AuthorTAFA Archives
April 2024
Categories
All
|
Back to Blog
In the ever-evolving landscape of cybersecurity, traditional antivirus software is no longer sufficient to combat the sophisticated and rapidly evolving threats. As cybercriminals become more adept at evading detection, the integration of machine learning (ML) and artificial intelligence (AI) has emerged as a game-changing approach to enhance the effectiveness of cybersecurity defenses. This is especially important as cyber attacks are rapidly increasing and evolving. For instance, it has been estimated that 560,000 new pieces of malware are detected every day, and there are now more than 1 billion malware programs circulating. This is especially true on the organization level. Depending on the size of the organization, there could be up to several hundred billion time-varying signals that need to be analyzed to accurately calculate risk. Hence, analyzing and improving cybersecurity defense is NOT a human-scale problem anymore. As a team of human experts cannot possibly address all of them. To make things worse, cybercriminals are increasingly utilizing AI to craft malicious content that are very convincing and execute sophisticated attacks. For instance, WormGPT, a black-hat-based tool has recently been launched by cybercriminals and it has the potential to conduct various social engineering attacks and Business Email Compromise (BEC) attacks, also known as whaling. Cybercriminals have long been using ChatGPT and other AI-based tools to generate malicious emails that seem legitimate to trick employees to give sensitive information. Hence, the use of AI in cybersecurity is essential in order to catch up with these malicious tactics. In this article, we will explore the role of machine learning and AI in cybersecurity and discuss why traditional antivirus solutions are becoming obsolete. The Power of Machine Learning and AI in Cybersecurity: “Time is the new currency in cybersecurity both for the defenders and the attackers” Chris McCurdy, General Manager, IBM AI and machine learning have become critical technologies in information security as they are effective tools for combating cyberattacks. It has been reported that 61% of organizations stated they will not be able to identify critical threats without AI, while 69% believe that AI is necessary to respond to cyberattacks. As we explore the power of machine learning and AI in cybersecurity, we will also frame the current pain points in cybersecurity. These pain points can be treated under the umbrella of machine learning and AI technologies.
Benefits of Machine Learning and AI Increase Speed Of Detection And Response As machine learning and AI can analyze large amounts of data in seconds. This makes them much faster than manually detecting threats, making them less time consuming. Furthermore, they can mitigate risk in near real-time, causing vast improvement in response times. This is especially important with the emergence of increasing sophisticated and ever-evolving cyber threats. From IBM’s report, security AI and automation had the biggest impact on speed of breach identification and containment for the surveyed company. Organizations that heavily utilized both AI and automation experienced a data breach lifecycle that was 108 shorter compared to organizations that did not deploy these technologies (214 days versus 322 days). Improve Accuracy And Efficiency Machine learning and AI security systems provide improved accuracy and efficiency as compared to traditional security solutions. As they are able to scan a myriad of devices and systems for potential vulnerabilities much faster than the time it would take human operators to do the same task. Additionally, they can also recognize patterns that may be difficult for the human eye to detect. This leads to a more accurate detection of potential cyber threats and malicious activities Cost Savings Machine learning and AI are cost-effective strategies as they reduce the effort and time required to detect and respond to threats. Hence, this lowers the cost of defending against cyber threats. According to Ponemon Institute, machine learning and AI can potentially save an average of more than $2.5 million in operating costs. Furthermore, they can automate tedious security tasks, freeing valuable resources to focus on other business areas. IBM’s report identified that AI and automation is the BIGGEST cost saver, with a saving of an average of US$1.76 million compared to those that had limited or no use. Improve Your Organization’s Security Posture Machine learning and AI helps strengthen cybersecurity over time as more data is analyzed and they become more proficient at identifying suspicious activities. Furthermore, they can overcome one of the security challenges: human error and negligence. Why Antivirus Solutions Are Becoming Obsolete:
