AuthorTAFA Archives
April 2024
Categories
All
|
Back to Blog
Last week, breaches and cyberattacks occurred across several industries from the public, tech, e-commerce, hotel, optical supplies to the healthcare sector. Devastating consequences have been uncovered from earlier data breaches and attacks, such as 4,4 million SurveyLama users’ personal information has been exposed and that Leicester City Council’s confidential documents have been leaked on the dark web after a ransomware attack. Additionally, it was found that the 2023 Hong Kong Cyberport data breach affected 13,362 staff and jobseekers. Furthermore, new vulnerabilities and patches have also been found and released. It is highly recommended to not only be aware of them but to also update them as soon as possible.
Read on to receive a quick summary of what happened this week in the space of cybersecurity. US cancer centre suffers a data breach: 827,000 patients’ information exposed. Cancer treatment and research centre, City of Hope, is starting to notify 827,000 individuals that their personal and health information has been compromised in a data breach. In a data breach letter filed with the Maine Attorney General's Office, the data breach occurred between 19 September - 12 October 2023, whereby an unauthorised 3rd party managed to access a subset of City of Hope systems and copied some files that contained the affected individual’s information. The stolen data includes affected individuals’ names, birth dates, email addresses, phone numbers, driver’s licence numbers, ID numbers, social security numbers, bank accounts numbers, credit card details, health insurance information and medical information. City of Hope also clarified that not every data type listed was compromised for every patient - the level of exposed information varied per case.Upon detection, City of Hope stated that they took steps to contain the breach, notified relevant authorities, and retained a cybersecurity firm to put in security measures to improve their system’s security. The cancer centre has also stated that so far there has been no identification of any identity theft or fraud pertaining to the stolen information. Affected individuals are offered complimentary identity monitoring services for 2 years. It is highly recommended for impacted individuals to monitor their banking statements, and be vigilant against phishing attacks, unsolicited communications or requests for additional information. Jackson County in state of emergency after a ransomware attack. Jackson County, Missouri, declared a state of emergency on 2 April 2024 after a ransomware attack took down some of their services on Tuesday. The Assessment, Collection and Recorder of Deeds offices at all County locations will likely be closed until the end of the week as the IT department works on restoring tax payment, marriage licence, and inmate search systems impacted in the incident. Fortunately, based on a statement published on Tuesday, the Kansas City Board of Elections and Jackson County Board of Elections are not affected by this system outage. Officials have alerted the relevant authorities of this incident, and are currently working with 3rd party IT security experts to investigate the attack. Jackson County Executive Frank White, Jr. declared a state of emergency to expedite IT orders, activate emergency workers, and protect against a ransomware attack. As White stated, all county staff are taking the necessary steps to protect resident data, county assets and continue essential services to mitigate the impact of the ransomware attack. County officials have confirmed that residents’ financial information is not affected as the compromised systems did not store residents’ financial data. Acuity confirms hackers have stolen old non-sensitive government data from its GitHub repositories. Acuity, a federal contractor that works with U.S. government agencies, has confirmed that hackers have breached its GitHub repositories and stole old non-sensitive government documents. In an emailed statement, Acuity stated that they identified a cybersecurity incident related to GitHub repositories that contained old and non-sensitive information. However, once they were aware of the zero-day vulnerability, Acuity did the relevant security updates and performed mitigating actions according to the vendor’s guidance. After an investigation, Acuity saw no evidence of impact on any of their clients’ sensitive data. Although Acuity did not provide additional information due to the ongoing investigation, IntelBroker (1 of the threat actors behind the attack) has leaked thousands of records that contain information that belongs to the Justice Department, State Department, DHS and FBI employees. IntelBroker also claimed that they stole Five Eyes intelligence alliance documents, which some contain allegedly classified information. Another threat actor, Sangierro, told BleepingComputer, that the breach occurred on 7 March 2024, and they allegedly exploited a vulnerability in an Acuity Tekton CI/CD server to steal GitHub credentials and access their private repositories. PandaBuy, a shopping platform, suffered a data leak that impacted 1.3 million users. PandaBuy, a shopping platform that allows international users to purchase from various e-commerce platforms in China such as Tmall, Taobao and JD.com, was allegedly breached by 2 threat actors that exploited multiple vulnerabilities. The 2 threat actors, Sanggiero and IntelBoker, claimed that they managed to steal data that contained but not limited to 3 million unique UserId, first name, last name, phone numbers, email addresses, login IP, orders data, orders ID, home addresses, zip and country. According to Have I Been Pwned, 1,348,407 PandaBuy accounts have been exposed in the breach. The threat actor has also provided a small sample of email addresses, customer names, order numbers and details, shipping addresses, transaction dates and times, and payment IDs as evidence. Troy Hunt, creator of HIBP, tested password reset requests using the leaked addresses and confirmed that at least 1.3 million email addresses are valid and come from PandaBuy. However, the rest were made-up and duplicate addresses, so the 3 million figure was inflated by the threat actors. It is highly recommended for those who have PandaBuy accounts to reset your password, and remain vigilant against any phishing attacks and scams. Chilean data centre and hosting provider, IxMetro Powerhost suffered a cyberattack. IxMetro Powerhost, a data centre, hosting and interconnectivity company in locations in the U.S, South America and Europe, suffered a cyberattack by a new ransomware gang called SEXi, which encrypted the company’s VMware ESXi servers and backup. On 1 April, PowerHost’s Chile division, IxMetro, warned customers that they suffered a ransomware attack early Saturday morning which had encrypted some of the company’s VMware ESXi servers that are used to host virtual private servers for customers. Customers that hosted their websites or services on these servers are down as the company attempts to restore terabytes of data from backups. In one update, PowerHost has warned their customers that they might not be able to restore the servers as the backups have also been encrypted. PowerHost CEO, Ricardo Ruben, stated that they had attempted to negotiate with the threat actors to receive a decryption key, however the ransomware gang has demanded 2 BTC per victim, which would be equal to $140 million. For impacted VPS customers who still have their website content, the company is offering to set up a new VPS so that customers can bring their sites back online. SurveyLama suffers a data breach: 4.4 million users’ personal information exposed. SurveyLama, an online platform that rewards registered users for completing surveys, suffered a data breach in February 2024 which resulted in the exposure of 4,426,879 million users’ sensitive data. In early February, Have I Been Pwned (HIBP’s) creator, Troy Hunt, received information about a data breach impacted the service. The exposed data types include full names, birth dates, email addresses, IP addresses, passwords, phone numbers, and physical addresses. SurveyLama has notified impacted users via email, and confirmed the security incident. It is highly recommended for SurveyLama account holders to reset their passwords immediately and on other platforms that use the same credentials. As of now, there is no evidence of the compromised data being posted publicly online, which makes the exposure currently limited. Hoya confirms a cyberattack has disrupted optics production and orders. Hoya Corporation, a global manufacturer of optical products, that the Group’s head quarter and several of their business divisions have suffered an IT system incident, which caused servers at some of their production plants and business divisions to go offline on 30 March. In response to the incident, Hoya isolated the affected servers and informed the relevant authorities in the impacted countries. The optics company has also hired 3rd party forensic investigators to determine the cause of the incident, and whether the hackers accessed or extracted any confidential or personal information stored on the compromised systems. As a direct result of this incident, some production plants and ordering systems for certain products have been impacted. Omni Hotels confirms cyberattack behind ongoing nationwide IT outage. Omni Hotels & Resorts has confirmed a cyberattack that caused a nationwide IT outage in the U.S., in which some locations are still