.x and lower. It is highly advised for Firemon customers to immediately upgrade to one of the patched versions - v12.3.5 or 11.1.14, and then to upgrade all Flowmon modules. More information is available here: https://support.kemptechnologies.com/hc/en-us/articles/24878235038733-CVE-2024-2389-Flowmon-critical-security-vulnerability https://www.csa.gov.sg/alerts-advisories/alerts/2024/al-2024-044
Back to Blog
Last week, breaches and cyberattacks occurred across several industries from hospitality, software, aviation, pharmaceutical, to the debt collection industry. Devastating consequences have been uncovered from earlier data breaches and attacks, such as the UnitedHealthcare's CEO stating that the recent data breach may affect a third of US citizens. Additionally, Philadelphia Inquirer revealed that the May 2023 data breach have led to 25,549 individuals' personal and financial information stolen. Furthermore, new vulnerabilities and patches for GitLab and weak DMARC policies have also been found and released. It is highly recommended to not only be aware of them but to also update them as soon as possible. Read on to receive a quick summary of what happened this week in the space of cybersecurity. Panda Restaurants disclose a March data breach: Corporate systems compromised and associates’ personal information stolen. Panda Restaurant Group, the parent company of Panda Express, Panda Inn and Hibachi-San, disclosed a data breach that occurred on 10 March 2024, which compromised some of their corporate systems. However, in-store systems, operations, and guest experience were unaffected. Furthermore, current and former associates’ data were stolen. The exposed information includes victims’ names or other personal identifiers, and their driver’s licence numbers or non-driver identification card numbers. The unauthorised hacker accessed their corporate systems between 7 March - 11 March 2024. As soon as they detected the incident, the company carried out remediation and recovery efforts, and started an investigation with 3rd party cybersecurity experts and law enforcement agencies to find the nature and extent of the breach. Panda has yet to disclose the total number of individuals whose personal information was accessed or stolen in this breach. Dropbox disclose data breach: Signs’, eSignature Service, customers impacted. Dropbox disclosed on 2 May 2024 that a threat actor managed to gain access to the Sign production environment and accessed customer information. The compromised personal information includes customers’ email addresses, usernames, phone numbers, hashed passwords, data on general account settings, and authentication data such as API keys, OAuth tokens and multi-factor authentication. It is noted that even users who only received or signed a document through Sign without creating an account had their names and email addresses compromised. Fortunately, there is no indication that payment information or customers’ files (signed documents and agreements) were accessed. Investigation is currently ongoing, but so far there is no evidence that other Dropbox products were impacted. The company is notifying impacted customers, logging them out of the Sign service, and resetting their passwords. In addition, API keys and OAuth tokens are being rotated. It is also highly advised for customers that use an authenticator app for MFA to reset it, and to change passwords on other online services which use the same password as Sign. Qantas loyalty app data breach: Customers’ able to access strangers’ travel information. Australia’s Qantas Airways stated on 2 May 2024 that they are investigating issues that impacted their frequent flyer application after media reports suggested there was a data breach that allowed users to access other passengers’ travel information - this includes their names, upcoming flights plans, points balance and boarding pass. Some users can see others’ full travel information, and one was able to cancel someone else’s tickets. The airlines apologised for this issue, and stated that this technical disruption was not a cyber security incident. Rather it was caused by a technology issue that may be related to recent system changes. London Drugs closed all stores following a ‘cybersecurity incident’. Canadian pharmacy chain, London Drugs, closed all their stores - over 80 outlets - over the weekend until further notice following a “cybersecurity incident”. A London Drugs spokesperson stated that a “cybersecurity incident” was behind the store closures, and declined to answer specific questions about the incident. Furthermore, their phone lines are temporarily taken down and people should go to their stores for urgent pharmacy needs.The giant stated that they immediately took counter security measures, and has started an investigation with 3rd party cybersecurity experts. As of then, they found no evidence that customer or employee data has been compromised. FBCS, a debt collection agency, warns 1.9 million individuals impacted by a data breach. Financial Business and Consumer Solutions (FBCS), a U.S licensed debt collection agency, is notifying 1,955,385 impacted individuals in the U.S. that the company suffered a data breach after they discovered that unauthorised actors had breached its network since 14 February 2024. The threat actor was able to view or acquire certain information on the FBCS network during the period of access. The compromised data includes customers’ full name, social security number, birth date, account information, and drivers licence number or ID card. It is highly recommended that impacted individuals stay vigilant against unsolicited communications and to monitor their account statements and credit reports for any suspicious activity. Philadelphia Inquirer revealed that May 2023 data breach have led to 25,549 individuals’ personal and financial information stolen. Philadelphia Inquirer revealed that attackers behind the May 2023 data breach have stolen 25,549 individuals’ personal and financial information. The information exposed during the breach includes individuals’ names, and other personal identifiers in combination with financial account numbers or credit/debit card numbers (in combination with security code, access code, password or PIN for the accounts). It is highly recommended that impacted individuals monitor their accounts for identity theft and fraud attempts. All impacted individuals are offered 24 months of free Experian credit monitoring and identity restoration services. UnitedHealthcare’s CEO: Recent data breach may affect a third of US citizens. Change Healthcare’s parent company UnitedHealth Group’s CEO, Andrew Witty, stated during a House hearing that “maybe a third” of US citizens may be affected by the recent data breach which led to personal information being stolen. Witty stated that he was reluctant to give a more precise answer as investigations are still ongoing, and they are trying to figure out exactly how many people were affected. During the hearing, Witty stated it will probably take “several months” before the company can notify victims of the data breach. So far, the company has found no evidence of exfiltration of materials such as doctors’ charts or full medical histories among the data. It was found that hackers used compromised credentials to access a Change Healthcare Citrix portal that was not protected by MFA. Witty confirmed to senators that UnitedHealth did pay $22 million to the ransomware group. CISA: Actively exploited maximum severity GitLab vulnerability allows attackers to take over accounts. CISA warned on 1 May 2024 that attackers are actively exploiting a maximum-severity vulnerability (tracked as CVE-2023-7028) in GitLab that