AuthorTAFA Archives
April 2024
Categories
All
|
Back to Blog
Last week, breaches and cyberattacks occurred across several industries from the public sector, mortgage, IT, cryptocurrency, to the water and wastewater treatment industry. Devastating consequences have been uncovered from earlier data breaches and attacks, such as the massive data leak of 26 billion records detected from sites like Twitter, Canva, Telegram etc., and raw genotype data and health reports stolen from the 23andMe data breach. Furthermore, new vulnerabilities and patches have also been found and released. It is highly recommended to not only be aware of them but to also update them as soon as possible.
Read on to receive a quick summary of what happened this week in the space of cybersecurity. LoanDepot data breach impacts 16.6 million customers. LoanDepot has confirmed that around 16.6 million of their customers have had their personal information stolen. In a new filing to the US Securities and Exchange Commission (SEC), LoanDepot gave more details about the cyber incident that affected their computer systems on 8 January. From the filing, initial results show that an unauthorised 3rd party had managed to access approximately 16.6 million individuals’ personal data in their systems. The company has promised to notify impacted customers and will offer free credit monitoring and identity protection services. The company also indicated that they had made “significant progress” in restoring their systems including their MyloanDepot and Servicing customer portals. The company has also set up a new microsite - loandepot.cyberincidentupdate.com to provide operational updates. Massive data leak of 26 Billion records detected from sites like Twitter, Linkedin etc. Researchers from Security Discovery and Cybernews revealed that a massive database that contains no less than 26 billion leaked records were found on an unsecured page dubbed “Mother of all Breaches”, and runs to 12 terabytes in size. It contains 26 billion records, over 3,800 folders, with each folder corresponding to a separate data breach. The database contains sensitive information from Twitter, Linkedin, Dropbox, Chinese messaging giant Tencent, Chinese social media platform Weibo, Adobe, Canva, Telegram etc. Records from an assortment of US and other government organisations can also be found. In the database, several username and password combinations were found. However, fortunately only a minor part of the database is new. The research team said that it’s more a case of compiled records from thousands of previous breaches and data leaks. The research team also believes the database was compiled by a malicious actor or data broker. The Australian government issues sanctions on an individual linked to the Medibank data breach. The Australian federal government has revealed Russian citizen and cybercriminal Aleksandr Ermakov is linked to the Medibank Private data breach that saw the personal identifiable information and critical medical information of Australian citizens and international students leaked on the dark web. The government imposed targeted financial and travel sanctions on Aleksandr Ermakov, an Australian first for cybercrimes. This means providing assets to Ermakov or to use or deal with his assets (this also includes cryptocurrency wallets or ransomware payments) is a criminal offence punishable by up to 10 years’ imprisonment and heavy fines. The US and UK have also joined Australia in sanctioning Aleksandr Ermakov. The Kansas City Area Transportation Authority (KCATA) was hit by a ransomware attack. KCATA announced that they were hit by a ransomware attack on 23 January that impacted all their communication systems. They have contacted all appropriate authorities. Due to the attack, the regional RideKC call centres cannot receive calls, nor can any KCATA landline. In the announcement, they have provided alternative phone numbers for Freedom and Freedom-On-Demand Paratransit customers who need to schedule a trip. Despite the disruption in call centres, passenger transit operations have not been impacted. As of yet, the agency has not has not elaborated on if the sensitive information of their customers have been compromised. The Medusa ransomware gang has claimed responsibility for the attack on KCATA, and posted data samples that allegedly belong to the agency on their extortion portal. Veolia North America, a water services giant, suffers a ransomware attack. Veolia North America disclosed that they have been hit by a ransomware attack which impacted systems that are part of the Municipal Water division, and disrupted their bill payment systems. Upon detecting the attack, Veolia has implemented defensive measures, and has taken some of their systems offline temporarily to contain the breach. Veolia is now working with law enforcement and 3rd party forensic experts to determine the impact of the attack on their operations and systems. Veolia stated that the systems and servers that were taken offline after the attack are now back online, and customers’ payments will not be affected. The company also states that customers will not be penalised for late payments or charged interest for their bills due to this service interruption. As the attack was only confined to their internal back-end systems, there’s no evidence to suggest that the attack affected their water or wastewater treatment options. As of now, the company has discovered a limited number of individuals that may have had their personal information impacted during the breach. Exposed Trello API abused to link email addresses to 15 million accounts. A publicly exposed Trello API was used to associate email addresses with public Trello profiles. News of the Trello data leak occurred when ‘emo’ , an alias, attempted to sell the data of 15,115,516 Trello members on a popular hacking forum, which includes their emails, usernames, full names and other account information. From emo, it was found that you can query REST API using an email address, and if there is an associated account, retrieve their public profile information. Emo further said that the API was publicly accessible, which means one does not have to log into a Trello account or use an API authentication key. Using this, emo built a list of 500 million email addresses, and fed them into the API to determine if they were associated with a Trello account. Trello replied that they have made a change to the REST API so that unauthenticated users/services cannot request another users’ public information by email. To those concerned, the Trello leak has been added to the Have I Been Pwned data breach notification service. This allows anyone to check if they are among the 15 million leaked email addresses. Personal data of 66,000 customers exposed in Trezor support data breach. Trezor, a hardware cryptocurrency wallet vendor, has issued a security alert after a data breach on 17 January was identified