|
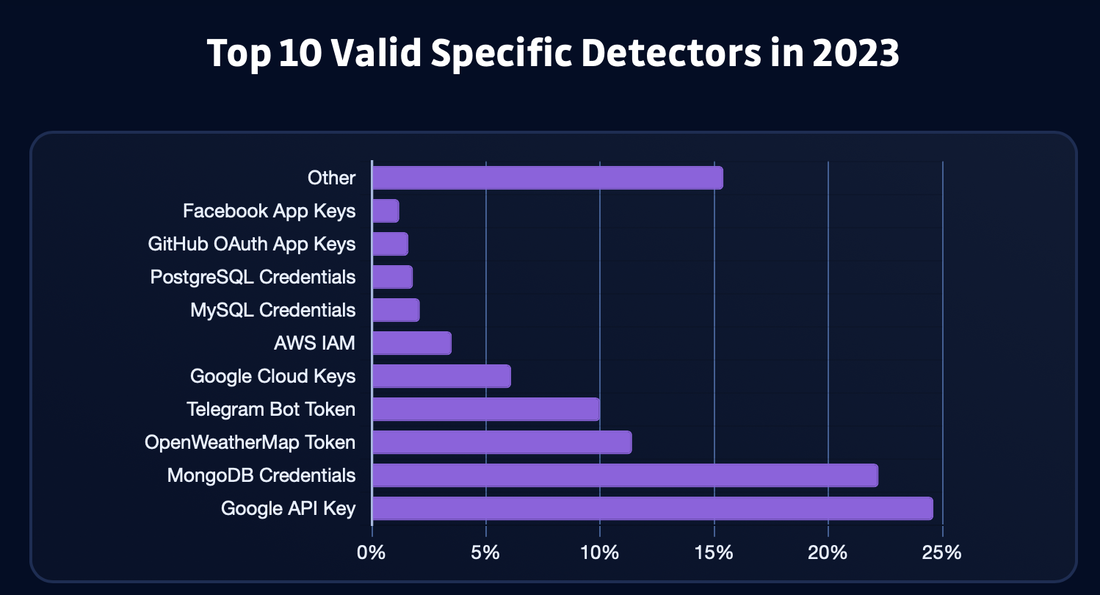
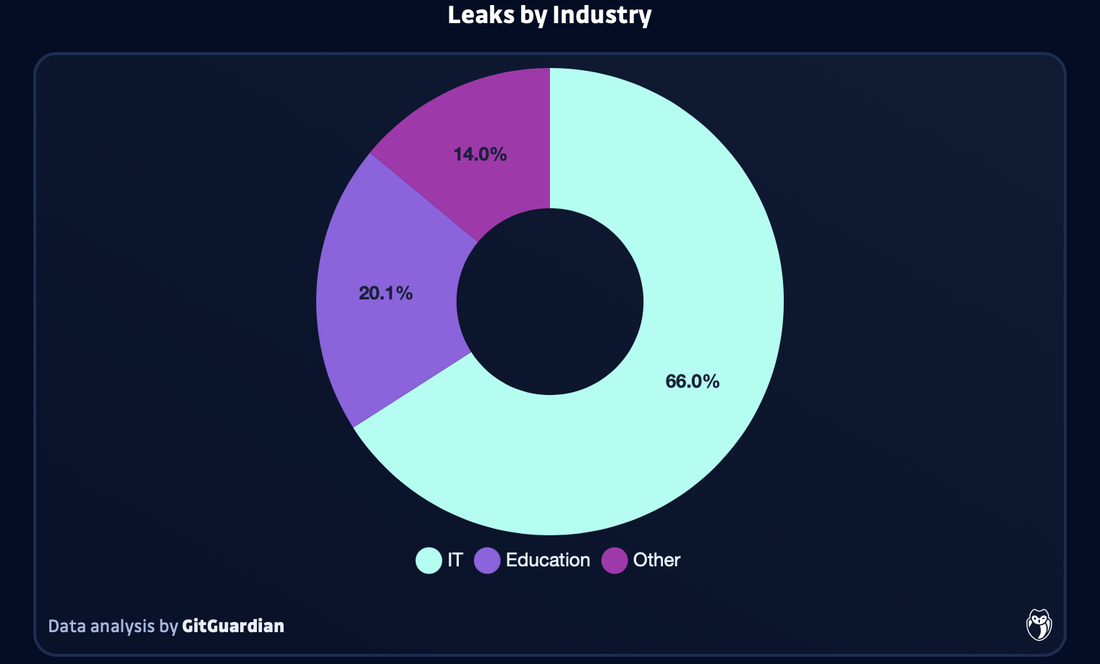
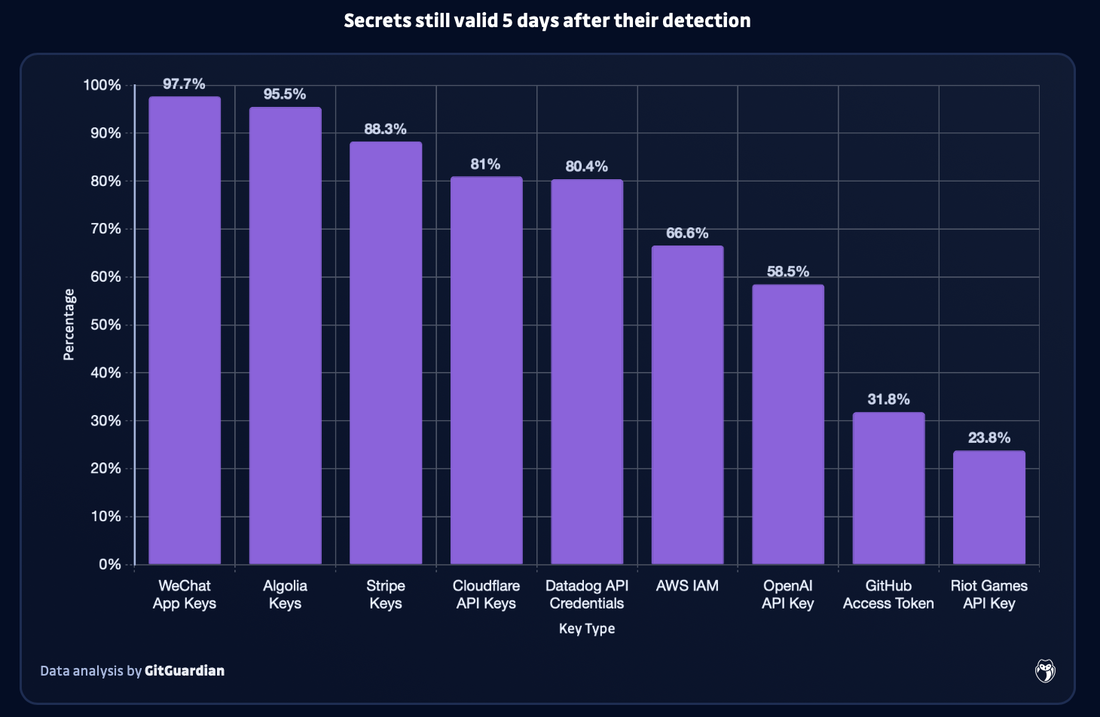
In the digital age, the protection of sensitive information is paramount. However, GitGuardian found that in 2023, GitHub users accidentally exposed 12.8 million authentication and sensitive secrets in over 3 million public repositories, with the vast majority of these secrets being still valid after 5 days. This incident serves as a stark reminder of the importance of robust cybersecurity measures and the need for increased vigilance. Join us as we delve into the details of this significant data breach, its implications for cybersecurity, and steps individuals and organisations can take to protect themselves... GitHub Leak: Unveiling the Scope In 2023, the number of authentication and sensitive secrets leaked on GitHub was 12.8 million. This is a 28% increase as compared to the previous year (10 million in 2022). Unfortunately, this is not surprising due to hard-coded credentials have always been one of the primary causes of security incidents in the software world. This is being exacerbated with the increasing complexity of digital supply chains. For instance, Sophos 2023 Report found that in 2023 compromised credentials was the top root cause of attacks for the first time. It was found that in the first half of the year, compromised credentials accounted for 50% of root causes, followed by vulnerability at 23%. What was Leaked The exposed secrets include account passwords, API keys, TLS/SSL certificates, encryption keys, cloud service credentials, OAuth tokens, as well as other sensitive data that could give external actors unlimited access to a range of private resources and services. All of this can lead to data breaches and financial damage. In 2023 alone, over 1 million valid occurrences of Google API secrets, 250,000 Google Cloud secrets, and 140,000 AWS secrets were detected.The reasoning for this is that there has been an increase in the number of code repositories on Github, with a 22% increase (50 million) in new repositories added in the past year. Therefore, this enhances the risk of accidental and deliberate exposure of sensitive information. Countries with the Most Leaks The top 10 countries with the most leaks are India, United States, Brazil, China, France, Canada, Vietnam, Indonesia, S.Korea and Germany. Sectors with the Most Leaks The most affected sector was the IT sector (this also includes software vendors), as it encompasses 65.9% of all detected leaks. This is