Takeaway As cyber threats become increasingly sophisticated and dynamic, the integration of machine learning and AI in cybersecurity is revolutionizing the defense against these malicious activities. The power of these technologies lies in their ability to analyze vast amounts of data, detect anomalies, and respond in real-time. With their adaptive nature and predictive capabilities, machine learning and AI are reshaping the cybersecurity landscape, rendering traditional antivirus solutions obsolete. As organizations strive to protect their digital assets, embracing these advanced technologies becomes crucial for staying ahead of evolving cyber threats and ensuring robust security in the digital age. Cyber Security For Organizations with TAFA With the current cyber environment, organizations are facing increasingly sophisticated cyber threats. To protect against these threats, it is necessary to utilize cybersecurity solutions that can prevent zero-day and advanced cyber threats and help ensure regulatory compliance. With our prevention first and zero-trust approach to security using machine learning (ML) and artificial intelligence (AI), TAFA Shield will strengthen your company's ability to prevent and block cyber attacks and threats. To learn more information about TAFA Shield and how we can help your company, do not hesitate to contact us for more information. Related Topics Cybersecurity Wake-Up Call: The Skyrocketing Breach Costs of 2023 At All-Time High Ransomware Payments Skyrocket in 2023: The Unprecedented Surge and its Implications7 Types of Cyber Security Measures SMEs Need to Protect Their Business The Common Signs Of Being Cyberattacked
Back to Blog
In today's technology-driven world, cybersecurity has become one of the most important aspects of business operations. Companies and organizations need to ensure that their computer systems and networks are secure from threats such as malware, viruses, and other forms of cyberattacks. Two common approaches to endpoint security are Endpoint Detection and Response (EDR) and Endpoint Protection Platform (EPP). While both approaches focus on endpoint security, they differ in their features, functionalities, and capabilities. It is important to recognise that instead of choosing one of these approaches, organizations should select a solution that combines both EDR and EPP. Identify threats within your network with Endpoint Detection and Response (EDR) Endpoint detection and response (EDR) is a cybersecurity approach that focuses on detecting and responding to cyber threats on endpoint devices such as desktops, laptops, and servers. EDR solutions use advanced analytics and machine learning algorithms to identify suspicious activities on endpoints. EDR solutions also provide real-time visibility and alerts for security teams to respond to potential threats. EDR solutions typically provide the following functionalities:
Protect your endpoints with Endpoint Protection Platform (EPP) Endpoint protection platform (EPP) is a comprehensive security solution that provides a wide range of security features to protect endpoints from cyber threats. EPP solutions typically provide the following functionalities:
EDR vs EPP The main difference between EDR and EPP is their approach to endpoint security:
EDR solutions provide real-time visibility and alerts for security teams to respond to potential threats. While EPP solutions are designed to prevent cyber threats before they can cause harm. Now, you might now ask: so which one is better, and which one should I choose? The short answer: Both. Although both solutions are different in their approaches, they are both crucial solutions for endpoint security. Instead of choosing one of the solutions, you should choose a solution that offers both EDR and EPP. This will enable your company to have a comprehensive defense to protect your endpoints Takeaway Endpoint Detection and Response (EDR) and Endpoint Protection Platform (EPP) are two common approaches to endpoint security. EDR focuses on detecting and responding to cyber threats on endpoints, while EPP provides a comprehensive security solution that includes endpoint protection and prevention capabilities. EDR solutions provide real-time visibility and alerts for security teams to respond to potential threats, while EPP solutions provide a wide range of security features to prevent cyber threats before they can cause harm. EDR and EPP are complementary tools. EPP acts as a preventative security measure, while EDR supports incident detection and response. Therefore, both are needed to ensure comprehensive defense is implemented to protect your endpoints Securing the Endpoint with TAFA Shield With the current cyber environment, endpoint protection is now essential to your cybersecurity strategy. There are many endpoint solutions that exists in this space, therefore selecting the right endpoint security protection is necessary to prevent and block cyber attacks and threats. With our prevention first and zero-trust approach to security, TAFA Shield will strengthen your company's ability to prevent and block cyber attacks and threats. To learn more information about TAFA Shield and how we can help your company, do not hesitate to contact us for more information.
Back to Blog
Exciting Announcement!
Paul will bring his knowledge to our team and help us create innovative solutions to address the ever-evolving cybersecurity landscape.