due to unauthorised access to their 3rd party support ticketing portal. The company stated that investigations are ongoing but so far they found no evidence that users’ funds were compromised in this breach. However, 66,000 users who interacted with Trezor Support since December 2021 may have had their names or usernames, and email addresses exposed to an unauthorised party. Although postal addresses, phone numbers and other personally identifiable information were also stored on the breached system, Trezor does not believe that these were impacted. Trezor has confirmed 41 cases where exposed data has been exploited, with threat actors approaching users, via email, to trick them into giving away their recovery seeds - a string of words that contain all the information needed to gain access to a wallet. They do so by emailing users that seems like an automated reply from support, which requests the users to disclose the 24-word phrase used for setting up their Trezor wallets. Trezor has reached out to all potentially affected users, and warns them of phishing attacks that would attempt to obtain their recovery seeds. It is highly recommended for Trezor users, especially those who connected support after December 2021, to be highly vigilant against phishing and scamming attempts. Tietoevry ransomware attack causes widespread outages in Swedish firms. Tietoevry, a Finnish IT services and enterprise cloud hosting provider, suffered an Akira ransomware attack that occurred on last Friday night into Saturday morning, and has impacted one of their data centres in Sweden. The company immediately isolated the affected platform upon discovering the attack, and hence has not affected other parts of the company’s infrastructure. The attack encrypted the company’s virtualisation and management servers used to host the websites or applications for Swedish firms which led to widespread outrages for these firms. Continuation of 23andMe data breach: Customers’ raw genotype data and health reports stolen. 23andMe, the genetic testing provider, confirmed that the hackers stole impacted customers’ raw genotype data and health reports - such as health-predisposition reports, wellness reports, and carrier status reports. The data were stolen as a result of an unnoticed credential stuffing attack from 29 April to 27 September. Some of the stolen data has been posted on the BreachForums hacking forum and the unofficial 23andMe subreddit site. The leaked information includes 4.1 million people living in the UK, and 1 million Ashkenazi Jews. For customers who utilised 23andMe’s DNA Relatives feature, it’s possible that the attackers also scraped their DNA Relatives and Family Tree profile information. The following information may have also been compromised if shared via the DNA Relatives feature: Ancestry reports and matching DNA segments, self-reported location (city/zip code), ancestor birth location and family names, profile picture, birth year, and anything includes in the “Introduce yourself” section. Hewlett Packard Enterprise (HPE) corporate emails breached by Russian hackers. HPE disclosed on 24 January that suspected Russian hackers, Midnight Blizzard, gained access to their Microsoft Office 365 email environment to steal data from their cybersecurity team and other departments. In a new Form 8-K SEC filing, HPE stated they were notified on 12 December that the suspected Russian hackers breached their cloud-based email environment in May 2023. From their investigation, it was found that the hackers accessed and exfiltrated data from a small percentage of mailboxes belonging to individuals in their cybersecurity, go-to-market, business segments, and other functions. The company continues to work with external cybersecurity experts and law enforcement to investigate the incident. This breach comes days after Microsoft disclosed that the inboxes that belong to their senior leadership has been breached by a Russian threat actor believed to be Midnight Blizzard. Southern Water confirmed they were hit by a data breach after a ransomware group leaked customers’ data. Southern Water, a UK water supplier, confirmed that they suffered a data breach after the Black Basta ransomware group seemed to have leak their customers’ data. In a post on 23 January by Southern Water, the company admitted that “a limited amount of data has been published”. The post stated that the company is aware of the ransomware gang claim, and that they had previously detected suspicious activity, as well as stated they had launched an investigation. The company emphasised that their usual services have not been impacted by the breach. A spokesperson of the company has also stated on their Twitter account that as of now, there is no evidence that customer relationships or financial systems have been affected, and if customer data has been stolen, their customers will be notified directly. The ransomware gang has claimed earlier that they managed to breach Southern Water and published a small amount of data. The stolen data included customers’ identity documents such as passports and driving licences, HR-related documents that displays customers’ personal data such as their home address, office address, birthdates, nationalities and email addresses, and corporate car-leasing documents. Black Basta has stated that the rest of the data will be released unless the company pays the ransom by 29 February. EquiLend hit by a cyberattack: Operations disrupted with some systems taken offline. Equilend, a securities lending platform, stated that their operations have been disrupted after portions of their systems were taken offline in the Monday cyberattack. Following the incident, the company also detected unauthorised access to their network, and are now working to restore all affected services. The company has also hired third-party cybersecurity experts to help assist in investigating the security breach and to help speed up their restoration efforts. Equilend’s clients have been advised that this may take several days. The company has yet to disclose if any company or customer data were compromised or stolen during the cyberattack. Lockbit ransomware representative, LockBitSupp, claimed responsibility for the attack in a statement to Bloomberg. However, Equilend has yet to confirm this claim on their page dedicated to sharing more information on the incident. Critical severity flaw in WordPress database plugin active on 1 million sites being exploited by hackers. Researchers have observed that hackers have been targeting a critical severity flaw (tracked as CVE-2023-6933) in the ‘Better Search Replace’ WordPress plugin with over thousands of attempts occurring in 24 hours. This WordPress plugin has more than 1 million installations. This vulnerability is a PHP object injection vulnerability which allows unauthenticated users to inject a PHP object. This can lead to code execution, unauthorised access to