allows them to take over accounts via password resets. This flaw allows remote unauthenticated threat actors to send password reset emails to email accounts under their control to change the password and hijack targeted accounts without user interaction. Although, attackers are unable to exploit this vulnerability for accounts that have 2FA enabled. It is critical to patch systems where accounts are not protected with 2FA. This vulnerability impacts GitLab Community and Enterprise editions, and GitLab fixed it in 17.7.2, 16.5.6, and 16.6.4 and backported patches to versions 16.1.6, 16.2.9, and 16.3.7. Finland: Ongoing Android malware attacks attempting to breach online bank accounts. Finland’s Transport and Communications Agency (Traficom) warns of an ongoing malware attack that is attempting to breach online bank accounts. Multiple cases of attacks include SMS messages instructing users to call a number. The scammer will instruct victims to install a McAfee app for protection, which is malware that allows attackers to breach victim’s bank accounts. These messages are supposedly sent from banks or payment service providers like MobilePay. In one case, a victim lost 95,000 euros as the scammers managed to log into the victim’s banking account and transfer money. Traficom states that the campaign targets only Android devices. If you have installed the malware, immediately contact your bank for protection measures and restore “factory settings” on the infected device to erase all data and apps. NSA & FBI: North Korean hackers are exploiting weak email DMARC policies to mask attacks. The NSA and FBI jointly caution that APT43, a North Korea-linked hacking group, is exploiting weak email Domain-based Message Authentication Reporting and Conformance (DMARC) policies to mask spear phishing attacks. The attackers utilise this weakness to send spoofed emails which seems to come from credible sources such as journalists, academics, and other experts in East Asian affairs. NSA stated that these campaigns are utilised to collect intelligence on geopolitical events, adversary foreign policy strategies, and any information that affects DPRK interests by gaining illicit access to targets’ private documents, research and communications. To mitigate the threat, it is advised for defenders to update their organisation’s DMARC security policy to use “v=DMARC1; p=quarantine;” or “v=DMARC1; p=reject;” configurations. It is also recommended for organisations to set other DMARC policy fields, such as ‘rua’ to receive aggregate reports about the DMARC results for email messages from the organisation’s domain. That is all! Enjoy the rest of the week and don't forget to update your devices and systems to the latest patches!
Back to Blog
The digital age has revolutionised the way we shop, but it has also opened the door to new threats. Europol has notified 443 online shops that they have been infected with credit card stealers in December 2023. This highlights the pervasive nature of cybercrime and the need for heightened vigilance. Join us as we explore the implications of this warning, the tactics used by cybercriminals, and steps businesses can make to protect themselves in an increasingly risky online shopping landscape. On Credit Card Stealers Threat actors have hacked online shops with malicious scripts that steal customers’ debit and credit cards. Skimmers (which are small snippets of JavaScript code) have been added to checkout pages or loaded from remote resources to evade detection. This is a major cybersecurity threat as digital skimming steals credit card information or payment card data from online stores’ customers. As the transaction data is intercepted during the online purchase checkout process, customers tend not to notice anything unusual. How Does Digital Skimming Work? Generally, there are 3 stages in a digital skimming attack:
What do these codes do? They intercept and steal payment card numbers, expiration dates, verification numbers, names and shipping addresses. This personal information will then be uploaded to the attackers’ servers. Consequences of Credit Card Stealers The consequences of the stolen data is that threat actors can use them to perform unauthorised transactions (e.g. online purchases) or resell them to other cybercriminals on the dark web. Unfortunately, these attacks can go undetected for weeks or even several months. Furthermore, cybercriminals can even collect large amounts of payment card details if the breached e-commerce platforms are highly popular. Scale of The Operation This 2 month international operation was coordinated by Europol and spearheaded by Greece, involved law enforcement from 17 countries and private entities such as Group-IB and Sansec. Tips for Business To Protect Themselves
What To Do If You Become A Victim?
Conclusion Europol's warning serves as a stark reminder of the ever-present threat of cybercrime in the digital age. By staying informed, exercising caution, and following best practices for online security, consumers can protect themselves from falling victim to credit card stealers and other malicious threats. Together, let us work towards a safer online shopping experience for all. Related Topics 26 Billion Records Compromised in Huge Data Leak - dubbed as “Mother of All Breaches”. 12.8 million authentication and sensitive secrets leaked on GitHub in 2023 Apple's Alarming Report: 2.6 Billion User Records Exposed By Data Breaches in Past 2 Years 71 Million Emails from Naz.API stolen account list added to Have I Been Pwned.
Back to Blog
The PuTTY project has released a security update to address a critical vulnerability (tracked as CVE-2024-31497) in PuTTY 0.68 through 0.80. This vulnerability could potentially allow attackers to access 60 cryptographic signatures that can be utilised to recover the private key used for their generation. This consequence of this critical vulnerability is that it will allow unauthorised access to SSH servers or sign commits as the developer. This can potentially lead to supply chain attacks on impacted software projects. This vulnerability is caused by how PuTTY generates temporary unique cryptographic numbers for the NIST P-521 curve used for SSH authentication. PuTTY is a popular open-source terminal emulator, serial console, and network file transfer application that supports SSH, Telnet, SCP, and SFTP. The developers have fixed the vulnerability in PuTTY version 0.81. However, it is noted that any P521 private keys generated using the vulnerable version of the tool should be considered unsafe and be replaced by new, secure keys. Listed below are confirmed software that uses the vulnerable PuTTY:
It should be noted that it is likely that there are more software tools impacted by this vulnerability, depending on the PuTTY version incorporated. It is highly advised that users check their tools and take the preventive action needed. More information is available here: https://www.chiark.greenend.org.uk/~sgtatham/putty/wishlist/vuln-p521-bias.html https://www.csa.gov.sg/alerts-advisories/alerts/2024/al-2024-042 https://www.bleepingcomputer.com/news/security/putty-ssh-client-flaw-allows-recovery-of-cryptographic-private-keys/
Back to Blog
Last week, breaches and cyberattacks occurred across several industries from healthcare to the public sector. Devastating consequences have been uncovered from earlier data breaches and attacks, such as UnitedHealth confirming that they paid the ransom to stop their patients’ data from being leaked. Furthermore, new vulnerabilities and patches for WP Automatic WordPress and Progress Flowmon have also been found and released. It is highly recommended to not only be aware of them but to also update them as soon as possible.