affected. The hotel chain has stated that since 29 March, Omni Hotels & Resorts have been responding to a cyberattack on their systems. In response to the attack, Omni took down the impacted systems, and their IT teams are working to restore and bring them back online. Furthermore, they have launched an investigation with a 3rd party cyber security response team, which is still ongoing. According to Omni employees, the IT teams are manually restoring the affected systems from scratch, and have been informed that the systems will be available again on 4 April 2024. The outage triggered by the cyberattack has affected many of Omni’s services which includes their reservations, hotel room door lock, and point-of-sale systems. It has been reported that front desk employees have been experiencing issues with credit card payments, new reservations, and modifying already-made reservations. Leicester City Council confirms ransomware attack after confidential documents were leaked. Leicester City Council in England confirmed that the March cyber incident was a ransomware attack after it was discovered that the malicious actors had uploaded the stolen documents to their dark web extortion site. Leicester’s strategic director, Richard Sword, confirmed on 3 April that “a small number of documents” on their servers has been published by a ransomware group (the INC Ransom). According to Sword, INC Ransom published around 25 or so confidential documents. These confidential documents include rent statements, applications to purchase council housing and identification documents such as passport information. Sword also stated they are unable to be certain whether other documents have been extracted from their systems, although they do believe that the threat actors have. The council also stated that most of their systems and phone lines are now operating as per normal after it was decided to shut everything down on 7 March when the attack was detected. It is highly advised for people in Leicester to report if anyone claims to have their data to the Leicestershire Police using the non-emergency call service 101 or an online form. Hong Kong privacy watchdog found that the 2023 Hong Kong Cyberport data breach affected 13,632 staff and jobseekers. Hong Kong’s Office of the Privacy Commissioner for Personal Data found that 13,632 staff and job seekers' personal data had been stolen when hackers attacked Hong Kong’s Cyberport last year. The investigation found that out of the 13,682 affected, 8,000 had employment ties with the company which includes 5,292 unsuccessful applicants and former employees. Others were managerial staff, interns and business partners. The personal data stolen includes names, ID cards, passport numbers, financial information such as bank account numbers, medical reports, photos, birthdates, social media accounts and academic information. For each affected individual, the amount of stolen information varies. Furthermore, it was found that 13 Window systems and 2 virtual servers were compromised. The watchdog has slammed the organisation’s cybersecurity oversights as they had failed to implement sufficient and effective security measures to ensure their systems security. It was found that they did not keep information secure, and kept information over the intended retention period. They have also sent an enforcement notice to the government-funded technology hub last week demanding them to carry out a list of improvements and submit a report within 2 months. MarineMax, a yacht retailer, disclosed data breach after a cyberattack. MarineMax, a boat and yacht retailer, stated that employee and customers’ data were stolen after their systems were breached in a March cyberattack. On 1 April 2024, in a new 8-K filing, it was revealed that the hackers gained access and stole personally identifiable data that belonged to an undisclosed number of individuals. Although the company did not attribute the attack to a specific threat group, the Rhysida ransomware gang has claimed the attack and is selling the allegedly stolen data for 15 BTC (just over $1,000,000). Rhysida has also leaked screenshots of what appears to be MarineMax’s financial documents, employee driver’s licences and passports on their data leak site as evidence. LayerSlider WordPress plugin critical flaw impacts 1 million sites. The LayerSlider WordPress plugin that is used in over 1 million sites, has a critical flaw (tracked as CVE-2024-2879) which allows unauthenticated SQL injection. The flaw impacts versions 7.9.11 through 7.10.0 of the plugin, and this could allow attackers to extract sensitive data such as password hashes from the site’s database. This puts these sites at risk of complete takeover or data breaches. The developer released a security update on 27 March. All users of LayerSlider are highly recommended to upgrade to version 7.10.1 which addresses this critical vulnerability. That is all! Enjoy the rest of the week and don't forget to update your devices and systems to the latest patches!
Back to Blog
Security researchers, Red Hat, warned users that the latest versions of the “xz” tools and libraries in Linux distributions contain malicious code that appears to allow unauthorised access and gain remote access to the entire system.
This vulnerability is tracked as CVE-2024-3094, and has been scored a 10 out of 10 on the Common Vulnerability Scoring System (CVSSv3). Specifically, this critical vulnerability is present in XZ versions 5.6.0 and 5.6.1. Users who use these versions are highly advised to immediately downgrade to older versions that do not contain the malicious code. Red Hat has warned users to immediately stop usage of any Fedora 41 or Fedora Rawhide instances for work or personal activity until users can downgrade their XZ version. Red Hat has also reverted to 5.4.x versions of XZ in Fedora 40 beta. Linux administrators can verify which version of XZ is installed by querying their package manager. CISA and CSA have published advisories warning developers and users to downgrade to an uncompromised XZ version (e.g. 5.4.6 Stable) and to look out for any malicious or suspicious activity on their systems. For more information: https://www.csa.gov.sg/alerts-advisories/alerts/2024/al-2024-033 https://www.redhat.com/en/blog/urgent-security-alert-fedora-41-and-rawhide-users https://www.bleepingcomputer.com/news/security/red-hat-warns-of-backdoor-in-xz-tools-used-by-most-linux-distros/#google_vignette
Back to Blog
Last week, breaches and cyberattacks occurred across several industries from the jewellery, discount retailer to the health industry. Devastating consequences have been uncovered from earlier data breaches and attacks, such as as 73 million AT&T customers’ data has been leaked on a hacker forum and that more than 2.8 million Point32Health customers’ personal information has been stolen in a breach. Additionally, 28 apps (including 17 free VPN apps) on Google Play have been found to turn Android devices into proxies, and that Google’s new AI search results encourage sites that push malware scams.
Furthermore, new vulnerabilities and patches have also been found and released. It is highly recommended to not only be aware of them but to also update them as soon as possible. Read on to receive a quick summary of what happened this week in the space of cybersecurity. New variant TheMoon malware infects 6,000 ASUS routers in 88 countries within 72 hours. Black Lotus Labs researchers have found a new variant of “TheMoon” malware botnet that has been infecting thousands of outdated small office and home office (SOHO) routers and IoT devices in 88 countries. The researchers have observed that 6,000 ASUS routers were targeted in under 72 hours during the latest TheMoon campaign which started in early March 2024. It is highly recommended to use strong admin passwords and upgrade your device’s firmware to the latest version to ensure that vulnerabilities are addressed. Common signs of malware infection on routers and IoTs include connectivity problems, overheating, and suspicious setting changes. Massachusetts health insurer has been hit by a data breach: More than 2.8 million individuals’ personal information stolen. Point32Health, the 2nd largest health insurer in Massachusetts, has announced that more than 2.8 million individuals’ personal information was stolen during an April 2023 ransomware attack. This ransomware attack impacted systems associated with Point32Health’s Harvard Pilgrim Health Care brand. In a notification letter, the company reports that they have identified signs that the data was copied and taken from Harvard Pilgrim systems from 28 March to 17 April 2023, and that these files may contain customers’ personal information. The stolen information includes names, addresses, birthdates, phone numbers, social security numbers, health insurance account information, financial account information, medical history, diagnoses, and treatment information. This week, the company filed a refreshed data breach notice to update the number of affected individuals to more than 2.86 million. The company is providing affected individuals with complimentary credit monitoring and identity protection services. Poh Heng Jewellery hit by data breach: Customers’ personal information could be compromised. Poh Heng Jewellery, a jewellery chain, notified their customers about a database breach that occurred on 25 March. The company has stated that the unauthorised access may have compromised their customers’ personal information. The compromised information could include customers’ names, telephone numbers, email