sensitive data, file manipulation or deletion, and trigger an infinite loop denial of service condition. The Better Search Replace plugin is not directly vulnerable but can be exploited to execute code, retrieve sensitive data or delete files if another plugin or theme on the same site contains the Property Oriented Programming (POP) chain. As WordPress security firm, Wordfence, reports hackers have been taking advantage of the vulnerability as they have blocked over 2,500 attacks targeting the vulnerability on their clients over the past 24 hours. This flaw impacts all Better Search Replace versions up to 1.4.4. Users are strongly recommended to upgrade to 1.4.5 immediately. Apple released security updates to fix the 1st zero-day vulnerability exploited in attacks. Apple released security updates to fix 2024's first zero-day vulnerability (CVE-2024-23222) exploited in attacks that could impact iPhones, Macs, and Apple TVs (iOS, macOS, tvOS, Safari). This vulnerability is a WebKit confusion issue that attackers can exploit to gain code execution on targeted devices. This will allow attackers to execute arbitrary malicious code on devices running these vulnerable versions after opening a malicious web page. This vulnerability is addressed with improved checks in iOS 16.7.5 and later, iPadOS 16.7.5 and later, and macOS Monterey 12.7.3 and higher, as well as on tvOS 17.3 and later. It is highly recommended for all Apple users to update their devices to the latest version. That is all! Enjoy the rest of the week and don't forget to update your devices and systems to the latest patches!
Back to Blog
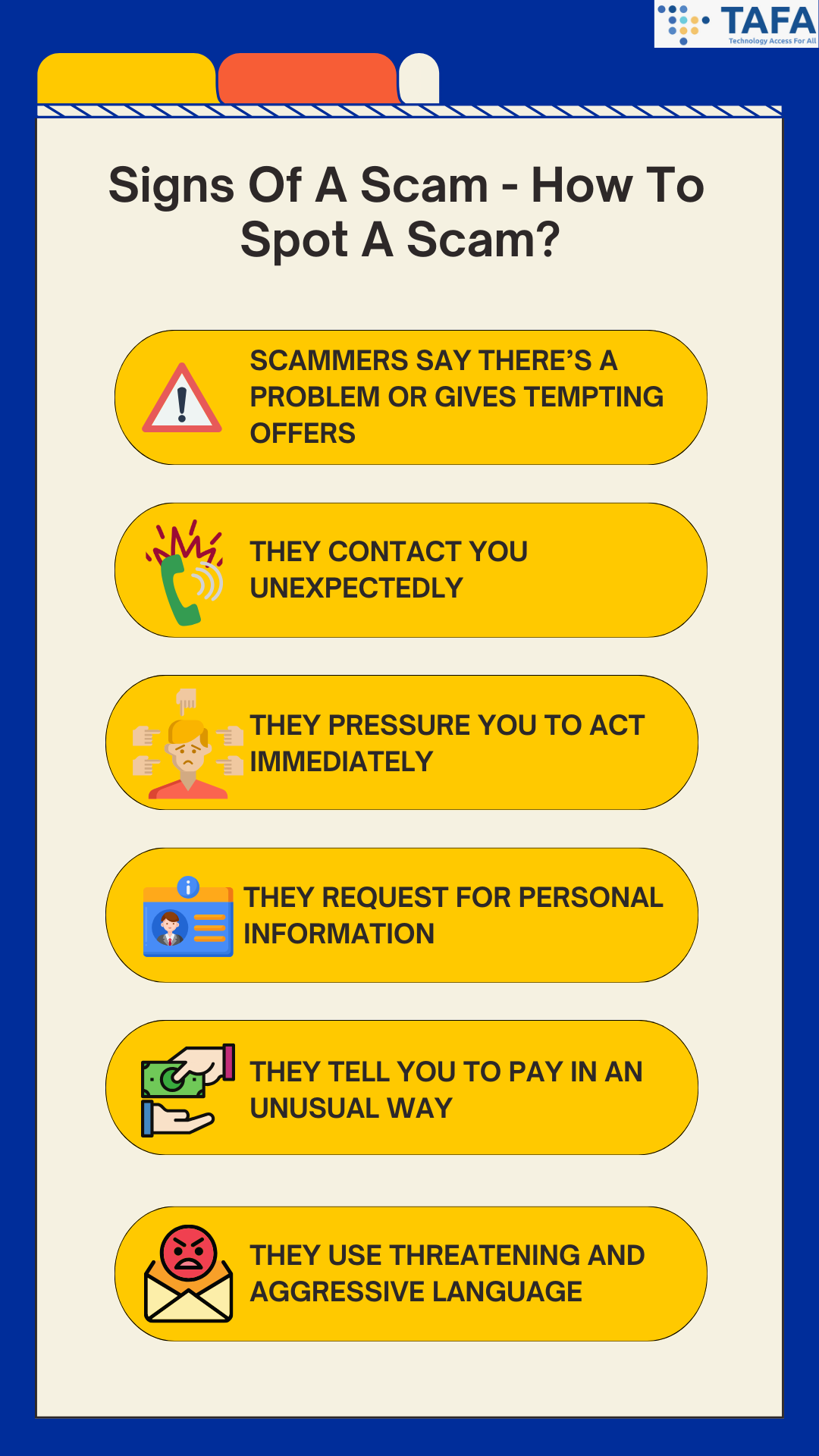
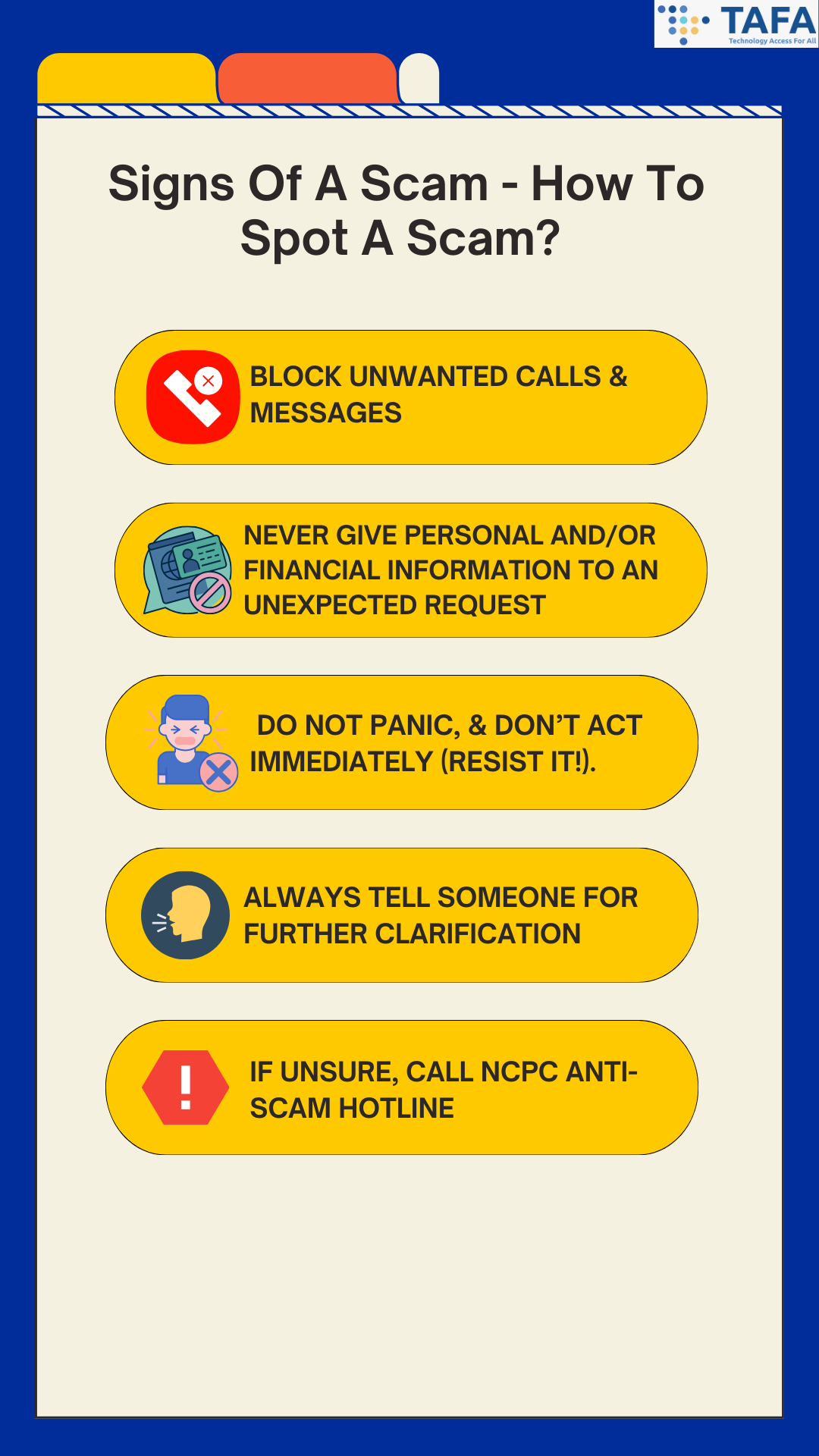
In the vast landscape of the internet, deception often lurks behind enticing offers and too-good-to-be-true deals. Scams have evolved into sophisticated forms, but so has our ability to recognize and thwart them. Read on to find out how to recognise the signs, and avoid getting scammed. Signs Of A Scam - How To Spot A Scam? 1) Scammers say there’s a problem or gives tempting offers Scammers might say you are in trouble with the government, money is owed, there’s a problem with your account (be it social media, email or banking accounts), a computer virus has been detected or someone in your family had an emergency. Or alternatively, they give you tempting offers - e.g. deals that are price way below market rates. If it sounds too good to be true, it probably is! This sign tends to appear in scams such as loan scams, e-commerce scams. Investment scams, job scams, and money laundering scams. 2) They contact you unexpectedly One of the easiest ways to spot a scammer is that they will tend to contact you first. If you receive any unexpected emails, messages or phone calls from someone you don’t know, it is best to verify they are who they said they are by contacting their business or agency directly. If you are not 100% convinced by the identity of the caller, hang up and contact the company directly. 3) They pressure you to act immediately Pressure can take all sorts of forms, the most common ones are asking you to act immediately before it’s too late (as you might get arrested, sued etc.), deals presented as limited time only or an urgent flash deal. Basically pressuring you into acting fast before you miss out. Scams use a sense of urgency to pressure you into either divulging your personal information or making fund transfers. They want you to react emotionally, instead of rationally. Instead of acting immediately, pause and think. Maybe even do a little bit of research. There is no need to act or decide immediately, as the only thing you might be missing out is being scammed. 4) They request for personal information Scammers are able to disguise themselves and create believable personas that will trick you into giving over sensitive personal and financial information, such as your PIN, OTP, account name and password. Scammers can disguise themselves as a government official or from a legitimate business, and there are scammers who impersonate your friends and family by taking over their accounts. 5) They tell you to pay in an unusual way For instance, they will ask you to pay via apple vouchers or through transfer services like oneyGram or Western Union. 6) They use threatening and aggressive language Along with urgency, scammers will also use threats to convince you to do what they say. Often, they will impersonate the police, FBI or tax collector, and threaten that you will be arrested. How To Avoid A Scam 1) Block Unwanted Calls & Messages. Do not reply to these unwanted calls and messages. 2) Never Give Personal and/or Financial Information To An Unexpected Request. Usually businesses and government agencies will not call, text or email you to ask for your sensitive personal information such as your bank account number, accounts, credit card numbers, PIN, your NRIC etc. 3) Do Not Panic, & Don’t Act Immediately (Resist it!). Businesses will give you time to make a decision. Anyone who pressures you to give them your sensitive personal information or to pay are scammers! 4) Always Tell Someone For Further Clarification. Before any action is taken, it is best to tell someone (e.g. family, friend, neighbour) about what happened. 5) If Unsure, Call NCPC Anti-Scam Hotline at 1800-722-6688. In Singapore, if you have any doubts or suspicions about a potential scam, you can seek a second opinion with the National Crime Prevention Council (NCPC) Anti-Scam hotline via calling them or by checking their website for further information. *This is only valid in Singapore. Conclusion In a digital world teeming with opportunities and pitfalls, our vigilance becomes the shield that guards against deception. By recognizing the subtle signs of scams and maintaining cyber hygiene, we fortify ourselves against malicious intentions. Let us navigate the online realm with discernment and wisdom, ensuring our digital lives remain secure and thriving. In the face of scams, knowledge is not just power—it's our strongest defence. Stay informed, stay safe, and together we can unmask deception. Related Topics A Personal Cybersecurity Checklist - How Cyber Secure Are You? 12 Tips For A Safer Online Shopping: How To Avoid Falling For Online Shopping Scams Password Security Tips: How To Fortify Your Password Security What is Multi-Factor Authentication (MFA) & Why Does It Matters?
Back to Blog
Last week, breaches and cyberattacks occurred across several industries from the public sector, apparel, financial, to the higher education industry. Devastating consequences have been uncovered from earlier data breaches and attacks, with millions of individual's personal data stolen and outages of systems persists disrupting services to customers. Furthermore, new vulnerabilities and patches have also been found and released. It is highly recommended to not only be aware of them but to also update them as soon as possible.