Read on to receive a quick summary of what happened this week in the space of cybersecurity. U.S. health conglomerate Kaiser notifies 13.4 million customers of data breach. On Thursday, Kaiser posted a notice in which they will be notifying millions of their members of a data breach that occurred earlier this month. The Kaiser Foundation Health Plan confirmed that 13.4 million current and former residents and patients had their information leaked to 3rd party trackers that were installed on their websites and mobile applications. These 3rd party vendors include Google, Microsoft Bing, and X(Twitter). The leaked data may include IP addresses, names, information that could indicate a member or patient has signed into a Kaiser Permanente account or service, details showing how a member or patient interacted with and navigated through the website and mobile app, and search terms used in the health encyclopaedia. Normally, this information is shared with an extensive network of marketers, advertisers, and data brokers. The organisation has stated that the trackers were discovered and removed following a voluntary internal investigation. Additional security measures have also been implemented to prevent this incident from reoccurring. As of now, Kaiser found no evidence of any member’s or patient’s personal information being misused. DPRK hacking groups breached South Korea’s defence contractors to steal information. The National Police Agency in South Korea issued an urgent warning on 23 April that North Korea hacking groups have breached defence industry entities to steal technology information. North Korean hacking groups - Lazarus, Andariel and Kimsuky have been found to have breached S.Korean defence companies via leveraging vulnerabilities in targets’ or subcontractors’ environments to plant malware to exfiltrate data. It was found that multiple companies had been compromised since late 2022 but were unaware of the breach until authorities informed them. The Korean police recommends both defence companies and their subcontractors to improve their network security segmentation, reset their passwords periodically, set up 2FA on all critical accounts, and block foreign IP addresses. LA County Health Services: Data breach has exposed thousands of patients’ data. The LA County of Health Services disclosed a data breach after approximately 6,085 patients’ personal and health information was exposed in a data breach due to a recent phishing attack that impacted over 2 dozen employees. In the data breach notification, 23 employees had their mailboxes compromised after their credentials were stolen in a February attack. Hence, attackers gained access to patients’ personal and health data that were stored in the employees’ email inboxes. The compromised information includes patients’ full name, birth date, home address, phone number, email address, medical record number, client identification number, dates of service, medical information (e.g. diagnosis/condition, treatment, test results, medications), and/or health plan information. Affected individuals are impacted differently. Upon discovering the breach, the organisation disabled the impacted email accounts and quarantined all suspicious incoming emails. No evidence has been found that the attackers have accessed or misused the exposed personal and health information. However, LA County Health Services do advise all affected patients to contact their healthcare providers to verify the content and accuracy of their medical records. UnitedHealth confirmed it paid the ransom to stop data leak. UnitedHealth Group confirmed on Monday that they have paid the ransom to the ransomware gang to protect patient data from being leaked. This followed the February cyberattack on their subsidiary, Change Healthcare. The company also confirmed that files containing personal information were compromised in the breach. In a statement to CNBC, the company said that they are currently working with law enforcement and multiple cybersecurity firms. The company has launched a call centre that will offer free identity theft protections and credit monitoring for 2 years. However, the call centre will not be able to offer any details about individual data impact due to the ongoing investigation and complexity of the data review. Concerned patients can visit their dedicated website for access to resources. Okta warns of a spike in proxy-driven credential stuffing attacks aimed at online services. Okta has warned of a surge in the frequency and scale of credential stuffing attacks aimed at online services. In an alert published, Okta warned that these attacks were facilitated by the broad availability of residential proxy services, lists of previously stolen credentials and scripting tools. Okta stated that they detected a surge in credential stuffing activity against user accounts from 19 April - 26 April 2024, from likely similar infrastructure. It was found that sometimes a user device has been infected with malware and became enrolled as a botnet, which allows threat actors to conceal their malicious traffic. From their observation, it seems that most of the traffic in these credential stuffing attacks appear to originate from the mobile devices and browsers of everyday users. To mitigate the risks of account takeovers, Okta recommends that organisations enforce users to switch to strong passwords, enable 2FA, deny requests originating from locations where they don't operate, and IP addresses with poor reputation, and add support for passkeys. Critical vulnerability in the WP Automatic Wordpress plugin is being exploited: More than 5.5 million attacks detected. Threat actors have started to exploit a critical severity vulnerability (tracked as CVE-2024-27956) in the WP Automatic plugin for Wordpress to create user accounts with administrative privileges and to plant backdoors for long-term access. This plugin is currently installed on more than 30,000 websites. This vulnerability is an SQL injection issue and it impacts WP Automatic versions before 3.9.2.0. It has been observed that more than 5.5 million attacks were trying to leverage this vulnerability, in which most were recorded on 31 March. It is highly recommended for administrators to update the WP Automatic plugin to version 3.92.1 or later. Maximum severity vulnerability found in Progress Flowmon: Patch available now. A top severity security vulnerability (tracked as CVE-2024-2389) in Progress Flowmon, a tool for monitoring network performance and visibility and used by more than 1,500 companies globally, has been found. An attacker can exploit the vulnerability to gain remote unauthenticated access to the Flowmon web interface and execute arbitrary system commands. This vulnerability impacts versions of the product v12.x and v11.x. It is highly encouraged for system administrators to upgrade to the latest releases - v12.3.4 and 11.1.14. The security update was released to all Flowmon customers either via automatic package download system or manually from the vendor's download centre. It is also highly recommended to upgrade all Flowmon modules afterwards. That is all! Enjoy the rest of the week and don't forget to update your devices and systems to the latest patches!