addresses, residential addresses, member ID, birth dates and country of residence. Fortunately, no passwords and payment information were compromised. The company’s data protection officer, Ezekiel Chin, stated that once they discovered the breach, they immediately took action to secure their systems, and have reported the incident to relevant authorities. The company has recommended customers to be highly vigilant against phishing attempts, such as malicious links and websites whereby they request their passwords or other personal information. Giant Tiger, discount retailer, states customer data has been compromised in a 3rd party breach. Giant Tiger, a discount retailer, has announced that some of their customers’ contact information has been compromised in a third-party breach. The spokesperson for the company, Alison Scarlett, stated that the vendor would not be named, however the company was utilised by Giant Tiger to manage their customer communications and engagement. Furthermore, it was added that Giant Tiger is working to resolve the issue “as quickly and openly as possible”. In an email to customers, the retailer stated they discovered the security breach on 4 March, and concluded on 15 March that customer information was compromised. The compromised information varied between customers, and it included names and email addresses of those who subscribe to Giant Tiger emails. Furthermore, loyalty members and those who placed online orders for in-store pickups might have had their names, emails and phone numbers compromised. Some customers who placed online orders for home delivery may have had the same information and additionally their street addresses compromised. INC Ransom threatens to leak the stolen 3TB of NHS Scotland data. The INC Ransom extortion gang has threatened to publish 3 TB of data that is allegedly stolen after breaching the NHS of Scotland. In a post published on 27 March, the cybercriminals shared several sample documents with sensitive information about doctors and patients, including medical assessments, analysis results, and psychological reports. They stated that they would leak the data “soon” unless the NHS pays the ransom. A spokesperson for the Scottish Government has stated that the cyberattack only impacts NHS Dumfries and Galloway, which are one of the regional health boards that make up NHS Scotland. Furthermore, the government is working with multiple entities such as the health board, Police Scotland, National Crime Agency, and the National Cyber Centre, to determine the impact and plausible implications of the breach. NHS Dumfries and Gaolloway has confirmed that a ransomware group has leaked a small number of patients’ clinical data. All impacted patients will be informed by the NHS directly so that they can take appropriate measures to protect themselves. AT&T confirms 73 million customers’ data has been leaked on hacker forum. AT&T has now confirmed that 73 million current and former customers have been affected by a data breach after initially denying the leaked data originated from them. In a statement shared with BleepingComputer, AT&T stated that based on their preliminary analysis, the data set appears to be from 2019 or earlier, and has impacted approximately 7.6 million current AT&T account holders and approximately 65.4 million former account holders. Furthermore, security passcodes used to secure accounts were also leaked for 7.6 million customers. AT&T are reaching out to all 7.6 million impacted customers and have reset their passcodes. The company will notify all 73 million former and current customers about the breach and the following steps they should take. Free VPN apps on Google Play found to turn Android devices into proxies used for cybercrime and shopping bots. 17 VPN apps on Google Play have been found to use a malicious software development kit that turned Android devices into residential proxies that are likely used for cybercrime and shopping bots. Residential proxies are devices that route internet traffic through devices located in homes. This makes traffic appear legitimate and less likely to be blocked. Cybercriminals tend to use them to conceal malicious activities such as ad fraud, spam, phishing, credential stuffing and password spraying. A report published by HUMAN’s Satori threat intelligence team lists 28 apps on Google Play that secretly turned Android devices into proxy servers. Out of these, 17 apps were free VPN apps. The 28 apps are:
For safety precaution, it may be the safest to remove any of these apps that you used via uninstalling them. A Google spokesperson has confirmed that all 28 malicious apps have been removed from Google Play. Google’s new AI search results encourage sites that push malware scams. Google’s new AI-powered ‘Search Generative Experience’ algorithm has been found to recommend scam sites that redirect visitors to unwanted Chrome extensions, fake iPhone giveaways, browser spam subscriptions, and tech support scams. Lily Ray, a SEO consultant, found that Google’s SGE is recommending malicious websites within their conversational responses, making it easier for people to fall for scams. As since SGE links the websites within the answers, this can make malicious sites seem more trustworthy and believable. It was found that most redirects lead users to fake captchas or Youtube sites that attempt to trick the visitor into subscribing to browser notifications. Browser notifications are a common tactic scammers use to send visitors unwanted ads directly to the operating system desktop, even when you are not on the website. Google has reported that they continuously update their systems and ranking algorithms to protect against spam, and have taken actions to remove these spam out of Search. That is all! Enjoy the rest of the week and don't forget to update your devices and systems to the latest patches!
Back to Blog
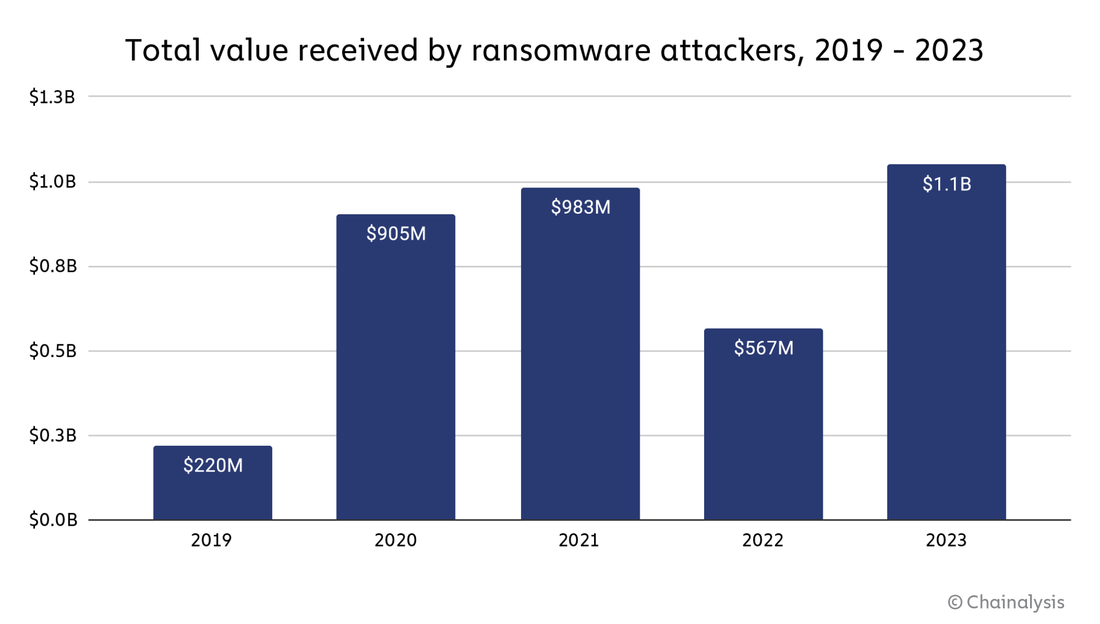
In the ever-evolving landscape of cybercrime, ransomware has emerged as a formidable threat, with cybercriminals raking in record-breaking sums through their malicious activities. The year 2023 saw a staggering $1.1 billion paid in ransom payments, underscoring the urgent need for heightened cybersecurity measures and increased awareness. Join us as we delve into the intricacies of this alarming trend, uncover the factors driving the surge in ransom payments, and explore strategies to combat this growing menace. On 2023 Ransomware Payments Ransomware payments soared in 2023 to $1.1 billion, and broke the previous record of $983 million in 2021. Unfortunately, this indicates that the decrease in ransomware activities in 2022 was an anomaly. This anomaly could be attributed to several reasons such as geopolitical events (e.g. Russian-Ukrainian conflict), an overall reluctance to pay ransoms due to potential sanction risks, and also law enforcement taking on ransomware groups (e.g. Hive intervention). This overall trend line, created by Chainalysis, from 2019 to 2023 indicates that ransomware is an escalating issue. Furthermore, it is important to note that the numbers calculated did not reflect the monetary impact in terms of productivity loss and repair costs. For instance, the MGM ransomware attack was estimated to cost MGM over $100 million. Furthermore, not all ransom payments, especially cryptocurrencies payments, were traceable. Hence, the figures made are all conservative estimates, and are likely to increase when new ransomware addresses are found.
Ransomware Resurgence: Understanding the Surge in Payments According to a new Chainalysis report, the 2023 record can be attributed to:
Combating the Ransomware Epidemic: Strategies for Prevention & Mitigation
Conclusion The surge in ransom payments in 2023 serves as a stark reminder of the evolving nature of cyber threats and the critical need for proactive cybersecurity measures. The ransomware landscape in particular has evolved significantly in 2023 via the changes in tactics and affiliations among threat actors which has led to a more aggressive and efficient approach. Although ransomware attackers have innovated and adapted to regulatory changes and law enforcement actions, there were also significant steps made against ransomware via collaboration of government agencies, affected organisations, and blockchain intelligence. By understanding the factors driving this trend, implementing robust security practices, and fostering a culture of awareness and collaboration, we can collectively combat the ransomware epidemic and protect our digital future. Related Topics 71 Million Emails from Naz.API stolen account list added to Have I Been Pwned. 26 Billion Records Compromised in Huge Data Leak - dubbed as “Mother of All Breaches”. Apple's Alarming Report: 2.6 Billion User Records Exposed By Data Breaches in Past 2 Years
Back to Blog
Last week, breaches and cyberattacks occurred across several industries from the telecommunications, software, bakery to the IT sector. Devastating consequences have been uncovered from earlier data breaches and attacks, such as a malware campaign that has been found to have infected over 39,000 WordPress websites in the past 6 months, and MarineMax alleged stolen data being put up on sale for 15 bitcoin. In addition, a misconfiguration at Firebase has been found to expose 19 million plaintext passwords and over 125 million sensitive user records. Furthermore, new vulnerabilities have been found and patches have also been found and released. It is highly recommended to not only be aware of them but to also update them as soon as possible.