Read on to receive a quick summary of what happened this week in the space of cybersecurity. Majorca City Calvià hit by ransomware attack: Extorted for $11 million by cybercriminals. The Calvià City Council in Majorca announced that they were targeted by a ransomware attack last Saturday, which hit their systems, forcing the council to form a crisis committee to evaluate the damage done and formulate mitigation measures. The City Council is working to restore their systems as soon as possible, and the mayor Juan Antonio Amengual stated that a team of IT specialists are investigating the attack to estimate the extent of unauthorised access and to recover the impacted systems and services. The IT outages caused the City to suspend any administrative deadline for submitting allegations, requests etc. till 31 January. However, citizens who need to urgently submit any document for registration can still do so through the General State Administration portal. The announcement also stated that citizen services can also still be reached via the phone, and that telephone and face-to-face communication is maintained normally. A local media outlet has learned that the ransom set by the cybercriminals is €10,000,000 or approximately $11M. The mayor has told the local press that the municipality would not be paying the ransom. VF Corp, Supreme and Vans owner, states 35 million customers’ personal data were stolen. VF Corp, the parent company of Supreme, Vans, and The North Face, stated on Thursday that 35.5 million customers’ personal data were stolen by hackers in the December cyberattack. The company reported the data breach to regulators in a filing on Thursday. However, the filing did not specifically state the kinds of personal data stolen, or if the company yet knows what was stolen. VF Corp did state they do not retain customers’ social security numbers, bank account information, or payment card information. Furthermore, the company also stated that they did not find evidence of customers’ passwords being stolen. Canterbury, Dover and Thanet Councils in Kent hit by simultaneous cyberattacks. 3 local authorities in Kent - Canterbury City Council, Dover District Council, and Thanet District Council - have been hit by near-simultaneous cyberattacks, knocking multiple public-facing systems offline. All 3 authorities are working with the National Cyber Security Centre (NCSC) on incident response and remediation. For Canterbury, services including their planning department, online forms and maps have been taken offline. Meanwhile, Dover residents have lost access to online forms, and Thanet also appears to have lost its planning department and online forms. In a coordinated statement, Canterbury and Dover councils stated they are taking a precautionary approach and are investigating the incident. They will provide updates as soon as possible. A spokesperson for Thanet Council told reporters that they had proactively limited access to their online systems following reports of an incident. Several Swiss federal government websites were temporarily down after a cyberattack. On 17 January 2024, several federal government websites were temporarily down after a cyberattack. The attack was claimed by a pro-Russian group ‘NoName’, and they cited the presence of Volodymyr Zelensky at the World Economics Forum in Davos as the reason for the attack. According to the NCSC, the group launched a DDoS attack, which sends a high volume of requests to online services to overload them, making websites unavailable. In a press release, NCSC stated that the attack was promptly detected, and the Federal Administration's specialists took action to quickly restore access to the websites. LoanDepot outage continues into the 2nd week after ransomware attack. LoanDepot customers say that they have been unable to make mortgage payments or access their online accounts after a suspected ransomware attack on LoanDepot last week. On social media and forums, customers say they have struggled to access their account information or submit payments. Some even say that they have been unable to close deals during the ongoing disruption at LoanDepot, while others were able to do so on the phone with the company. LoanDepot’s cyber incident page states that several LoanDepot customer portals returned online as of 19 January 2024, although with limited functionality. Payoneer accounts in Argentina were hacked and users had their funds stolen. Starting last weekend, many Payoneer, a financial services platform providing online money transfer and digital payment services, users in Argentina reported that they lost access to their accounts or logged in to empty wallets - losing from $5000 to $60,000. The hackers were able to bypass 2FA which the accounts were protected by. The users report that right before the incident, they would receive an SMS requesting approval from a password reset on Payoneer, which they did not grant. Many stated that they did not click on the URLs, and some even claimed that they did not see the SMS until after their accounts were hacked. Many impacted users said that their stolen funds were sent to an unknown email address at the 163.com domain. Local journalists have found that most affected users were customers of the mobile service providers Movistar and Tuenti, with the majority using Movistar. This raised suspicions that the recent Movistar data leak may be behind the accounts hacked, however the leak did not expose users’ email addresses which are required for Payoneer users to reset their passwords. An official statement from Movistar simply states that they are not responsible for messages sent through its network. However, they have taken preventative measures with those numbers used in the smishing campaign. Payoneer also released a statement stating that they are aware of the hack which impacted “a very limited number of customers”. In the statement, Payoneer placed the blame on the users, alleging that those impacted clicked on the fake links and shared their account login information. However, many affected users state they did not click on phishing links, and accused Payoneer of attempting to deflect responsibility and failing to acknowledge a potential error or vulnerability within the platform. The company also stated that they are currently working with relevant authorities on this incident, and took swift action to contain the attempts at fraud from spreading. Kansas State University(K-State) hit by a cyberattack: IT network and services disrupted. K-State announced on Tuesday that they were experiencing disruption in some IT systems such as VPN, K-State Today emails, and video services on Canvas and Mediasite. By the afternoon, they confirmed that a cyberattack caused the disruption. Impacted systems were immediately taken offline once the attack was detected. This resulted in VPN, emails, Canvas and Mediasite videos, printing, shared drives, and mailing list management services (Listservs) being unavailable. K-State has engaged with 3rd party IT forensic experts to assist them in ongoing investigation, and have provided guidance to academic deans to maintain educational continuity - this includes using alternative resources. On 17 January, another status update was published, which informs that email services for K-State Today, which delivers daily announcements and research news, will become available starting on 18 January. However, the service will resume in a temporary format that features a different header image and a lower volume with select content. A 48-hour delay in the email delivery is also to be expected. On 18 January, it was updated that KSU Wireless is currently unavailable, and recommended to use KSU Guest during this time. On 19 January, the University stated that they will be working on the IT disruption this weekend, and ask students and staff to be vigilant against possible phishing attempts. Microsoft ‘senior leadership’ emails suffered a cyberattack from the same Russian SolarWinds hackers. Microsoft revealed on 20 January 2024 that they discovered a ‘nation-state attack’ on their corporate systems from the Russian SolarWinds hackers known as Nobelium. They were able to access email accounts of some memberships of their senior leadership team late last year. In the beginning of late November 2023, the hackers used a password spray attack to compromise a legacy non-production test tenant account, which allowed them to access a very small percentage of Microsoft corporate email accounts. This included members of their senior leadership team and employees in their cybersecurity, legal, and other functions. The hackers were able to exfiltrate some emails and attached documents. Microsoft discovered the attack on 12 January, and has not yet disclosed how long the attackers were able to access their systems. Ivanti VPN zero-day flaws being mass-exploited by hackers. 2 critical zero-day vulnerabilities (CVE-2023-46805 and CVE-2024-21887) in Invanti’s corporate VPN appliance are being mass-exploited by malicious hackers. Volexity, which previously reported that the 2 unpatched flaws in Ivanti Connect Secure, are being exploited by China state-backed hackers, now say that there is evidence of mass exploitation. According to Volexity, more than 1,700 Ivanti Connect Secure appliances worldwide have been exploited so far - this affects organisations in the aerospace, banking, defence, government and telecommunications industries. Volexity stated that victims are globally distributed, and vary in sizes (from small to some of the largest organisations in the world). It was also stated that Ivanti VPN appliances were “indiscriminately targeted”. However, Volexity notes that the number of compromised organisations are likely to be far higher. In Ivanti’s updated advisory on Tuesday, they confirmed that their findings are consistent with Volexity’s new observations, and that the mass-hacks appear to have started on 11 January, a day after Ivanti disclosed the vulnerabilities. Despite mass exploitation, Ivanti has yet to publish patches. They plan to release fixes on a staggered basis starting 22 January. For this while, admins are highly advised to apply the provided mitigation measures on all affected VPN appliances on their network - such as resetting passwords and API keys, and revoking and reissuing any certificates stored on the affected appliances. VMware confirms a critical vCenter flaw is being exploited in attacks. VMware confirmed that a critical vCenter Server remote code execution vulnerability (CVE-2023-34048) that was patched in October is now under active exploitation. The vulnerability was reported by Grigory Dorodnov, a Trend Micro vulnerability researcher. According to Shodan data, more than 2000 VMware Center servers are currently exposed online, potentially vulnerable to attacks and exposing corporate networks to breach risks given their vSphere management role. As there is no workaround, VMware urged admins who are unable to patch their servers to strictly control network perimeter access to all vSphere management components (e.g. storage and network components). The specific network ports linked to potential exploitation in attacks are 2012/tcp, 2014/tcp, and 2020/tcp. Google releases security updates to fix the first actively exploited Chrome zero-day vulnerability of 2024. On Tuesday Google published a security advisory stating that they are aware of reports that a zero-day vulnerability (CVE-2024-0519) is being exploited in the wild. This high severity zero-day vulnerability is due to a high severity out-of-bounds memory access weakness in the Chrome V8 JavaScript engine. This can allow attackers to gain access to data beyond the memory buffer, thus providing them access to sensitive information or triggering a crash. Furthermore, this zero-day can bypass protection mechanisms to make it easier to achieve code execution via another weakness. The company fixed the zero-day for users in the Stable Desktop channel, with patched versions being released globally to Windows (120.0.6099.224/225), Mac (120.0.6099.234), and Linux (120.0.6099.224) users. Those who prefer not to update their web browser manually can rely on Chrome to automatically check for new updates and install them after the next launch. Today, Google also patched V8 out-of-bounds write (CVE-2024-0517) and type confusion (CVE-2024-0518) flaws, allowing for arbitrary code execution on compromised devices. That is all! Enjoy the rest of the week and don't forget to update your devices and systems to the latest patches!