We're confident that with Paul's leadership, our new cybersecurity services and education venture will help individuals and organisations stay protected and educate and inspire the next generation of cybersecurity professionals. Join us in giving Paul a warm welcome!
Back to Blog
As a renowned cybersecurity expert, Campbell has earned his stripes as an ethical hacker and a cyber threat intelligence specialist. He has been a keynote speaker at various international events, offering unique insights into the ever-evolving cyber landscape.
Outside of his work, Campbell's love for sailing and expertise in marine electronics adds a unique dimension to his skill set. We're excited to have Campbell on board, helping to shape the future of our cybersecurity business and strengthening our commitment to providing cutting-edge solutions for our clients. Get to know more about Campbell's expertise here: Please join us in welcoming Campbell Murray to the team!
Back to Blog
Endpoint detection and response (EDR) is a critical security technology that provides organizations with the ability to detect and respond to advanced threats that may bypass traditional security defenses such as firewalls and antivirus solutions. EDR solutions focus on monitoring endpoints, such as laptops, desktops, servers, and mobile devices, for suspicious activity and provide real-time alerts to security teams to take action and prevent potential breaches. The need for EDR solutions has grown as cyber attackers have become more sophisticated in their methods and are constantly finding new ways to bypass traditional security measures such as firewalls and antivirus software. With EDR solutions, you can have a more proactive approach to security, detecting and preventing attacks before they cause significant damage. How EDR works EDR solutions operate by collecting data from endpoints, analyzing it in real-time and providing security teams with a comprehensive view of the organization's security posture. The data can include information on user behavior, system configurations, network connections, and application activity. EDR solutions use advanced techniques such as behavioral analysis, machine learning, and artificial intelligence to detect threats that may evade traditional security solutions. When EDR solutions identify a potential threat, they provide security teams with a detailed alert that includes information on the source of the threat, the type of attack, and the potential impact on the organization. This allows security teams to take immediate action to isolate the threat, contain the attack and prevent it from spreading across the network. Why use EDR? The Benefits There are several benefits of implementing an EDR solution, including:
Takeaway
EDR solutions are a critical security technology that provides your company with the ability to detect and respond to advanced threats. By providing real-time alerts, improved visibility, and advanced threat detection, EDR solutions can help your company stay ahead of cyber attackers and prevent potential breaches. Companies that invest in EDR solutions can have a more proactive approach to security and reduce the risk of significant data breaches. Securing the Endpoint with TAFA Shield There are many endpoint protection solutions that exists in this space. Therefore selecting the right endpoint security solution is necessary to prevent and block cyber attacks and threats. With our prevention first and zero-trust approach to security, TAFA Shield will strengthen your company's ability to prevent and block cyber attacks and threats. To learn more information about TAFA Shield and how we can help your company, do not hesitate to contact us for more information.
Back to Blog
In today's world, endpoint security is essential and crucial than ever before. With the rise of remote work and the increasing number of endpoints being used by organizations, the attack surface for cybercriminals has grown significantly. Endpoint devices can be a weak point in an organization's security posture, as they are often outside of the network perimeter and can be easily compromised if not properly protected. Hence, EPP is important in helping your organization to protect your endpoints from cyber attacks. What is EPP? Endpoint protection platforms (EPP) are a type of security software that helps organizations protect their endpoint devices from cyber threats. These devices could include laptops, desktops, mobile phones, tablets, servers, and even IoT devices. EPP solutions provide a range of security features, including malware detection and prevention, firewall protection, intrusion detection and prevention, data loss prevention, and more. What are the benefits of EPP? Endpoint protection platforms offer several benefits to organizations looking to secure their endpoints. 1. They provide a centralized platform for managing and monitoring the security of all endpoint devices across an organization. This makes it easier for IT teams to identify and respond to threats quickly and efficiently. 2. EPP solutions typically offer advanced threat detection and prevention capabilities, using a combination of signature-based and behavioral analysis techniques.
3. EPP solutions can provide additional security features, such as firewall protection, intrusion detection and prevention, and data loss prevention.
How to choose an EPP? These are several factors that you should consider when choosing an endpoint protection platform: 1. You should look for a solution that offers comprehensive security features.