Read on to receive a quick summary of what happened this week in the space of cybersecurity. 70 million AT&T accounts leaked online: AT&T claimed leaked data did not originate from their systems. As many as 70 million AT&T customers’ data are on sale on a data theft forum for a starting price of $200,000 and incremental offers of $30,000. The threat actor, ShinyHunters, has also offered a ‘buy it now’ option with a price of $1,000,000. Another threat actor, MajorNelson, has now offered the same data, although less than half of AT&T’s customer records, for free. The data is claimed to be stolen from a breach sometime in 2021 or earlier. However, AT&T claimed it did not originate from them and that their systems were not breached. AT&T has also told BleepingComputer that they have seen no evidence of a breach in their systems, The stolen information includes customers’ names, addresses, phone numbers, birthdates, and social security numbers. It is highly recommended for AT&T customers (especially those before and through 2021) to be vigilant against any phishing attacks - such as SMS and email phishing. Mintlify data breach: Customers’ GitHub tokens exposed. Mintlify, a documentation startup, publicly disclosed that 91 of their customers had their GitHub tokens exposed in a 1st March data breach. In a blog post, Mintlify stated that the data breach occurred due to a vulnerability in their own systems, which leaked the company’s internal admin credentials to customers. These credentials can be utilised to access the company’s internal endpoints to access other unspecified sensitive user information. Mintlify co-founder, Han Wang, stated that they have notified the affected customers, and they are currently working with GitHub to identify whether the compromised tokens were used to access private repositories. If these tokens were stolen, a threat actor could obtain the same level of access to a person’s source code. Fujitsu suffered a cyberattack, and attackers may have stolen customer’s information. Fujitsu, a Japanese technology giant, confirmed a cyberattack in a statement on Friday. In the statement, it was confirmed that it was a malware attack, whereby they detected malware on multiple work computers. Upon further investigation, they discovered that files that contained personal information and customer information may have been stolen. Fujitsu stated that they had disconnected the affected systems from their network, and are currently investigating how the malware compromised their network, and whether there was a data breach. As of now, Fujitsu did not elaborate on the nature of the attack, nor whose or the type of personal information that may have been stolen. Fujitsu has reported this incident to relevant authorities in Japan “in anticipation” that personal information may have been stolen. International Consolidated Airlines Group (IAG) warns Air Europa customers of data breach that has led to their personal data being compromised. IAG, the parent company of British Airways and Iberia, has sent an email to Air Europa’s customers that due to an October security incident, their personal data has been compromised. The exposed data includes customers’ names, birthdays, nationalities, ID cards or passport information, and phone numbers. The company stated that they do not have evidence of the leaked data being inappropriately used, and further stated that if “it were to happen, the resulting inconvenience would be limited in any case”. Update: IAG confirmed in a statement that they have not acquired Air Europa and would never email their customers directly. They further stated it is a matter for Air Europa and not IAG. Spa Grand Prix official email account hacked: Targeted fans to phish for their bank information. Threat actors have hacked into the official contact email of Spa Grand Prix, the Belgian Grand Prix event. The race organisers stated that the email account was hijacked on 17 March, and the threat actor has sent fraudulent emails to an undisclosed number of fans that informs the recipients of a €50 voucher via clicking an embedded link. The link that directs victims to a fake website similar to the official portal of the Spa Grand Prix, which asks for victims’ personal information such as their banking information. Once this security issue was noticed, SPA GP sent alert emails to their customers that the previous message was a phishing scam and warned them not to click on any links. Additionally, the organisation has asked their IT security subcontractor to put in additional security measures to prevent this incident from reoccuring. SPA GP has filed a complaint with the Belgian cyber police, and will also file a civil claim with an examining magistrate. Currently, an investigation is underway to determine the cause and circumstances that led to this attack. Greggs, a UK bakery chain, is the latest victim of POS system outages: Forced to close some stores. Greggs has fallen victim to point of sale (POS) system outages that has led to their stores being forced to close. On the morning of 20 March, it has been reported on social media that customers have been unable to pay with their cards or found their local branches of Greggs closed. This indicates that there could be a technical issue with their POS, which processes purchases. A statement from Greggs said that some stores have not been able to take card and cash payments, and that they had “resolved a technical issue” that affected tills in some of its shops and has apologised for the inconvenience. This incident has followed recent card payment outages in the UK from Sainsbury’s and Tesco, to McDonalds. Misconfiguration at Firebase exposed 19 million plaintext passwords. 3 cybersecurity researchers have found that due to misconfigured instances of Firebase, a Google platform that hosts databases, cloud computing and app development, has led to almost 19 million plaintext passwords being exposed on the public internet. The researchers scanned more than 5 million domains, and found 916 websites from organisations that either had no security rules enabled or had set them up incorrectly. They were able to find more than 125 million sensitive user records. This includes emails, names, passwords, phone numbers, and billing information with banking details. In particular, the problem of the exposed passwords gets worse, as 98% of them (19,867,627) are in plaintext. After analysing the data, the researchers tried to warn all impacted companies of improperly secured Firebase instances, and sent 842 emails over 13 days. Although just 1% of the site owners replied, a quarter of the notified site administrators have fixed the misconfiguration in their Firebase platform. However, some organisations that were contacted had unprofessional responses. For instance, an Indonesian gambling network that manages 9 websites mocked the researchers when they reported the problem and gave guidance on how to fix it. Unfortunately, this company accounted for the largest number of exposed bank account records (8 million) and plaintext passwords (10 million). Sign1, a malware campaign, has infected over 39,000 WordPress websites. Sign1, a previously unknown malware campaign, has been found to have infected over 39,000 websites in the past 6 months. This campaign has caused visitors to see unwanted redirects and pop-up ads. Sucuri, a website security firm, discovered the campaign after a client’s website randomly displayed popup ads to their visitors. The threat actors use WordPress custom HTML widgets or install the legitimate Simple Custom CSS and JS plugin to inject malicious JavaScript code. Based on Sucrui’s analysis, the malware generates dynamic URLs that change every 10 minutes to evade blocks. Furthermore, the malicious code checks for specific referrers and cookies before executing - they tend to target visitors from major sites like Google, Yahoo, Instagram and Facebook. Furthermore, the malware creates a cookie on the target’s browser so that the popup is only displayed once per visitor, making it less likely to generate reports towards the compromised website owner. Sucuri warns that Sign1 has evolved over the past 6 months, with infections increasing exponentially when a new version of the malware was released. The latest attack wave, which has been underway since January 2024, has claimed 2,500 sites. It is highly recommended for site administrators to use a strong/long password, and update your plugins to the latest version. Furthermore, it is best to remove unnecessary add-ons to reduce your attack surface. Rhysida ransomware group takes responsibility for the MarineMax cyberattack: Offers stolen data for 15 bitcoin. The Rhysida ransomware group has taken responsibility for the Marinemax, one of the largest retailers of recreational boats and yachts globally, cyberattack. MarineMax announced in a SEC filing earlier this month that they were targeted in an attack that led to some disruption. Now, the Rhysida ransomware group is auctioning the alleged stolen data from MarineMax on their website, with a starting price of 15 bitcoin ($950,000). As proof of MarineMax’s stolen data, they have published some screenshots that show financial documents and some spreadsheets. Due to their low resolution, it is unclear how sensitive the data is. However, MarineMax stated in their filing that they did not store sensitive data in the compromised environment. Saflok electronic locks security vulnerability can be exploited to open millions of doors. Dormakaba’s Saflok electronic locks have a security vulnerability, named Unsaflok, that can be exploited to forge keycards and open doors. This vulnerability impacts more than 3 million locks that are commonly used in hotels, and multi-family housing environments. It has been found that a total of more than 13,000 locations across 131 countries are likely affected. The vulnerable lock models include Saflok MT and the Quantum, RT, Sapphire and Confidant series devices, which are used in combination with the System 6000, Ambiance, and Community management software. According to the security researchers, an attacker can use a keycard from a property where the vulnerable locks are used, forge them and unlock any door on that property. Furthermore, any device that can write or emulate MIFARE Classic cards can be used in this attack. Dormakaba has worked on patches for this security vulnerability and has started rolling them out in November 2023. However, the process is slow and only 36% of affected locks have received the fix. The reason is that upgrading each hotel is an intensive process. The company has reported that till now they are unaware of any reported instances in which this vulnerability has been exploited, and has strongly recommended their customers to upgrade as soon as possible to address this vulnerability. Microsoft released a patch for an Xbox vulnerability. Microsoft has released a patch for an Xbox vulnerability (tracked as CVE-2024-2891) and it impacts Xbox Gaming Services. According to Microsoft, it has ‘important’ severity and this vulnerability can be easily exploited by a local attacker with low privileges to escalate permissions to the System. Microsoft has informed customers that app package versions 19.87.13001.0 and later to patch the vulnerability. For those users who have automatic updates enabled, the fix should be automatically delivered. Microsoft stated that although there is no evidence currently of malicious exploitation, the flaw has been assigned with an ‘exploitation more likely’ rating. That is all! Enjoy the rest of the week and don't forget to update your devices and systems to the latest patches!