Back to Blog
Last week, breaches and cyberattacks occurred across several industries from the public sector, clothing, electronic manufacturing, tourism, banking, mortgage to the healthcare industry. Devastating consequences have been uncovered from earlier data breaches and attacks, with millions of individual's personal data exposed. Furthermore, new vulnerabilities and patches have also been found and released. It is highly recommended to not only be aware of them but to also update them as soon as possible.
Read on to receive a quick summary of what happened this week in the space of cybersecurity. Halara investigates a breach after data of 950,000 customers was leaked. Halara, a popular Hong Kong athleisure clothing company, is investigating a potential data breach after the alleged data of almost 950,000 customers was leaked on a hacking forum. This comes after a person named ‘Sanggiero’ claimed to have breached Halara earlier this month, and shared a text file that contains the stolen customer data on a hacking forum and a Telegram channel. Over 1 million rows of data from Halara was posted. The data posted contained a unique address id, full names, phone numbers, country, home address, zip, province, city, and iso. BleepingComputer reviewed the leaked data, they found that the text file only contains 941,910 records. Although BleepingComputer has not been able to confirm if all the data is accurate, however they did contact multiple people listed in the file, and confirmed that they are all Halara customers, and that their listed names, phone numbers, and addresses are accurate. Sanggerio stated that data was stolen via exploiting a bug in an API on Halara’s website, which is still unfixed. Sanggiero stated they did not contact Halara and decided to release the stolen data for free as selling it would not have a lot of value. Halara customers should be vigilant against targeted SMS phishing that will attempt to steal other personal info such as passwords. Framework discloses data breach after its accounting service provider fell victim to a phishing attack. Framework Computer, a laptop computer manufacturer, disclosed a data breach that exposed the personal information of an undisclosed number of customers after their accounting service provider, Keating Consulting Group, fell victim to a phishing attack. The company stated in a data breach notification letters sent to affected individuals, that an accountant from Keating Consulting Group was tricked on 11 January by a threat actor impersonating Framework’s CEO into sharing a spreadsheet that contains customers’ personally identifiable information (PII) that is “associated with outstanding balances for Framework purchases”. Exposed PII includes full name, email address and balance owed. The company also warned affected customers of phishing attacks, and stated that they only send emails from ‘support@frame.work’ for customers to update their information when a payment has failed, and will never ask for payment information via email. Customers are highly encouraged to contact the company’s support team if they receive any suspicious emails. HMG Healthcare hit by data breach: Data from 40 nursing facilities compromised. HMG Healthcare, a Texas-based healthcare services provider, was hit by a cyberattack on their server that led to data from residents and employees across 40 nursing facilities being compromised. The hackers were able to exfiltrate unencrypted files that contain personal information. Personal information compromised includes individuals’ names, birthdates, social security numbers, contact details, employee records, and medical treatment information. HMG has not disclosed the nature of the attack nor the number of people affected by the breach, but did dismiss the possibility of further compromise. As stated by the health provider, they “worked diligently to ensure that the stolen files were not further shared by the hackers to other sources.” HMG highly recommends affected individuals to be vigilant of any suspicious activity in their credit reports and account statements. Inspiring Vacations, an Australian travel agency, hit by data breach: More than 112k records such as passport and travel details exposed. Inspiring Vacations, an Australian travel agency, has fallen victim to a data breach. It has resulted in thousands of customers’ passports and travel details being compromised. Jeremiah Fowler, a cybersecurity researcher that discovered the data breach, reported that the publicly exposed database totaled 112,605 records and 28.6 GB in size. The exposed database includes high-resolution passport images, travel visa certificates, and itineraries or ticket files.Majority of the affected individuals in this data breach are Australian citizens, however identification documents from New Zealand, the United Kingdom and Ireland were also present. There are an estimated 1,000 identification documents in a limited sample, along with additional files that contain passport numbers, and other personally identifiable information. Notably, passport document names included individuals’ names in plain text. Furthermore, the breach revealed 48 spreadsheets that had information of about 13,684 customers. The exposed information includes travellers’ names, email addresses, trip costs, destinations, and internal details. To add on, approximately 24,000 itinerary and e-ticket pdf documents were exposed, some even displaying partial credit card numbers.The database also had internal documents - 17,000 tax invoices to partners and affiliates specifying gross costs and commissions paid. Oregon Pacific Bank hit by data breach: Consumers’ sensitive information compromised. Oregon Pacific Bank (OPB), a financial institution based out of Florence, Oregon, filed a notice of data breach with the Attorney General of Oregon after they discovered that an unauthorised party accessed consumers’ sensitive information. Upon discovery of this data breach, OPB conducted an investigation to determine the type of information, and which consumers were impacted. However, OPB did not state the specific data types that were compromised. OPB has begun to send out data breach notification letters to all individuals affected by this data breach. Hathway suffers from alleged massive data breach: 41.5 million customers exposed. Hathway, one of India’s largest Internet Service Providers (ISP) and cable television operators, was hit by a data breach which occurred in December 2023. The hacker called ‘dawnofdevil’ claimed responsibility for the breach. The hacker stated that a vulnerability in the Laravel framework application, the content management system used allowed them to compromise the company’s data. According to the hacker’s message, the Hathway data leak exposes over 41.5 million customers’ sensitive information. The exposed data includes names, email addresses, phone numbers, physical addresses, and other personally identifiable information. The hacker claims that 200+ GB of data has been dumped, which comprises 739 CSV files. Swiss Air Force hit by cyberattack: Documents leaked on the darknet. A US security company that provides communication technology to defence firms globally, fell victim to a cyberattack. Switzerland’s Federal Department of Defence officially confirmed that the Swiss Air Force was affected by the breach, and is currently investigating the incident. Hackers are believed to have stolen thousands of documents from the US security company. Around 30GB of partly sensitive and classified documents are believed to have ended up on the darknet, and hence are accessible to the public. The leaked documents include a contract between the Swiss Department of Defence and the US company for almost US$5 million, as well as emails and payment receipts that show when the transactions took place. Fidelity National Financial (FNF) confirmed November cyberattack exposed 1.3 million customers’ data. FNF, an American provider of title insurance and settlement services to the real estate and mortgage industries, confirmed that a November cyberattack, which has been claimed by the BlackCat ransomware gang, has exposed 1.3 million customers’ data. FNF confirmed this in an amended SEC Form 8-K filing, and confirmed that the cyberattack was successfully contained 7 days later. According to the filing, the attackers used a non-propagating malware that could exfiltrate data from the breached systems. The company is providing credit monitoring, web monitoring and identity theft restoration services to affected customers. The filing also clarified that the breach was contained on FNF systems, and the attack was not extended to any of the connected customer-owned systems. loanDepot, a U.S. mortgage lender, confirmed ransomware attack that disrupted operations. loanDepot confirmed on 8 January that the cyber incident they experienced over the weekend was a ransomware attack that led to data encryption. Customers started to encounter into issues on Saturday when trying to log into loanDepot’s payment portal or when trying to contact them via phone. Due to the attack, loanDepot had to take certain systems offline to block the attackers’a access to other devices on its network, and that they are investigating to understand the extent of the attack, and taking measures to minimise the impact. From their investigation so far, they found that the attackers had accessed some of their systems and encrypted files. The company also notified relevant authorities of the incident. Using social media, the company informed customers that recurring automatic payments would still be processed, although delayed before they appear in the payment history. However, making new payments via the servicing portal will not be possible, and advised affected customers to reach out to the call center for assistance. As ransomware gangs tend to steal corporate and customer data during breaches, it is highly recommended that customers of loanDepot to be vigilant against phishing attacks and identity theft attempts. Toronto Zoo hit by ransomware attack. Toronto Zoo, the largest zoo in Canada, stated that a ransomware attack had hit their systems, but had no impact on the animals, their website, or their day-to-day operations. The zoo stated that they do not store credit card information, and are investigating whether the attack affected their guests’, members’ or donors’ records. The attack has been reported to relevant authorityies, and the zoo is working with 3rd party cybersecurity experts, and the City of Tornonto’s Chief Information Security Office to determine the extent of the damage. 2 vulnerabilities in a plugin that are used on 150k WordPress sites can help attackers take control of sites. There are 2 vulnerabilities (CVE-2023-6875 & CVE-2023-7027) that impact the POST SMTP Mailer WordPress plugin, an email delivery tool used by 300,000 websites. These vulnerabilities can help attackers take complete control of a site authentication. CVE-2023-6875 is a critical authorisation bypass flaw, and this impacts all versions of the plugin up to 2.8.7. This vulnerability can be exploited to reset the API key and view sensitive log information, this includes password reset emails. CVE-2023-7027 is a cross-site scripting problem, and impacts all versions of the plugin up to 2.8.7. This vulnerability could let attackers inject arbitrary scripts into web pages of the affected site. On 1 January 2024, the plugin vendor published version 2.8.8 that includes security fixes for both issues. However, based on statistics, there are roughly 150,000 sites that still run a vulnerable version of the plugin. It is highly recommended to update to the latest version as soon as possible. Microsoft January 2024 Patch Tuesday fixes 49 flaws & 12 remote code execution vulnerabilities. 9 January 2024 was Microsoft’s January 2024 Patch Tuesday which includes security updates for 49 flaws and 12 remote code execution (RCE) vulnerabilities. 2 vulnerabilities were classified as critical, with one being a Windows Kerberos Security Feature Bypass and the other a Hyper-V RCE. The vulnerabilities include: 10 Elevation of Privilege Vulnerabilities, 7 Security Feature Bypass Vulnerabilities, 12 RCE Vulnerabilities, 11 Information Disclosure Vulnerabilities, 6 Denial of Service Vulnerabilities, 3 Spoofing Vulnerabilities. To access the full description of each vulnerability and the system it affects, you can view the report here. That is all! Enjoy the rest of the week and don't forget to update your devices and systems to the latest patches!