Back to Blog
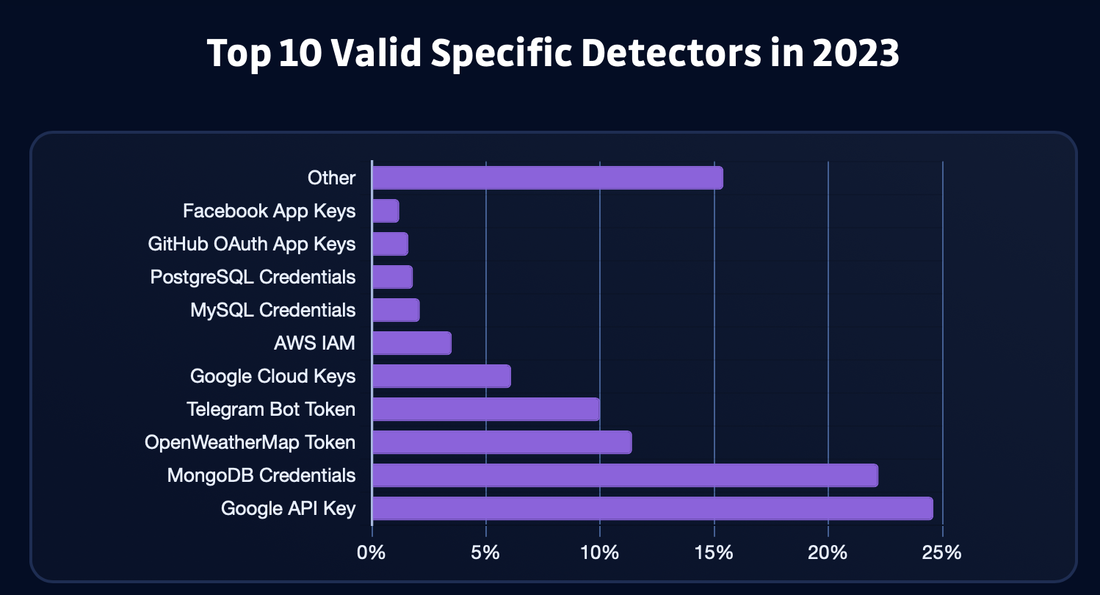
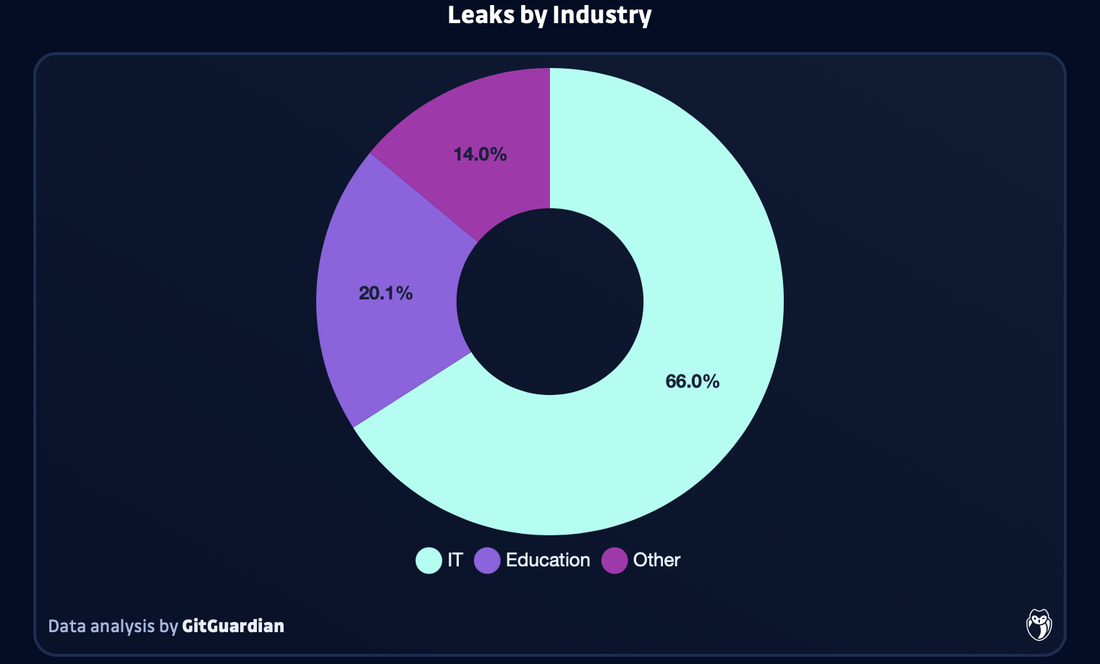
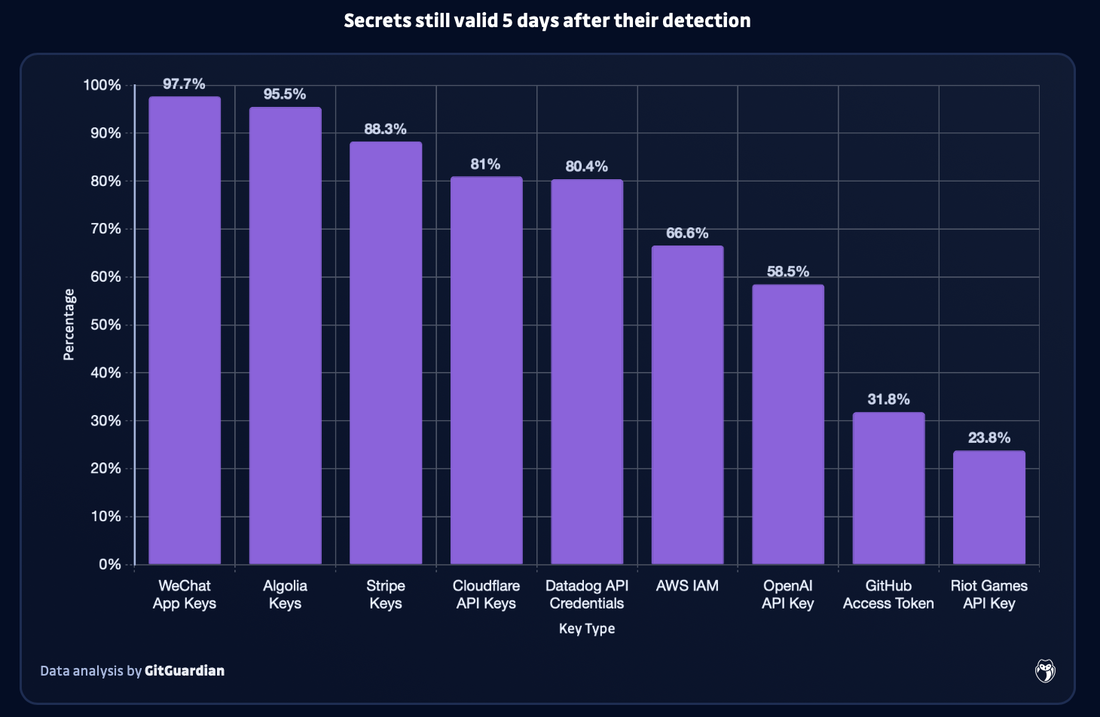
In the digital age, the protection of sensitive information is paramount. However, GitGuardian found that in 2023, GitHub users accidentally exposed 12.8 million authentication and sensitive secrets in over 3 million public repositories, with the vast majority of these secrets being still valid after 5 days. This incident serves as a stark reminder of the importance of robust cybersecurity measures and the need for increased vigilance. Join us as we delve into the details of this significant data breach, its implications for cybersecurity, and steps individuals and organisations can take to protect themselves. GitHub Leak: Unveiling the Scope In 2023, the number of authentication and sensitive secrets leaked on GitHub was 12.8 million. This is a 28% increase as compared to the previous year (10 million in 2022). Unfortunately, this is not surprising due to hard-coded credentials have always been one of the primary causes of security incidents in the software world. This is being exacerbated with the increasing complexity of digital supply chains. For instance, Sophos 2023 Report found that in 2023 compromised credentials was the top root cause of attacks for the first time. It was found that in the first half of the year, compromised credentials accounted for 50% of root causes, followed by vulnerability at 23%. What was Leaked The exposed secrets include account passwords, API keys, TLS/SSL certificates, encryption keys, cloud service credentials, OAuth tokens, as well as other sensitive data that could give external actors unlimited access to a range of private resources and services. All of this can lead to data breaches and financial damage. In 2023 alone, over 1 million valid occurrences of Google API secrets, 250,000 Google Cloud secrets, and 140,000 AWS secrets were detected.The reasoning for this is that there has been an increase in the number of code repositories on Github, with a 22% increase (50 million) in new repositories added in the past year. Therefore, this enhances the risk of accidental and deliberate exposure of sensitive information. Countries with the Most Leaks The top 10 countries with the most leaks are India, United States, Brazil, China, France, Canada, Vietnam, Indonesia, S.Korea and Germany. Sectors with the Most Leaks The most affected sector was the IT sector (this also includes software vendors), as it encompasses 65.9% of all detected leaks. This is then followed by Education (20.1%), Science & Tech (7%), Retail (1.5%), Manufacturing (1.2%), and Finance & Insurance (1%). Generative AI Leaks Trend Generative AI tools are exponentially growing in terms of their use in 2023 as many businesses and employees utilise them. However, this has also led to an exponential growth in generative AI leaks on GitHub last year as well. GitGuardian observed that in 2023, there was a 1,212 increase in the number of OpenAI API keys leaked on GitHub as compared to 2022. It was averaged that 46,441 API keys were leaked per month - this was the highest growing data point in GitGuardian’s report. Although OpenAI leads drastically in the number of leaks detected on GitHub, open-source AI models repository HuggingFace had a steep increase in leaked secrets month after month. This could indicate that there is a growing interest among developers and researchers of this AI tool. Other AI tools that were found to have leaks include Cohere, Claude, Clarifai, Google Bard, Pinecone, and Replicate. Although these AI tools were found to have leaks at a much lower level as compared to OpenAI and HuggingFace. Troubling Trend of Leaks GitGuardian monitored how well authors fixed leaks via revoking the secret as soon as possible to reduce the impact of the incident. Unfortunately, more than 90% of the secrets still remained valid 5 days after being leaked. Furthermore, only 2.6% of the leaks were revoked within 1 hour after GitGuardian notified them of the leak via email. However, not all types of leaked secrets were revoked at the same rate. Based on their analysis, leaked WeChat App (97.7% still remain valid after 5 days) and Algolia keys (95.5% still remain valid after 5 days) were the most likely to remain exposed for over 5 days. This is then followed by Strip keys (88.3%) and Cloudflare API keys (81%). Developers should be more concerned about these keys as they would be prime targets in credential harvesting campaigns.
GitHub Rectification In February, Github enabled push protection as a default for all public repositories to prevent accidental exposure of secrets when pushing new code. Related Topics 26 Billion Records Compromised in Huge Data Leak - dubbed as “Mother of All Breaches”. Apple's Alarming Report: 2.6 Billion User Records Exposed By Data Breaches in Past 2 Years 71 Million Emails from Naz.API stolen account list added to Have I Been Pwned.
Back to Blog
Last week, breaches and cyberattacks occurred across several industries from software, semiconductor, geospatial intelligence, consumer discretionary, gaming, telecom providers, smoke alarm, healthcare to the public sector. Devastating consequences have been uncovered from earlier data breaches and attacks, such as the Change Healthcare ransomware attack that cost UnitedHealth $872 million. Furthermore, new vulnerabilities and patches have also been found and releasedIt is highly recommended to not only be aware of them but to also update them as soon as possible.