Back to Blog
Last week, breaches and cyberattacks occurred across several industries from the streaming, fast food, ICT, financial to the public sector. Devastating consequences have been uncovered from earlier data breaches and attacks, such as Nissan confirming that 100,000 people’s data has been breached and Stanford University confirming that 27,000 individual’s personal information has been compromised during a breach. Furthermore, new vulnerabilities have been found and patches have also been found and released. It is highly recommended to not only be aware of them but to also update them as soon as possible.
Read on to receive a quick summary of what happened this week in the space of cybersecurity. French Employment Agency data breach exposes up to 43 million people’s data. France’s Employment Agency suffered a data breach that could potentially expose up to 43 million users’ data, and this affected users who registered over the past 20 years. French Travail, the French national employment agency, announced on 13 March 2024 that their IT systems and those of Cap Emploi, a government employment service, were breached. The exposed personal data includes names, birth dates, social security numbers, user IDs, email addresses, postal addresses, and phone numbers of France Travail and Cap Emploi users. Through a statement, the agency confirmed that login credentials, passwords and bank details were not compromised. Although this breach does not affect allowance payments, and users can still connect to their account, it is highly advised to be vigilant against any phishing attacks such as messages that pretend to be from their services, and identity theft. France Travail has notified relevant authorities, and investigations have started to determine whether sufficient data security measures were put in place in compliance with the EU’s GDPR. It was indicated that the malicious actor had gained unauthorised access to Cap Emploi’s systems around 6 February and French Travail that the threat actor impersonated a Cap Emploi civil service officer to do so. The agency started to notice suspicious activity in their IT systems a few days later. More than 15,000 Roku customers’ accounts were sold for as little as 50¢ each to make illegal purchases. Roku has disclosed a data breach whereby 15,363 customers accounts have been hacked in a credential stuffing attack. This has led to the hacked accounts being sold for as little as 50¢, which allows the purchasers to make fraudulent purchases of hardware and streaming subscriptions. Roku stated that once an account was breached, it allowed threat actors to change the account’s information which includes passwords, email addresses and shipping addresses. This allows threat actors to use stored credit card information without the account holder receiving order confirmation emails. Roku stated that they have secured the impacted accounts and forced a password reset upon detecting the incident. Furthermore, Roku’s security team said that any unauthorised purchases will be cancelled and will be refunded. Legitimate account holders who are impacted must visit “my.roku.com” and click on ‘Forgot password?’ to get a reset link. The International Monetary Fund (IMF) suffers a cyberattack: Email accounts breached. The IMF has disclosed that they have suffered a cyber incident which was detected on 16 February 2024 and it was determined that 11 IMF email accounts were compromised. The impacted email accounts have been re-secured, and so far they found no evidence of attackers gaining access to other systems or resources outside of the breached email accounts. Investigations into this breach are still ongoing. Due to security reasons, IMF no further details were disclosed. McDonald’s stated that the global outage was caused by a 3rd party service provider’s configuration change. McDonald’s blamed a 3rd party service provider’s configuration change for the global outage that forced many of their fast-food restaurants to close. According to a statement shared by the company’s Chief Information Officer Brian Rice, the global technology system outage began around midnight CDT on Friday. Rice stated that many markets are back online, and the rest are in the process of coming back online. Rice emphasised that the outage was not directly caused by a “cybersecurity event” rather it was caused by a configuration change. In a separate message sent to employees via the company’s OTP portal, McDonald’s stated that the issue is being resolved and that all impacted stores and systems are returning online. The massive IT outage impacted restaurants worldwide - such as in the US, the UK, Japan, Australia, Canada, the Netherlands, Italy, and New Zealand. Employees has shared on social media that they could not take orders, open cash registers, or process payments because POS systems were down. Acer confirms Philippines employees’ data has been leaked. Acer Philippines confirmed that employee data has been stolen during a cyberattack on their 3rd party vendor after a threat actor leaked the data on a hacking forum. On 12 March, a threat actor - ph1ns published a link to download a stolen database that contains Acer employee data on a hacking forum. The attacker told BleepingComputer that no ransomware or encryption was involved and that it was a pure data theft attack. They further confirmed that they were not attempting to extort the company, but they provided evidence that they wiped the data on the breached servers before they lost access. Acer Philippines emphasised that no customer data has been affected, and that their systems remained uncompromised. Acer has also notified relevant authorities, and an investigation of the breach is underway. Nissan confirms that 100,000 people's data has been exposed after a ransomware attack. Nissan Oceania is warning that a December 2023 ransomware attack has impacted 100,000 people due to a data breach. Nissan has confirmed that the hackers have stolen data on some current and former employees, and customers of Nissan, Mitsubishi, Renault, Skyline, Infiniti, LDV and RAM dealerships in the region. In an updated statement, Nissan will notify approximately 100,000 individuals of the data breach over the coming weeks on what information of theirs that was exposed, what they can do, and the forms of support available. Based on their estimates, about 10% of the impacted individuals had some form of government identification compromised. It includes approximately 4000 Medicare cards, 7,500 drivers licence, 220 passports, and 1300 tax file numbers. The remaining 90% had other personal information impacted which includes loan-related documents, employment details and birth dates. Unfortunately, Akira (the ransomware group that attacked them) has already leaked the stolen data via their extortion page on the dark web. Nissan will be providing free access to IDCARE, free credit monitoring services through Equifax in Australia and Centrix in New Zealand, and reimbursement for the replacement of compromised government IDs. It is highly recommended to be vigilant against any suspicious activity on their accounts and immediately report any suspicious activity to the authorities. Equilend January 2024 ransomware attack has led to a data breach of employee’s data. Equilend, a Fintech firm, is sending notification letters to their employees to inform them that their personal information has been compromised in a January 2024 ransomware attack. The personal information impacted are names, birthdates, social security numbers, and Equilend payroll information. In the notification letter, Equilend stated that they have found no evidence that any personal information has been used to commit identity theft or fraud. However, Equilend will be providing impacted individuals with complementary identity theft protection services. Stanford University data breach compromised 27,000 individuals’ personal information. Stanford University is starting to send notification letters to 27,000 individuals that their personal information has been stolen in a ransomware attack on Stanford’s Department of Public Safety (DPS). Akira ransomware group claimed responsibility for the attack. In the notification letter, it was stated that the stolen personal information includes individuals’ names, birthdates, social security numbers, passport numbers, driver’s licence numbers, government ID numbers and other information. Although, the type of personal information varies for each individual. For some individuals, other types of information leaked include biometric data, health/medical information, email address with password, username with password, security questions and answers, digital signature, and credit card information with security codes. The university also stated that they have found no evidence of the compromised information being misused. Impacted individuals are offered identity theft protection services including credit monitoring for free. Fortinent released patch for critical RCE vulnerability in endpoint management software. Fortinent has released a patch for a critical RCE vulnerability (tracked as CVE-2024-48788) in its FortiClient Enterprise Management Server (EMS) software. This vulnerability can allow attackers to gain remote code execution on vulnerable servers in low-complexity attacks that do not require user interaction. This vulnerability impacts FortiClient EMS versions 7.0 (7.0 through 7.0.10) and 7.2 (7.2.0 through 7.2.2). Fortinent has not revealed if there is any evidence of this vulnerability being exploited in attacks before patching. Fortinent has also fixed another critical out-of-bounds write weakness (CVE-2023-42789) in the FortiOS and FortiProxy captive portal that could let unauthorized users to remotely execute unauthorised code or commands. 2 other high–severity flaws (tracked as CVE-2023-36554 and CVE-2023-47534) has also been patched this week, which allows attackers to execute arbitrary commands or code on vulnerable systems. That is all! Enjoy the rest of the week and don't forget to update your devices and systems to the latest patches!
Back to Blog
Last week, breaches and cyberattacks occurred across several industries from life insurance, semiconductor, financial to the public sector. Devastating consequences have been uncovered from earlier data breaches and attacks, such as the Play ransomware attack that resulted in 65,000 Switzerland government documents leaked, and UniCredit being fined $3.1 million for data breach by Italy privacy watchdog. Furthermore, new vulnerabilities have been found and patches have also been found and released. It is highly recommended to not only be aware of them but to also update them as soon as possible.