Back to Blog
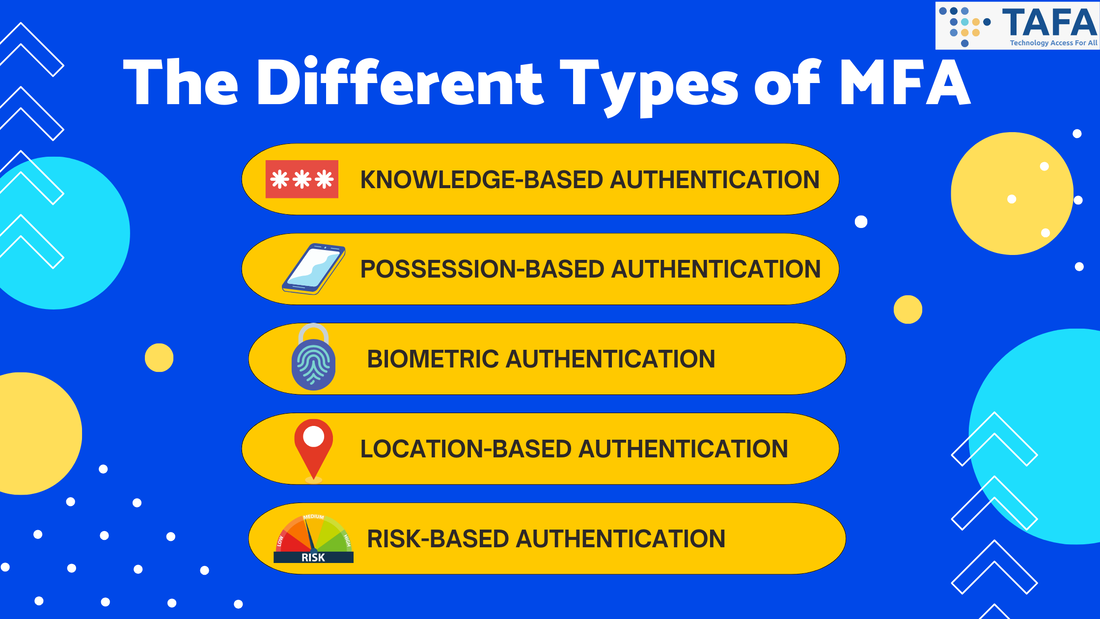
In a world where our lives are increasingly intertwined with the digital realm, fortifying our online presence has never been more critical. Passwords, once the stalwart guardians of our virtual kingdoms, are no longer enough to thwart the nefarious ambitions of cyber intruders. Enter Multi-Factor Authentication (MFA), a digital sentinel that provides an extra layer of protection. In this article, we unravel the mystery of MFA, illuminate its paramount importance in the modern era of cybersecurity, and provide instances of when the implementation of MFA is essential. What Is Multi-Factor Authentication (MFA)? MFA is a security measure that requires two or more verification vectors to gain access. MFA is a strong component of a strong identity and access management policy. Common examples of MFA include personal devices such as security tokens, biometrics, SMS authorisation codes and authenticator apps. By requiring one or more additional authentication vectors, this decreases the likelihood of a successful cyberattack. Most MFA authentication methodology is usually based on 1 of 3 types of additional information: something you know (like a password or PIN), something you have (like a mobile device), and something you are (biometrics like a fingerprint). Why Does MFA Matters? MFA helps you to escape from single-point vulnerability. Through the incorporation of various authentication factors, MFA mitigates the risk associated with a single compromised password. Especially now, authentication based on just your username and password is unreliable due to the fact how easily they can now be acquired by threat actors via hacking, phishing and malware. Furthermore, MFA is dynamic as it can adapt to evolving threats via offering a flexible security framework that remains robust against a plethora of attack vectors. The Different Types Of MFA
When Should I Use MFA? It is highly recommended to turn on MFA wherever possible, starting with very important accounts. Examples include:
Conclusion Multi-Factor Authentication stands as a sentinel guarding the gates to our digital lives. In this dynamic landscape of cyber threats, a single password is no longer sufficient to protect our valuable data. MFA, with its multifaceted approach, ensures that even if one defence falters, another stands strong. MFA is a necessity in fortifying our digital existence and standing firm against the tide of cyber threats. Remember, in the world of cybersecurity, it’s not just about having the key; it’s about having the right combination to unlock the future securely. Related Topics A Personal Cybersecurity Checklist - How Cyber Secure Are You? 12 Tips For A Safer Online Shopping: How To Avoid Falling For Online Shopping Scams Password Security Tips: How To Fortify Your Password Security What to Do When You've Fallen for a Phishing Scam The Risks of Public Wi-Fi & Tips On How To Stay Safe Is This QR Code Safe? Top Tips to Ensure Your QR Scans are Secure
Back to Blog
Last week, breaches and cyberattacks occurred across several industries from the legal, information technology, telecommunications to the healthcare industry. Devastating consequences have been uncovered from earlier data breaches and attacks, with millions of individual's personal data compromised, services still remain disrupted, and core systems and networks being completely wiped out causing millions without an internet connection. Additionally, 23andMe are under hot waters for victim blaming and hackers are increasingly targeting government and business profiles on X for crypto scam.