2. You should consider ease of management and deployment of the solution.
3. You also have to consider the cost of the solution, as well as any ongoing maintenance and support fees. While EPP solutions can be expensive, they are essential for protecting endpoint devices from cyber threats. Hence, this solution should be considered a necessary investment for any organization. Key Takeaway Endpoint protection platforms are an essential component of any organization's security strategy. They provide comprehensive security features for protecting endpoint devices from a wide range of threats, and offer a centralized platform for managing and monitoring endpoint security. By investing in an EPP solution, especially the next-generation EPP solution, organizations can ensure that their endpoints are protected from cyber threats and that their sensitive data remains secure. Securing the Endpoint with TAFA Shield There are many endpoint protection solutions that exists in this space. Therefore selecting the right endpoint security solution is necessary to prevent and block cyber attacks and threats. With our prevention first and zero-trust approach to security, TAFA Shield will strengthen your company's ability to prevent and block cyber attacks and threats. To learn more information about TAFA Shield and how we can help your company, do not hesitate to contact us for more information.
Back to Blog
Network security is a critical component of modern information technology infrastructure. In today's interconnected world, networks are a central part of how we communicate, conduct business, and share information. Hence, protecting these networks from security threats is vital to maintaining the confidentiality, integrity, and availability of data and services. In this post, we'll explore the basics of network security, including common threats and best practices for protecting your network. What is network security? Network security refers to the practice of protecting computer networks from unauthorized access, misuse, modification, or destruction. Network security involves a combination of hardware, software, policies, and procedures that work together to prevent and mitigate security risks. Overall, the goal of network security is to create a safe and secure environment for users to access and share information over a network, while minimizing the risks of unauthorized access, data breaches, and other security threats. Common threats & vulnerabilities Effective network security requires a comprehensive approach that addresses various types of threats and vulnerabilities, including: 1. Unauthorized access: The risk of unauthorized access to a network is one of the most significant threats. Hackers and other malicious actors may try to gain access to a network to steal sensitive information, disrupt services, or plant malware. 2. Malware: Malware, or malicious software, is a common threat to network security. Malware can be used to steal information, damage systems, or disrupt network services. 3. Phishing: Phishing is a social engineering technique that involves tricking users into revealing sensitive information, such as usernames, passwords, and credit card numbers. 4. Denial of service (DoS): A DoS attack is an attempt to overwhelm a network with traffic, rendering it inaccessible to users. 5. Data breaches: A data breach is the unauthorized access to, or disclosure of, sensitive data, such as customer information, financial data, or intellectual property How to protect your network Protecting your network requires a multi-layered approach that addresses various security threats and vulnerabilities. Here are some best practices for securing your network: 1. Strong passwords: Passwords are a critical part of network security. Ensure that all users choose strong passwords that are difficult to guess, and change them regularly. 2. Use firewalls: Firewalls are a network security tool that can help prevent unauthorized access to your network. Ensure that your network has both hardware and software firewalls in place. Also ensure that they are regularly updated. 