Read on to receive a quick summary of what happened this week in the space of cybersecurity. American Express customer data exposed in third-party breach. Due to a hack at American Express’ merchant processor in which American Express Card member data was processed, American Express is warning customers that due to the 3rd party breach, customers’ credit cards were exposed. In a data breach notification filed with the state of Massachusetts, the company warned customers that their account information may have been compromised. The compromised data includes customers’ credit card account numbers, names and card expiration dates. However, it is not clear the amount of customers impacted, the merchant processor that was breached, and when the attack occurred. American Express stated that they have begun investigation into the breach, and that they have notified relevant authorities. Furthermore, the company stated that if a cardmember’s credit card is used to make fraudulent purchases, the customers would not be responsible for the charges. It is highly advised for customers to regularly review their bank statements for the next 12-24 months, and report any suspicious behaviour. The company also suggests enabling instant notifications via the American Express mobile app to receive fraud and purchase alerts. Furthermore, it is encouraged to request a new card number if your card information was stolen to prevent usage of your card from bad actors. Canada’s anti-money laundering agency hit by a cyberattack: Forced to go offline. The Financial Transactions and Reports Analysis Centre of Canada (FINTRAC) announced that they had to take their corporate systems offline as a precaution due to a “cyber incident”. FINTRAC is a Canadian government agency that operates as their financial intelligence unit. In a statement posted on their website, the agency stated that intelligence or classified systems were not accessed. FINTRAC is collaborating with federal partners to restore their operations and enhance their defences to prevent similar incidents from reoccurring. Fidelity Investments Life Insurance Company (FILI) informing roughly 28,000 individuals of data breach. FILI is notifying 28,268 individuals that their personal information has been compromised due to a third party breach from services provider Infosys McCamish System (IMS). In their notification letter, FILI noted that the threat actor had obtained information held by IMS about the individual and their policy. The compromised information includes customers' names, birthdates, state of residence, social security numbers, bank account and routing numbers, and credit card numbers. However, as investigation is still ongoing, they are unable to determine with certainty exactly what personal information was accessed during the attack. The impacted individuals are offered a free 2 years of credit monitoring. Switzerland reports that the Play ransomware attack resulted in 65,000 government documents leaked. The National Cyber Security Centre (NCSC) of Switzerland released a report on their investigation of a data breach following a ransomware attack by the Play ransomware gang on Xplain, a Swiss technology and software solutions provider for various Swiss government departments. It was disclosed that 65,000 sensitive Federal government files were leaked in the breach. It was stated that out of approximately 1.3 million files published by Play ransomware, about 5% (65,000 documents) are relevant to the Federal Administration. 95% of those files impact the administrative units of the Federal Department of Justice and Police: the Federal Office of Justice, the Federal Office of Police, the State Secretariat for Migration, and the internal IT service centre. 3% of the data were from the Federal Department of Defence, and the Civil Protection and Sport. Around 5,000 documents contained sensitive information such as personal data (e.g. names, email addresses, telephone numbers, and addresses), technical details, classified information, and account passwords. A small set of a few hundred files contained IT system documentation, software or architectural data, and passwords. Jersey finance regulator suffers a data breach: Allowing access to nonpublic names and addresses. The Jersey Financial Services Commission (JFSC) has been hit by a data breach which allowed access to nonpublic names and addresses. In a statement, the watchdog stated that they detected a vulnerability in their registry system on 23 January 2023, and took action to resolve the issue. With an independent cybersecurity partner, they conducted a forensic review and identified that the vulnerability was caused by a misconfiguration in their 3rd party supplied registry system. In an update on their website, it was said that the JFSC’s corporate network was not compromised, and the breach did not link any individuals to a specific registered entity or any role held. However, 66,806 individuals did have their names and addresses accessed where it was not already public on the register. North Korea hacks 2 South Korean chip firms and stole engineering data. South Korea’s National Intelligence Service (NIS) warns that North Korean hackers are targeting domestic semiconductor manufacturers. NIS stated that these attacks have increased in the latter half of 2023 until recently, whereby they target internet-exposed servers vulnerable to flaws to access corporate networks. NIS mentioned that in December 2023 and February 2024, at least 2 cyberattacks on separate entities occurred, whereby the company’s configuration management and security policy servers were hacked. Reportedly, this resulted in sensitive data being compromised such as product design drawings and facility site photos. The 2 victims were not named in the report. However, NIS reports that they postulate that these cyberattacks are aimed at collecting valuable technical data which North Korea could utilise to develop their own chip-making program which can help to develop weapons. Italy privacy watchdogs fines UniCredit $3.1 million for data breach. Italy’s data protection authority has fined UniCredit, Italy’s second-largest bank, US$3.1 million for a 2018 data breach that resulted in approximately 788,000 customers and former customers. The bank responded that they will appeal the decision to court as no bank data had been compromised, and the incident had been immediately resolved. The 2018 data breach on their mobile banking platform resulted in approximately 788,000 customers and former customers’ data such as names, tax codes, and other identification codes. The authority stated that the sanctions took into account the large number of people involved in the data breach and the seriousness of the breach, as well as the timely adoption of corrective measures. Apple was fined $1.95 million by the European Commission for “abusive” App store rules. The European Commission has fined Apple US$1.95 million for allegedly abusing their market dominance in music streaming app distribution to prevent developers from promoting cheaper services outside the app. The Commission found that Apple applied restrictions on app developers which prevented them from informing iOS users about alternative and cheaper music subscription services available outside of the app, which is illegal under EU antitrust rules. The investigation began after Spotify and an e-book/audiobook distributor issued complaints on 2 Apple App Store policies: (1) charging a 30% commission fee on all subscription fees through Apple’s in-app purchase system, and (2) preventing developers from promoting cheaper membership options outside the app. The European Commission stated that although market dominance is not illegal under EU antitrust rules, dominant companies do have a special responsibility to ensure that they do not abuse their position. However, Apple stated that they believe that the European Commission has not found any evidence of consumer harm or proof of anti-competitive behaviour. Instead, Apple stated that Spotfiy is the primary benefactor of this decision, and that Spotify chose not to promote in-app subscriptions even though they were involved in the initial complaints. Furthermore, Apple stated that Spotify has the largest music streaming app in the world, and has met with the European Commission more than 65 times during the investigation. Furthermore, Spotify has 56% of Europe’s music streaming market, and pays Apple for none of the services that have helped them become one of the most recognisable brands in the world. Apple also attributed their App Store for Spotify’s pop[u;larity, and that Spotify utilises Apple’s tools and technology to build, update and share their app with Apple users around the world. Apple stated they respect the Commission’s decision, but they will be appealing the fine. Apple released emergency security updates to fix 2 zero-day vulnerabilities. Apple released emergency security updates to fix 2 iOS zero-day vulnerabilities (tracked as CVE-2024-23225 and CVE-2024-23296) which are exploited in attacks on iPhones. Both vulnerabilities allow bad actors to bypass kernel memory protections. Apple stated they addressed the flaws for devices running iOS 17.4, iPadOS 17.4, iOS 16.76 and iPad 16.7.6. The list of impacted devices includes:
That is all! Enjoy the rest of the week and don't forget to update your devices and systems to the latest patches!
Back to Blog
This massive stolen account list, with a list of 1 billion credentials, was compiled via credential stuffing lists and data stolen through the use of information-stealing malware.