Read on to receive a quick summary of what happened this week in the space of cybersecurity. 23andMe deflects: Tells data breach victims that they are at fault for the breach. According to a letter sent to a group of victims, 23andMe is blaming victims in an attempt to absolve itself from any responsibility. 23andMe stated that “users negligently recycled and failed to update their passwords following these past security incidents, which are unrelated to 23andMe.” Hence, this breach “was not a result of 23andMe’s alleged failure to maintain reasonable security measures”. As stated by Hassan Zavareei, one of the lawyers representing the victims, 23andMe are “downplaying the seriousness of these events”. Hackers were able to break into the first set of victims (14,000 of them) via credential stuffing, whereby they brute-force into accounts with passwords used by victims before. However, the hackers were then able to access the personal data of another 6.9 million victims from this initial set of victims, as they had opted-in to 23andMe’s DNA Relatives feature. In short, the hackers were able to scrape the personal data of another 6.9 million customers whose accounts were not directly hacked. As Zavareei stated the breach “impacted millions of customers whose data was exposed through the DNA Relatives feature on 23andMe’s platform, not because they used recycled passwords.” HealthEC LLC, a healthcare tech firm data breach impacts 4.5 million patients. HealthEC LLC, a provider of healthcare management solutions, suffered a data breach that impacted 4,452,782 individuals who received care through one of the company’s customers. On 22 December, the company disclosed that they suffered a data breach between 14-23 July 2023, which resulted in unauthorised access to some of their systems. Stolen personal information includes affected individuals’ name, address, birthdate, social security number, taxpayer identification number, medical record number, medical information (e.g. diagnosis, diagnosis code, mental/physical condition, prescription information, and provider’s name and location), health insurance information (e.g. Medicaid/Medicare identification, beneficiary number, subscriber number), and billing and claims information (e.g. patient account number, patient identification number, and treatment cost information). In total, there are 17 healthcare service providers and state-level health systems that were impacted by the cyberattack on HealthEC. The company has also recommended impacted individuals to remain vigilant, and to report any suspicious activities to relevant parties such as financial institutions, the healthcare provider, and insurance company. Orrick Herrington & Sutcliffe, a law firm that handles data breaches, was hit by a data breach. Orrick Herrington & Sutcliffe, a law firm that works with companies affected by security incidents, suffered a cyberattack whereby hackers stole the personal information and sensitive health data of more than 637,000 data breach victims. The law firm stated the sensitive information was stolen from a file share on their network during an intrusion in March 2023. In a series of data breach notification letters sent to affected individuals, the law firm states that the breach of its systems involved its clients’ data, including individuals who had vision plans with insurance giant EyeMed Vision Care and those who had dental plans with Delta Dental. The firm also notified health insurance company MultiPlan, behavioural health giant Beacon Health Options and the U.S. Small Business Administration. The stolen data includes affected individuals’ names, birth dates, postal addresses, email addresses, and government-issued identification numbers (e.g. social security numbers, passport numbers, driver licence numbers, tax identification numbers). Stolen data also includes medical treatment and diagnosis information, insurance claims information, healthcare insurance numbers, and provider details. Furthermore, the law firm also states that the breach includes online account credentials and credit or debit card numbers. Xerox confirms subsidiary XBS U.S. was data breach following ransomware attack. Over the weekend, Xerox, a printing solutions giant, confirmed that their US-based subsidiary Xerox Business Solutions (XBS) experienced a data breach. The company states that this breach was limited to XBS U.S. and was contained by their cybersecurity team. In an incident notice published on their website, it was stated that based on their preliminary investigation, “limited personal information in the XBS environment may have been affected.” As per their policy, they will be notifying all affected individuals. Although Xerox did not share on the type of cybersecurity incident XBS U.S. fell victim to, Inc Ransom, a ransomware gang, claimed responsibility for the attack. On 30 December, Inc Ransom listed Xerox on its Tor-based leak site, and as proof of the attack, posted screenshots of documents that they allegedly stole from the company. However, since then, the entry has been taken down. This could suggest that Xerox may have engaged in communication with the ransomware group to prevent the stolen data from being published online. Australia Victoria Court recordings exposed after suffering a cybersecurity incident in December. Australia’s Court Services Victoria (CSV) warned that video recordings of court hearings were exposed after a December cybersecurity incident. In a statement, CSV stated that the cybersecurity incident led to unauthorised access that caused disruption of the audio visual in-court technology network, impacting video recording, audio recordings and transcription services. Recording of some hearings in courts between 1 November and 21 December 2023 may have been accessed. It is also possible that some hearing before 1 November 2023 may also be accessed. CSV also stated that they immediately took action to isolate and disable the affected network, and put in place arrangements to ensure continued operations across the courts. CSV has notified the relevant authorities, and are working with authorities and cybersecurity experts to investigate this incident. Although CSV did not specify who is behind the attack, based on sources speaking to ABC news, it was reported that the Qilin ransomware group is behind the hack. Five Guys to pay $700,000 to settle a proposed class-action lawsuit over 2022 data breach. Five Guys Enterprises LLC will pay $700,000 to settle a proposed class-action alleging that they failed to protect the personal information of nearly 38,000 employees and others that was exposed in a September 2022 data breach. The settlement fund will cover benefits to class members, up to $251,000 in attorneys’ fees and costs, service awards of $2500 to 4 class representatives and the cost of administering the settlement. Class members could receive up to $400 for ordinary out-of-pocket losses and lost time related to the breach. Those with extraordinary losses would be eligible for up to $6500 in additional payments. The deal also provides for an alternative cash payment of $150 in lieu of other claims, a payment of $100 for California class members, and 2 years of identity theft protection and credit monitoring services. A final approval hearing has been set for 12 July. All systems on KyivStar, Ukraine’s largest telecommunications service provider, were wiped by Russian hackers. KyivStar had all their systems on the telecom operator’s core network wiped in a December breach. After the incident, Kyivstar’s mobile and data services were down, leaving most of their 25 million mobile and home internet subscribers without an internet connection. Illia Vitiuk, head of the Security Service of Ukraine’s cybersecurity department, told Reuters that the threat actors breached Kyivstars’ network in May 2023. However, only launched the attack months later which “completely” destroyed “the core” of the telecoms operator, and wiped thousands of virtual servers and computers. Following the incident, Kyivstar’s CEO and the SSU suggested that Russian hackers may have been involved. A day later, the attack was claimed by Russian hackers from the Solntsepek group (believed to be linked to the Sandworm Russian military hacking group). They claimed that they wiped 10,000 computers, thousands of servers on Kyivstar’s network, and all cloud storage and backup servers. Memorial University continues to deal with cyberattack aftereffects - delays semester starts. The Memorial University of Newfoundland (MUN), the largest public university in Atlantic Canada, continues to deal with the effects of a December cyberattack and had to postpone the start of classes in one campus. On 29 December, the university detected a cyberattack and activated security protocols to isolate impacted systems and launched an investigation. The university announced on 2 January that the services at the Marine Institute campus have been restored. For the Grenfell campus, the start to the semester was postponed until 4-8 January. Additional specialists from other campuses are supporting Grenfell’s IT team to expedite the system restoration process. In a 4 January update, the university announced that the internet and WiFi for resident students are still not operational. Furthermore, payment terminals for credit and debit card transactions are also not working. According to the university, there is no indication that the cyberattack has impacted systems or data on other campuses. Hackers increasingly target government and business profiles on X for crypto scam. Hackers are increasingly targeting verified accounts on X that belong to government and business profiles on X that are marked with ‘gold’ and ‘grey’ checkmarks to promote crypto scams, phishing sites, and sites with crypto drainers. A recent high-profile case is that Mandiant’s, a cybersecurity firm and a Google subsidiary, X account was hijacked to distribute a fake airdrop that emptied cryptocurrency wallets. MalwareHunterTeam has been tracking this type of activity on X and reported several notable examples of compromised “gold” and “grey” accounts. For instance, the account of Amina Gerba, a Canadian senator, has been renamed and is being used to spread a scam. A recent report from CloudSEK, a digital risk monitoring platform, highlights the growing of a new black market whereby hackers sell compromised gold and grey X accounts for prices between $1,200 and $2,200. CloudSEK says they observed 6 sales of such accounts in a month. One of them, dormant since 2016 and had 28,000 followers, was advertised for $2500. Researchers recommend companies to close dormant accounts that are inactive for a long period, review their security settings, and activate 2-factor authentication. That is all! Enjoy the rest of the week and don't forget to update your devices and systems to the latest patches!