Read on to receive a quick summary of what happened this week in the space of cybersecurity. Cisco’s Duo Multi-Factor Authentication (MFA) service breached. A 3rd party telephony service provider for Cisco’s Duo MFA service has been compromised by a social engineering cyber attack. Cisco Duo customers have been sent a notice to be on alert for any phishing attacks. In the notice sent to customers, the company explained that the 3rd party provider that handled SMS and VOIP MFA messaging traffic for them was breached on 1 April 2024. Reportedly, the threat actors utilised compromised employee credentials for the attack, and had managed to download SMS logs for specific users within a certain time frame once they were inside the service provider’s systems. In Cisco’s customer advisory, the attacker downloaded message logs for SMS messages that were sent to certain users under their Duo account between 1 March - 31 March 2024. The compromised information includes customers’ phone number, phone carrier, country and state to which each message was sent, as well as other metadata such as date and time of the message, type of message. However, no message content was compromised. In their advisory, Cisco Duo did not identify the breached telephony provider. Cisco advised impacted customers to notify anyone whose information was exposed, and to remain vigilant against any phishing attacks. Nexperia, a Dutch chipmaker, confirmed a data breach after a ransomware gang leaked stolen data. In a press statement on Friday, Nexperia disclosed that attackers managed to breach some of their IT servers in March 2024, which forced them to shut down the affected IT systems to contain the incident and implement extensive mitigation. Nexperia confirmed the incident after a ransomware group, Dunghill, claimed to have stolen 1 TB of confidential data and leaked a sample of the allegedly stolen files on 10 April 2024. The threat actors published images of microscope scans of electronic components, employee passports, non-disclosure agreements, and various other samples. However, the authenticity of the allegedly stolen data has not been confirmed by Nexperia. Dunghill claims that they plan to leak 371GB of design and product data, 246GN of engineering data, 96GB of commercial and marketing data, 41.5GB of corporate data, 109GB of client and user data, and 121.1GB of various files and miscellaneous data if the ransom demand is not paid. Nexperia has launched an investigation with the support of 3rd party experts to determine the nature and scope of the incident and to implement strong measures to prevent this incident from reoccurring. Nexperia also reported the incident to relevant authorities. UN investigating a ransomware attack that led to data theft. In a statement published on Tuesday, the United Nations Development Programme (UNDP) disclosed that they received a threat intelligence notification that a threat actor had hacked into their local IT infrastructure in UN city, Copenhagen, in late March. The stolen data included certain human resources and procurement information. The UN agency stated that actions were immediately taken to identify the source, contain the affected server and to determine the specifics of the exposed data, and the individuals impacted by this attack. Although the UN agency did not disclose the specific threat group, the 8Base ransomware gang added a new UNDP entry to their data leak website on 27 March. The attackers stated that they managed to exfiltrate large amounts of sensitive information, which includes personal data, accounting data, certificates, employment contracts, confidentiality agreements, invoices, receipts and more. Space Eyes data breach exposed sensitive data from critical US government agencies. Intelgroup, a threat group, has claimed to breach Space-Eyes, a geospatial intelligence firm that works exclusively with US government agencies. This includes the Department of Justice, the Department of Homeland Security, various branches of the US Armed Forces, and crucial intelligence bodies such as the National Geospatial Intelligence Agency. The breach has allegedly compromised the digital infrastructure of the firm, which could expose the US national security data. IntelBroker claimed that they only took 10-15 minutes to access the sensitive data from Space-Eyes systems. Singapore’s Ministry of Education (MOE): A 3rd party data breach has compromised the personal data of parents and staff at 127 schools. A data breach at one of MOE’s vendors has resulted in the names and email addresses of parents and staff from 5 primary schools and 122 secondary schools being compromised. MOE stated that they were notified by Mobile Guardian, a device management app installed on personal learning devices used by students, that their user management portal was breached on Wednesday, with the incident occurring at the company’s headquarters in Surrey, UK. As Mobile Guardian’s management portal was used for administrative purposes, user’s name, email address, time zone, school name and whether the user was a parent or school staff has been accessed. MOE also stated that their own device management app was not affected by the data breach as it is separate from Mobile Guardian’s user management portal. The Ministry has stated that all affected parties have been informed of the breach, and recommended victims to be vigilant against any phishing emails. The ministry stated that they have expressed their concerns to Mobile Guardian, and have lodged a police report. Mobile Guardian has implemented further security measures such as locking down all administrative accounts in response to the incident, and have also apologised for the breach. A Hospital in France had to postpone procedures after a cyberattack. The Hospital Simone Veil in Cannes (CHC-SV) announced on Tuesday that they were cyberattacked, which led to a severe impact on their operations. CHC-SV is an important medical establishment in France, particularly in the region of Cannes. The hospital were forced to take all their computers offline earlier this week due to a cyberattack, and had only their telephone systems available for communication. The hospital did not disclose much details but stated they have not received any ransom demand. Investigations are currently underway. Although all their units are continuing operations, all data has been reverted to pen and paper, and some patients had to be diverted to other hospitals nearby. Furthermore, roughly 30% of all non-urgent surgical procedures scheduled this week were cancelled, and many non-urgent consultations were rescheduled for later. The hospital stated that as of now their priority is to restart patient care systems that contain test results and patient records. However, this is dependent on