Credential stuffing is a type of cyberattack in which credentials that have been previously obtained from a data breach are used to attempt to log into other services/systems. The Naz.API dataset allegedly contains over 1 billion lines of stolen credentials. This dataset garnered attention after it was used as part of an open-source intelligence (OSINT) platform called illicit.services, although the data list has been shared around the data breach community for a while. Illicit.services allows one to search for stolen information, which includes victims’ names, phone numbers, email addresses, and other personal data. Fortunately, the service was shut down in July 2023 due to concerns for cyberattacks such as Doxxing and SIM-swapping attacks. However, the service was once again made available in September. From a screenshot of the dataset, each line consists of a login URL, login name, and an associated stolen password. Understanding the Risks
Stolen Dataset Added to HIBP On 17 January 2024, it was announced that Naz.API dataset was added to Have I Been Pwned, a data breach notification service, after they received the data list from a well-known tech company. According to them, the dataset consists of 319 files, which totals to 104 GB, and contains 70,840,771 unique email addresses. It is important to note that although there are 70,840,771 unique email addresses, for each email, there are likely many other records for the different sites’ credentials that were stolen from. It was also noted that the Naz.API data is likely old as it contained some of their own and subscribers’ passwords that were used in the past. From this, they were able to extrapolate that some of the data were over 13 years old. It is recommended that you should check if your credentials are in the Naz.API dataset, via searching your credentials on Have I Been Pwned. If it is found that your email is part of the stolen data list set, the site will warn you. This indicates that at some point your computer has been compromised with information-stealing malware. If your email address is part of the stolen data list, we do highly recommend you to change passwords for all of your saved accounts, especially those accounts that are highly confidential. This includes passwords for your email accounts, bank accounts, and other personal accounts. Other Steps to Safeguard Your Digital Identity Other than checking the Have I Been Pwned, it is also important to:
Conclusion As we navigate the digital landscape, the Naz.API data breach serves as a stark reminder of the importance of cybersecurity. By taking proactive steps to protect ourselves, staying informed, and spreading awareness, we can mitigate the risks posed by data breaches and safeguard our digital identities. Remember, in the digital age, vigilance is key, and knowledge is your shield against cyber threats. Stay safe, stay secure, and empower yourself in the digital realm. Related Topics 26 Billion Records Compromised in Huge Data Leak - dubbed as “Mother of All Breaches”. Apple's Alarming Report: 2.6 Billion User Records Exposed By Data Breaches in Past 2 Years Unmasking Phishing: Your Guide to Spotting The Signs of Phishing Protect Yourself: Best Practices to Combat Phishing Attacks
Back to Blog
Last week, breaches and cyberattacks occurred across several industries from AI, pharmaceutical, healthcare, legal, steel to the public sector. Devastating consequences have been uncovered from earlier data breaches and attacks, such as LoanDepot confirming that 16.9 million individual’s personal information was stolen in the early January ransomware attack, and that the May 2023 breach at Houser LLP led to more than 325,000 people’s personal information being exposed. Furthermore, new vulnerabilities have been found and patches have also been found and released. It is highly recommended to not only be aware of them but to also update them as soon as possible.
Read on to receive a quick summary of what happened this week in the space of cybersecurity. 20 million Cutout.Pro users’ personal information leaked on a data breach forum. Cutout.Pro, an AI service, suffered a data breach that resulted in the exposure of 20 million members’ personal information. The exposed information includes their names, email addresses, IP addresses, hashed and salted passwords. On 27 February, a threat actor called ‘KryptonZambie’ shared a link on the BreachForums hacking forum to CSV files that contain 5.93 GB of data stolen from Cutout.Pro. 3 CSV files contains what appears to be a database dump of 41.4 million record, whereby 20 million records consist of unique email addresses. The bad actor also stated that they still had access to the breached system. From samples seen by BleepingComputer, the leaked data includes: user id, profile picture, API access key, account creation data, email address, User IP address, mobile phone number, password and salt used in hashing, user type and account status. Have I Been Pwned, a data breach monitoring service, added to their breach catalogue, confirmed that the leaked dataset includes the information of 19,972,829 people. Furthermore, the threat actor has distributed the files on their personal Telegram channel. This caused a much wider circulation of the stolen data. Although Cutout.Pro has not verified the data breach, it has been verified via multiple sources that the email listed in the data leak matches Cutout.Pro users. It is highly recommended that Cutout.Pro users reset their passwords on this service, and any other accounts that use the same credentials. It is very important that all Cutout.Pro users be vigilant against phishing scams. Cencora disclosed a cyberattack: Personal Information stolen from their systems. Cencora, a global pharmaceutical solutions provider, disclosed that they identified a data breach on 21 February in a filing with the SEC. Although, it is not yet clear the type of data exfiltrated, and if employees and/or customers are affected. In the filing, the company stated they have taken steps to contain the incident, and an investigation is underway with assistance from law enforcement and 3rd party cybersecurity experts. As of the date of the filing, the data breach has not impacted their operations. Along with Global Affairs’ cyberattack, Canada’s RCMP has also been hit by a cyberattack. The attack on the network of the Royal Canadian Mounted Police (RCMP) was disclosed on Friday, but as of Monday, the RCMP was still “actively managing” the attack. Although the details of the extent and nature of the attack was not shared, RCMP stated that they are working with other Canadian government agencies to assess the “breadth and scope” of the breach and “hold those responsible accountable”. According to the RCMP, the attack did not impact their operations, nor the safety and security of Canadians and RCMP partners. However, during the weekend, RCMP’s website was briefly unavailable. Last Monday, the Office of the Privacy Commissioner (OPC) confirmed that they were aware of the RCMP incident, and announced that they are investigating a data breach due to the attack on Global Affairs Canada’s internal network. As of now, it is unclear whether the RCMP and Global Affairs Canada attacks are related. ThyssenKrupp, one of the world’s largest steel producers, confirms a cyberattack on the automotive division. ThyssenKrupp confirms that they had suffered a cyberattack which led to their systems in its Automotive division breached. This forced them to shut down their IT systems to contain the threat. In a statement to BleepingComputer, ThyssenKrupp stated that their Automotive Body Solutions business unit recorded unauthorised access to their IT infrastructure last week, and since detection have been working with ThyssenKrupp Group’s IT security team to contain the threat. The company disclosed that no other business units or segments have been impacted by the attack, and that they are gradually returning to normal operations. Law firm disclosed more than 325,000 people’s personal information was exposed in May 2023 data breach. Houser LLP, a US law firm, stated in a regulatory filing that the May 2023 system breach exposed more than 325,000 people’s personal information. The exposed data includes names, social security numbers, drivers licence numbers, individual tax identification numbers, financial account information, and medical information. It was also stated that the unauthorised actor informed Houser that they deleted copies of any stolen data and would not distribute any stolen files. Once a 3rd party vendor completed their review on 18 January this year, Houser began notifying their clients of the investigation and findings. Furthermore, the firm has also offered to mail letters to potentially impacted individuals on the behalf of their clients. Affected clients have been offered credit monitoring services, and law enforcement has been notified about the incident. BlackCat ransomware gang claims they allegedly stole 6TB of data from Change Healthcare. The BlackCat ransomware gang claimed responsibility for a cyberattack on Optum, a subsidiary of UnitedHealthGroup (UHG). In a statement published on their data leak site, BlackCat stated that they allegedly stole 6TB of data from Change Healthcare’s network that belonged to “thousands of healthcare providers, insurance providers, pharmacies, etc.” The ransomware gang claims that they stole source code for Change Healthcare solutions and sensitive information that belongs to their partners. This includes the US military’s Tricare healthcare program, the Medicare federal health insurance program, CVS Caremark, MetLife, Health Net etc. From their claims, the stolen sensitive data includes medical records, insurance records, dental records, payments information, claims information, patients’ PII data (e.g. email addresses, addresses, social security numbers, phone numbers), and active US military/navy personnel PII data. On a dedicated status page, Optum stated that they are working to restore the impacted systems. As of 1 March, they have restored Change Healthcare’s Rx ePrescribing service, however other services are not operational. They also added that Optum, United Healthcare, and UnitedHealth Group systems have not been affected. In the page, Optum has also confirmed that the attack was caused by the BlackCat ransomware gang. Hessen Consumer Center hit by a ransomware attack causing disruption in their systems. The Hessen Consumer Center in Germany was hit by a ransomware attack which caused their IT system to shut down, disrupting their operations. In an announcement on 22 February, the organisation stated that their telephone and email communications have been impacted. Although the communication disruptions have been mostly addressed, people still have trouble reaching the consumer advice centre and consumer advocates. It was also reported that 3rd party security experts are aiding them to restore the availability of all communication channels in the impacted advice centres. However, an estimate for the return to normal operations has not been given. At this stage, the organisation is unable to confirm whether any data or what type of data has been stolen. Although they did state that once they are able to determine the type of data stolen, they will inform the affected individuals. Rhysida ransomware gang claimed cyberattack on Lurie Children’s Hospital: Demands $3.7 million for the stolen data. The Rhysida ransomware gang has claimed the cyberattack on Lurie Children’s Hospital in Chicago beginning of this month. The cyberattack forced the hospital to take their IT systems offline, and postpone some of their medical care. The attack caused their email, phone, accesstoMyChart, and on-premises internet were all impacted. Furthermore, their ultrasound and CT scan results were rendered unavailable, patient service prioritisation systems were taken down, and doctors were forced to switch to pen and paper for prescriptions. On 28 February, the ransomware gang listed the hospital on their extortion portal and they claimed to have stolen 600GB of data from the hospital. They are offering to sell the data for 60 BTC (~$3.7 million) to a single buyer. As of 2 March, some of their services are still unavailable, and their systems are still offline. LoanDepot confirmed 16.9 million individuals’ personal information was stolen in the early January ransomware attack. LoanDepot informed the Maine Attorney General’s Office that more than 16.9 million individuals were impacted by the early January attack, and has started sending out notification letters to them. In the letter, LoanDepot stated that via their investigation, it was determined that an unauthorised 3rd party gained access to some of their systems and managed to access sensitive personal information. The compromised personal information includes names, addresses, email addresses, birthdates, social security numbers, and financial account numbers. For those impacted, LoanDepot is offering free identity protection and credit monitoring services. It is highly recommended for affected individuals to also be vigilant against any suspicious activity, especially in their financial accounts. Anycubic 3D printers hacked to expose a critical security bug. According to online reports from Anycubic customers, someone has hacked into their 3D printers to alert them that their printer is impacted by a critical security bug that exposes them to cyberattacks. The person who hacked into the printers added a hacked_machine_readme.gcode.file to their devices, a file that usually contains instructions. This vulnerability allegedly can allow threat actors to control any Anycubic 3D printer using the company’s MGTT service API. The file also asked Anycubic to open-source their 3D printers as their software “is lacking”. The text file states that their machine has a critical vulnerability, and that immediate action is strongly recommended to prevent potential attacks. It adds that affected customers can disconnect the printer from the Internet if they do not want to get hacked, and that this is just a harmless message and that the hacker does not intend or has harmed them in any way. The text file also states that 2,934,635 devices have downloaded the message via the vulnerable API. Customers who received the message are highly recommended to disconnect their printers from the Internet until the company patches the security issue. That is all! Enjoy the rest of the week and don't forget to update your devices and systems to the latest patches!