3. Use Endpoint Detection and Response [EDR] & Endpoint Protection Platforms [EPP] solutions: Firewalls helps you control large groups of computers, however precise device security is essential. These device security solutions helps secure laptops and BYOD devices by creating security layers. They are complementary tools - EPP acts as a preventative security measure (1st line of defense - identifying and blocking malware), while EDR supports incident detection and response (2nd line of defense - proactively identify threats and protecting from them). It is best to use a solution that offers both EPP and EDR to protect you from cyber threats. 4. Audit regularly: Perform regular audits to identify vulnerabilities in your systems and confirm the overall efficacy of your security infrastructure. This is akin to regular health checkups to ensure that your systems are protected, and help point out any vulnerabilities that you can fix in your systems. Security audits can be done via third party penetration testing and vulnerability assessment. 5. Implement access controls: Access controls limit the ability of users to access sensitive data or systems. Implement access controls based on the principle of least privilege, where users are only given access to the minimum resources necessary to perform their job. 6. Encrypt sensitive data: Encryption is the process of converting data into a secret code to prevent unauthorized access. Use encryption to protect sensitive data, such as credit card numbers, passwords, and customer information. 7. Educate users: Employee education is a critical component of network security. Ensure that all users are aware of security risks, best practices, and policies. Takeaway
In today's digital age, network security is more critical than ever. A single security breach can result in significant financial losses, reputational damage, and legal liabilities. Protecting your network requires a comprehensive approach that includes hardware, software, policies, and procedures. By following best practices for network security, you can minimize the risks of security threats and ensure the confidentiality, integrity, and availability of your data and services
Back to Blog
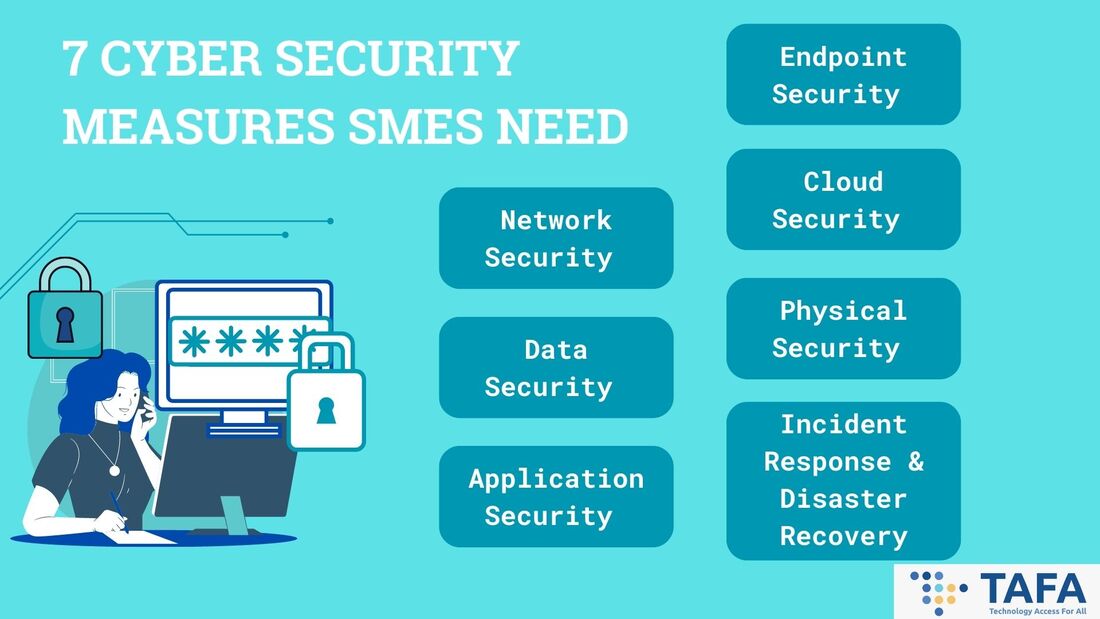
As cyber attacks become more prevalent, small and medium-sized enterprises (SMEs) need to be aware of the different types of cyber security measures they can implement to protect their business. So how do you stay safe? Here are 7 types of cyber security that SMEs should be aware of. 1. Network Security Network security refers to securing a business's computer network against unauthorized access, misuse, or hacking. SMEs can implement firewalls, intrusion detection and prevention systems, and virtual private networks (VPNs) to protect their network from cyber threats. 2. Data Security Data security involves protecting sensitive information from unauthorized access, disclosure, or destruction. SMEs can use encryption, access control, and data backup and recovery solutions to protect their data. 3. Application Security Application security involves securing business applications against cyber threats. SMEs can implement secure coding practices, regular software updates, and vulnerability testing to ensure their applications are secure. 4. Endpoint Security Endpoint security involves securing devices such as laptops, desktops, and mobile devices that are used to access a business's network. SMEs should replace their anti-viruses software with next-generation and future proof endpoint security solutions as anti-viruses are no longer effective against modern day cyber threats, which are more sophisticated. SMEs can also implement firewalls, and encryption to protect their endpoints from cyber threats. Related Topics: Endpoint Protection Platform VS Endpoint Detection & Response 5. Cloud Security Many SMEs are now using cloud services to store and access data. Cloud security involves securing cloud infrastructure and data against unauthorized access, disclosure, or destruction. SMEs can use access controls, encryption, and regular security audits to protect their data in the cloud. 6. Physical Security Physical security involves securing physical assets such as servers, routers, and other network devices against theft, damage, or destruction. SMEs can implement physical access controls, surveillance systems, and backup power supplies to protect their physical assets. 7. Incident Response and Disaster Recovery This type of security involves having a plan in place to respond to cyber attacks and recover from them. SMEs should have a detailed incident response plan that outlines the steps to take in the event of a cyber attack, and a disaster recovery plan that outlines the steps to take to recover from a cyber attack Takeaway