the progress of the technical investigations which could take a long time. Atlantic fisheries body confirms data theft after 8Base ransomware gang claims breach. The Atlantic States Marine Fisheries Commission (ASMFC) disclosed that their email systems were down, and was forced to create a temporary email address and phone number. Tina Berger, director of communications for ASMFC, stated that they are responding to a cyber incident that is affecting their systems, but did not confirm if it was a ransomware attack. On Monday, the 8Base ransomware gang added ASMFC to their data leak site, and gave officials 4 days to meet their ransom demand. The gang claimed to have stolen invoices, personal data, contracts and more. Home Depot suffered a 3rd party breach: 10,000 employees’ personal information leaked. Home Depot has disclosed that a 3rd party breach from their SaaS vendor has resulted in a subset of employee data being leaked. The incident was known when IntelBroker, a known threat actor, claimed that they stole 10,000 Home Depot employees’ personal information. A Home Depot spokesperson has confirmed that the Atlanta, Georgia-based company has suffered a data breach. The personal information exposed includes employees’ names, work email addresses, and User IDs that were utilised during testing of their systems. Home Depot did not disclose the identity of the breached vendor, and it is unclear if Home Depot or the external vendor has notified the impacted individuals about the breach. Frontier Communications, a telecom provider, suffers a cyberattack: Forced to shut down their systems causing operational disruption. Frontier Communications, a leading American telecommunications provider, was forced to partially shut down some of their systems during a cyberattack to avoid threat actors from laterally moving through the network. This has resulted in some operational disruption. Despite their response, Frontier has stated that the attackers could access some personally identifiable information. Frontier believes that they have contained the breach, and has since restored their affected core IT systems, and is working on restoring normal business operations. Despite the company’s assurances, many customers have reported that their Internet connection has been down and that the support phone numbers are playing pre-recorded messages instead of redirecting to a human operator. In their SEC filing, Frontier stated they are currently investigating the incident with cybersecurity experts, and has also notified the relevant authorities. Void Interactive suffers from a massive data breach: Over 4TB of data stolen, including full source code. Void Interactive, the developer of Ready or Not, suffers from a massive data breach whereby over 4TB of data has been stolen, and this includes over 2.1 million files. The ransomware group announced in March that they had accessed Void Interactive’s data. However, Void Interactive has not announced any breach or concern regarding Ready or Not. Insider Gaming has been shown the contents of the stolen data, and it includes all of the Ready or Not source code, and code for what appears to be console builds of the game and results of various performance tests. Insider Gaming was also shown images of the game running on the PlayStation 4 test kit. There was also build data for Xbox 1, Xbox Series X|S, and PlayStation 5. Fortunately, it seems that the personal information of players or staff members have not been compromised, and the stolen data seems to be centred around the game itself. Smoke Alarm Solutions, a smoke alarm company in Australia, suffers from data breach. One of Australia’s largest smoke alarm companies, Smoke Alarm Solutions, have left 762,856 documents, which totals to 107GB of sensitive customer information exposed online in a non-password protected database, for nearly 3 months. The files included more than 355,000 detailed invoice data from 2021-2024, records of inspections, estimates, compliance reports, electrical safety inspections, service quotes, and service reports. Furthermore, nearly 25,000 additional documents marked as “on-site quotes” contained names and email addresses of the business, agent or individual obtaining the quote. Cybersecurity researchers have warned that these sensitive customer information were “very likely” accessed by malicious actors. Mr Fowler, in a report on this incident, stated that this exposure is “perfect timing” as this came days after Australia’s consumer watchdog warned of a surge in fake invoice scams which have cost Australians more than $16 million. As it is likely the threat actors accessed these sensitive customer data to use for scams and phishing attempts. UnitedHealth reported Change Healthcare ransomware attack cost $872 million. UnitedHealth Group reported that the February ransomware attack has cost $872 million on their Q1 earnings. This total cost includes $593 million in direct cyberattack response costs and $279 million due to business disruptions. Currently, the company is still working to mitigate the cyberattack’s impact on their consumers and care providers, while expanding financial assistance to affected providers. This report comes 1 day after the RansomHub extortion gang started leaking documents that allegedly contain patient and corporate data stolen from Change Healthcare’s compromised systems. The threat actors also warned that they have 5 days to pay the ransom to stop the data from being sold. Forminator WordPress plugin vulnerability affects over 300,000 sites. The Forminator WordPress plugin has a critical vulnerability (CVE-2024-29980) that allows malicious actors to perform unrestricted file uploads to the server. Site admins that use this plugin are highly advised to upgrade to the latest version 1.29.3, which addresses this vulnerability as soon as possible. Since the release of the security update on 8 April 2024, roughly 180,000 site admins have downloaded the plugin. However, this means that there are still 320,000 sites that remain vulnerable to attacks. That is all! Enjoy the rest of the week and don't forget to update your devices and systems to the latest patches!