Back to Blog
Massive data leak shows Chinese firm foreign government and activists. I-Soon, a Chinese tech security company that competed for Chinese government contracts, was found to be able to breach foreign government systems, infiltrate social accounts and hack into personal computers. This was revealed by experts that analysed a massive data leak. The leaked documents from I-Soon showed that they compromised more than a dozen governments - such as the government office networks in India, Thailand, Vietnam and S.Korea. They breached “democracy organisations” in Hong Kong, universities, and the Nato military alliance as reported by SentinelLabs researchers. The leak contained hundreds of files that contained chat logs, presentations, and lists of targets. Lists of Thai and British government departments and screenshots of attempts to log in to an individual’s Facebook account were found. Furthermore, many of the files were versions of marketing materials, whereby the company listed targeting counterterrorism centres (such as in Pakistan and Afghanistan) as evidence of their ability to perform these tasks. There were also screenshots of arguments between an employee and supervisor over salaries, and a document describing software aimed at accessing a target’s Outlook emails. The company was also found to offer potential clients the ability to break into individuals’ accounts on X to monitor their activity, read their private messages and send posts. I-Soon also laid out how their hackers could access and take over a person’s computer remotely - allowing them to execute commands and monitor what they type. Other services include ways to breach iPhones and other smartphone operating systems, and custom hardware (e.g. power bank). Philippine education ministry hit by data leak: Over 210,000 school and tax records leaked. Jeremiah Fowler, a cybersecurity researcher, found a vulnerability that gave nearly full access to an online platform used by senior school students applying for government vouchers to cover their tuition costs. It was a serious potential security lapse as they were stored without password protection and hence was available to anyone with Internet access. This has resulted in the exposure of over 210,000 records of the Philippine education ministry. This cloud-stored database included 154 GB worth of tax filings, consent forms, government certifications, and employment and death certificates. The online application forms in particular contained the applicants’ full name, their photos, birthdate, gender, address, contact information, parents’ sources of income and properties owned. The Philippines’ National Privacy Commission stated that they were informed by Fowler of the breach in January, and that the vulnerability has been patched. Wyze security camera breach: 13,000 strangers able to look into other’s homes. After an outage on 16 February, as Wyze security cameras were brought back online, users started seeing images and videos in their Events that were not from their cameras. The company explained that due to the system becoming overloaded caused device IDs to be mapped incorrectly. This resulted in some accounts being connected to the wrong cameras. Wyze stated that the root cause was from a 3rd party caching client library that they recently integrated into their system. It has been estimated that 13,000 people were about to peek into someone else’s home. However, only 1500 of them enlarged a thumbnail or viewed a video. The company stated that 99% of their users weren’t impacted at all, and that they had already contacted all affected users. Fortunately, the breach resulted in only events being seen, and not a live view. As once Wyze discovered the problem, the events tab was immediately disabled. Wyze has stated that they have taken steps to ensure this incident would not reoccur. Critical infrastructure software maker confirms ransomware attack. PSI Software SE, a German software developer for complex production and logistics processes, confirmed that the cyber incident disclosed last week was a ransomware attack that impacted their internal infrastructure. The attack forced them to disconnect from several IT systems, including email, as a measure to mitigate data loss risk. This attack is alarming as if the attackers accessed PSI’s software code or data, they could pose risks to public services, energy and transport, as PSI serves critical infrastructure sectors. PSI says the investigation so far has not revealed any evidence that the attacker pivoted to customer systems. The company has informed all relevant authorities, and experts from the Federal Office for Information Security have been assisting them in incident response and remediation efforts. U-Haul informs customers that hackers accessed customer records using stolen credentials. U-Haul has started informing customers that a hacker used stolen account credentials to access an internal system for dealers and team members to track customer reservations. The exposed personal information includes full names, birthdates and drivers licence numbers. Fortunately, the breach system is not part of their payment system, hence the hackers did not access payment card data. U-Haul stated they had reset passwords for all affected accounts and implemented additional security safeguards and controls to prevent such incidents from happening again. Recipients of the data breach notification will receive a 1 year identity theft protection service. As of yet, U-Haul has not determined how many customers have been exposed from this incident. Insomniac Games suffered a ransomware attack: Impacted employees being notified that their personal data has been leaked online. Insomniac Games, a subsidiary under Sony, suffered a ransomware attack in November, and are currently sending data breach notification letters to impacted employees whose personal data was stolen and leaked online. 1.67 TB of documents were leaked on the dark web leak site after the game studio refused to pay the $2 million ransom. As a result, the leaked files included the personal information of their employees, former employees, and independent contractors. Furthermore, the leaked files included many ID scans and internal documents, such as contract information, licensing agreements, and screenshots of their upcoming Wolverine game. The company is extending the ID Watchdog services offered as part of their employees benefit package, with 2 additional years of complimentary credit monitoring and identity restoration beyond the current enrollment period. The company also had a dedicated call centre to answer questions from affected employees. Carousell fined S$58,000 over data leaks that affected more than 2.6 million users. Carousell, an e-commerce platform, has been fined S$58,000 over 2 data breaches. One of which resulted in at least 2.6 million customers’ data put up for sale, and the other resulted in 44,477 users’ data in Singapore, Malaysia, Indonesia, Taiwan and the Philippines being exposed. PDPC determined the financial penalty by taking account of some factors like Carousell’s cooperation with investigations, their “prompt and effective remediation actions” once the breaches were discovered, their first time being breached, and the second breach being “particularly sophisticated”. Over 28,500 Exchange servers are vulnerable to an actively exploited flaw. Up to 97,000 Microsoft Exchange servers may be vulnerable to a critical severity privilege escalation flaw (tracked as CVE-2024-21410) that are being actively exploited. Microsoft addressed this flaw on 13 February, however 28,500 servers are currently being identified as vulnerable. Furthermore, a threat monitoring service, Shadowserver, identified that there were approximately 97,000 potentially vulnerable servers. It is highly recommended to apply the Exchange Server 2019 Cumulative Update 14 (CU14) update released in the February 2024 Patch Tuesday. Hackers exploiting critical RCE flaw in WordPress Brick Builder Theme. Hackers are actively exploiting a critical RCE vulnerability (tracked as CVE-2024-25600) that impacts the Brick Builder Theme in Wordpress. This vulnerability can lead to attackers running malicious code on vulnerable sites. A fix became available on 13 February with the release of version 1.9.6.1. It was observed that in the post-exploitation phase, the attackers used specific malware to disable security plugins like Wordfence and Sucuri. Wordfence also confirmed that they had seen 24 detections of this vulnerability being exploited in a day, showing that this vulnerability is being actively exploited. It is highly recommended that Bricks users upgrade to version 1.9.3.1 immediately either by navigating “Appearance>Themes” in WordPress dashboard and clicking update or to manually update them. That is all! Enjoy the rest of the week and don't forget to update your devices and systems to the latest patches! |
|
© 2021, TAFA HOLDINGS (S) PTE LTD. ALL RIGHTS RESERVED
|

 RSS Feed
RSS Feed