Back to Blog
Last week has been relatively quiet as compared to the previous weeks. There was not much news released related to breaches and cyberattacks. Although, there were still attacks that occurred such as the ones against Yakult Australia, Ohio Lottery, libraries, Sabah government etc . Devastating consequences have also been disclosed from earlier data breaches whereby millions of people’s personal information have been compromised, and even victims being sent extortion threats from the attackers. Read on to receive a quick summary of what happened this week in the space of cybersecurity. LoanCare notifying more than 1.3 million individuals of a data breach that impacts their personal information. LoanCare, a mortgage servicing firm that is a subsidiary of Fidelity National Financial (FNF), has started informing more than 1.3 million individuals of a data breach that impacts their personal information. In a notification letter, the company stated that the data breach occurred due to a cyberattack on FNF’s internal systems. LoanCare also stated that the attackers had exfiltrated data from FNF’s systems, including personal data such as names, addresses, social security numbers and loan numbers. It was also further stated that FNF has started an investigation, notified relevant authorities and also taken precautionary measures to assess and contain the incident. The company said that as of now, there is no evidence that the stolen personal information has been used fraudulently. However, free identity monitoring services are provided to impacted customers. Panasonic reports data breach that compromised personal and health information after December 2022 cyberattack. Panasonic Avionics Corporation, a leading supplier of in-flight communications and entertainment systems, disclosed a data breach that affects an undisclosed number of individuals after their corporate network was breached in December 2022. In the statement filed with the Office of California's Attorney General, the company stated that they identified that some personal and health information was exposed during the incident, but has yet to find any evidence that the exposed information has been misused since the attack. Information impacted during the breach includes the affected individuals' names, birth dates, email addresses, mailing address, telephone number, medical and health insurance information, financial account numbers, company employment status, and government identifiers (e.g. social security number). The company stated that the impact of the incident is restricted to “a limited amount of employee and business customer data”. Panasonic will be providing 24 months of free identity and credit monitoring services to impacted individuals, and warn affected individuals to check the reports for signs of suspicious activity. EasyPark suffers a massive data breach: Millions of customers’ personal information may have been compromised. EasyPark, the largest parking app operator in Europe who also owns RingGo and ParkMobile, has been impacted by a data breach. As a result, the information of thousands of EasyPark Group clients in Europe has been stolen. EasyPark first found the vulnerability on 10 December, and notified the impacted customers immediately. In a press release, they also stated that the attack resulted in a breach of “non-sensitive customer data”. The press release also stated that customers do not need to take any actions, and just be aware of phishing attacks. Customers’ personal information exposed includes names, phone numbers, addresses, email addresses, and credit card numbers were purportedly stolen in the data breach. The company however did state that “a few digits of IBAN or credit card numbers” were compromised, however no combination could be utilised to make payments. EasyPark has notified multiple regulatory bodies of the cyberattack, and a thorough investigation of the breach is underway. National Amusements, an entertainment giant, discloses that more than 82,000 affected by the cyberattack. National Amusements, the company that owns Paramount movie studio, CBS, MTV, and thousands of movie theatres across the UK, U.S. and Latin America, disclosed that 82,128 people have been affected by a data breach. The company stated that they detected suspicious activity on their network last year on 15 December 2022. An investigation found that the attackers had access to files on the company's systems between 13-15 December. The information compromised includes names, financial account numbers, credit card numbers, debit card numbers, and PINs. In the breach notification letter, all affected customers will be given 1 year of free identity protection services. Yakult Australia confirms cyberattack after 95 GB data was leaked. In a statement, Yakult Australia has confirmed that they experienced a “cyber incident” whereby both the company's Australian and New Zealand IT systems have been affected. Cybercrime actor, DragonForce claimed responsibility for the attack, and has also leaked 95GB of the company’s data. According to DragonForce, the data dump contains the “company database, contracts, passports and much more”. From analysis of a small portion of the leaked data, it appears that several business documents, spreadsheets, credit applications made by Yakult Australia, employee records, and copies of identity documents such as passports were found. Yakult Australia stated that they first became aware of the incident on the morning of 15 December, and have yet to confirm the extent of the incident and how exactly the incident occurred. The company is currently working with cybersecurity experts to investigate the incident, and further updates will be provided as information becomes available. Although their offices in Australia and New Zealand were hit, offices in both regions will continue to remain open and operational. Yakult Australia has also notified all the relevant authorities. Kroll reveals personal information of FTX bankruptcy claimants exposed. Kroll has revealed that the personal information of FTX bankruptcy claimants have been exposed due to the August data breach. A letter was sent to affected customers that the personal information exposed included their names, email addresses, phone numbers, address, claim number, claim amount, FTX account ID and/or coin holdings and balances, and for some, their birth dates. Kroll stated that the data breach dfid not affect any FTX systems or FTX digital assets, and highlighted that Kroll does not maintain passwords to FTX accounts. In their statement, Kroll advised all affected customers to remain vigilant and take precautionary measures to protect their accounts. Kroll also warned affected customers of potential phishing attacks to gain unauthorised access to their cryptocurrency accounts and digital assets. Libraries in several Sydney suburbs hit by a cyberattack: Data of library users potentially exposed. Libraries in several Sydney suburbs have been hit by a cyberattack. Woollahra Council has been contacting residents in surrounding suburbs with library accounts to warn them that their data might be exposed. Multiple library functions have been disrupted after the attack was launched on the external software. This affects services in Double Bay, Paddington, and Watsons Bay. The software is used to manage bookings, issue fines, and grant computer access, and printing or scanning. An email sent to library users stated that the information stored in the affected software is limited to contact details only. This includes library users’ name, email address, mobile number, landline number and postal address. However, for a small number of customers, the compromised data also includes their encrypted passwords, and partial credit card payment details. It was stated that upon detection of the incident, the system was isolated to prevent further unauthorised access. Relevant authorities have also been notified. The spokesperson has also stated that the provider of the software has secured the system. As of now, the extent of the attack is currently unknown. East Malaysia Sabah government's website breached: 109 documents leaked. The Sabah government’s official website in East Malaysia faced a security breach on 22 December, with hackers purportedly extracting 109 files. The hackers stated that many of which were “classified documents or Excel tables that mention internal information”. As proof of the hack, sections of 3 government documents were posted: an internal memo from Sabah state library, a Sabah Finance Ministry letter to the Semporna district engineer, and a Kota Belud district officer’s letter to another state agency. The cybersecurity head at the Sabah Computer Services Department, Ebenezer Godomon, confirmed the breach, and also stated that a forensic investigation is underway to determine the extent of the breach. He states that they have traced the breach’s origin back to human error. He also stated that they have isolated the main source of the leakage, and are taking necessary actions to prevent future incidents. Integris Health hit by cyberattack: 2 million patients’ personal information compromised & hackers send extortion threats to patients. Integris Health was compromised by a cyberattack and had verified the breach on 28 November. This led to the personal information of more than 2 million patients being compromised. Since 24 December, hackers have been sending extortion threat emails to patients, which threatens patients that they will sell their stolen data to other threat actors if they do not pay $50 to delete their data by 5 January 2024. Inside the emails is a link to a dark web page where the stolen data, includes patients’ names, social security numbers, birth dates, information about hospital visits, and more. The list has about 4,674,000 people. In a data privacy notice, Integris Health advised patients to not reply to the hackers or follow any instruction found in the extortion emails. Ohio Lottery hit by cyberattack. The DragonForce ransomware group claimed responsibility. The Ohio Lottery was forced to shut down some key systems after a cyberattack affected some of their internal applications on Christmas Eve. Investigation is currently underway, and the lottery is working to restore all impacted services. In a press release, the lottery stated that mobile cashing and prize cashing above $599 at Super Retailers are not available. Instead, those over $600 must be mailed to the Ohio Lottery Central Office or claimed using the digital claim form. Furthermore, winning numbers for KENO, Lucky One and EZPLAY Progressive Jackpots are not available on their website or mobile app. Although customers can check them at any Ohio Lottery Retailer. The attack has been claimed by the DragonForce ransomware gang. They claimed to have encrypted devices and stolen data during the attack. From their data leak site, their posts also suggest that the allegedly stolen files contain information that belongs to more than 3 million Ohio Lottery customers and employees. Stolen data includes full names, mail, addresses, winning amounts, social security numbers and birth dates. That is all! Enjoy the rest of the week and don't forget to update your devices and systems to the latest patches! |
|
© 2021, TAFA HOLDINGS (S) PTE LTD. ALL RIGHTS RESERVED
|

 RSS Feed
RSS Feed