Back to Blog
Palo Alto has warned on 13 April 2024 that hackers were actively exploiting an unauthenticated remote code execution vulnerability in their PAN-OS firewall software (tracked as CVE-2024-3400) since 26 March 2024. This critical vulnerability can allow hackers to use compromised devices to breach internal networks, steal data and credentials. Patches for this critical vulnerability have been available since 14 April 2024. It is strongly recommended for users and administrators of affected versions to immediately upgrade to the latest version.
This vulnerability affects the following products:
Palo Alto Networks decided to disclose this flaw and release mitigations earlier as the flaw was being used in attacks. They also released mitigations so that customers could protect their devices until patches were complete. Volexity has provided a method to detect if a Palo Alto Networks firewall has been compromised:
More information is available here: https://security.paloaltonetworks.com/CVE-2024-3400 https://docs.paloaltonetworks.com/pan-os/11-0/pan-os-admin/device-telemetry/device-telemetry-configure/device-telemetry-disable https://live.paloaltonetworks.com/t5/globalprotect-articles/applying-vulnerability-protection-to-globalprotect-interfaces/ta-p/340184 https://www.volexity.com/blog/2024/04/12/zero-day-exploitation-of-unauthenticated-remote-code-execution-vulnerability-in-globalprotect-cve-2024-3400/
Back to Blog
Last week, breaches and cyberattacks occurred across several industries from the streaming, business intelligence, veterinary, audio to the healthcare industry. Devastating consequences have been uncovered from earlier data breaches and attacks, such as Hoya receiving a $10 million ransomware demand for a file decryptor and for the allegedly 1.7 million stolen files to not be released. Additionally, it was found that a hacker that claimed responsibility for the Giant Tiger data breach has allegedly leaked 2.8 million customers’ records online. Furthermore, new vulnerabilities and patches have also been found and released for Microsoft, WordPressLG Smart TVs and Telegram Windows app. It is highly recommended to not only be aware of them but to also update them as soon as possible. Read on to receive a quick summary of what happened this week in the space of cybersecurity. Roku confirmed a second security incident: About 576,000 user accounts were hacked. Roku, a streaming giant, has confirmed a second security incident, in which about 576,000 user accounts were accessed via credential stuffing. However, Roku stated that fewer than 400 user accounts were breached, and where the malicious hackers made fraudulent purchases of Roku hardware and streaming subscriptions using the payment data stored in those users’ accounts. The company stated that they have refunded the affected customers. Furthermore, they emphasised that the malicious hackers did not access sensitive user information or full credit card details. Following these incidents, Roku has implemented 2-factor authentication, which helps add another layer of security to their users’ accounts. Sisense, a company that sells big-data analytic tools, suffers a data breach: CISA issues a red-alert. CISA, the US government cybersecurity agency, issued a red-alert on Thursday warning of a compromise of Sisense customer data, and highly recommended Sisense customers to immediately reset their credentials and secrets. Although the exact nature of the breach is unclear, the alert could suggest a massive supply chain security incident that exposed data from thousands of companies globally. CISA stated that they are partnering with private industry partners to respond to the incident and advised Sisense’s customers to reset their credentials and secrets, and to investigate and report to CISA if any suspicious activity has been detected. CISA is taking an active role as this data breach directly impacts critical infrastructure sector organizations. Sisense, which provides business intelligence and analytics tools that help process massive volumes of data, is involved in organizations in the U.S. healthcare, manufacturing, retail and technology sectors, hence a supply chain breach can have severe consequences. Non-profit healthcare service provider, GHC-SCW, disclosed that a ransomware gang has stolen 533,000 individuals’ health data. Group Health Cooperative of South Central Wisconsin (GHC-SCW) disclosed that a ransomware gang breached their networks on 25 January and stole 533,809 individuals’ personal and medical information. The health data stolen includes individuals’ names, birth dates and/or deaths, addresses, telephone numbers, email addresses, social security numbers, member numbers, and Medicare and/or Medicaid numbers. The attackers could not encrypt the compromised devices, which allowed GHC-SCW to secure their systems and bring them back online after they were isolated to contain the breach. GHC-SCW stated that they have added security measures to prevent such breaches from reoccurring, such as strengthening existing controls, data backup and user training. Impacted individuals are recommended to monitor all communications from healthcare providers - such as electronic messages, billing statements, and other communications, and to report any suspicious activity to GHC-SCW immediately. UK’s CVS Group suffers a cyberattack: Veterinary operations disrupted. UK veterinary services provider CVS Group disclosed that they had suffered a cyberattack which resulted in their IT services being disrupted across the country. In an announcement published on the London Stock Exchange site, CVS Group stated that threat actors gained unauthorized access to some of their IT systems. In response, the company took their IT systems offline, which disrupted their operations considerably over the past week. CVS stated that they have engaged in 3rd party specialists to help investigate the attack and to restore IT services safely across its clinics. CVS also announced that this cyberattack has sped up their plan to migrate all IT infrastructure to the cloud, which is expected to extend the period of operational disruption by several weeks for UK-based practices. BoAt, an Indian audio giant, is investigating a possible data breach of 7.5 million customers. BoAt, India’s largest audio and wearables brand, is investigating a possible data breach that may have compromised more than 7.5 million customers after hackers uploaded a sample of their alleged customer data on a known cybercrime forum. The stolen alleged data includes customers’ full name, phone number, email address, mailing address, and order numbers. TechCrunch reviewed a portion of the data, and found that the data reviewed seems genuine based on checks against exposed phone numbers. The hackers claim that the breach occurred in March. In a