then followed by Education (20.1%), Science & Tech (7%), Retail (1.5%), Manufacturing (1.2%), and Finance & Insurance (1%). Generative AI Leaks Trend Generative AI tools are exponentially growing in terms of their use in 2023 as many businesses and employees utilise them. However, this has also led to an exponential growth in generative AI leaks on GitHub last year as well. GitGuardian observed that in 2023, there was a 1,212 increase in the number of OpenAI API keys leaked on GitHub as compared to 2022. It was averaged that 46,441 API keys were leaked per month - this was the highest growing data point in GitGuardian’s report. Although OpenAI leads drastically in the number of leaks detected on GitHub, open-source AI models repository HuggingFace had a steep increase in leaked secrets month after month. This could indicate that there is a growing interest among developers and researchers of this AI tool. Other AI tools that were found to have leaks include Cohere, Claude, Clarifai, Google Bard, Pinecone, and Replicate. Although these AI tools were found to have leaks at a much lower level as compared to OpenAI and HuggingFace. Troubling Trend of Leaks GitGuardian monitored how well authors fixed leaks via revoking the secret as soon as possible to reduce the impact of the incident. Unfortunately, more than 90% of the secrets still remained valid 5 days after being leaked. Furthermore, only 2.6% of the leaks were revoked within 1 hour after GitGuardian notified them of the leak via email. However, not all types of leaked secrets were revoked at the same rate. Based on their analysis, leaked WeChat App (97.7% still remain valid after 5 days) and Algolia keys (95.5% still remain valid after 5 days) were the most likely to remain exposed for over 5 days. This is then followed by Strip keys (88.3%) and Cloudflare API keys (81%). Developers should be more concerned about these keys as they would be prime targets in credential harvesting campaigns.
GitHub Rectification In February, Github enabled push protection as a default for all public repositories to prevent accidental exposure of secrets when pushing new code. Related Topics 26 Billion Records Compromised in Huge Data Leak - dubbed as “Mother of All Breaches”. Apple's Alarming Report: 2.6 Billion User Records Exposed By Data Breaches in Past 2 Years 71 Million Emails from Naz.API stolen account list added to Have I Been Pwned. Comments are closed.
|
Archives
June 2024
Categories
All
|
|
© 2021, TAFA HOLDINGS (S) PTE LTD. ALL RIGHTS RESERVED
|


 RSS Feed
RSS Feed