SMEs should be aware of the different types of cyber security measures they can implement to protect their business. By implementing these measures, SMEs can safeguard their network, data, applications, endpoints, cloud infrastructure, physical assets, and respond effectively to cyber attacks. Hence, it is important to work with a trusted cybersecurity provider to help assess your current security posture and develop a comprehensive security strategy tailored to your specific needs. With this, your business, customers, and their data will be protected from the increasing cyber threats that are impacted SMEs globally. Looking to enhance your company’s cyber security? Contact us for more information. With our prevention first and zero-trust approach to security, TAFA Shield will strengthen your ability to secure your business.
Back to Blog
TAFA Partners with BlackBerry to Strengthen Cybersecurity Offering for SMBs in Philippines and ASEAN12/8/2022 New agreement gives more small and medium businesses access to BlackBerry’s AI-driven, prevention-first cybersecurity solutions and managed (XDR) services Manila, Philippines – TAFA Holdings (S) Pte Ltd, a cybersecurity consulting company based in Singapore, announced a distribution agreement with BlackBerry Limited (NYSE: BB; TSX: BB) for wider availability of BlackBerry® cybersecurity solutions and services for ASEAN organizations. SMBs now have access to enterprise-grade cybersecurity and round-the-clock support at a fraction of the cost, thanks to BlackBerry’s shared service model. TAFA Holdings has been granted a license to provide Managed Security Operations Centre (SOC) Monitoring Service by Singapore’s Cybersecurity Services Regulation Office (CSRO) to ensure the highest level of trust for customers of cybersecurity services. Under the agreement, TAFA will offer the full BlackBerry® Cyber Suite, including Cylance® Protect, Cylance® Optics and Cylance® Guard, as a 24/7 managed Extended Detection and Response (XDR) service. This partnership will help organisations protect end-points and data from malware and breaches. Cylance Guard’s XDR capability will also help to address cyber-skills shortages for businesses with lean or non-existent in-house security teams. “As organisations across ASEAN experience heightened cyber threats, traditional signature-based solutions fail to address the severity of attacks,” said Wee Ah Kee, CEO, TAFA. “By expanding our offering with BlackBerry’s, we can further help businesses of any size improve their security posture with a prevention-first approach.” Blackberry 2022 Threat Report showed an increasing ransomware-as-a-service (RaaS) and malware-as-a-service (MaaS) tools to execute high-impact attacks, with that, SMEs are now facing 11 to 13 cyberattacks per device per day. In the Philippines, SMBs make up the back bone of the economy, making cybersecurity an integral aspect as SMBs gear towards digitalization. Graeme Pyper, Director, Channel Partner and Alliances, APAC, BlackBerry adds, “BlackBerry's eighth-generation AI engine and on-demand cybersecurity experts, make it possible for organisations to prevent threats and address IT security skills gaps to get their business running.” TAFA is proud to partner with HAFA Asia Corporation to provide managed cybersecurity services that help businesses of all size achieve Total Security Compliance. For information about BlackBerry® Cyber Suite, visit here. To download a copy of the 2022 BlackBerry Threat Report , visit here. For more information about TAFA click here. Check out our article at Philippines Star here. You can also find us on page 10-11 in the latest issue of PHILSME Magazine here. |
|
© 2021, TAFA HOLDINGS (S) PTE LTD. ALL RIGHTS RESERVED
|

 RSS Feed
RSS Feed