statement, boAt stated they have launched an investigation into recent claims of a potential customer data leak but did not disclose specifics. It was found that the leaked data also include references to Shopify. India outlet Athenil reported that the alleged hackers claimed the data was obtained via using credentials stolen from boAt’s systems. AT&T is now notifying that the data breach has actually impacted 52 million customers. AT&T is notifying 52 million former and current customers that a data breach has exposed their personal data on a hacking forum. While the leak contained the personal information of more than 70 million people, AT&T is now saying that the data breach impacted a total of 51,226,382 customers. The reason for the large difference is that some customers had multiple accounts in the dataset. In their notification, the exposed information varied for individuals and accounts, and it may include customers’ full name, email address, mailing address, phone number, social security number, birthdate, AT&T account number and passcode. AT&T stated that for each impacted customer they will notify the type of personal information that has been stolen. However, the company has still not disclosed how the data was stolen, and why it took them 5 years to confirm that the stolen data belonged to them and alert the impacted customers. Hoya, an optic giant, received a $10 million ransomware demand. Hoya Corporation has been hit by a cyberattack recently which was conducted by the ‘Hunters International’ ransomware operation. The ransomware group has demanded a $10 million ransom for a file decryptor and for the alleged 1.7 million stolen files, which amounted to 2 TB of data, to not be released. Currently, no files have been released on the ransomware group’s site, and the threat actors have not publicly claimed responsibility for the Hoya attack. LeMagIT has posted evidence via screenshots from the ransomware operation’s negotiation panel that victims use to negotiate a ransom payment. The ransomware group has applied a “No Negotiation/No Discount policy” on Hoya. The company has not provided any update on the business status since 4 April 2024, hence it is assumed that their production remains impacted and remediation efforts are still underway. Giant Tiger data breach claimed by hacker who leaked 2.8 million records online. A threat actor has publicly claimed responsibility for the Canadian retail chain - Giant Tiger data breach that occurred in March 2024, and has claimed to have uploaded the “full” database of the stolen Giant Tiger customer records - which amounts to 2.8 million records on a hacker forum. The stolen customer records include over 2.8 million unique email addresses, names, phone numbers and physical addresses. As well as the “website activity” of Giant Tiger customers. As of 12 April, the leaked data set has been added to the “Have I Been Pwned?” database, which is a free online service that allows one to check if their data has been compromised in known data breaches. The number of breached records associated with this data breach that has been added to HIBP is 2,842,669. Microsoft resolved a security lapse that exposed internal passwords. Security researchers from SOCRader discovered an open and public storage server that was hosted on Microsoft’s Azure cloud service that stored internal information relating to Microsoft’s Bing search engine. The internal information stored included code, scripts and configuration files that contain passwords, keys and credentials used by Microsoft employees to access other internal databases and systems. However, the storage server itself was not protected with a password, and could be accessed by anyone on the internet. The exposed internal information could potentially assist malicious actors in identifying or accessing other places where Microsoft stores its internal files, and hence could result in more significant data leaks and even services being compromised. The researchers notified Microsoft of the security lapse on 6 February, and Microsoft resolved the security lapse on 5 March. 4 vulnerabilities found which could lead to over 90,000 LG Smart TVs being exposed to remote attacks. Bitdefender security researchers have found 4 vulnerabilities (CVE-2023-6317, CVE-2023-6318, CVE-2023-6319, CVE-2023-632) that impact multiple versions of WebOS, the operating system used in LG smart TVs. The vulnerabilities allow different degrees of unauthorized access and control. This includes authorization bypass, privilege escalation, and command injection. Bitdefender explains that although the vulnerable LG WebOS service is supposed to be used only in local area networks (LAN) settings, an internet scan shows that 91,000 exposed devices are potentially vulnerable to the flaws. The vulnerabilities impact webOS 4.9.7 – 5.30.40 on LG43UM7000PLA, webOS 04.50.51 – 5.5.0 on OLED55CXPUA, webOS 0.36.50 – 6.3.3-442 on OLED48C1PUB, and webOS 03.33.85 – 7.3.1-43 on OLED55A23LA. Impacted users should apply the security update by selecting “Check for Update”. Thousands of WordPress sites compromised to promote crypto drainers. It has been discovered that over 2,000 compromised WordPress websites now display fake NFT and discount pop-ups to trick visitors into connecting their wallets to crypto drainers that would automatically steal their funds. According to MalwareHunterTeam, the threat actors have begun to monetize the hacked sites to display pop-ups promoting fake NFT offers and crypto discounts. And an Urlscan search showed that over 2,000 compromised websites have been loading the malicious scripts for the past week. To prevent falling victim to crypto drainers, only connect your wallet to trusted platforms. Furthermore, it is recommended to be vigilant against any unexpected pop-up windows, especially pop-ups that do not align with the website’s primary subject or design. Telegram released security patch to fix a Windows app zero-day vulnerability that could automatically launch Python scripts. Telegram has fixed a zero-day vulnerability in their Windows desktop app that could be used to bypass security warnings and automatically launch Python scripts. In a statement to BleepingComputer, Telegram disputes the existence of zero-click vulnerabilities as inaccurate. However, they have confirmed that they fixed the “issue” in the Windows app to prevent Python scripts from automatically launching when clicked. As stated it was a server-side fix that ensures that this issue no longer occurs, whereby when clicked it will cause Windows to ask what program you wish to open rather than automatically launching in Python. That is all! Enjoy the rest of the week and don't forget to update your devices and systems to the latest patches! |
|
© 2021, TAFA HOLDINGS (S) PTE LTD. ALL RIGHTS RESERVED
|

 RSS Feed
RSS Feed